没有合适的资源?快使用搜索试试~ 我知道了~
CSMA/CA MAC Protocol with Function of Monitoring based on Binary...
0 下载量 110 浏览量
2021-02-06
22:52:48
上传
评论
收藏 512KB PDF 举报
温馨提示

试读
17页
The CSMA/CA protocol is the most widely-compete agreement used by a network. Therefore, MAC .layer of cognitive radio networks mostly use the CSMA/CA protocol to provide the competitive channel .resources. Due to the unique characteristics and related needs of the cognitive radio networks, design .their network protocol is a critical task. For its characteristics, design and implement a comprehensive .CSMA/CA protocol, including arrival rate control, priority services, monitoring, conflict resol
资源详情
资源评论
资源推荐

DOI: 10.4018/IJSSCI.2016040103
Copyright © 2016, IGI Global. Copying or distributing in print or electronic forms without written permission of IGI Global is prohibited.
Volume 8 • Issue 2 • April-June 2016
Yifan Zhao, School of Information, Yunnan University, Kunming, China
Shengjie Zhou, School of Information, Yunnan University, Kunming, China
Hongwei Ding, School of Information, Yunnan University, Kunming, China
Shaowen Yao, School of Information, Yunnan University, Kunming, China
Zhijun Yang, School of Information, Yunnan University, Kunming, China
Qianlin Liu, School of Information, Yunnan University, Kunming, China
The CSMA/CA protocol is the most widely-compete agreement used by a network. Therefore, MAC
layer of cognitive radio networks mostly use the CSMA/CA protocol to provide the competitive channel
resources. Due to the unique characteristics and related needs of the cognitive radio networks, design
their network protocol is a critical task. For its characteristics, design and implement a comprehensive
CSMA/CA protocol, including arrival rate control, priority services, monitoring, conflict resolution
and increased throughput; elaborated protocol model, system throughput and other parameters,
demonstrates the correctness of the CSMA/CA protocol; comparison with other protocols, highlighting
the advantages of the agreement.
ACK, Binary Tree Conflict Resolution, Cognitive Radio Network, CSMA/CA, Multichannel, Throughput
Cognitive radio network (CRN) also called smart radio network, has some significant features, such
as: flexible, intelligent, reconfigurable and so on. It purposefully changes certain operating parameters
(such as transmission power, the carrier frequency and modulation techniques, etc.) to adapt to the
internal state of the received radio signal statistics changes in order to achieve any time, any place
highly reliable communication and efficiently use limited radio spectrum resources in heterogeneous
network by sensing the external environment and use of artificial intelligence techniques to learn
from the environment real-time. The core idea of cognitive radio network is through intelligence of
learning ability and spectrum sensing to realize dynamic spectrum allocation and spectrum sharing.
In the network, secondary users dynamically search spectrum holes for communicating, a technique
called dynamic spectrum access. When users occupy a primary licensed spectrum, secondary users
35

Volume 8 • Issue 2 • April-June 2016
36
must exit from the band. They went to search for other free ones to complete their communications
(Peng et al., 2016).
In cognitive wireless networks, MAC protocol analysis and design versatility is still current hot
research issues.
MAC protocol’s performance using a multi-channel way to jump the intersection is optimal.
Because such agreements can give full play to the advantages of supports that multi-channel in
multiplexing (Lou, 2015). However, these studies use S-ALOHA MAC protocol.
Although the use of CSMA/CA MAC protocol can avoid the shortage of S-ALOHA MAC
protocol, the problem of collisions between data packets is inevitable in CSMA/CA MAC protocol
(Zhou et al., 2015).
In this paper, study for the cognitive radio networks, explain the random multiple access
technology which is widely used in computer systems and communication networks. The biggest
advantage of this technology is to enable user occupation of public resources dynamically, make use
of existing data storage area and information transfer channels to its maximum.
Because there are a lot of users in the networks, so the channel resources are limited. If every
user sends messages according to no law, then the collision channel will be quite severe (Ding et
al., 2015). Thus the researchers can also use the CSMA/CA protocol, in which a node listens to the
channel and then sends a message if the channel is idle; the probability of such a collision would be
significantly reduced (Dongfeng, 1999).
When the information is sent out, without feedback, the node will not know whether the
information was successfully sent or not. On this basis, if coupled with an ACK message segment at
the end of each information packet, in this way, the information has been sent successfully or not at a
glance (Yingxu Wang, 2015). However, the channel collision will still occur for the existence of delay.
Therefore, the ability of conflict resolution is critical in the efficient of systems work. In various
conflict resolutions algorithm, tree algorithm is a more effective decomposition method (Zhou et al.,
2015). Conflict resolution for binary trees is proved to be an effective method of conflict resolution,
but so far such algorithms are more complex analysis. Based on random multiple access system, a
new algorithm analysis-isolated algorithm of binary trees for conflict resolution; the basic idea of
the algorithm is: force the information packets to be sent at the same time slot into an activation
source group, and each activation source do the same set of independent Bernoulli trials; if the result
is ‘0’, then select the left slot (the first slot) to send information; if the result is ‘1’, then select right
slot (the second slot) to send information packets (Dongfeng, 1997). When the number of terminal
station which information packets selected left slot to send is 0, the system turned to the right slot to
activate the right slot until the number of terminal station is zero too.
After the introduction of binary collision resolution mechanism, information packet collisions
can be sent again in the next time after all the collisions is divided making the system more robust;
increases the system throughput.
When the researchers introduce the multichannel mechanism, the system has N channels to
transmit packets, the nodes occupied of channel resources randomly according to their different
business requirements3. Each priority has no limit on the number of users, the order of priority from
high to low be priority N, priority N-1... priority 1 (Shang, 2007). Priority
i
of business occupied
the channel 1 to channel
i
, as shown in Figure 1.
The arrival Information packets on the channel
i
obey
Poisson
distribution with arriving rate
isG
i
, the arrival process of priority
r
on the channel
i
obedience the process with arrival rate
λ
i i
G N i= − +/ ( )1 . Such system is a load balancing system, the same arrival rates for each channel
isG G i N
i
= =( , ,..., )1 2 (Ma Zuchang, 2004). Different quality of service according to different
requirements, the multi-channel CSMA protocol realized different services of different QoS
prioritization requirements by prioritizing.

Volume 8 • Issue 2 • April-June 2016
37
In the analysis of a network or a device, the authors often want to be able to reach the control
the rate of the information transmission or throughput of the system, etc. For this problem, three-
dimensional probability is introduced; use different probabilities to control different time transmission
process respectively and getting the results needed. Even the researchers can use multi-channel,
priority to control the access of each node to the channel resources, making the network or device
can be debugged in different network environments.
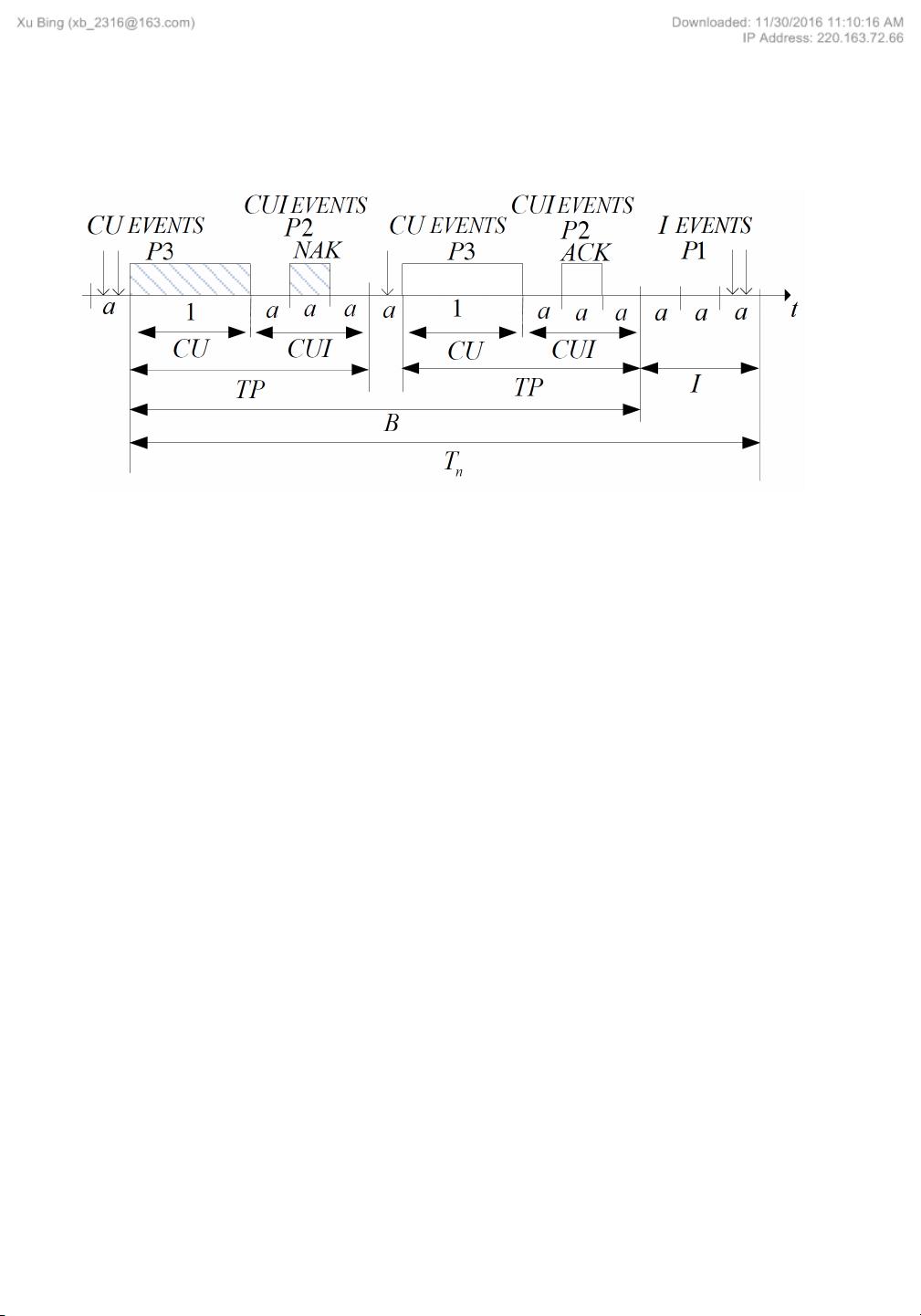
In the proposed protocol, there will be three random events:
• U events: Event that information packets are sent successfully.
• C events: Event that information packets collide with each other (the collision appears).
• I events: Event that there is no information packets in the channel arrive, the channel is idle.
These three events above continuously staggering circulate on the time axis and the cycle is
variable T
n
(Feng Xie, 2015). They are forced into: the channel is idle (I events) event, the channel
is busy (CU events) and the channel is idle following the CU events (CUI events); the packet is sent
successfully or unsuccessfully (combined C events with U event, denoted by CU event); force the
CU events and the CUI events into B events (Shengjie Zhou et al., 2015). Then use three-dimensional
probability:
P1
,
P2
,
P3
to control the period of I events, CUI events and CU events separately.
The model of multichannel three-dimensional probability CSMA/CA protocol with function of
monitoring based on binary tree conflict resolution algorithm (MAB-CSMA/CA) in channel
i
is
showed as Figure 2.
Consider the system having N channels and N priorities, the nodes are accessed to the channels
randomly by the business priorities of themselves.
Assume that the priority sequence is arranged from low to high as priority 1, priority 2… priority
N. The service with priority
i
occupies channel 1 to
i
(
i
=1, 2… N), that is the service with priority
Figure 1. The system model based multiple channels CSMA/CA/CA
Volume 8 • Issue 2 • April-June 2016
38
1 occupies channel 1, priority 2 occupies channel 1 and channel 2, and the service with priority N
occupies channel 1 to channel N (Zhou et al., 2015).
In channel i , if the channel is idle, then the user decides to send an information packet probability
P1 ; if the channel is busy, when CU events happen, the user listens to the channel at probability P2
; if the channel is busy, when CUI events happen, the user listens to the channel at probability P3
;in the transportation period, if the channel is the first idle following the CU events, then the user
listens to the channel at probability P3 (Zhou et al., 2015). This control strategy, P1 , P2 and P3
by three-dimensional selection enables the system under different load utilization and throughput is
guaranteed.
Before analyze the system performance, first do the following assumptions:
1. The channel is ideal with no noise and interference
2. The basic unit of the system control clock is
a
, the information packets arrived at time
a
will
transmit at the starting time of the next slot
3. The channel propagation delay is
a
, the packet length is unit length and is an integral
multiple of
a
4. The access method of number i i N=
( )
1 2, ,. .., channel is timeslot three-dimensional probability
CSMA/CA protocol, and the arrival process of number
i
channel satisfy the Poisson process
whose independent parameter is
i
G
, each arrival process on the channel is independent of each
other (Shengjie Zhou et al., 2015)
5. The channel using the MAB-CSMA/CA protocol, the information packets need to be sent at the
first slot in the transmission period can always detecting the state of the channel at last moment
6. During the transmission of information packets, the phenomenon of packet collisions occurs
inevitably, and continues to be sent after a random time delay, it sends will not produce any
adverse effects on the arrival process channel
Figure 2. The model based multichannel three-dimensional probability CSMA protocol with function of monitoring based on binary
tree conflict resolution in channel
i
剩余16页未读,继续阅读
weixin_38558870
- 粉丝: 4
- 资源: 900
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

评论0