没有合适的资源?快使用搜索试试~ 我知道了~
Keep Your Data Secure with the New Advanced Encryption Standard
温馨提示

试读
14页
数据加密经典文献 The Advanced Encryption Standard (AES) is a National Institute of Standards and Technology specification for the encryption of electronic data. It is expected to become the accepted means of encrypting digital information, including financial, telecommunications, and government data. This article presents an overview of AES and explains the algorithms it uses. Included is a complete C# implementation and examples of encrypting .NET data. After reading this article you will be able to encrypt data using AES, test AES-based software, and use AES encryption in your systems.
资源推荐
资源详情
资源评论
Encrypt It
Keep Your Data Secure with the New Advanced Encryption
Standard
James McCaffrey
This article assumes you're familiar with C# and bit manipulation
Level of Difficulty 1 2 3
Download the code for this article: AES.exe
(143KB)
SUMMARY The Advanced Encryption Standard (AES) is a National Institute of Standards and Technology
specification for the encryption of electronic data. It is expected to become the accepted means of encrypting
digital information, including financial, telecommunications, and government data. This article presents an overview
of AES and explains the algorithms it uses. Included is a complete C# implementation and examples of
encrypting .NET data. After reading this article you will be able to encrypt data using AES, test AES-based software,
and use AES encryption in your systems.
he National Institute of Standards and Technology (NIST) established the new Advanced Encryption
Standard (AES) specification on May 26, 2002. In this article I will provide a working implementation of
AES written in C#, and a complete explanation of exactly what AES is and how the code works. I'll show
you how to encrypt data using AES and extend the code given here to develop a commercial-quality AES
class. I'll also explain how and why to incorporate AES encryption into your software systems, and how to
test AES-based software.
Note that the code presented in this article and any other implementation based on this article is subject to
applicable Federal cryptographic module export controls (see Commercial Encryption Export Controls
for the exact
regulations).
AES is a new cryptographic algorithm that can be used to protect electronic data. Specifically, AES is an iterative,
symmetric-key block cipher that can use keys of 128, 192, and 256 bits, and encrypts and decrypts data in blocks
of 128 bits (16 bytes). Unlike public-key ciphers, which use a pair of keys, symmetric-key ciphers use the same ke
y
to encrypt and decrypt data. Encrypted data returned by block ciphers have the same number of bits that the input
data had. Iterative ciphers use a loop structure that repeatedly performs permutations and substitutions of the
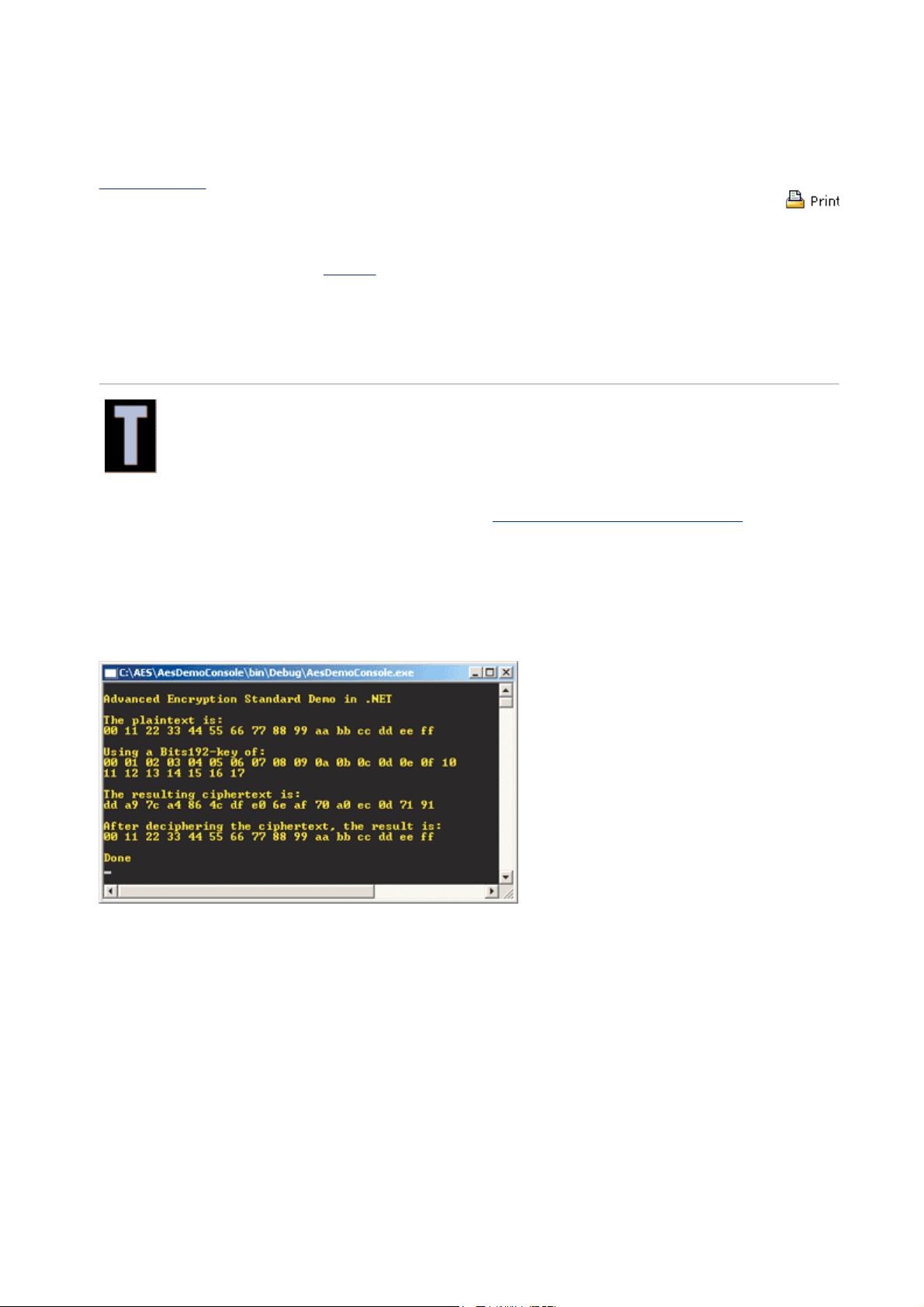
input data. Figure 1 shows AES in action encrypting and then decrypting a 16-byte block of data using a 192-bit
key.
Figure 1 Some Data
AES is the successor to the older Data Encryption Standard (DES). DES was approved as a Federal standard in
1977 and remained viable until 1998 when a combination of advances in hardware, software, and cryptanalysis
theory allowed a DES-encrypted message to be decrypted in 56 hours. Since that time numerous other successful
attacks on DES-encrypted data have been made and DES is now considered past its useful lifetime.
In late 1999, the Rijndael (pronounced "rain doll") algorithm, created by researchers Joan Daemen and Vincent
Rijmen, was selected by the NIST as the proposal that best met the design criteria of security, implementation
efficiency, versatility, and simplicity. Although the terms AES and Rijndael are sometimes used interchangeably,
they are distinct. AES is widely expected to become the de facto standard for encrypting all forms of electronic data
including data used in commercial applications such as banking and financial transactions, telecommunications, and
private and Federal information.
Overview of the AES Algorithm
The AES algorithm is based on permutations and substitutions. Permutations are rearrangements of data, and
substitutions replace one unit of data with another. AES performs permutations and substitutions using several
different techniques. To illustrate these techniques, let's walk through a concrete example of AES encryption using
the data shown in Figure 1.
The following is the 128-bit value that you will encrypt with the indexes array:
Pa
g
e 1 of 14Encr
yp
t It: Kee
p
Your Data Secure with the New Advanced Encr
yp
tion Standar
d
23-10-2003htt
p
://msdn.microsoft.com/msdnma
g
/issues/03/11/AES/
p
rint.as
p
00 11 22 33 44 55 66 77 88 99 aa bb cc dd ee ff
0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15
The 192-bit key value is:
00 01 02 03 04 05 06 07 08 09 0a 0b 0c 0d 0e 0f 10 11 12 13 14 15 16 17
0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23
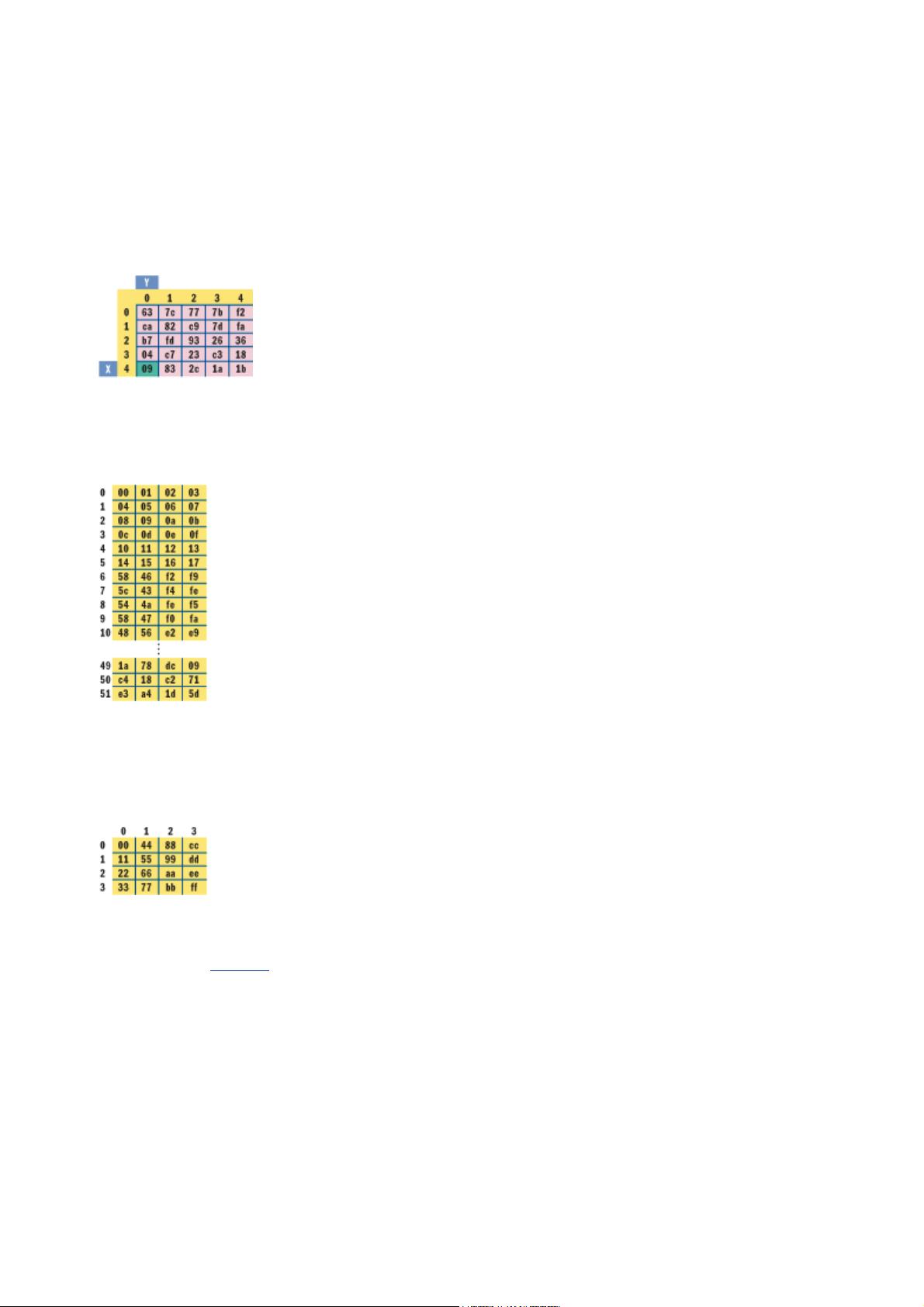
Figure 2 Sbox
When the AES constructor is called, two tables that will be used by the encryption method are initialized. The first
table is a substitution box named Sbox. It is a 16 × 16 matrix. The first five rows and columns of Sbox are shown
in Figure 2. Behind the scenes, the encryption routine takes the key array and uses it to generate a "key schedule"
table named w[], shown in Figure 3.
Figure 3 Key Sched.
The first Nk (6) rows of w[] are seeded with the original key value (0x00 through 0x17) and the remaining rows
are generated from the seed key. The variable Nk represents the size of the seed key in 32-bit words. You'll see
exactly how w[] is generated later when I examine the AES implementation. The point is that there are now many
keys to use instead of just one. These new keys are called the round keys to distinguish them from the original
seed key.
Figure 4 State
The AES encryption routine begins by copying the 16-byte input array into a 4×4 byte matrix named State (see
Figure 4). The AES encryption algorithm is named Cipher and operates on State[] and can be described in
pseudocode (see Figure 5
).
The encryption algorithm performs a preliminary processing step that's called AddRoundKey in the specification.
AddRoundKey performs a byte-by-byte XOR operation on the State matrix using the first four rows of the key
schedule, and XORs input State[r,c] with round keys table w[c,r].
For example, if the first row of the State matrix holds the bytes { 00, 44, 88, cc }, and the first column of the key
schedule is { 00, 04, 08, 0c }, then the new value of State[0,2] is the result of XORing State[0,2] (0x88) with w
[2,0] (0x08), or 0x80:
1 0 0 0 1 0 0 0
0 0 0 0 1 0 0 0 XOR
1 0 0 0 0 0 0 0
The main loop of the AES encryption algorithm performs four different operations on the State matrix, called
SubBytes, ShiftRows, MixColumns, and AddRoundKey in the specification. The AddRoundKey operation is the same
as the preliminary AddRoundKey except that each time AddRoundKey is called, the next four rows of the key
Pa
g
e 2 of 14Encr
yp
t It: Kee
p
Your Data Secure with the New Advanced Encr
yp
tion Standar
d
23-10-2003htt
p
://msdn.microsoft.com/msdnma
g
/issues/03/11/AES/
p
rint.as
p
schedule are used. The SubBytes routine is a substitution operation that takes each byte in the State matrix and
substitutes a new byte determined by the Sbox table. For example, if the value of State[0,1] is 0x40 and you want
to find its substitute, you take the value at State[0,1] (0x40) and let x equal the left digit (4) and y equal the right
digit (0). Then you use x and y as indexes into the Sbox table to find the substitution value, as shown in Figure 2.
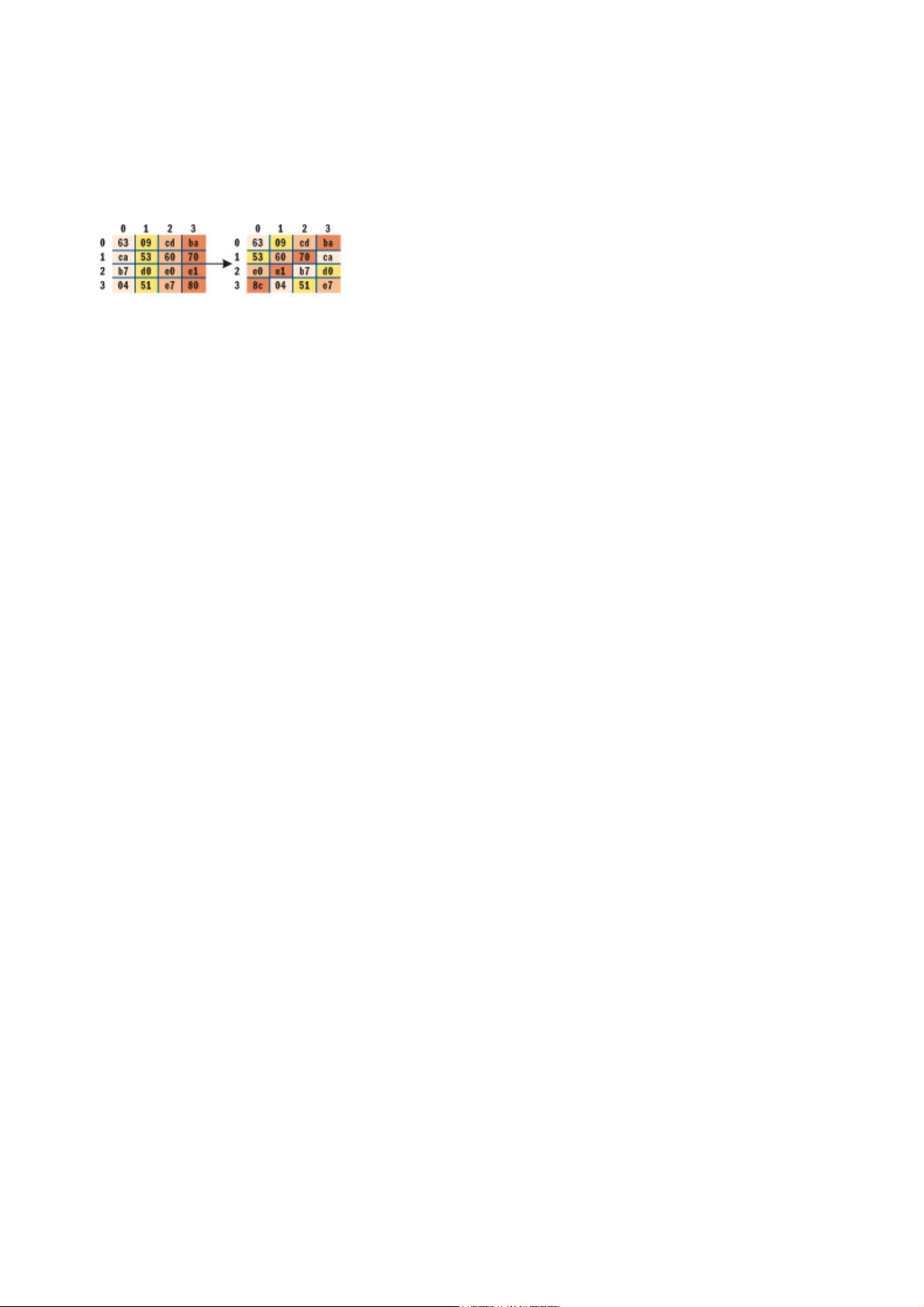
ShiftRows is a permutation operation that rotates bytes in the State matrix to the left. Figure 6 shows how
ShiftRows works on State[]. Row 0 of State is rotated 0 positions to the left, row 1 is rotated 1 position left, row 2
is rotated 2 positions left, and row 3 is rotated 3 positions left.
Figure 6 Running ShiftRows on State
The MixColumns operation is a substitution operation that is the trickiest part of the AES algorithm to understand.
It replaces each byte with the result of mathematical field additions and multiplications of values in the byte's
column. I will explain the details of special field addition and multiplication in the next section.
Suppose the value at State[0,1] is 0x09, and the other values in column 1 are 0x60, 0xe1, and 0x04; then the
new value for State[0,1] is shown in the following:
State[0,1] = (State[0,1] * 0x01) +
(State[1,1] * 0x02) +
(State[2,1] * 0x03) +
(State[3,1] * 0x01)
= (0x09 * 0x01) + (0x60 * 0x02) + (0xe1 * 0x03) +
(0x04 * 0x01)
= 0x57
The addition and multiplication are special mathematical field operations, not the usual addition and multiplication
on integers.
The four operations SubBytes, ShiftRows, MixColumns, and AddRoundKey are called inside a loop that executes N
r
times—the number of rounds for a given key size, less 1. The number of rounds that the encryption algorithm uses
is either 10, 12, or 14 and depends on whether the seed key size is 128, 192, or 256 bits. In this example, because
Nr equals 12, the four operations are called 11 times. After this iteration completes, the encryption algorithm
finishes by calling SubBytes, ShiftRows, and AddRoundKey before copying the State matrix to the output
parameter.
In summary, there are four operations that are at the heart of the AES encryption algorithm. AddRoundKey
substitutes groups of 4 bytes using round keys generated from the seed key value. SubBytes substitutes individual
bytes using a substitution table. ShiftRows permutes groups of 4 bytes by rotating 4-byte rows. MixColumns
substitutes bytes using a combination of both field addition and multiplication.
Field Addition and Multiplication in GF(28)
As you've seen, the AES encryption algorithm uses fairly straightforward techniques for substitution and
permutation, except for the MixColumns routine. The MixColumns routine uses special addition and multiplication.
The addition and multiplication used by AES are based on mathematical field theory. In particular, AES is based on
a field called GF(28).
The GF(28) field consists of a set of 256 values from 0x00 to 0xff, plus addition and multiplication, hence the
(28). GF stands for Galois Field, named after the mathematician who founded field theory. One of the
characteristics of GF(28) is that the result of an addition or multiplication operation must be in the set {0x00 ...
0xff}. Although the theory of fields is rather deep, the net result for GF(28) addition is simple: GF(28) addition is
just the XOR operation.
Multiplication in GF(28) is trickier, however. As you'll see later in the C# implementation, the AES encryption and
decryption routines need to know how to multiply by only the seven constants 0x01, 0x02, 0x03, 0x09, 0x0b,
0x0d, and 0x0e. So instead of explaining GF(28) multiplication theory in general, I will explain it just for these
seven specific cases.
Multiplication by 0x01 in GF(28) is special; it corresponds to multiplication by 1 in normal arithmetic and works
the same way—any value times 0x01 equals itself.
Now let's look at multiplication by 0x02. As in the case of addition, the theory is deep, but the net result is fairly
simple. If the value being multiplied is less than 0x80, then the result of multiplication is just the value left-shifted
1 bit position. If the value being multiplied is greater than or equal to 0x80, then the result of multiplication is the
value left-shifted 1 bit position XORed with the value 0x1b. This prevents "field overflow" and keeps the product of
the multiplication in range.
Once you've established addition and multiplication by 0x02 in GF(28), you can use them to define multiplication
by any constant. To multiply by 0x03 in GF(28), you can decompose 0x03 as powers of 2 and additions. To multipl
y
an arbitrary byte b by 0x03, observe that 0x03 = 0x02 + 0x01. Thus:
b * 0x03 = b * (0x02 + 0x01)
= (b * 0x02) + (b * 0x01)
This can be done because you know how to multiply by 0x02 and 0x01 and how to perform addition. Similarly, to
Pa
g
e 3 of 14Encr
yp
t It: Kee
p
Your Data Secure with the New Advanced Encr
yp
tion Standar
d
23-10-2003htt
p
://msdn.microsoft.com/msdnma
g
/issues/03/11/AES/
p
rint.as
p
剩余13页未读,继续阅读
资源评论

 草吃兔2012-11-30果然经典,不过貌似不能用作毕设翻译啊,文章真心不错
草吃兔2012-11-30果然经典,不过貌似不能用作毕设翻译啊,文章真心不错 shankugan2013-03-11为什么不能用来毕设翻译?不能因为别人翻译过你就不去翻译了嘛…经典的东西,赞!
shankugan2013-03-11为什么不能用来毕设翻译?不能因为别人翻译过你就不去翻译了嘛…经典的东西,赞!
xlong1
- 粉丝: 2
- 资源: 5
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- 王姿.html
- 51单片机学习(1)-软件keil下载
- 历届(第1-21届)希望杯数学竞赛初一试题及答案(最新整理).doc全国数学邀请赛(264页资料)
- 水滴.psd
- TokenPocket_V2.1.2_release.apk
- Apache-druid-kafka-rce.yaml
- 基于C#的ASP.NET数据库原理及应用技术课程指导平台的开发
- 基于ROS的智能车轨迹跟踪算法的仿真与设计源码运用PID跟踪算法.zip.zip
- Bug Bounty Tip - i春秋Self-XSS变废为宝的奇思妙想
- 1991-2015年全国初中化学竞赛复赛试题汇编(212页)(24年竞赛复赛真题).docx天原杯
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功