天津理工大学考试试卷
2005 ~ 2006 学年度第 2 学期
《计算机网络技术》 期末考试试卷
课程代码: 0600100 试卷编号: 1-A 命题日期: 2006 年 5 月 20 日
答题时限: 120 分钟 考试形式:闭卷笔试
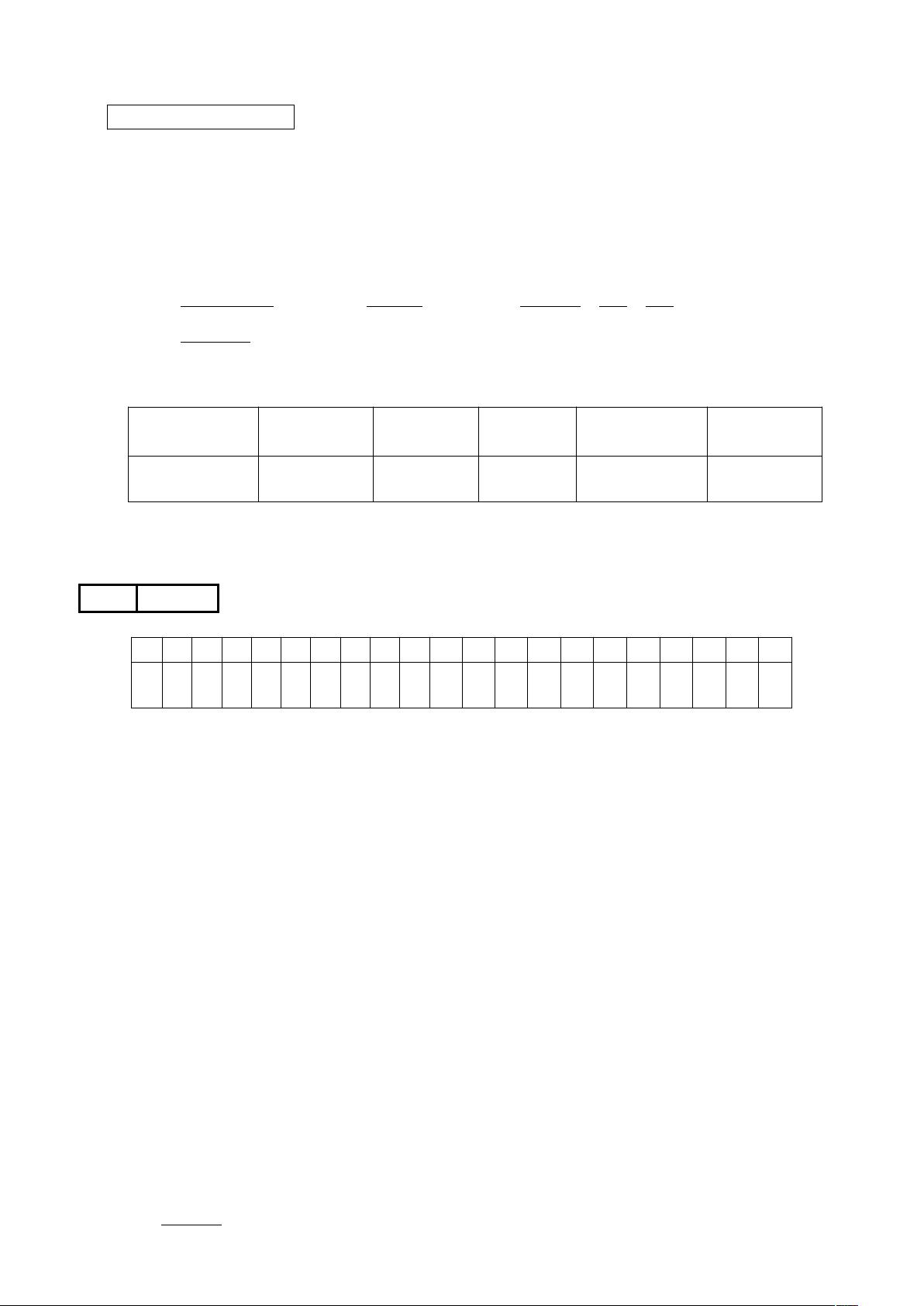
得分统计表:
大题号
总分
一 二 三 四 五
PART Ⅰ: Single Choice (1 point per question – total: 20 points)
Instructions: Select one of the letters beside the choice that is the best answer for each question.
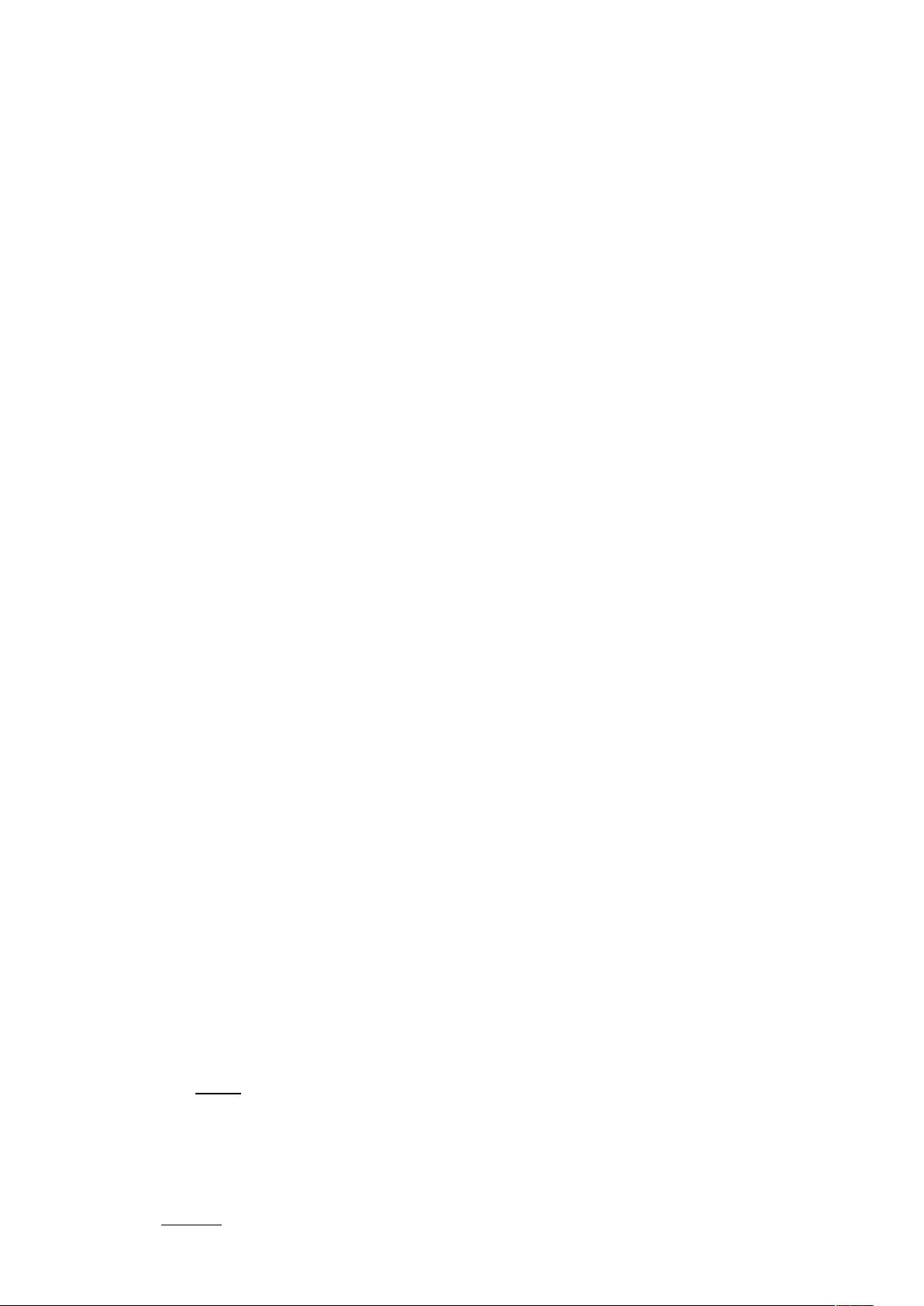
得分
Q 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20
A
1. Which of the following services does the Internet network layer provide for the Internet transport
layer?
a) In-order delivery of data segments between processes
b) Best effort delivery of data segments between communicating hosts
c) Multiplexing and demultiplexing of transport layer segments
d) Congestion control
2. The main task of the Internet’s Domain Name System (DNS) is to:
a) Translate port numbers to IP addresses
b) Specify the standards for Internet domain names
c) Provide an authority for registering domain names
d) Translate mnemonic names to IP addresses
3. RDT3.0’s receiver FSM is same to:
a) RDT1.0 b) RDT2.1 c) RDT2.2 d) RDT2.0
4. The Transmission Control Protocol (TCP) provides which of the following services?
a) End-to-end station addressing
试卷编号: 1-A 第 1 页 共 14 页

b) Application multiplexing
c) Inter network routing
d) Medium access control (MAC)
5. When a destination host transport layer receives data from the network layer, it unambiguously
identifies the appropriate process to pass the data to by using a triplet consisting of:
a) Source port #, destination IP address, and source IP address
b) Destination port #, source port #, process ID#
a) Destination port #, source port #, destination IP address
c) Destination port #, source port #, source IP address
6. Given that the requested information is not available at any intermediate databases, a non-
iterated DNS query from a requesting host would follow the path:
a) Root name server, local name server, authoritative name server
b) Authoritative name server, root name server, host name server
c) Local name server, root name server, local name server, authoritative name server
a) Local name server, root name server, authoritative name server
7. From the list below, select the items found in the TCP segment structure that are not found in
the UDP segment structure:
a) Application Generated Data
b) Destination Port #
c) Source Port #
a) Sequence #
8. Select the four essential steps, briefly described, for terminating a TCP connection between a
client and a server, assuming that the initiating host is the client:
(1) Client sends TCP segment with ACK0 and final sequence number
(2) Client sends TCP segment with FIN =1 and goes into FIN_WAIT state
(3) Server sends TCP segment to ACK the client’s FIN request and enters CLOSE_WAIT
state
(4) Server sends TCP segment with FIN=0
(5) Server sends TCP segment with FIN=1
(6) Client sends TCP segment with to ACK server’s FIN and enters second FIN_WAIT state
(7) Client sends TCP segment with FIN=0
a) 2,3,5,6 b) 5,1,2,3 c) 1,3,5,7 d) 2,3,4,6
9. The RIP routing protocol is based on an algorithm that is:
a) Based on information received only from link “neighbors”
b) A link state algorithm
c) An OSPF algorithm
d) A centralized routing algorithm
试卷编号: 1-A 第 2 页 共 14 页
10. When compensating for link cost changes in the distance vector algorithm, it can generally be
said that:
a) Increased costs are propagated quickly, i.e., “bad news” travels fast
b) Decreased costs are propagated rapidly, i.e., “good news” travels fast
c) Decreased costs do not converge
d) None of the above
11. Two important reasons that the Internet is organized as a hierarchy of networks for the
purposes of routing are:
a) Least cost and maximum free circuit availability
b) Scale and administrative autonomy
c) Message complexity and speed of convergence
d) Link cost changes and link failure
12. With an exterior routing protocol, which of the following issues generally dominates the
routing decisions?
a) Geographical distance between AS’s
b) Policy
c) Number of AS’s traversed
d) Current congestion levels in the AS’s
13. The host component of a CIDR address of the form a.b.c.d/22 can contain addresses for:
a) 2
(32-22)
hosts (minus “special” hosts)
b) 512 hosts (minus “special” hosts)
c) d times 22 hosts
d) 10 hosts (minus “special” hosts)
14. As an IP datagram travels from its source to its destination:
a) the source IP address is changed at each router to identify the sending router
b) the router uses the destination IP address to consult its routing table
c) the router does not use the IP addresses in the datagram
d) the destination IP address is changed at each router to reflect the next hop
15. From the list below, choose the bit pattern which could be a valid generator value for the CRC
code (R) 11010:
a) 1110
b) 011010
c) 100101
试卷编号: 1-A 第 3 页 共 14 页

d) 10011
16. The primary function of the address resolution protocol (ARP) that resides in Internet hosts
and routers is:
a) To provide LAN router functions
b) To translate between LAN addresses and physical interface addresses
c) To translate between IP addresses and LAN addresses
d) To calculate the shortest path between two nodes on a LAN
17. Consider sending a 1300 byte IPv4 datagram into a link that has an MTU of 500 bytes:
a) Three fragments are created.
b) Four fragments are created.
c) Three fragments are created with offsets 0, 500 1000
d) The last fragment consists of exactly 300 bytes of data from the original datagram
18. Suppose one IPv6 router wants to send a datagram to another IPv6 router, but the two are
connected together via an intervening IPv4 router. If the two routers use tunneling, then:
a) The sending IPv6 router creates an IPv4 datagram and puts it in the data field of an IPv6
datagram.
b) The sending IPv6 router creates one or more IPv6 fragments, none of which is larger
than the maximum size of an IPv4 datagram.
c) The sending IPv6 router creates an IPv6 datagram and puts it in the data field of an IPv4
datagram.
d) The sending IPv6 router creates an IPv6 datagram and intervening IPv4 router will reject
the IPv6 datagram
19. Which of the following was an important consideration in the design of IPv6
a) fixed length 40-byte header and specified options to decrease processing time at IPv6
nodes
b) 128-bit addresses to extend the address space
c) different types of service (flows) defined
d) all of the above
20. A network bridge table is used to perform the following:
a) Mapping MAC addresses to bridge port numbers
b) Forwarding frames directly to outbound ports for MAC addresses it handles
c) Filtering (discarding) frames that are not destined for MAC addresses it handles
d) All of the above
PART Ⅱ: True / False (1 points per question – total:15 points)
试卷编号: 1-A 第 4 页 共 14 页

Instructions: Mark the symbol “√” (for True) if the statement is correct, or the symbol “χ” (for
False) if the statement is incorrect.
得分
Q 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15
A
1. The Internet’s Transport Layer protocol provides reliable data transfer between end systems.
2. Networks should be designed such that the Traffic Intensity value for each network node is less
than 1.
3. The maximum size of a single UDP segment is limited to 2
16
–1 bits.
4. FTP uses two separate TCP connections, one to port 20 and one to port 21, and is said to send its
commands “out of band”.
5. During the first step of a TCP connection handshake between a client and a server, the server
receives a TCP segment with a null sequence number and the SYN bit set to 1.
6. TCP congestion control is designed to prevent buffer overflow in network end-systems.
7. Due to the characteristics of its congestion avoidance algorithm, TCP can be said to be a “fair”
protocol with regard to sharing available bandwidth among users of a common transmission link.
8. In the Internet, interior routers in the same autonomous system execute the same routing
algorithm to compute routing paths.
9. All link layer protocols that support IP have the same frame structure (i.e., length of frame,
number and length of header fields).
10. Routers sometimes use transport layer protocols, such as TCP or UDP, to exchange routing
table information with each other.
11. Any node in the IP network defined by 192.118.15.0/24 would be required to have an IP address
of the form 192.118.15.xxx.
12. Pure Aloha is more efficient than Slotted-Aloha.
13. The entries in a bridge table need to be configured by the network administrator.
14. Layer-2 switches can be used to isolate one LAN segment’s collision domain from that of
another LAN segment.
15. The Time Division Multiplexing (TDM) channel partitioning protocol is appealing because it
eliminates collisions and is perfectly fair with regard to bandwidth availability.
PART Ⅲ: Briefly answer each of the following questions. (1 points per question –
total: 20 points)
得分
1. Explain the difference between connection-oriented messaging service and connectionless
试卷编号: 1-A 第 5 页 共 14 页















