没有合适的资源?快使用搜索试试~ 我知道了~
资源详情
资源评论
资源推荐
WHITE PAPER
Linux Kernel Hardening
Taylor Merry
Copyright SANS Institute 2021. Author Retains Full Rights.
This paper was published by SANS Institute. Reposting is not permitted without express written permission.

© SANS Institute 2003, Author retains full rights
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
© SANS Institute 2003, As part of the Information Security Reading Room. Author retains full rights.
Linux Kernel Hardening
Taylor Merry
November 18, 2003
Abstract
While not inherently insecure, the standard Linux kernel lacks advanced features to
prevent or contain certain types of malicious attacks. This paper explores two
approaches to hardening the standard Linux kernel: address space (memory)
protection and advanced access control. Additions to the kernel which place restrictions
on an application's address space make it possible to prevent many types of buffer
overflows attacks. The addition of an access control system can remove many, if not all
of the privileges assigned to the traditional superuser account.
After brief overviews of three methods of address space protection and three advanced
access control systems, this paper outlines the installation and configuration of a
Grsecurity-enhanced kernel. The Grsecurity kernel patch provides both address space
protection and an advanced access control system.
Linux kernel hardening is an effective strategy for preventing many forms of attacks and
providing enhanced host-level security, however the approach described in this paper
should not be expected to prevent all attacks against Linux hosts.
Background
Like any other operating system, application level security flaws leave Linux vulnerable
to a variety of malicious attacks. Over the years, many tools and techniques have been
developed to “harden” Linux hosts in an attempt to mitigate the risk posed by buggy
software. Removing or disabling unnecessary services and daemons, properly
configuring services and changing vendor defaults, applying the appropriate security
and bug patches, setting up backups, and configuring monitoring tools are all essential
steps in building a secure system.
Once an operating system has been set up and placed in production, daily monitoring
of vendor notices and security forums is necessary to ensure that software is kept
current with the latest security issues. Unfortunately, this method of administration is
entirely reactionary and leaves hosts susceptible to compromise before vulnerabilities
are publicly announced and fixes have been distributed. While many systems are
compromised due to lack of proper maintenance (ie. patches not applied when they are
made available), there is a strong need for methods to further reduce the risks
associated with flawed software. Keeping systems up to date with vendor patches will
prevent the casual attacker from gaining access to a system, but will not always keep
out an attacker that is targeting a system.
In today's computing environments, there is an ever increasing number of applications
that require network connections. It is rare to find a machine that can simply be
@ 2021 SANS Institute Author Retains Full Rights
© SANS Institute 2003, Author retains full rights
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
© SANS Institute 2003, As part of the Information Security Reading Room. Author retains full rights.
disconnected from a network in an attempt to prevent it from being compromised.
The Carnegie Mellon University's Computer Emergency Response Team Coordination
Center (CERT/CC) reports a dramatic increase in the number of security incidents
reported in the past 10+ years:
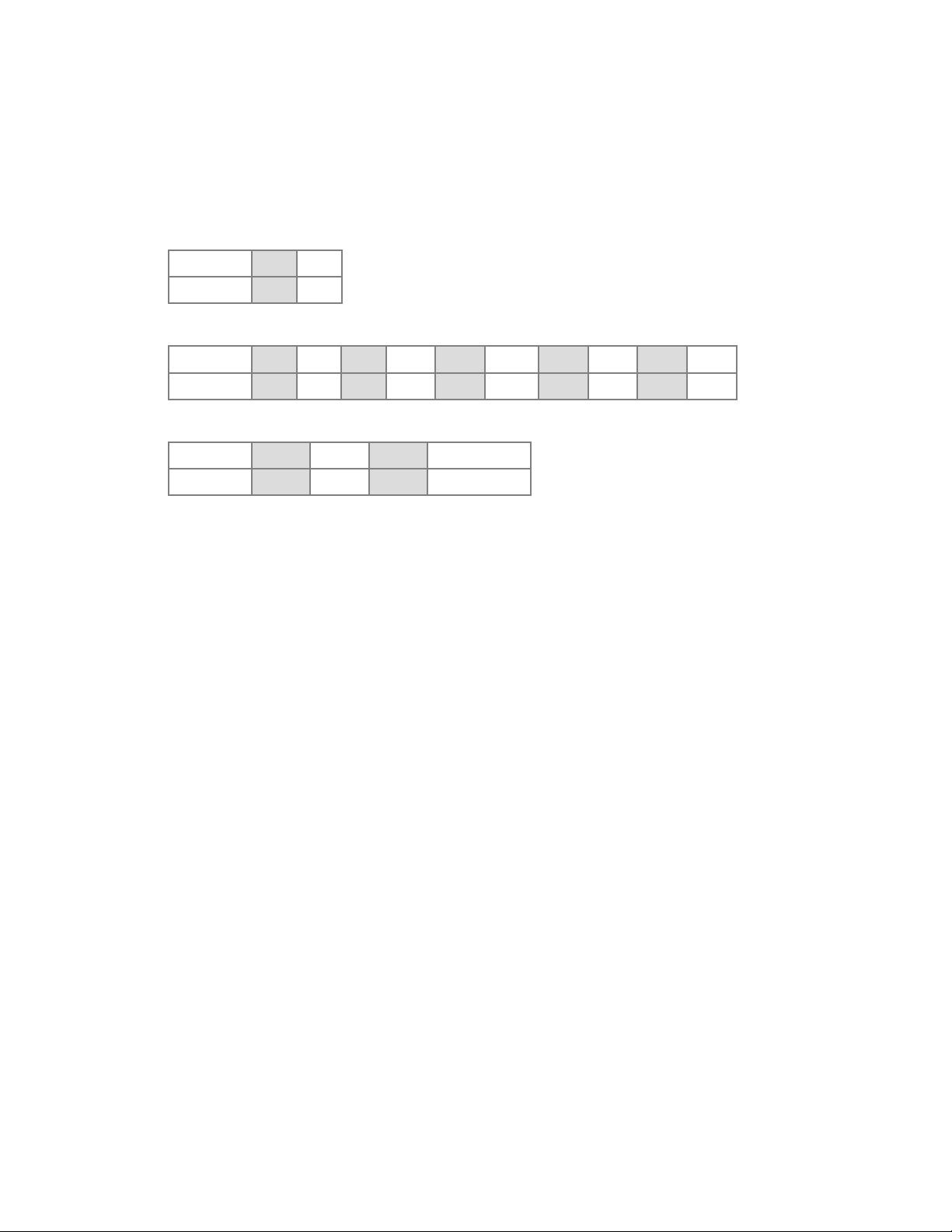
1988-1989
Year 1988 1989
Incidents 6 132
1990-1999
Year 1990 1991 1992 1993 1994 1995 1996 1997 1998 1999
Incidents 252 406 773 1,334 2,340 2,412 2,573 2,134 3,734 9,859
2000-2003
Year 2000 2001 2002 1Q-3Q 2003
Incidents 21,756 52,658 82,094 114,855
Total incidents reported (1988-3Q 2003): 297,318
Please note that an incident may involve one site or hundreds (or even thousands) of sites. Also, some
incidents may involve ongoing activity for long periods of time(1).
While the number of computers connected to the Internet can be directly correlated with
this trend, the number of attacks and the amount of damage incurred will only increase
as more people become dependent on this connectivity. There is a need to reassess
the trade-off made between host-level security and the convenience offered by various
types of services and features if the intent is to keep these hosts connected to the
Internet.
In general, the initial goal of an attacker attempting to gain access to a Linux host (or
any other UNIX variant) is to gain control of the superuser (aka. root) account. The
traditional superuser account has unrestricted access to all components of the system.
In most cases, there is little to no monitoring or auditing of actions taken by the
superuser. Even when configured, an attacker with superuser privileges has the ability
to disable these services, or cover their tracks by modifying log files. Once an attacker
has control of the superuser account, even the most novice attacker will likely install
rootkits and kernel modules that will allow them to continue to use the system for
nefarious purposes without being easily noticed.
Aside from instances where an attacker is able to bypass physical access restrictions,
the ability to gain control of a system is often due to “trusted” programs. A “trusted”
program is one that an administrator allows to run with superuser privileges. This is not
always the fault of the administrator – certain applications do not function correctly
without these privileges. The exploitation of bugs in flawed software can allow an
attacker to gain the privileges of a compromised program. Cowan, et al., (2) outlines
buffer overflows, race conditions and special character processing as the most widely
known application vulnerabilities that allow an attacker to acquire superuser privileges.
@ 2021 SANS Institute Author Retains Full Rights

© SANS Institute 2003, Author retains full rights
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
© SANS Institute 2003, As part of the Information Security Reading Room. Author retains full rights.
• Buffer Overflows
The result of a program failing to properly check the boundaries of user input.
If more data is entered into a memory buffer than it was intended to store, the
data will overwrite data in adjacent buffers potentially giving an attacker
control of the vulnerable application and access to the system privileges
granted to that application.
• Race Conditions
A vulnerability in a program that does not properly check for the previous
existence of a file before writing to it. In some cases, the delay between a
check and the creation of the file may afford an attacker enough time to create
a link to an important system file so that when the application tries to create
the new file, it ends up overwriting or corrupting the other file.
• Special Character Processing
A vulnerability that allows an attacker to insert special characters into URLs
pointing to scripts that process web forms. These character sequences could
allow attackers to execute arbitrary code on the web server. Although most
web servers are configured to run as unprivileged users today, these type of
attacks can allow for unauthorized entry into a system which can be used to
leverage attacks against other flawed applications.
Methods to prevent or mitigate the risk posed by a successful attack are generally
applied on either the application level or the operating system level. A standard way to
mitigate risk on the application level is by granting it the least amount of privilege
required to perform its duties. While most applications do not need to run as a
privileged user, there are some system level applications which require superuser
privileges to perform certain tasks. In the past, many attacks against applications such
as the Apache web server, the Berkeley Internet Name Domain (BIND) server, and the
Sendmail mail server led to full system compromise as they required superuser
privileges to function. In the 2.4 kernel series, enhancements to the kernel capabilities
system makes it possible for applications to execute initially as root and then drop
superuser privileges to run as a regular user. These enhancements are quite beneficial
to overall system security, and today, most Linux distributions configure applications
such as Apache, BIND, and Sendmail to run as unprivileged users by default.
Another tactic adopted to secure certain system level applications is through the use of
the chroot program. chroot makes an application execute inside a special shell with a
new root directory, effectively isolating it from the rest of the system. If an attacker were
able to exploit a vulnerability in an application running in a chroot jail, they would only
have access to this limited root file system containing the essential programs,
configuration files and libraries necessary for the application to operate. Unfortunately,
chroot jails are not exempt from security flaws – in some situations when an application
inside a chroot jail is running as a superuser, there are methods which allow attackers
to break out of the jails.(3)
The millions of lines of source code that comprise the applications used on today's
Linux systems make it nearly impossible to fully audit each application and remove all
potential vulnerabilities. While still a critical component of a defense in-depth strategy,
@ 2021 SANS Institute Author Retains Full Rights

© SANS Institute 2003, Author retains full rights
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46
© SANS Institute 2003, As part of the Information Security Reading Room. Author retains full rights.
hardening techniques at the application level are typically inadequate as a means in
protecting the rest of the system from flaws in the applications. Regardless of the time
spent hardening applications, a vulnerability exploited in one application will often lead
to a full system compromise. As the dependency upon network connectivity increases,
the need to look at lower level methods for preventing successful attacks becomes
apparent.
The Linux Kernel
The lowest software level components of “[e]ach computer system includes a basic set
of programs called the operating system. The most important program in the set is
called the kernel. It is loaded into RAM when the system boots and contains many
critical procedures that are needed for the system to operate.”(4) While the system is
running, the kernel acts as a mediator between the hardware components and the
processes running on the system – none of the processes directly access any hardware
components on their own. At an even lower level, features built into hardware
components help to enforce the separation between those that can (“kernel mode”) and
cannot (“user mode”) directly interact with the hardware components.
The Linux kernel provides for a multiuser operating system. This means that any user
can run any program at any time without worrying about the other users. Due to the
multiuser nature of the system, the kernel is also responsible for providing mechanisms
for user authentication and access control to prevent users or applications from
interfering with the activity of other users or programs. The access control system built
into the standard Linux kernel is based on the traditional Discretionary Access Control
(DAC) model. DAC is discussed in further detail later in this document.
Linux Kernel Modules
At a time when memory (RAM) was an expensive commodity, the idea of a modular
kernel was introduced in a few commercial UNIX distributions which allowed the loading
and unloading of pieces of kernel code to free up memory without having to rebuild the
entire kernel. Although memory is much less expensive today, the flexibility that
loadable kernel modules offer is one of the main reasons that they are still used heavily
today. The Linux kernel is one of the few modern monolithic kernels with the ability to
load and unload modules on the fly. This can prove to be a big time-saver as it prevents
an administrator from having to recompile the whole kernel and then reboot the system
for every minor change.
“Linux was first developed for 32-bit i386-based PCs. These days it also runs on (at
least) the Compaq Alpha AXP, Sun SPARC and UltraSPARC, Motorola 68000,
PowerPC, PowerPC64, ARM, Hitachi SuperH, IBM S/390, MIPS, HP PA-RISC, Intel IA-
64, DEC VAX, AMD x86-64 and CRIS architectures.”(5) Due to the variance in
hardware components between the platforms, many Linux distributions provide stock
kernels that rely heavily on the use of kernel modules. Not only does this approach
greatly assist in the initial setup of a Linux system, but it also allows Linux distributions
to maintain a small number of pre-built kernel images optimized for the various CPU
configurations. While this approach eliminates the need for a custom built kernel on
@ 2021 SANS Institute Author Retains Full Rights
剩余24页未读,继续阅读

内核沉思录
- 粉丝: 1864
- 资源: 19
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功


评论0