没有合适的资源?快使用搜索试试~ 我知道了~
Windows内核劫持不是一个选项MemoryRanger再次出手相救_Windows Kernel Hijacking Is
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 82 浏览量
2022-01-19
13:25:21
上传
评论
收藏 424KB PDF 举报
温馨提示

试读
29页
Windows内核劫持不是一个选项MemoryRanger再次出手相救_Windows Kernel Hijacking Is Not an Option MemoryRanger Comes to the Rescue Again.pdf
资源推荐
资源详情
资源评论

WINDOWS KERNEL HIJACKING IS NOT AN OPTION:
MEMORYRANGER COMES TO THE RESCUE AGAIN
Igor Korkin, PhD
Independent Researcher
Moscow, Russian Federation
igor.korkin@gmail.com
ABSTRACT
The security of a computer system depends on OS kernel protection. It is
crucial to reveal and inspect new attacks on kernel data, as these are used by
hackers. The purpose of this paper is to continue research into attacks on
dynamically allocated data in the Windows OS kernel and demonstrate the
capacity of MemoryRanger to prevent these attacks. This paper discusses three
new hijacking attacks on kernel data, which are based on bypassing OS security
mechanisms. The first two hijacking attacks result in illegal access to files open in
exclusive access. The third attack escalates process privileges, without applying
token swapping. Although Windows security experts have issued new protection
features, access attempts to the dynamically allocated data in the kernel are not
fully controlled. MemoryRanger hypervisor is designed to fill this security gap.
The updated MemoryRanger prevents these new attacks as well as supporting the
Windows 10 1903 x64.
Keywords: hypervisor-based protection, Windows kernel, hijacking attacks
on memory, memory isolation, Kernel Data Protection.
1. INTRODUCTION
The security of users’ data and
applications depends on the security of
the OS kernel code and data. Modern
operating systems include millions of
lines of code, which makes it
impossible to reveal and remediate all
vulnerabilities. Attackers can exploit
the OS vulnerabilities to perform
malicious actions. Windows OS kernel
remains one of the most desired targets
for hackers.
Another big challenge of OS
kernel protection is the third-party
kernel-mode drivers, which execute at
the same high privilege level as the OS
kernel, and they also include a variety
of vulnerabilities. Researchers
consider that “kernel modules (drivers)
introduce additional attack surface, as
they have full access to the kernel’s
address space” (Yitbarek and Austin,
2019).
At the recent DEF CON hacking
conference researchers from
Eclypsium released a list of more than
40 drivers from Microsoft-certified
hardware vendors, which are prone to
privilege escalation attacks (Jesse and
Shkatov, 2019).

Another vulnerability in a signed
third-party driver was presented at the
Blue Hat IL conference by security
experts from the Microsoft Defender
ATP Research Team. The vulnerable
driver uses a watchdog mechanism
based on user APC injection, which
can also be exploited by attackers to
bypass driver signature enforcement
and gain escalated privileges.
(Rapaport, 2019).
Recently revealed Banking trojan
“Banload”, which targets bank
customers in Brazil and Thailand,
applied a malicious kernel-mode
component to fight with anti-malware
and banking protection programs. This
digitally signed malware driver is
designed “to remove software drivers
and executables belonging to anti-
malware and banking protection
programs”, such as AVG, Avast, IBM
Trusteer Rapport (Bisson, 2019;
Kremez, 2019).
Kernel-mode drivers were also
used during the recent RobbinHood
ransomware attack. Hackers installed a
legitimate driver and exploited its
vulnerability to temporarily disable the
Windows OS driver signature
enforcement. Finally, they installed a
malicious kernel driver (Cimpanu,
2020).
Notorious cryptocurrency mining
malware also applies kernel-mode
rootkits to prevent them from being
terminated. Windows-based crypto
miner infected more than 50000
servers from 90 countries (Harpaz and
Goldberg, 2019; O'Donnell, 2019).
The Microsoft Security team do
their best to maintain a high level of
OS kernel protection by issuing
various security features, for example,
Microsoft Kernel Patch Protection
(KPP) aka PatchGuard etc. At the
same, time security researchers and
rootkit developers are discovering
different techniques to bypass
PatchGuard. The most notable of them
was GhostHook, which abused the
Intel Processor Trace (PT) feature to
overcome PatchGuard and patch the
kernel. Cimpanu (2019) underlines that
two recently published bypassing
techniques InfinityHook and ByePg
“establish a permanent foothold in the
kernel itself and open the door for the
return of rootkits on Windows 10”.
We can see that on the one hand,
all drivers and the OS kernel share the
same memory space, and on the other
hand, there are no built-in mechanisms
to restrict access to the kernel memory.
All drivers have full access to the
system and can be used by attackers.
Windows security features provide
limited kernel memory protection.
Threat model
Let us assume that using various
approaches, intruders are able to
execute malicious kernel code. This
paper analyses two types of attacks on
kernel data, which result in the
following, see Figure 1:
• gaining access to the files open
in an exclusive mode (Handle
Hijacking and Hijacking NTFS
data structures);
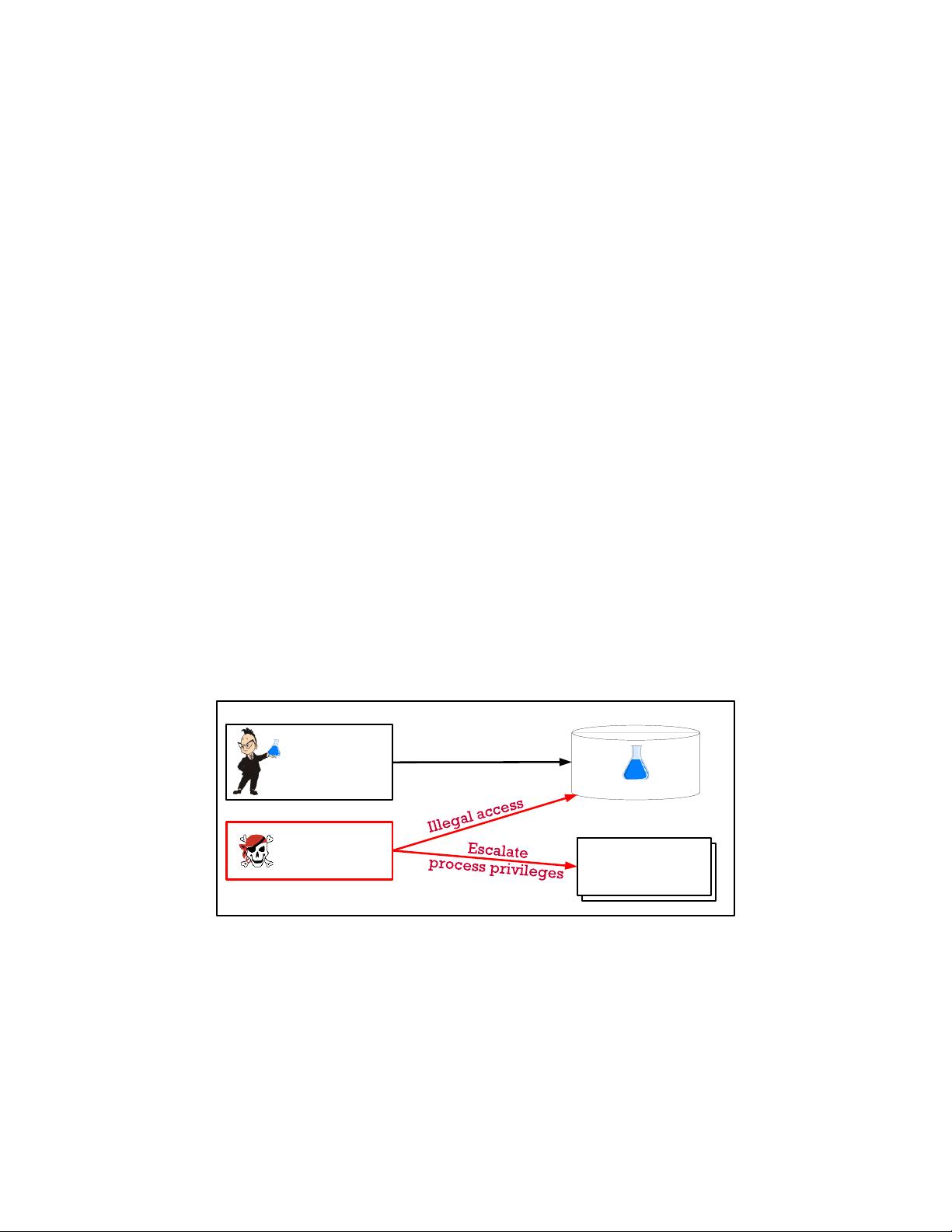
• escalating process privileges
without using the token
swapping technique (Token
Hijacking).
For the attacks on files, a legal
driver creates a file via ZwCreateFile
with zero flag ShareAccess, which
gives the caller exclusive access to the
open file. While the file remains
opened all attempts to gain access to
this file via ZwCreateFile are in vain.
Windows OS detects this illegal access
and returns a status sharing violation
code (0xC0000043), which indicates
that “a file cannot be opened because
the share access flags are
incompatible” (Microsoft, 2019).
This research reveals two different
attacks, which bypass Windows
security features and successfully gain
unauthorized access to the files opened
without shared access by patching OS
internal data structures, related to the
Object Manager and NTFS driver
components.
The third attack escalates process
privileges by patching the static and
the variable portions of _TOKEN
structure, without using token
swapping or token stealing techniques.
This type of attack is mapped to
MITRE ATT&CK (2020) under
Access Token Manipulation. The type
of escalation privilege attack based on
SeImpersonatePrivilege function is out
of the scope of this paper (Bisht,
2020).
All newly proposed attacks are
working transparently on Windows 10
1903 64 bit as well as for its security
features, such as Patch Guard, Device
Guard, and Security Reference
Monitor.
Figure 1. The following attacks will be considered: attacks on files and a privilege
escalation attack.
OS structures
Secret Formula
OS process
structures
Researcher s
Driver
Attacker s
Driver
Open file without
sharing access

To prevent all these attacks on
Windows OS kernel data the updated
MemoryRanger hypervisor will be
presented.
MemoryRanger prevents attacks
on files by running newly loaded
drivers in separated kernel spaces as
well as restricting access to the
corresponding sensitive memory areas.
The newest key feature of
MemoryRanger allows it to run a
special data enclave for sensitive OS
kernel data, such as _TOKEN
structures. This enclave includes these
sensitive OS structures, OS kernel
core, and a limited number of OS
kernel built-in drivers. This new
scheme prevents illegal access from all
drivers whether loaded before and after
MemoryRanger.
The remainder of the paper is as
follows.
Section 2 provides the details of
the control flow and corresponding
internal data structures involved during
file operations in kernel mode. Two
examples of hijacking attacks on files
will be given.
Section 3 presents the details of
access control issues in the Windows
OS kernel and shows how attackers
can hijack the corresponding structure
in order to escalate the process
privileges.
Section 4 contains the details of
adapting MemoryRanger to prevent
these attacks.
Section 5 and Section 6 focus on
the main conclusions and further
research directions respectively.
2. TWO HIJACKING ATTACKS
ON THE FILES OPENED
WITHOUT SHARED ACCESS
This section describes the
internals of file operations in the
Windows OS kernel: data structures
and correlations between them. Two
given hijacking attacks make it
possible to illegally read and overwrite
the content of the file opened in an
exclusive mode. These two hijacking
attacks are based on modifying the OS
internal data structures involved in file
operations.
2.1. Control Flow and Internal Data
Structures Involved in Read and
Write File Operations
Windows OS provides four main
kernel API routines to create,
read/write, and close files:
ZwCreateFile, ZwReadFile,
ZwWriteFile, ZwClose.
During file operations, several OS
kernel components are involved
(Russinovich, Solomon, and Ionescu,
2012; Tanenbaum and Bos, 2014).
Each time a driver calls ZwCreateFile
the control goes to the following OS
kernel subsystems: I/O manager,
Object Manager, Security Reference
Monitor, NTFS driver, and finally, the
control goes to the low-level drivers,
such as Disk Filter Driver and Disk
Class Driver. These are in charge of
access to the physical disk.

The key features revealed by
Korkin (2019) are that Security
Reference Monitor checks access
rights to the file for ZwCreateFile
routine, while routines ZwReadFile,
ZwWriteFile are uncontrolled by the
Security Reference Monitor.
Once a file is created via calling
ZwCreateFile, the OS creates a file
handle, adds an entry to the Handle
Table, allocates file object, NTFS data,
and other structures. The created file
handle is returned to the caller and is
used as a key to read and write the
open file using functions ZwReadFile
and ZwWriteFile.
The details of the control flow and
internal data structures involved in
read and write file operations are given
in Figure 2. Using a file handle, the OS
traverses through the handle table to
acquire the file object. By reading file
object fields the OS locates control
block structures (NTFS data
structures) and moves to them. Disk
drivers access the opened file on a disk
by using NTFS data structures.
OS kernel treats read and write
file access by traversing through these
structures without any checks by
Security Reference Monitor.
This vulnerability can be used to
gain full illegal access to the files
opened without shared access. To
achieve it, intruders can create a file
hijacker and patch any of the
structures, see Figure 2.
As a result, all intruders’ access
attempts using the file hijacker handle
will be redirected by the OS to the
secret file, see Figure 3. This is the key
point of all hijacking attacks on files.
Intruders can modify the
following data to change the control
flow, the corresponding attacks are in
brackets:
• handle table entries (Handle
Table Hijacking);
• file object (Hijacking
FILE_OBJECT);
• NTFS data structures
(Hijacking NTFS structures).
A File Object Hijacking attack
was presented by Korkin (2019).
The next two subsections will
describe the details of Handle
Hijacking and Hijacking NTFS
structures.
剩余28页未读,继续阅读
资源评论


易小侠
- 粉丝: 6453
- 资源: 9万+
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
