没有合适的资源?快使用搜索试试~ 我知道了~
SC-100微软MCP ET.pdf
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 22 浏览量
2024-04-29
10:46:10
上传
评论
收藏 18.91MB PDF 举报
温馨提示

试读
210页
必备的助力资源
资源推荐
资源详情
资源评论
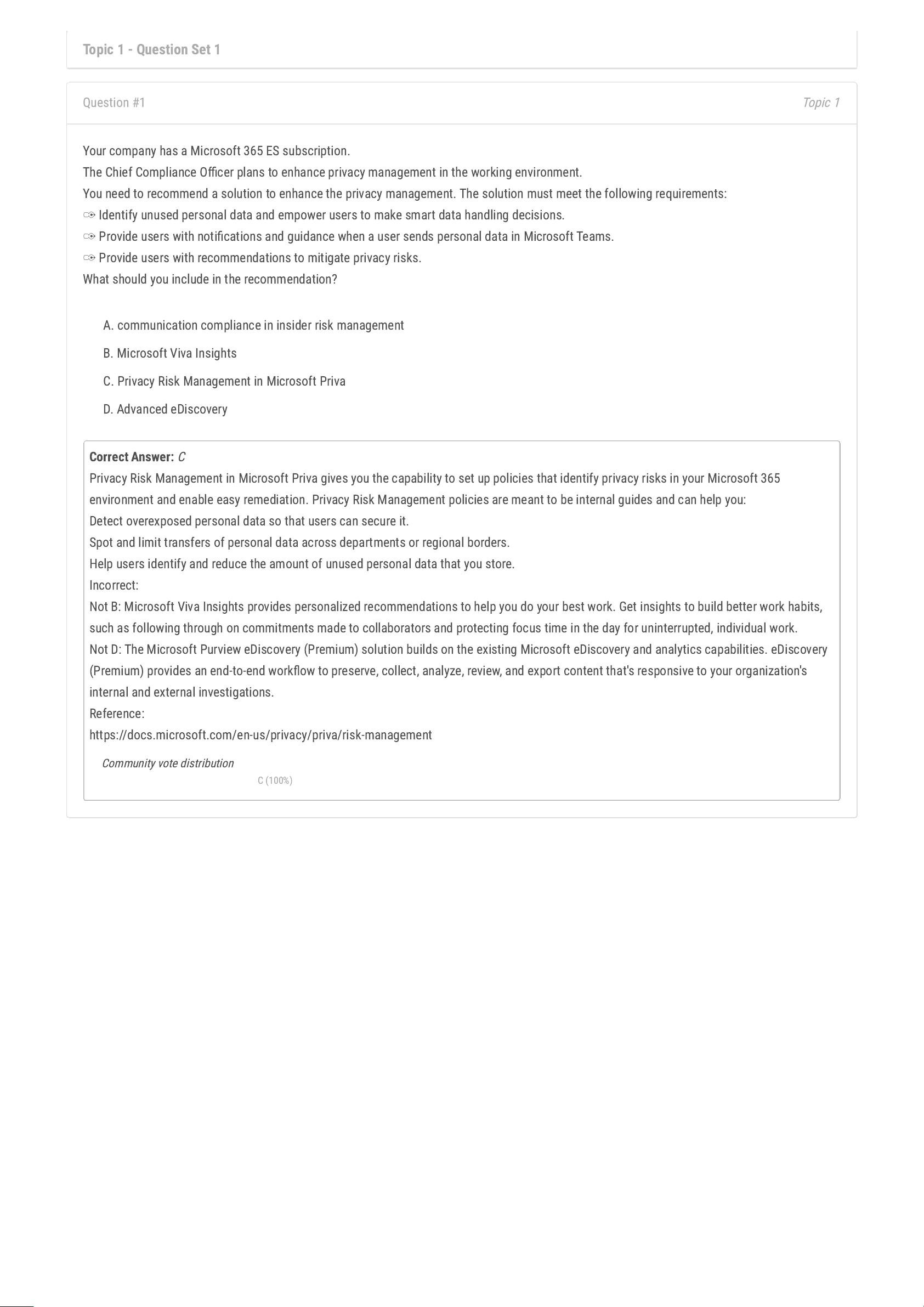
Topic 1 - Question Set 1
Topic 1
Question #1
Your company has a Microsoft 365 ES subscription.
The Chief Compliance Ocer plans to enhance privacy management in the working environment.
You need to recommend a solution to enhance the privacy management. The solution must meet the following requirements:
✑
Identify unused personal data and empower users to make smart data handling decisions.
✑
Provide users with notications and guidance when a user sends personal data in Microsoft Teams.
✑
Provide users with recommendations to mitigate privacy risks.
What should you include in the recommendation?
A. communication compliance in insider risk management
B. Microsoft Viva Insights
C. Privacy Risk Management in Microsoft Priva
D. Advanced eDiscovery
Correct Answer:
C
Privacy Risk Management in Microsoft Priva gives you the capability to set up policies that identify privacy risks in your Microsoft 365
environment and enable easy remediation. Privacy Risk Management policies are meant to be internal guides and can help you:
Detect overexposed personal data so that users can secure it.
Spot and limit transfers of personal data across departments or regional borders.
Help users identify and reduce the amount of unused personal data that you store.
Incorrect:
Not B: Microsoft Viva Insights provides personalized recommendations to help you do your best work. Get insights to build better work habits,
such as following through on commitments made to collaborators and protecting focus time in the day for uninterrupted, individual work.
Not D: The Microsoft Purview eDiscovery (Premium) solution builds on the existing Microsoft eDiscovery and analytics capabilities. eDiscovery
(Premium) provides an end-to-end workow to preserve, collect, analyze, review, and export content that's responsive to your organization's
internal and external investigations.
Reference:
https://docs.microsoft.com/en-us/privacy/priva/risk-management
Community vote distribution
C (100%)
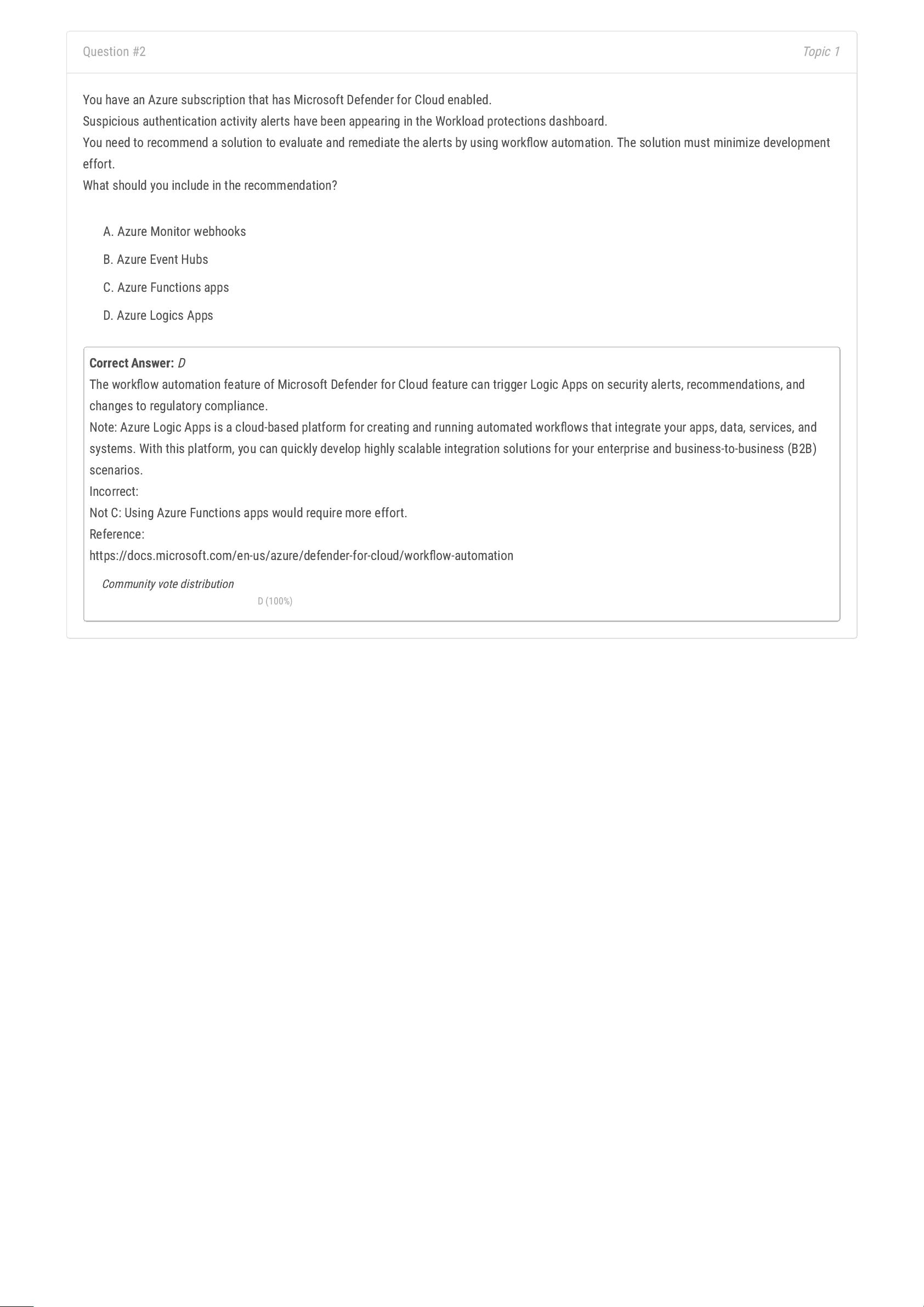
Topic 1
Question #2
You have an Azure subscription that has Microsoft Defender for Cloud enabled.
Suspicious authentication activity alerts have been appearing in the Workload protections dashboard.
You need to recommend a solution to evaluate and remediate the alerts by using workow automation. The solution must minimize development
effort.
What should you include in the recommendation?
A. Azure Monitor webhooks
B. Azure Event Hubs
C. Azure Functions apps
D. Azure Logics Apps
Correct Answer:
D
The workow automation feature of Microsoft Defender for Cloud feature can trigger Logic Apps on security alerts, recommendations, and
changes to regulatory compliance.
Note: Azure Logic Apps is a cloud-based platform for creating and running automated workows that integrate your apps, data, services, and
systems. With this platform, you can quickly develop highly scalable integration solutions for your enterprise and business-to-business (B2B)
scenarios.
Incorrect:
Not C: Using Azure Functions apps would require more effort.
Reference:
https://docs.microsoft.com/en-us/azure/defender-for-cloud/workow-automation
Community vote distribution
D (100%)
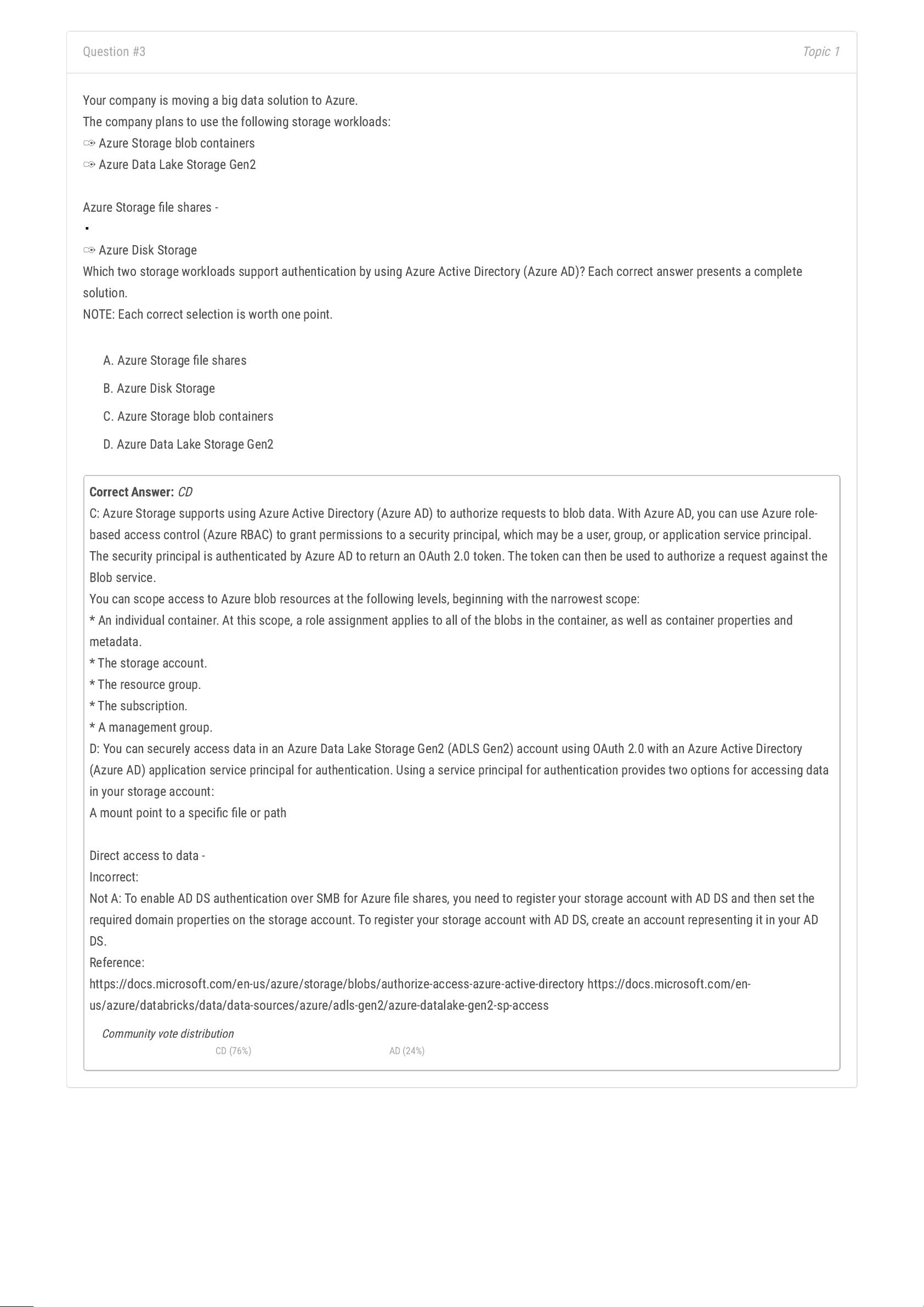
Topic 1
Question #3
Your company is moving a big data solution to Azure.
The company plans to use the following storage workloads:
✑
Azure Storage blob containers
✑
Azure Data Lake Storage Gen2
Azure Storage le shares -
✑
Azure Disk Storage
Which two storage workloads support authentication by using Azure Active Directory (Azure AD)? Each correct answer presents a complete
solution.
NOTE: Each correct selection is worth one point.
A. Azure Storage le shares
B. Azure Disk Storage
C. Azure Storage blob containers
D. Azure Data Lake Storage Gen2
Correct Answer:
CD
C: Azure Storage supports using Azure Active Directory (Azure AD) to authorize requests to blob data. With Azure AD, you can use Azure role-
based access control (Azure RBAC) to grant permissions to a security principal, which may be a user, group, or application service principal.
The security principal is authenticated by Azure AD to return an OAuth 2.0 token. The token can then be used to authorize a request against the
Blob service.
You can scope access to Azure blob resources at the following levels, beginning with the narrowest scope:
* An individual container. At this scope, a role assignment applies to all of the blobs in the container, as well as container properties and
metadata.
* The storage account.
* The resource group.
* The subscription.
* A management group.
D: You can securely access data in an Azure Data Lake Storage Gen2 (ADLS Gen2) account using OAuth 2.0 with an Azure Active Directory
(Azure AD) application service principal for authentication. Using a service principal for authentication provides two options for accessing data
in your storage account:
A mount point to a specic le or path
Direct access to data -
Incorrect:
Not A: To enable AD DS authentication over SMB for Azure le shares, you need to register your storage account with AD DS and then set the
required domain properties on the storage account. To register your storage account with AD DS, create an account representing it in your AD
DS.
Reference:
https://docs.microsoft.com/en-us/azure/storage/blobs/authorize-access-azure-active-directory https://docs.microsoft.com/en-
us/azure/databricks/data/data-sources/azure/adls-gen2/azure-datalake-gen2-sp-access
Community vote distribution
CD (76%) AD (24%)
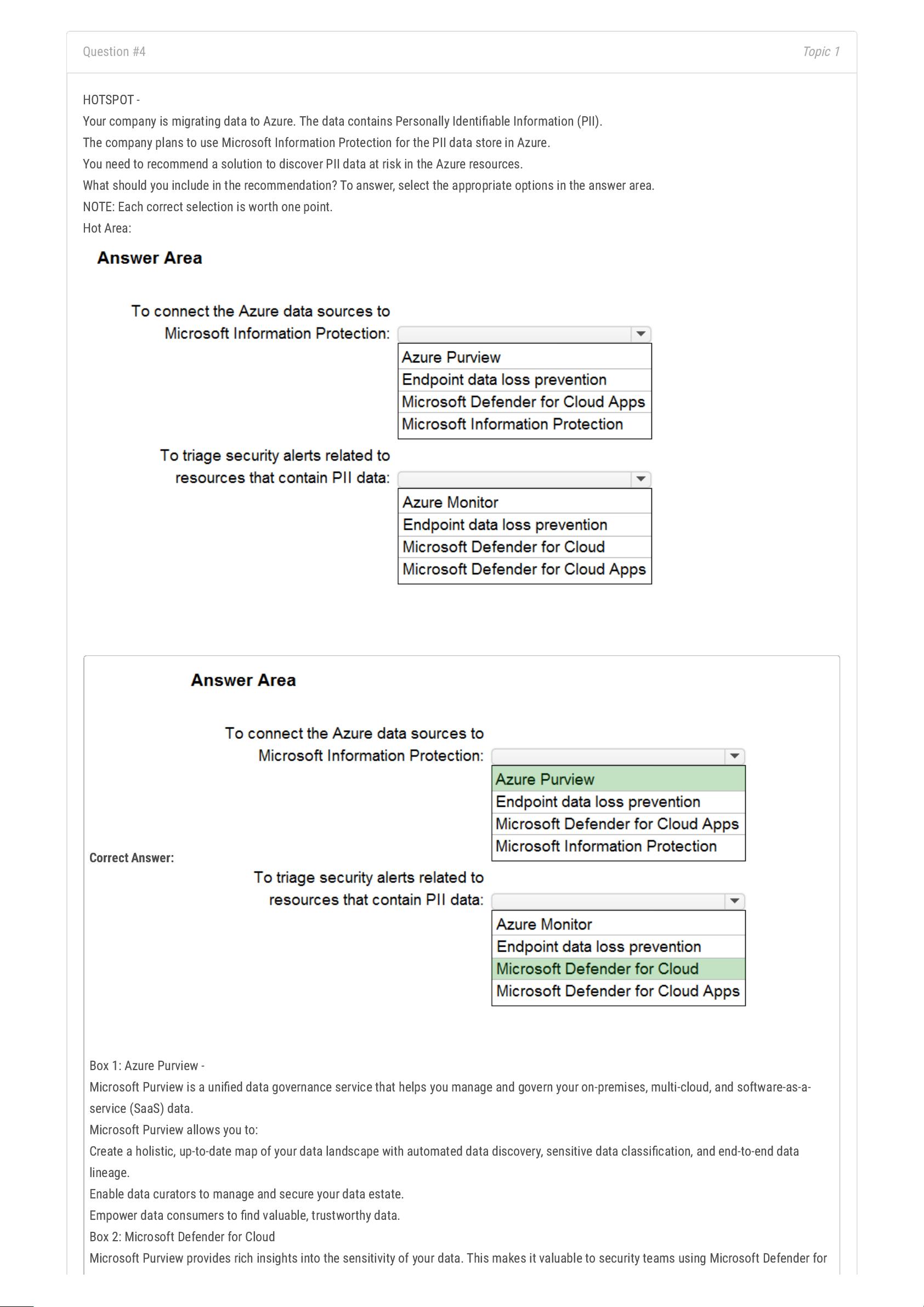
Topic 1
Question #4
HOTSPOT -
Your company is migrating data to Azure. The data contains Personally Identiable Information (PII).
The company plans to use Microsoft Information Protection for the PII data store in Azure.
You need to recommend a solution to discover PII data at risk in the Azure resources.
What should you include in the recommendation? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
Correct Answer:
Box 1: Azure Purview -
Microsoft Purview is a unied data governance service that helps you manage and govern your on-premises, multi-cloud, and software-as-a-
service (SaaS) data.
Microsoft Purview allows you to:
Create a holistic, up-to-date map of your data landscape with automated data discovery, sensitive data classication, and end-to-end data
lineage.
Enable data curators to manage and secure your data estate.
Empower data consumers to nd valuable, trustworthy data.
Box 2: Microsoft Defender for Cloud
Microsoft Purview provides rich insights into the sensitivity of your data. This makes it valuable to security teams using Microsoft Defender for
剩余209页未读,继续阅读
资源评论

xueyunshengling
- 粉丝: 183
- 资源: 511
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

