没有合适的资源?快使用搜索试试~ 我知道了~
AZ-801微软MCP ET.pdf
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 79 浏览量
2024-04-29
10:47:36
上传
评论
收藏 19.83MB PDF 举报
温馨提示

试读
172页
必备的助力资源
资源推荐
资源详情
资源评论
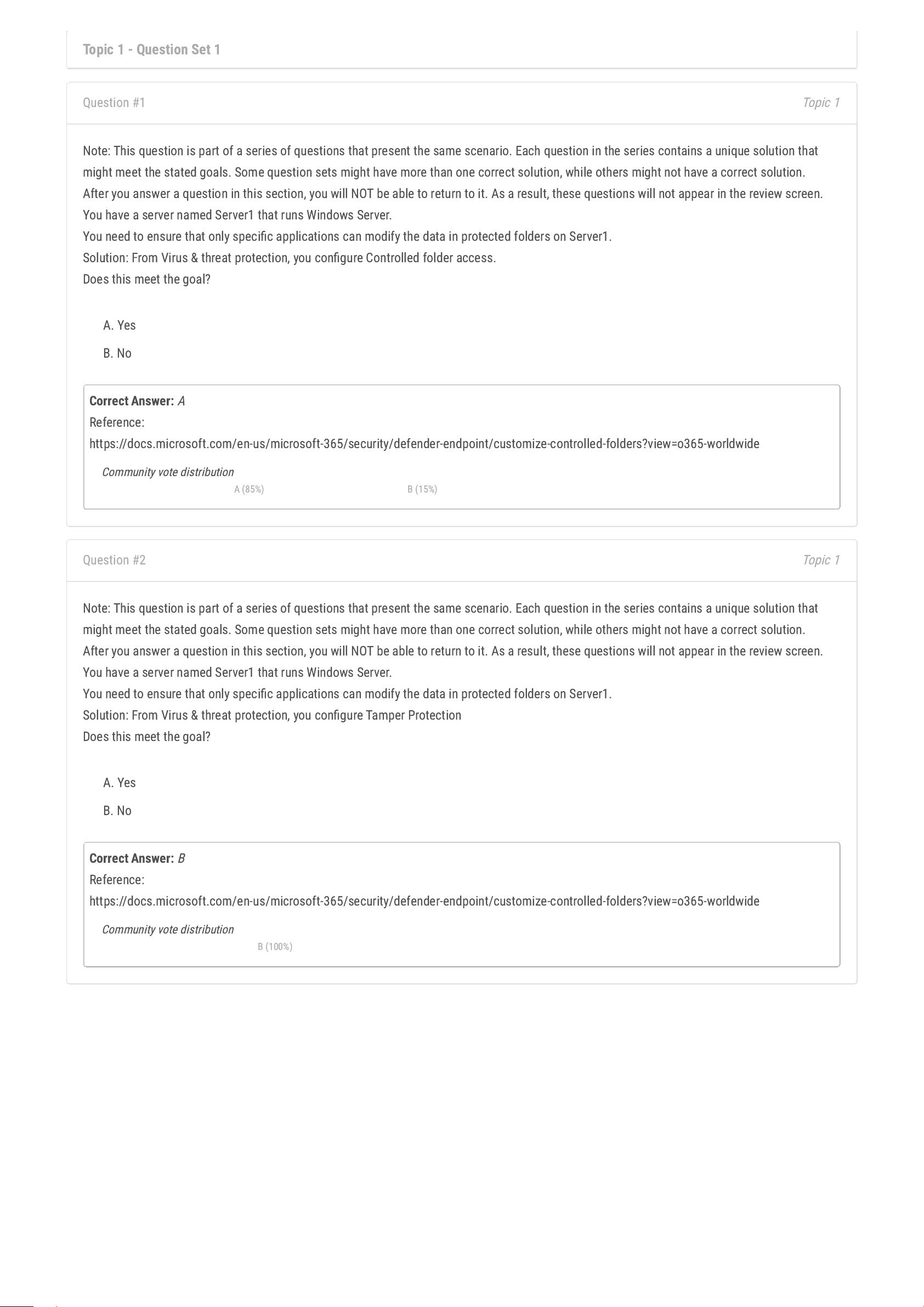
Topic 1 - Question Set 1
Topic 1
Question #1
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that
might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specic applications can modify the data in protected folders on Server1.
Solution: From Virus & threat protection, you congure Controlled folder access.
Does this meet the goal?
A. Yes
B. No
Correct Answer:
A
Reference:
https://docs.microsoft.com/en-us/microsoft-365/security/defender-endpoint/customize-controlled-folders?view=o365-worldwide
Community vote distribution
A (85%) B (15%)
Topic 1
Question #2
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that
might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specic applications can modify the data in protected folders on Server1.
Solution: From Virus & threat protection, you congure Tamper Protection
Does this meet the goal?
A. Yes
B. No
Correct Answer:
B
Reference:
https://docs.microsoft.com/en-us/microsoft-365/security/defender-endpoint/customize-controlled-folders?view=o365-worldwide
Community vote distribution
B (100%)
Topic 1
Question #3
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that
might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a server named Server1 that runs Windows Server.
You need to ensure that only specic applications can modify the data in protected folders on Server1.
Solution: From App & browser control, you congure the Exploit protection settings.
Does this meet the goal?
A. Yes
B. No
Correct Answer:
B
Reference:
https://docs.microsoft.com/en-us/microsoft-365/security/defender-endpoint/customize-controlled-folders?view=o365-worldwide
Community vote distribution
B (100%)
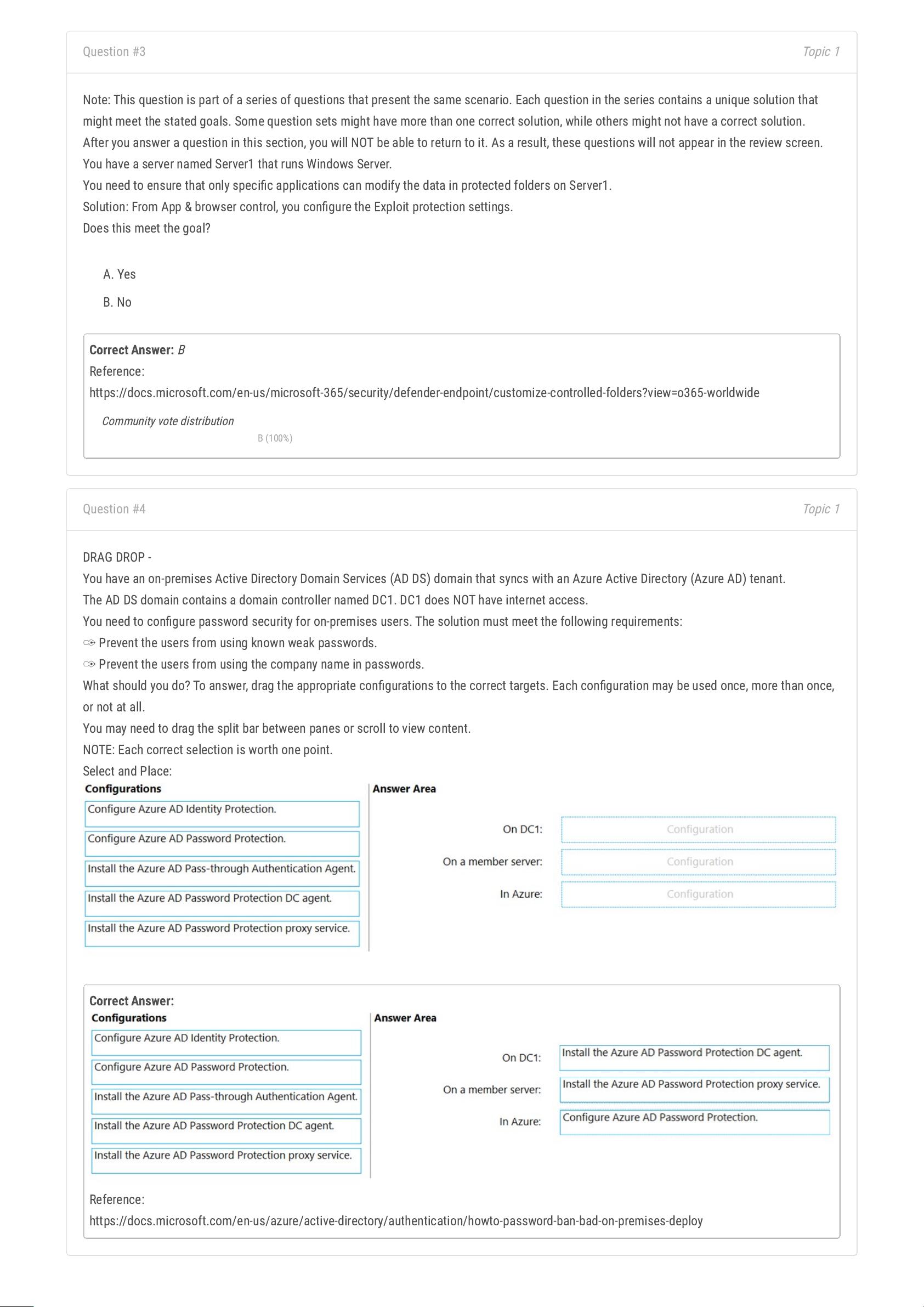
Topic 1
Question #4
DRAG DROP -
You have an on-premises Active Directory Domain Services (AD DS) domain that syncs with an Azure Active Directory (Azure AD) tenant.
The AD DS domain contains a domain controller named DC1. DC1 does NOT have internet access.
You need to congure password security for on-premises users. The solution must meet the following requirements:
✑
Prevent the users from using known weak passwords.
✑
Prevent the users from using the company name in passwords.
What should you do? To answer, drag the appropriate congurations to the correct targets. Each conguration may be used once, more than once,
or not at all.
You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place:
Correct Answer:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-password-ban-bad-on-premises-deploy
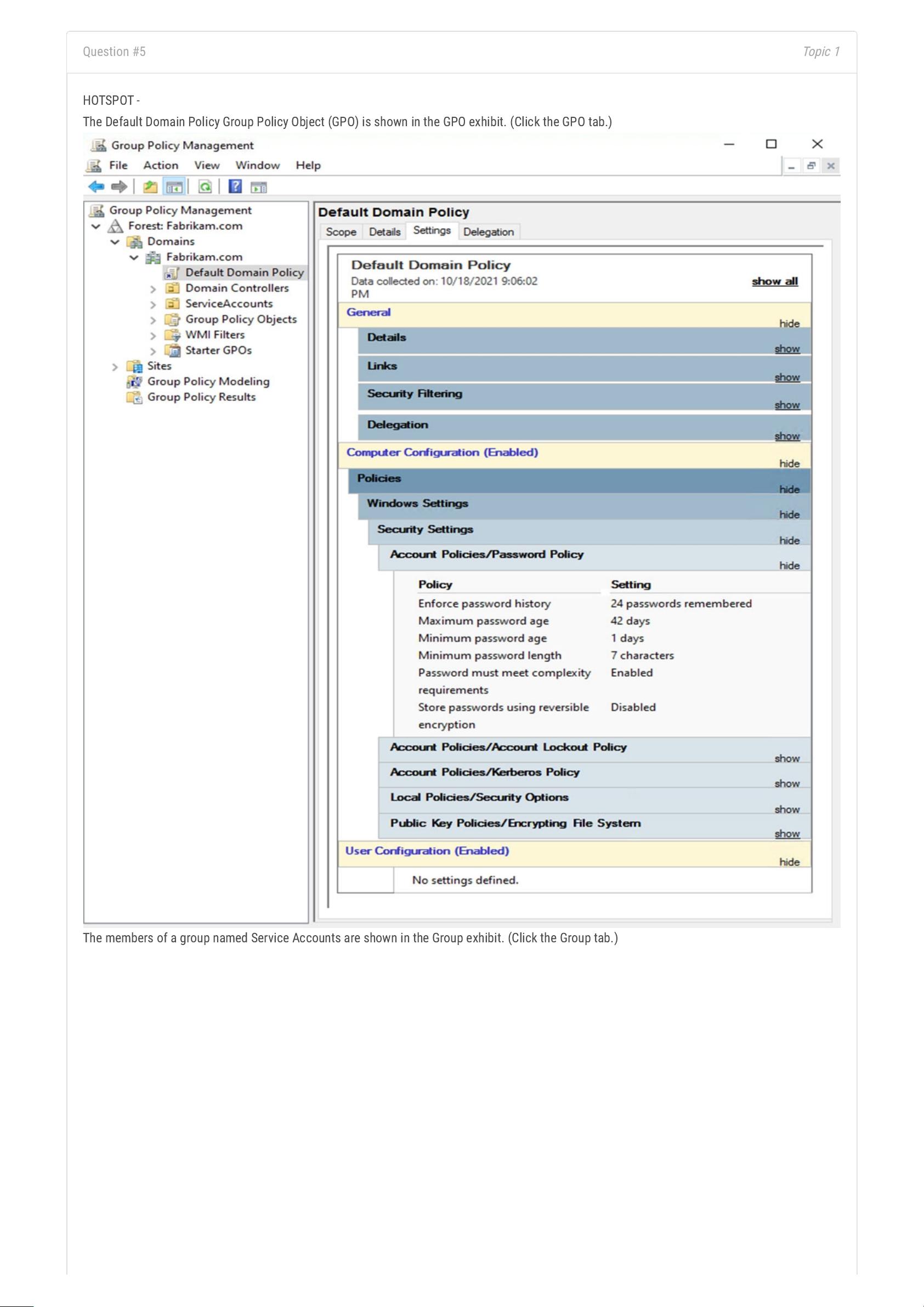
Topic 1
Question #5
HOTSPOT -
The Default Domain Policy Group Policy Object (GPO) is shown in the GPO exhibit. (Click the GPO tab.)
The members of a group named Service Accounts are shown in the Group exhibit. (Click the Group tab.)
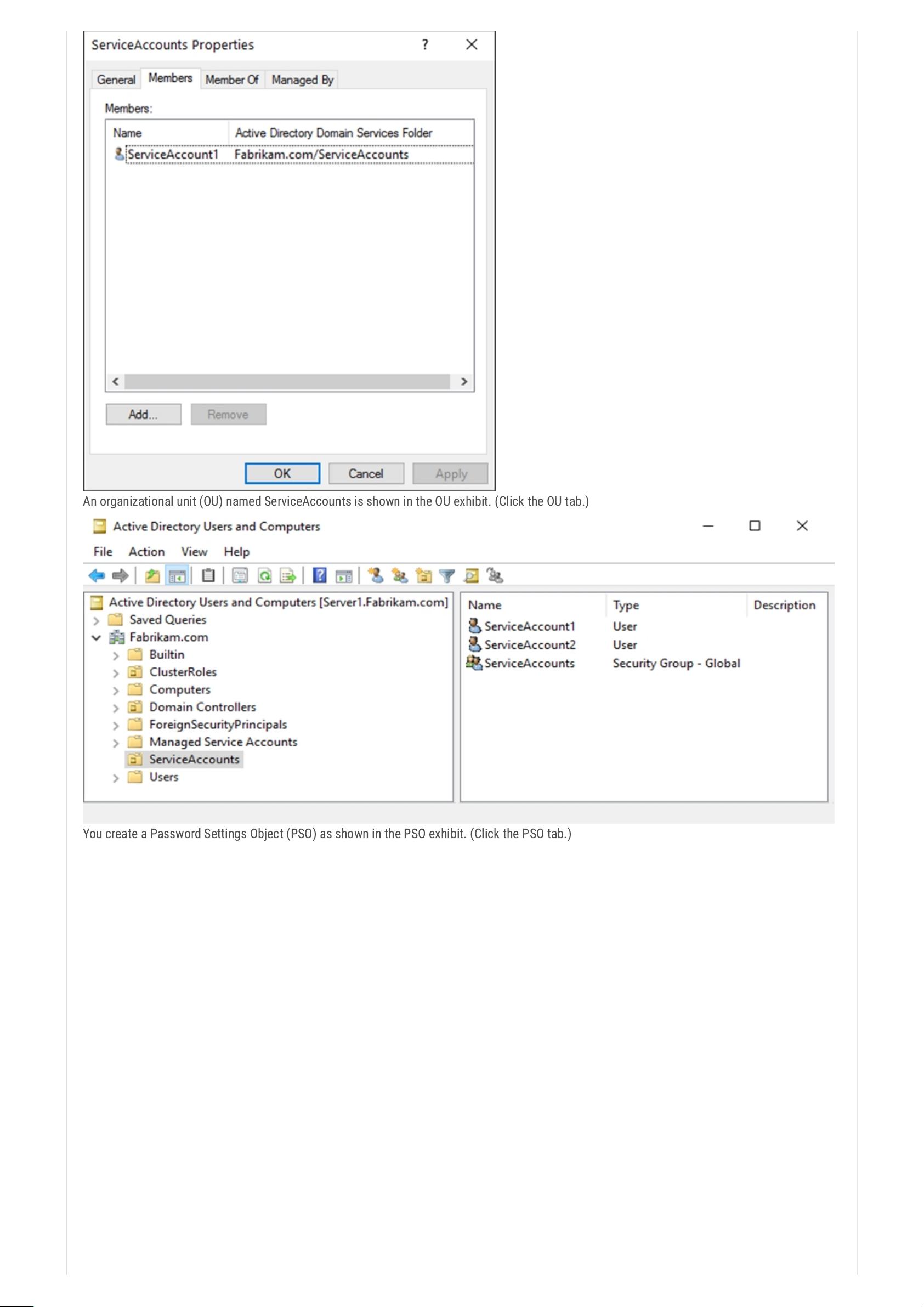
An organizational unit (OU) named ServiceAccounts is shown in the OU exhibit. (Click the OU tab.)
You create a Password Settings Object (PSO) as shown in the PSO exhibit. (Click the PSO tab.)
剩余171页未读,继续阅读
资源评论

xueyunshengling
- 粉丝: 183
- 资源: 511
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

