没有合适的资源?快使用搜索试试~ 我知道了~
FlexRay车载网络认证加密安全协议的研究1
需积分: 0 0 下载量 125 浏览量
2022-08-03
14:24:56
上传
评论
收藏 652KB PDF 举报
温馨提示

试读
5页
FlexRay车载网络认证加密安全协议的研究1
资源详情
资源评论
资源推荐
Abstract—Since the appearance of internet of vehicle (IoV),
the in-vehicles network is no longer an isolated system. The
OBD-II hardware, GPS, and the WiFi system could cause
intrusions during communications. There are many unresolved
network security problems yet in in-vehicle bus protocol, like
controller area network (CAN), local area network (LIN), and
FlexRay. In this paper, having considered the vulnerabilities
and a hidden attacking of FlexRay, an authenticated encryption
protocol is designed based on the Advanced Encryption
Standard (AES)-128 and SHA-1 algorithm for FlexRay. We
apply the protocol into a simulated FlexRay bus system which is
build by CAN software environment. The protocol is also
applied in a real Flexray network build by MC9S12XF512
evaluation board The both experimental results show that the
security and reliability of in-vehicle bus system are enhanced.
Index Terms—
FlexRay, in-vehicle bus network, network
reliability, security protocol.
I. INTRODUCTION
In the past tens of years, well developed traditional
in-vehicle bus systems provide basic hardware supports. With
beginning of the internal communication in vehicle, LIN,
CAN, and FlexRay are used in the bus protocol to achieve the
internal communication in vehicle. Based on the technology
of x-by-wire and mechanotronics, the in-vehicle bus system is
the main approach for ECU communications in the future
motoring. In fact, provided convenient service combing with
drivers other products like smart phone or Bluetooth are
always faster than the security upgrade of systems. Thus, there
are new challenging problems to be solved for sustainable
development. One of problems is how to defend attack and
patch the vulnerability on data and physical layers.
Recently, a lot of projects have carried out to improve the
in-vehicle network. In the EVITA project [1], requires of the
in-vehicle network are defined including information safety,
the confidentiality, and concerned infrastructures etc. [2]. The
project managed by Wolf stuff provides several of encryption
algorithms to embed a security block in vehicle respectively
[3]. In 2015, when the malicious APP on the mobile phone
linking to the infortainment system, the security protocol is
protected the system from this attack is by means of sending
the authentication data using the extend ID and CRC field [4].
In 2017, considered of real time transmission, a light weight
authentication protocol is proposed [5].
Manuscript received August 3, 2018; revised October 12, 2018. This
work was supported by the National Natural Science Foundation of China
(61763047).
The authors are with the College of Engineering of Yanbian University,
Yanji, 133002, China (e-mail: y[email protected]).
At the same time, new problems are updated too. For
example, intruding into in-vehicle network through OBD-II
interface could obtain and control messages including control
the key functions and the engine. That is, the vehicle is totally
controlled [6]. Intruder could gain control of vehicle telematic
component by intruding the vehicle telephone [7]. The
man-in-the-middle attack is also available to get the messages
transmitted between vehicle and external environment [8]. In
2015, it is reported that a remote intrusion is possible in the
distance of 16 kilometers [9]. Intruder could control the
infortainment system, the steering system, and braking
system.
In this paper, we propose an authenticated encryption
protocol in where AES-128 algorithm is used in the data
encryption. And HMAC (Hash-based message authentication
code) based on SHA (secure hash algorithm) -1 is used in the
authentication. It means that it is extremely hard to deduce
original message through the digest. Through analyzing some
representative attack model for in-vehicle bus system, the
experimental result and performances will be discussed.
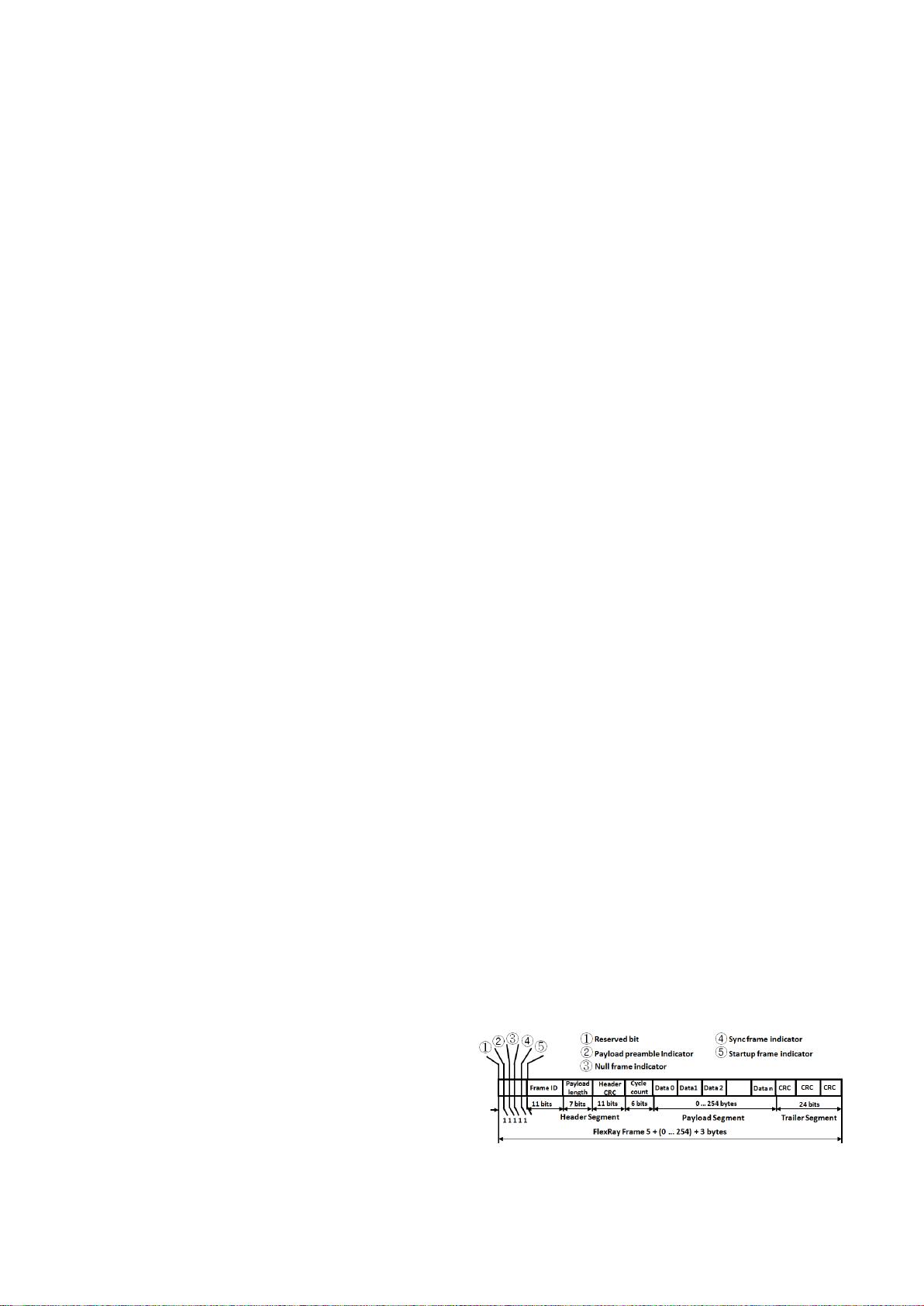
II. FLEXRAY COMMUNICATION PROTOCOL
FlexRay is a high speed network communication system
that supports a time-triggered scheme and an optional
event-triggered scheme. This FlexRay frame consists of three
segments: header segment, payload segment, and trailer
segment as depicted in Fig. 1. The first five bits define the
basic features of the frame. Frame ID (11 bits) is defined as
the slot position in the static segment and used to indicate the
priority of the frame for the dynamic segment. Payload
Length (7 bits) is defined as the data length. Header CRC (11
bits) is a Cyclic Redundancy Check, which is computed over
the Sync Frame Indicator (1 bit), Startup Frame Indicator (1
bit), Frame ID (11 bits), and Payload Length (7 bits). Cycle
Count (6 bits) is the serial number of the frame defined locally
in the node. Trailer Segment (24 bits) is for Cyclic
Redundancy Check, which is computed over the header
segment and payload segment.
Fig. 1. FlexRay frame format.
Payload Segment (0 to 254 bytes) contains main data.
These data will be transferred between vehicles, clouds, and
Research of Authenticated Encryption Security Protocol
for FlexRay In-vehicle Network
Meng-Zhuo Liu, Yi-Hu Xu, Yu-Jing Wu, and Yi-Nan Xu
International Journal of Computer Theory and Engineering, Vol. 10, No. 5, October 2018
175
DOI: 10.7763/IJCTE.2018.V10.1221
Orca是只鲸
- 粉丝: 27
- 资源: 317
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

评论0