没有合适的资源?快使用搜索试试~ 我知道了~
wireless communication and networks part3
温馨提示

试读
100页
wireless communication and networks William Stallings 2 edition英文版的影印版本
资源推荐
资源详情
资源评论
190
CHAPTER
7 / SPREAD
SPECTRUM
If
m,
a,
C,
and
X
o
are integers, then this technique will produce a sequence of integers
with each integer in the range 0
:5
X
n
<
m.
An
essential characteristic of a pseudoran-
dom number generator
is
that the generated sequence should appear random.
Although the sequence
is
not random, because it
is
generated deterministically, there
is
a variety of statistical tests that can be used to assess the degree to which a sequence
exhibits randomness. Another desirable characteristic
is
that the function should be a
full-period generating function. That
is,
the function should generate all the numbers
between 0 and
m
before repeating.
With the linear congruential algorithm, a choice of parameters
that
provides a
full period does
not
necessarily provide a good randomization. For example, consider
the two generators:
X
n
+
1
=
(6X
n
)mod
13
X
n
+
1
=
(7X
n
)mod
13
Write out the two sequences to show that both are full period. Which one appears
more random to you?
7.10 We would like
m
to be very large so
that
there
is
the potential for producing a long
series of distinct random numbers. A common criterion is
that
m
be
nearly equal
to
the
maximum representable nonnegative integer for a given computer. Thus, a value
of
m
near to or equal to 2
31
is typically chosen. Many experts recommend a value
of
2
31
-
1.
You may wonder why one should not simply use 2
3
\
because this latter num-
ber
can
be
represented with no additional bits, and the mod operation should
be
eas-
ier
to
perform.
In
general, the modulus
2
k
-
1
is
preferable to
2
k
.
Why
is
this so?
7.11
In
any use of pseudorandom numbers, whether for encryption, simulation,
or
statisti-
cal design, it
is
dangerous to trust blindly the random number generator that happens
to
be
available in your computer's system library. [PARK88] found
that
many con-
temporary textbooks and programming packages make use
of
flawed algorithms for
pseudorandom
number
generation. This exercise will enable you to test your system.
The test
is
based on a theorem attributed to Ernesto Cesaro (see [KNUT98] for
a proof), which states that the probability
is
equal
to
-;
that
the greatest common
7T
divisor of two randomly chosen integers
is
1.
Use this theorem in a program to deter-
mine statistically the value of
7T.
The main program should call three subprograms: the
random number generator from the system library to generate the random integers; a
subprogram to calculate the greatest common divisor of two integers using Euclid's
algorithm; and a subprogram that calculates square roots.
If
these latter two programs
are not available, you will have to write them
as
welL
The main program should loop
through a large number of random numbers to give an estimate of the aforementioned
probability. From this, it
is
a simple matter to solve for your estimate of
7T.
If
the result is close to 3.14, congratulations!
If
not, then the result
is
probably
low,
usually a value of around 2.7. Why would such an inferior result
be
obtained?
7.12 This problem demonstrates that different LFSRs can be used to generate an m-sequence.
a. Assume an initial state of 10000 in the
LFSR
of Figure 7.19a. In a manner similar
to Figure 7.13b, show the generation of
an
m-sequence.
b. Now assume the configuration
of
Figure 7.19b, with the same initial state, and
repeat part
a.
Show
that
this configuration also produces an m-sequence,
but
that
it
is
a different sequence from
that
produced by
the
first LFSR.
7.13 Demonstrate
that
the codes in an 8
X
8Walsh matrix are orthogonal to each other by
showing that multiplying any code by any other code produces a result of zero.
7.14 Consider a
CDMA
system in which users A and B have the Walsh codes
(
-1
1
-11
-1
1
-11)
and (
-1
-111
-1
-111),
respectively.
a. Show the
output
at the receiver if A transmits a data bit 1 and B does not transmit.
b. Show the
output
at the receiver ifA transmits a data bit 0 and B does not transmit.

7.7/
KEY
TERMS,
REVIEW
QUESTIONS,AND
PROBLEMS
191
Output
(a)
Output
(b)
Figure 7.19 Two Different Configurations of LFSRs
of
Length 5
c.
Show the
output
at the receiver ifA transmits a data bit 1 and B transmits a data
bit
1.
Assume the received power from
both
A and B
is
the same.
d. Show the
output
at the receiver if A transmits a data bit 0 and B transmits a data
bit
1.
Assume the received power from both A and B
is
the same.
e. Show the
output
at the receiver ifA transmits a data bit 1
and
B transmits a data
bit
O.
Assume the received power from both A and B
is
the same.
f.
Show the
output
at the receiver if A transmits a data bit 0
and
B transmits a data
bit
O.
Assume the received power from
both
A and B
is
the same.
g.
Show the
output
at
the receiver
if
A transmits a data bit 1
and
B transmits a data
bit
1.
Assume the received power from B is twice the received power from A. This
can
be
represented by showing the received signal component from A as consist-
ing of elements
of
magnitude
1(
+
1,
-1)
and the received signal component from
B as consisting
of
elements
of
magnitude 2(
+
2,
- 2).
h.
Show the
output
at the receiver if A transmits a data bit 0 and B transmits a data
bit
1.
Assume the received power from B
is
twice the received power from A.
Key Terms
Review Questions
Problems
8.1
Error Detection
Parity Check
Cyclic Redundancy Check
8.2 Block Error Correction Codes
Block Code Principles
Hamming Code
Cyclic Codes
BCH
Codes
Reed-Solomon Codes
Block Interleaving
8.3 Convolutional Codes
Decoding
Turbo Coding
8.4 Automatic Repeat Request
Flow Control
Error
Control
8.5 Recommended Readings
8.6
CODING
AND
ERROR
192
t
~.
8.1 /
ERROR
DETECTION
193
In
earlier chapters, we talked about transmission impairments and the effect of data
rate and signal-to-noise ratio on bit
error
rate. Regardless
of
the design
of
the trans-
mission system,
there
will
be
errors, resulting in the change
of
one
or
more
bits in
a transmitted frame.
Three approaches are
in
common use for coping with data transmission errors:
•
Error
detection codes
•
Error
correction codes, also called forward error correction
(FE
C) codes
• Automatic
repeat
request
(ARQ)
protocols
An
error
detection code simply detects the presence
of
an
error. Typically,
such codes are used in conjunction with a protocol at
the
data
link
or
transport
level (see Figure 4.4)
that
uses
an
ARQ
scheme. With
an
ARQ
scheme, a receiver
discards a block of
data
in which
an
error
is detected
and
the
transmitter retrans-
mits
that
block
of
data.
FEC
codes
are
designed
not
just
to
detect
but
corr,ect
errors, avoiding
the
need
for retransmission.
FEC
schemes are frequently used in
wireless transmission,
where
retransmission schemes
are
highly inefficient and
error
rates may
be
high.
This chapter looks at all three approaches in turn.
8.1 ERROR DETECTION
In
what follows, we assume
that
data are transmitted
as
one
or
more contiguous
sequences of bits, called
frames.
Let
us define these probabilities with respect to
errors in transmitted frames:
P
b:
Probability of a single bit error; also known as the bit
error
rate
(BER)
PI:
Probability
that
a frame arrives with no bit errors
P
2
:
Probability that, with an
error
detection algorithm in use, a frame arrives
with
one
or
more
undetected errors
P
3
:
Probability that, with an
error
detection algorithm in use, a frame arrives
with one
or
more
detected bit errors
but
no undetected bit errors
First consider the case when no means are
taken
to
detect errors. Then the
probability of detected errors (P
3
)
is
zero. To express the remaining probabilities,
assume the probability
that
any bit
is
in
error
(P
b
)
is
constant and independent for
each bit. Then we have
PI
=
(1
-
n)F
P
2
=1-P
I
where
F
is the number
of
bits
per
frame.
In
words, the probability
that
a frame
arrives with no bit errors decreases when the probability of a single bit error
increases, as you would expect. Also, the probability
that
a frame arrives with no bit
errors decreases with increasing frame length; the longer the frame, the more bits it
has and
the
higher
the
probability
that
one
of
these
is
in
error.
194
CHAPTER
8
I
CODING
AND
ERROR
CONTROL
Example 8.1 A defined objective for
ISDN
(Integrated Services Digital
Network)
con-
nections is
that
the
BER
on
a 64-kbps channel should
be
less
than
10-
6
on
at
least
90%
of
observed
i-minute
intervals. Suppose now
that
we have
the
rather
modest user require-
..
"
..
"'
",
',"
'.
..
' :... ",'
',-.
-,'
'.
.. ..
'.
.
'.
: : :
:"
" "
>',
: :
:::
'>
:.,,:.:>':-:.:
: :
::.:::.:.:.:.::.:.:
..
,::.::'
..
:.::
..
-::::
:.:
:
..
-.:.:.'.'.:.:::.:'
::.:.:
>:
ment
that
on
average one frame with an undetected bit
error
should occur
per
day
on
a continuously used 64-kbps channel,
and
let us assume a frame length of
1000
bits. The
number
of
frames that can
be
transmitted
in
a day comes
out
to
5.529
X
10
6
,
which yields
a desired frame
error
rate
of
P
2
=
1/(5.529
X
10
6
)
=
0.18
X
10-
6
.
But
if
we assume a
value
of
P
b
of
10-
6
,
then
PI
=
(0.999999)1000
=
0.999
and therefore
P
2
=
10-
3
,
which
is
about three orders of magnitude too large to
meet
our
requirement.
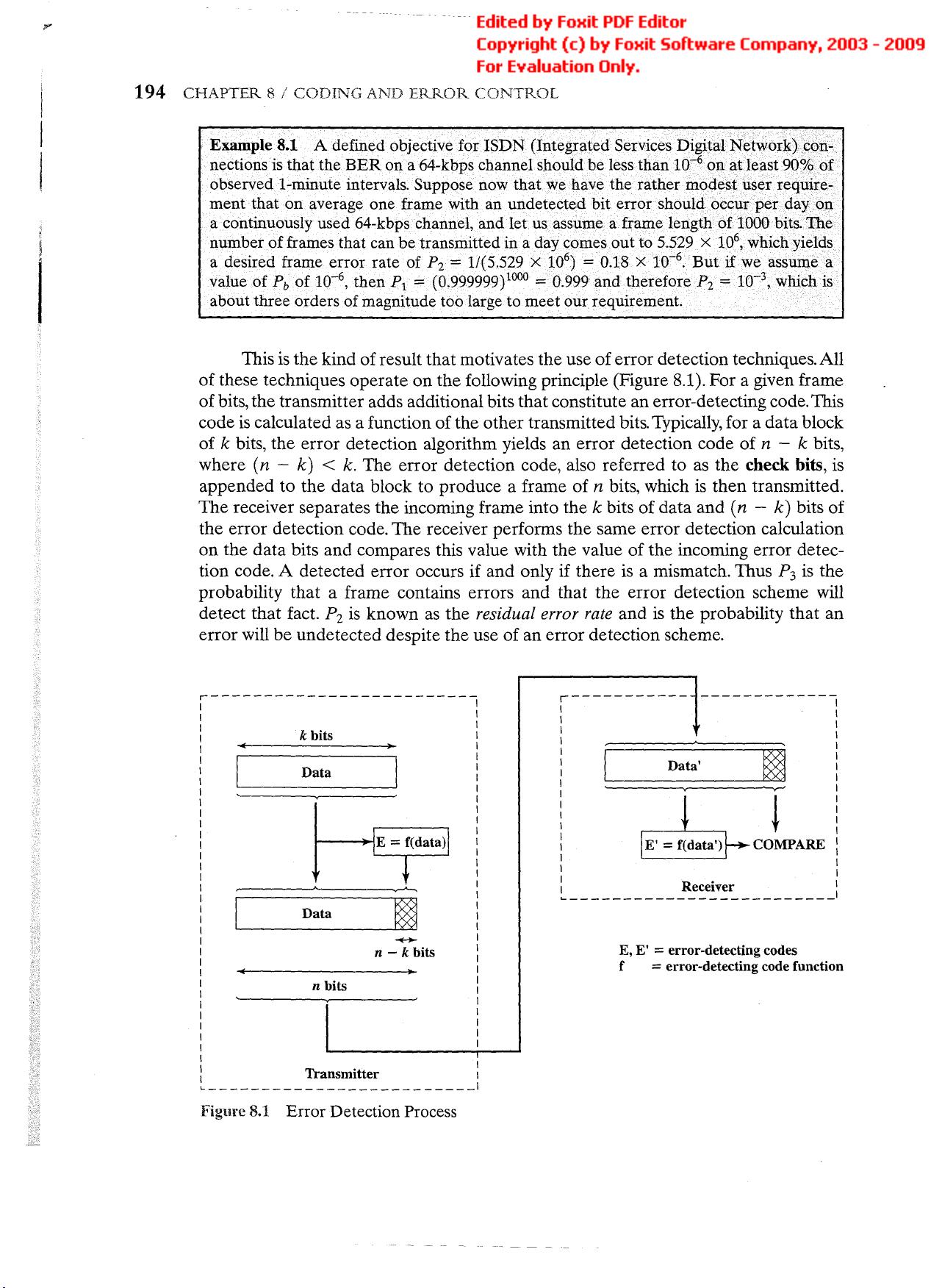
This
is
the kind ofresult that motivates the use oferror detection techniques. All
of these techniques operate
on
the following principle (Figure 8.1). For a given frame
ofbits, the transmitter adds additional bits that constitute an error-detecting code.This
code
is
calculated as a function ofthe other transmitted bits. Typically, for a data block
of
k
bits, the error detection algorithm yields an error detection code of
n -
k
bits,
where
(n -
k)
<
k.
The error detection code, also referred to
as
the check bits,
is
appended to the data block to produce a frame of
n
bits, which
is
then transmitted.
The receiver separates the incoming frame into the
k
bits of data and
(n -
k)
bits of
the error detection code. The receiver performs the same error detection calculation
on the
data
bits and compares this value with the value of the incoming error detec-
tion code. A detected error occurs if and only if there
is
a mismatch. Thus
P
3
is
the
probability that a frame contains errors and that the error detection scheme will
detect that fact.
P
z
is
known
as
the
residual error rate
and
is
the probability that an
error will be undetected despite the use of an error detection scheme.
~------------------------I
I I
I I
I
k
bits
I
I
»
I
I I
I
D~
I
I I
I I
I I
I I
I I
I I
I I
I I
I I
I I
I
~
I
i
Data
~
i
I
~
I
I
n -
k
bits
I
I I
I
'"
»1
I
n
bits
I
I I
I I
I I
I I
I I
I I
I I
: Transmitter
I
~-------------------
I
Figure 8.1
Error
Detection Process
r-----------
-------------
I I
I I
I I
I I
!
Data'
I
i
I
.---v-J
I
I
~
I
I I
I I
I I
I
COMPARE
I
I I
I I
I I
~
R!~e~v~~
:
E,
E'
=
error-detecting codes
f
=
error-detecting code function
剩余99页未读,继续阅读
资源评论

 米饭蚊子2015-02-01老师上课参考教材之一,很清晰,要是合在一起就最好了
米饭蚊子2015-02-01老师上课参考教材之一,很清晰,要是合在一起就最好了
luxiaomingag
- 粉丝: 0
- 资源: 7
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
