没有合适的资源?快使用搜索试试~ 我知道了~
云计算中的区块链安全:用例、挑战和解决方案1
需积分: 0 0 下载量 55 浏览量
2022-08-03
16:22:28
上传
评论
收藏 2.14MB PDF 举报
温馨提示

试读
13页
云计算中的区块链安全:用例、挑战和解决方案1
资源详情
资源评论
资源推荐
symmetry
S
S
Article
Blockchain Security in Cloud Computing: Use Cases,
Challenges, and Solutions
Jin Ho Park
1
and Jong Hyuk Park
2,
*
ID
1
Department of Computer Science, School of Software, SoongSil University, Seoul 06978, Korea;
2
Department of Computer Science and Engineering, Seoul National University of
Science and Technology, (SeoulTech) Seoul 01811, Korea
* Correspondence: [email protected]; Tel.: +82-2-970-6702
Received: 29 June 2017; Accepted: 1 August 2017; Published: 18 August 2017
Abstract:
Blockchain has drawn attention as the next-generation financial technology due to its
security that suits the informatization era. In particular, it provides security through the authentication
of peers that share virtual cash, encryption, and the generation of hash value. According to the
global financial industry, the market for security-based blockchain technology is expected to grow to
about USD 20 billion by 2020. In addition, blockchain can be applied beyond the Internet of Things
(IoT) environment; its applications are expected to expand. Cloud computing has been dramatically
adopted in all IT environments for its efficiency and availability. In this paper, we discuss the concept
of blockchain technology and its hot research trends. In addition, we will study how to adapt
blockchain security to cloud computing and its secure solutions in detail.
Keywords: blockchain; computer security; bitcoin; authentication; cloud computing
1. Introduction
With the need for next-generation financial technology recently increasing, there have been active
studies on blockchain for the secure use of electronic cash by communicating solely between peers
and without the involvement of third parties. A blockchain is the public ledger for transactions and it
prevents hacking during transactions involving virtual cash. As a type of distributed database and
a data record list that continuously grows, it is designed to disable arbitrary tampering by the operator
of distributed peers. Transaction records are encrypted according to a rule and operated in computers
that run the blockchain software. Bitcoin is an electronic currency using blockchain technology [1].
Using blockchain can provide higher security compared to storing all data in a central database.
In the data storage and management aspect, damage from attacks on a database can be prevented.
Moreover, since the blockchain has an openness attribute, it can provide transparency in data when
applied to an area requiring the disclosure of data. Due to such strengths, it can be utilized in diverse
areas including the financial sector and the Internet of Things (IoT) environment and its applications
are expected to expand [2–6].
The blockchain finalizes a transaction record through the work authentication process, when a
person who loans electronic cash forms a block by combining the transactions over the network.
The hash value is then generated by verifying it and connecting the previous block.
This block is
periodically updated and reflected on the electronic cash transaction details to share the latest
transaction detail block. This process provides security for the transaction of electronic cash and
allows the use of a reliable mechanism [7–9].
Cloud computing has been applied to many IT environments due to its efficiency and availability.
Moreover, cloud security and privacy issues have been discussed in terms of important security
elements: confidentiality, integrity, authentication, access control, and so on [10].
Symmetry 2017, 9, 164; doi:10.3390/sym9080164 www.mdpi.com/journal/symmetry

Symmetry 2017, 9, 164 2 of 13
In this paper, we seek to investigate the definition and base technology of blockchain and survey
the trend of studies to date to discuss areas to be studied, considering cloud computing environments.
In addition, we discuss the considerations for blockchain security and secure solutions in detail.
This paper studies the blockchain technology and surveys the blockchain by analyzing generic
technology and research trends and discusses the solution for using bitcoin safely as well as future
study areas. The results of this research can serve as important base data in studying blockchain and
will aid in understanding the known security problems thus far. We can foster the development of
future blockchain technology by understanding the trend of blockchain security.
The rest of this paper is organized as follows. In Section 2, we discuss related works including
the basic concept of blockchain and bitcoin as a use case. Section 3 presents a detailed discussion
and survey on the security considerations for blockchain including the settlement of blockchain, the
security of transaction, the security of wallet, and the security of software. In Section 4, we discuss
blockchain security case studies—authentication, security incidents, and 51% attack—and improve
the blockchain. Section 5 proposes secure solutions for the blockchain in cloud computing in detail.
Finally, we conclude our study in Section 6.
2. Related Works
In this section, we discuss the basic concept of blockchain and the existing research. We also study
the specific use of blockchain in bitcoin.
2.1. Blockchain
A blockchain is the technology that allows all members to keep a ledger containing all transaction
data and to update their ledgers to maintain integrity when there is a new transaction. Since the
advancement of the Internet and encryption technology has made it possible for all members to verify
the reliability of a transaction, the single point of failure arising from the dependency on an authorized
third party has been solved.
The blockchain has broker-free (P2P-based) characteristics, thereby doing away with unnecessary
fees through p2p transactions without authorization by a third party. Since ownership of the transaction
information by many people makes hacking difficult, security expense is saved, transactions are
automatically approved and recorded by mass participation, and promptness is assured. Moreover,
the system can be easily implemented, connected, and expanded using an open source and transaction
records can be openly accessed to make the transactions public and reduce regulatory costs [11].
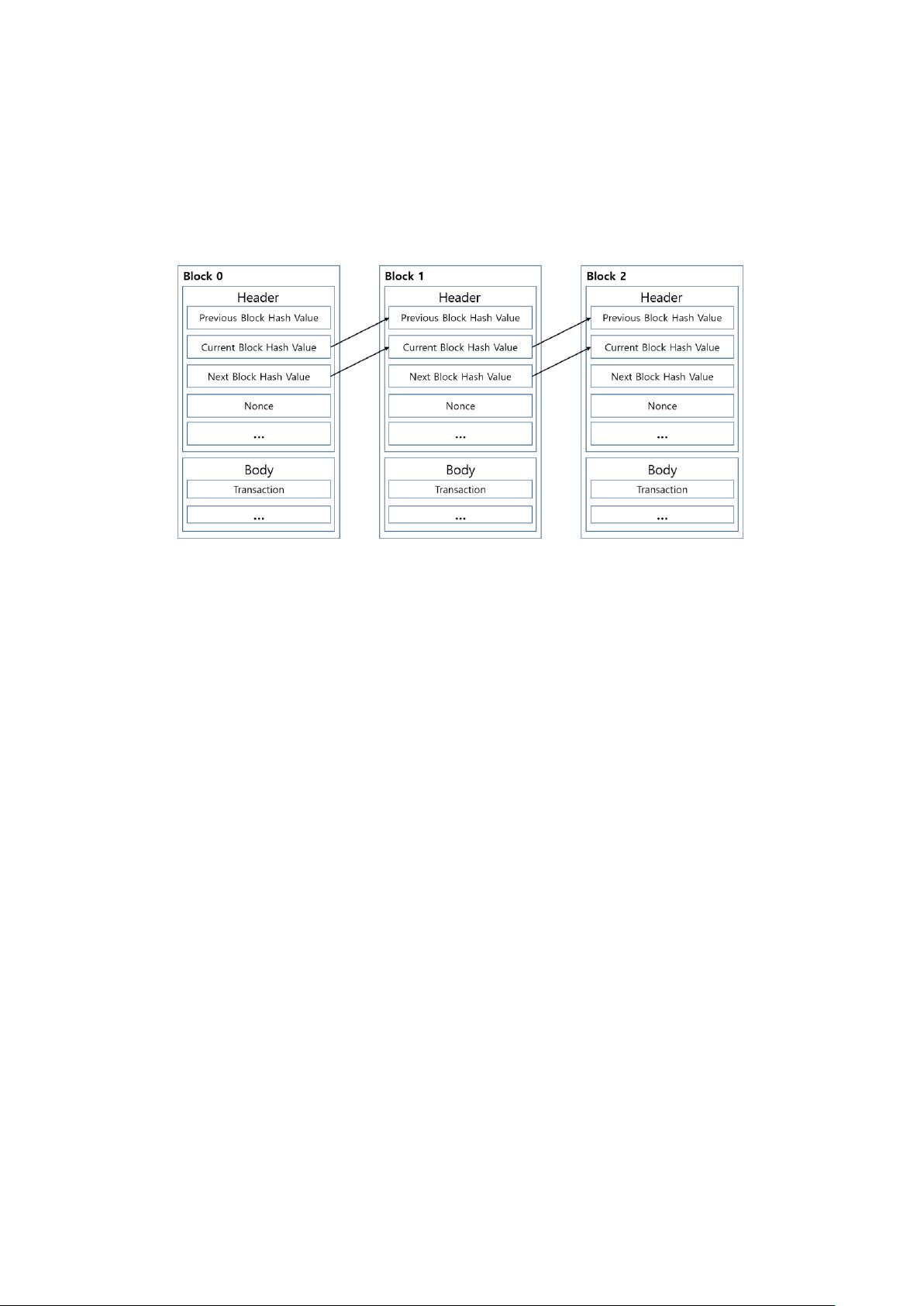
The blockchain is a structured list that saves data in a form similar to a distributed database
and is designed to make arbitrarily manipulating it difficult since the network participants save and
verify the blockchain. Each block is a structure consisting of a header and a body. The header includes
the hash values of the previous and current blocks and nonce. The block data are searched in the
database using the index method. Although the block does not contain the hash value of the next
block, it is added as a practice (Figure 1) [12].
Since the hash values stored in each peer in the block are affected by the values of the previous
blocks, it is very difficult to falsify and alter the registered data. Although data alteration is possible if
51% of peers are hacked at the same time, the attack scenario is realistically very difficult.
Public, key-based verification and a hash function that can be decrypted are both used to provide
security in the blockchain. The ECDSA (Elliptic Curve Digital Signature Algorithm) electronic signature
algorithm, which verifies the digital signature generated during a transaction between individuals,
is used to prove that the transaction data have not been altered.
Although using an anonymous public key as account information enables one to know who sent
how much to another peer, it still ensures anonymity since there is no way of finding information
pertaining to the owner [13–15].
The hash function is used to verify that the block data containing the transaction details are
not altered and to find the nonce value to get a new block, as well as to guarantee the integrity of
Symmetry 2017, 9, 164 3 of 13
transaction data during a bitcoin transaction. The integrity of the transaction details can be verified
through the public key-based encryption of the hash value of the transaction data. Moreover, using
the root hash value, which accumulates the hash value of each of the transaction details, enables easy
determination of whether the bitcoin data were altered since the root hash value is changed when the
value is changed in the process [16,17].
Symmetry 2017, 9, 164 3 of 13
Figure 1. Blockchain connection structure.
The hash function is used to verify that the block data containing the transaction details are not
altered and to find the nonce value to get a new block, as well as to guarantee the integrity of
transaction data during a bitcoin transaction. The integrity of the transaction details can be verified
through the public key-based encryption of the hash value of the transaction data. Moreover, using
the root hash value, which accumulates the hash value of each of the transaction details, enables easy
determination of whether the bitcoin data were altered since the root hash value is changed when the
value is changed in the process [16,17].
There are many ongoing studies to strengthen security using these characteristics of blockchain.
The most important part of the blockchain is security related to the personal key used in encryption
and there are studies on how to protect the personal key. An attacker attempts a “reuse attack” and
other attacks to obtain the personal key stored in a peer’s device in order to hack the bitcoin. The
attacker can hack the bitcoin since the data may be leaked if the attacker can obtain the personal key.
To solve this problem, studies on applying both hardware and software securities for approving
transactions are ongoing [18].
Bitcoin is very vulnerable to infection by malware since it is often traded in widely used devices
such as peers’ PCs or smartphones. The malware penetrating through various paths such as e-mail,
USB, or apps with poor security must be detected and treated since it can infect a peer’s device. The
need for security is growing, particularly in trades of items used in games since many of them use
bitcoins. As such, there have been studies on detecting and treating malware in the game
environment [19].
One of the strengths of bitcoin is that it is difficult to falsify and alter the ledger because so many
peers share the transaction ledger. Since it takes the data recorded in the majority of ledgers, hacking
is practically impossible unless the attacker alters and falsifies 51% of all peers’ ledgers, even if the
data of some ledgers are altered. Still, there are concerns that 51% of the ledgers can be falsified and
altered simultaneously considering increasing computing power and there are studies suggesting the
intermediate verification process or design of the verification process in order to solve the problem.
2.2. Bitcoin
Bitcoin is the digital currency proposed by Satoshi Nakamoto in 2009 to allow transactions
between peers without a central authority or a server to issue and manage the currency. Bitcoins are
traded with the P2P-based distributed databases based on public-key cryptology. Bitcoin is one of
the first implementations of cryptocurrency in 1998 [20].
The bitcoin transaction information is disclosed over the network such that all peers can verify
it and so currency issuance is limited. The peers participating in the network have the same
blockchain and the transaction data are stored in blocks in the same way as the distribution storage
of transaction data. Although there are many threats involved in electronic transactions, bitcoin can
be technically implemented to cope with them. For example, a person attempting to generate a
Figure 1. Blockchain connection structure.
There are many ongoing studies to strengthen security using these characteristics of blockchain.
The most important part of the blockchain is security related to the personal key used in encryption and
there are studies on how to protect the personal key. An attacker attempts a “reuse attack” and other
attacks to obtain the personal key stored in a peer’s device in order to hack the bitcoin. The attacker
can hack the bitcoin since the data may be leaked if the attacker can obtain the personal key. To solve
this problem, studies on applying both hardware and software securities for approving transactions
are ongoing [18].
Bitcoin is very vulnerable to infection by malware since it is often traded in widely used
devices such as peers’ PCs or smartphones. The malware penetrating through various paths such
as e-mail, USB, or apps with poor security must be detected and treated since it can infect a peer’s
device. The need for security is growing, particularly in trades of items used in games since many
of them use bitcoins. As such, there have been studies on detecting and treating malware in the
game environment [19].
One of the strengths of bitcoin is that it is difficult to falsify and alter the ledger because so many
peers share the transaction ledger. Since it takes the data recorded in the majority of ledgers, hacking
is practically impossible unless the attacker alters and falsifies 51% of all peers’ ledgers, even if the
data of some ledgers are altered. Still, there are concerns that 51% of the ledgers can be falsified and
altered simultaneously considering increasing computing power and there are studies suggesting the
intermediate verification process or design of the verification process in order to solve the problem.
2.2. Bitcoin
Bitcoin is the digital currency proposed by Satoshi Nakamoto in 2009 to allow transactions
between peers without a central authority or a server to issue and manage the currency. Bitcoins are
traded with the P2P-based distributed databases based on public-key cryptology. Bitcoin is one of the
first implementations of cryptocurrency in 1998 [20].
The bitcoin transaction information is disclosed over the network such that all peers can verify it
and so currency issuance is limited. The peers participating in the network have the same blockchain
and the transaction data are stored in blocks in the same way as the distribution storage of transaction
剩余12页未读,继续阅读
忧伤的石一
- 粉丝: 25
- 资源: 332
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

评论0