没有合适的资源?快使用搜索试试~ 我知道了~
资源推荐
资源详情
资源评论

Chapter 3
ELLIPTIC CURVES AND
BILINEAR PAIRINGS
3.1 Introduction
The complexity-theoretic foundation for modern public-key cryptography is based
on a class of hard problems: NP problems. An encryption algorithm should, on
the one hand, provide a legitimate user who is in possession of correct encryp-
tion/decryption keys with efficient algorithms, i.e., polynomial-time, for encryption
and/or decryption, and on the other hand, pose an intractable problem for any
illegitimate person (a non-user, an adversary, an attacker or a cryptanalyst) who
tries to extract plaintext from ciphertext, or to construct a valid ciphertext without
using correct keys. Thus, a cryptographic key plays the role of an auxiliary input
to an NP problem. If necessary, the reader may review §2.5, in particular §2.5.6 for
the meaning of an auxiliary input to an NP problem.
In §2.5.6 we have listed and discussed a number of NP computational and de-
cisional problems which are suitable for, and have been widely used in, the con-
struction of modern public-key cryptographic algorithms and protocols. Most of
the problems listed there, e.g., problems (2-4) in Example 2.14, relate their in-
tractabilities to that of the integer factorization problem or that of the discrete
logarithm problem. In these cases, which we shall call “conventional public-key
cryptographic primitives”, the difficulty of the intractability is a sub-exponential
expression sub
exp(k) given in (2.5.9), here k is the security parameter of the algo-
rithm in question, which is usually the size of the public key parameter.
Thus, for a conventional public-key cryptographic primitive, the computational-
complexity asymmetry between a user and a non-user is poly(k) against sub
exp(k).
In fact, the difference between these two quantities is not desirably large for small
k. In order to make the asymmetry sufficiently significant, conventional public-key
cryptographic primitives all use rather large key parameters, i.e., large k. Nowa-
days, k = 1024 is widely considered the least setting for conventional public-key
cryptographic primitives. Consequently, legitimate users suffers a high computa-
tional cost.
Miller [?] and Koblitz [?] suggest to construct public-key cryptographic primi-
111

112 Elliptic Curves and Bilinear Pairings Chapter 3
tives using some calculations on elliptic curves.. These calculations will privite us
with a more different asymmetry between legitimate users and non-users because
these calculations run polynomial time for users and exponential time for non-users.
Recently, elliptic curve also finds new and exciting applications in cryptography,
in particular in cryptographic protocols. This is from so-called bilinear pairing
of points over certain elliptic curves. Applying bilinear pairings, Diffie-Hellman,
a well-known class of hard computational problems, have easy decisional version,
that is, it is efficient to answer the question whether a quadruple (a, b, c, d) is a
Diffie-Hellman instance (this is a hard decisional problem in the general case, see
Example 2.14). The difference between the decisional version and the computational
version of a cryptographically useful NP problem enable revolutionarily new ways
to do many things which were thought impossible not too long ago.
In this chapter we introduce elliptic curves and bilinear pairings. The material
to be provided here has a focus on bilinear pairings and forms a self-contained
foundation for our future study (in this book) of interesting cryptographic protocols
which apply bilinear pairing techniques.
3.1.1 Chapter Outline
§3.2 introduces elliptic curves over finite fields. §3.3 introduces bilinear pairing
techniques.
3.2 Elliptic Curves
Elliptic curves for cryptography are defined over finite algebraic structures such as
finite fields. For ease of exposition, let us confine ourselves to the easy case of prime
fields F
p
of characteristic p > 3. An elliptic curve over F
p
is the set of geometric
solutions P = (x, y) to an equation of the following form
E : y
2
= x
3
+ ax + b (3.2.1)
where a and b are elements in F
p
(p > 3) satisfying 4a
3
+ 27b
2
6≡ 0 (mod p).
a
To
have the points on E to form a group, an extra point denoted by O is included.
This extra point is called the point at infinity and can be formulated as
O = (∞, ∞).
We write the set of all such points on E as
E(F
p
) = {P = (x, y) | x, y ∈ F
p
solved from (3.2.1) } ∪ {O}. (3.2.2)
This set of points form a group under a group operation which is conventionally
written additively using the notation “+” . We will define this operation in a
moment. We will use E in place of E(F
p
) whenever the omission of the presentation
of the underlying field will not cause confusion.
a
Reason to be given after Definition 3.1.

Section 3.2. Elliptic Curves 113
Denote by f (x) the cubic polynomial in the right-hand side of (3.2.1). If f(x)
is reducible over F
p
then (ξ, 0) ∈ E where ξ ∈ F
p
is a zero, also called root, of f(x)
(i.e. f (ξ) ≡ 0 (mod p) and this is why f (x) is reducible over F
p
). We will see in
a moment that these points have order 2 under the group operation “+” . Since
f(x) is a cubic polynomial, there are at most three such points. Depending how
the cubic polynomial f(x) is reducible over F
p
, there is either one order-2 point or
there are three such points. We will see in Fig 3.1 in a moment that these order-2
points are in where the curve cuts the real axis.
All other points apart form O and (ξ, 0) are of the form (η, ±
p
f(η)) where
η ∈ F
p
and f(η) 6≡ 0 (mod p) is a quadratic residue element in F
p
(i.e., a square
number modulo p, see §2.11). Indeed, each quadratic residue element in F
p
has
two distinct square roots modulo p (see Corollary 2.4) and hence if (η,
p
f(η)) is a
solution, so is (η, −
p
f(η)).
To this end we know that the points on the curve E(F
p
) are O, (ξ, 0), (η,
p
f(η))
and (η, −
p
f(η)) for all ξ, η in F
p
satisfying that f(ξ) ≡ 0 (mod p) and f(η) is a
quadratic residue element in F
p
.
3.2.1 The Group Operation
The set of points on E defined in (3.2.2) forms an abelian group under the operation
“+” defined as follows.
Definition 3.1: Elliptic Curve Group Operation (Chord-and-Tangent Oper-
ation) Let P, Q ∈ E, ` be the line containing P and Q (tangent line to E if P = Q),
and R, the third point of intersection of ` with E. Let `
0
be the line connecting R
and O. Then P “+” Q is the point such that `
0
intersects E at R, O and P “+” Q.
We can now explain why we have required the coefficients of the cubic polynomial
in (3.2.1) to satisfy 4a
3
+ 27b
2
6≡ 0 (mod p). Notice that
∆ = −4a
3
− 27b
2
is the discriminant of the cubic polynomial f(x) = x
3
+ ax + b. If ∆ ≡ 0 (mod p)
then f(x) ≡ 0 (mod p) has at least a double zero X (value which makes f(X) ≡
0 (mod p)) and clearly (X, 0) is on E. For E(x, y) = y
2
−x
3
−ax −b = 0, this point
satisfies
∂E
∂y
= 2y
y=0
=
∂E
∂x
x=X
= 0.
That is, (X, 0) is a singular point at which there is no unique tangent value. For
example, (X, 0) “+” (X, 0) is not uniquely defined and this means a vialation of
Closure Axiom. Therefore, when ∆ ≡ 0 (mod p), (E, “+” ) cannot form a group.
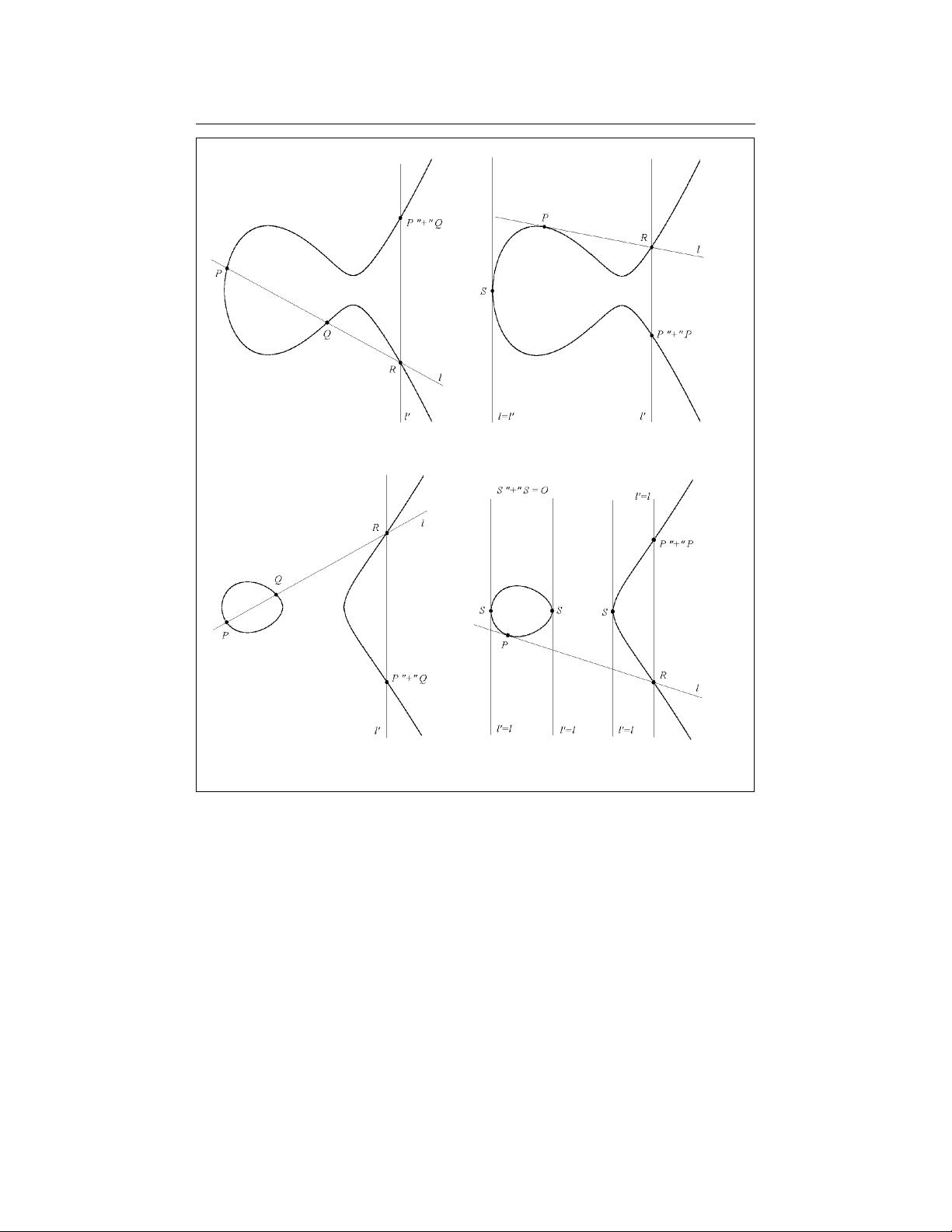
Fig 3.1 illustrates the Chord-and-Tangent Operation Note, the illustration only
makes sense for a curve defined over R. The top two curves are the case for ∆ < 0;
in this case the cubic polynomial has one real zero and so the curve cuts the real
114 Elliptic Curves and Bilinear Pairings Chapter 3
Figure 3.1. Elliptic Curves and the Group Operation
axis once. The lower two curves are the case for ∆ > 0; in this case the cubic
polynomial has three real zeros and so the curve cuts the real axis three times
(note, with ∆ 6= 0, these three zeros must be distinct).
We remark that any line connecting a finite point F = (X, Y ) ∈ E and “the
point at infinity” O = (∞, ∞) ∈ E is the virtical line x = X. Informally we can
think of O = (∞
x
, ∞
y
) ∈ E satisfying
∞
2
y
= ∞
3
x
+ ...

Section 3.2. Elliptic Curves 115
For this equation to hold, ∞
y
must a “greater infinity” than ∞
x
. Thus viewed
from the finite space, the point O is at the infinitely far distance “in the north
pole direction.” That’s why the line connecting any finite point F and O should be
virtical. In §?? we will see a formal evidence for this informal explanation.
Let us now show that (E, “+” ) does form a group.
3.2.1.1 Identity and Inverse
For any P = (X, Y ) ∈ E, let us apply Definition 3.1 to a special case of Q being O
(since we have included O in E). For this case, line ` intersecting P and O is
` : x = X.
Since P ∈ E, f(X) = X
3
+ aX + b must be a quadratic residue in F
p
and therefore
−Y is the other square root of y
2
= f (X). That is, ` also intersects point R =
(X, −Y ) ∈ E. It is now clear that `
0
= `, i.e., `
0
intersects the same three points P ,
R and O as ` does. By Definition 3.1 we obtain
P = P “+” O
for any P ∈ E.
Denoting (X, −Y ) = “ − ”(X, Y ) = “ − ”P , similar to the above reasoning we
know “ − ”P is on the curve and
P “+” “ − ”P = O.
Thus under the operation “+” , O functions exactly the identity element of a group
does. We have therefore shown that (E, Eplus) satisfies Identity Axiom and Inverse
Axiom.
A special case of this special case is y
1
= −y
2
= 0. This is the case of S = (X, 0);
clearly we have S = “ − ”S or equivalently S “+” S = O. Therefore, such S is an
order-2 element. We have mentioned this special element earlier: it is a solution
of y
2
= f(x) ≡ 0 (mod p). Such special points only exist when f(x) ≡ 0 (mod p)
has zeros in F
p
, i.e., when f(x) is reducible over F
p
. Illustrated in Fig 3.1, order-2
points are those which are tangented by virtical lines.
3.2.1.2 Closure
We have shown that points P = (X, Y ) and Q = (X, −Y ) which are connected by
the same vertical line satisfy Closure Axiom.
Now let us consider the general case of P = (X
1
, Y
1
) and Q = (X
2
, Y
2
) being
connected by ` which is a non-vertical line. The formula for ` is
` : y − Y
1
= λ(x − X
1
) (3.2.3)
剩余30页未读,继续阅读
资源评论

song2407
- 粉丝: 2
- 资源: 7
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

