没有合适的资源?快使用搜索试试~ 我知道了~
Implementing Infoblox DNS Firewall
需积分: 10 3 下载量 9 浏览量
2023-01-20
11:13:01
上传
评论
收藏 2.38MB PDF 举报
温馨提示

试读
21页
Implementing Infoblox DNS Firewall.非常详细的介绍了Infoblox DNS firewall的配置。
资源推荐
资源详情
资源评论
© 2017 Infoblox Inc. All rights reserved. Implementing Infoblox DNS Firewall January, 2017 Page 1 of 21
DEPLOYMENT GUIDE
Implementing Infoblox DNS Firewall.

© 2017 Infoblox Inc. All rights reserved. Implementing Infoblox DNS Firewall January, 2017 Page 2 of 21
Contents
Introduction ....................................................................................................................................... 3
Data Flow for DNS Firewall .............................................................................................................. 3
Requirements ................................................................................................................................... 3
Types of RPZs .................................................................................................................................. 4
Best Practices ................................................................................................................................... 4
Deployment Summary ...................................................................................................................... 5
Deployment Instructions ................................................................................................................... 5
Configure Local RPZ. ................................................................................................................. 5
Configure RPZ Feed with Infoblox Threat Intelligence Feed. .................................................. 13
Troubleshooting ....................................................................................................................... 21
© 2017 Infoblox Inc. All rights reserved. Implementing Infoblox DNS Firewall January, 2017 Page 3 of 21
Introduction
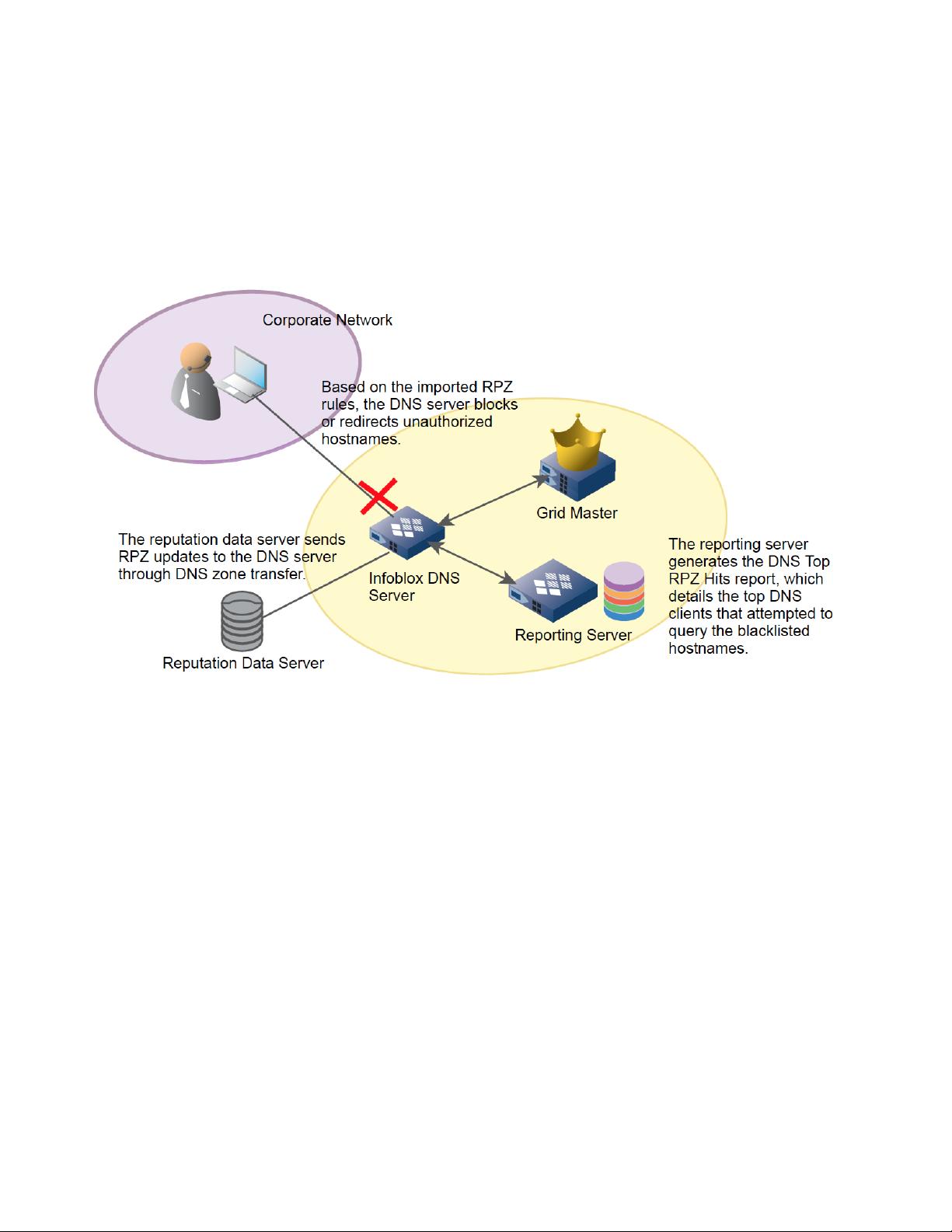
Infoblox DNS Firewall employs DNS RPZs (Response Policy Zones), a technology developed by ISC (Internet
System Consortium) for allowing reputable sources to dynamically communicate domain name reputation so you
can implement policy controls for DNS lookups.
This deployment guide shows how to deploy DNS Firewall.
Data Flow for DNS Firewall
There are five steps to a malware attack*:
1. Entry – downloading of the malware code from either an infected website or email with an attachment or
link that hijacks the user’s browser.
2. Distribution – Initial malware redirects the user’s browser to a select malicious site.
3. Exploit – an exploit kit now probes the computer for vulnerabilities.
4. Infection – Malicious payload is downloaded and infects the user’s system with malware.
5. Execution – The malware calls home with sensitive data or attempts to extort the user for money
(ransomware).
*source: Sophos.com
Step 5 is where DNS firewall gets involved. The malware performs a command and control step to steal sensitive
data. In order to talk to the command and control server, the malware makes a call to the DNS to resolve the
name of the command and control server. With DNS firewall and its local reputation entries and/or reputation
entries from a reputation feed, the DNS resolution can be blocked or redirected to a walled garden website. With
Infoblox, indications of a reputation hit can be seen in the syslog (i.e. CEF messages) or DNS RPZ report from
the reporting server. At this point, the workstation can be tracked down via IP address, username, and switchport
to clean off the malware.
Requirements
The following items are required for DNS Firewall:
RPZ license per recursive DNS member that will have DNS Firewall enabled.

© 2017 Infoblox Inc. All rights reserved. Implementing Infoblox DNS Firewall January, 2017 Page 4 of 21
Access to the Infoblox Cloud Service Platform RPZ management portal (https://csp.infoblox.com) or other
reputation feeds like Spamhaus.
Infoblox NIOS 8.0 or later is recommended.
Types of RPZs
Local RPZ–A local RPZ is a zone that allows administrators to define multiple response policies locally.
Query responses sent are based on the defined rules.
RPZ Feed–An RPZ feed receives response policies from external sources. DNS clients receive
responses based on the imported rules from a reputable source.
FireEye integrated RPZ–By integrating the NIOS appliance with the FireEye appliance, you can detect
malware and APTs and take necessary actions to mitigate those threats by importing updates from
FireEye appliance into a FireEye RPZ.
Best Practices
When you enable Infoblox DNS Firewall, DNS performance for all queries, recursive or authoritative, will
be affected.
If you have multiple DNS servers in a Grid, ensure that you configure RPZs on the recursive server that is
closest to your DNS clients. If you configure RPZs on second level DNS caching servers, you will not be
able to identify the DNS clients because only the IP addresses of the forwarding name servers can be
identified.
Infoblox recommends that you preview your RPZ rules to ensure ruleset integrity and to avoid unexpected
results. You can preview your rules by selecting Log Only (Disabled) when you configure Policy Override
for an RPZ, RPZ feed, or FireEye integrated RPZ.
The appliance logs all matching and disabled rules for all queries in the syslog. You can view the syslog
to ensure that the rules are set up correctly before they take effect. Ensure that you enable RPZ in the
Logging Category of Grid DNS Properties editor to log these events.
You can use the standard TSIG mechanism to ensure that feed zones come from the correct servers.
Grid members can function either as a primary or secondary servers for the RPZ. As with hosting any
zone as a secondary, please ensure that the appliance is sized properly to hold the zone contents in
memory.
You can only export or import the RPZ local zones using the CSV export or import feature, but you cannot
import or export FireEye zones using this feature.
Note that the NIOS blacklist and NXDOMAIN features take precedence over RPZs.
In order to leverage DNS, notify messages to trigger zone transfer of the feed zone, port 53 incoming on
the lead secondary must be open to receive such messages (TCP and UDP). If not, the zone will refresh
based on the refresh setting in the SOA.
The name of the zone, which is assigned to an RPZ member, must not exceed 256 characters. The name
can be a combination of alphanumeric characters. When the name exceeds this limit, respective zone
fails to load.
Best Practices for FireEye Integrated RPZs
Before you configure a FireEye integrated RPZ, consider the following:
FireEye integrated RPZs inherit default values from local RPZs. You can create, edit and delete rules
using the Infoblox GUI, API, and RESTful API.
To avoid false positives, Infoblox recommends that you create a whitelist of allowed zones using a local
RPZ that is sorted above the FireEye RPZ and add your own domain to the whitelist RPZ. For example,
you can add your company domain name, such as corp100.com. This list must contain popular domains,
such as Alexa 250, and other desired domains.
Note that there will be an impact on the storage capacity when you create a new FireEye alert and map it
with an RPZ rule. The processing of alerts will consume a few CPU cycles, which will have some impact
on the system.

© 2017 Infoblox Inc. All rights reserved. Implementing Infoblox DNS Firewall January, 2017 Page 5 of 21
You must properly configure the settings on a FireEye appliance. NIOS supports only Per Event delivery
mechanism and JSON Normal message format. To ensure that the NIOS appliance process alerts
properly, configure the FireEye appliance accordingly.
You cannot add a FireEye integrated RPZ during a scheduled full upgrade. However, updates to the
CNAME record are processed during a full upgrade. NIOS updates CNAME records in the database to
store information that is specific to FireEye alerts.
The rules created due to insertion of alerts will be visible through the FireEye RPZ viewer. Infoblox
recommends that you do not modify any internal objects. For more information, see Viewing RPZs on
page 1690.
Note that SSL certificate validation is not supported.
You must verify the following after you configure the FireEye and NIOS appliances:
o The URL configured on the FireEye appliance matches the URL in the FireEye integrated RPZ on
NIOS.
o Verify the username and password for FireEye admin on the FireEye appliance.
o Ensure that the settings are properly configured on the FireEye appliance.
o Verify the state of the FireEye appliance.
o Do note that all settings are case sensitive.
Note that the frequency of alerts received from FireEye can be minimal. A very small number of alerts are
generated on a weekly basis. For example, the FireEye appliance may generate only tens of alerts per
day.
Deployment Summary
Install a valid RPZ license. Refer to the Infoblox NIOS administrators guide for more information.
Enable recursion for your DNS view in which you want to deploy RPZs.
Configure RPZ logging to ensure all matching and disabled rules for all queries are logged in the syslog.
Refer to the Infoblox NIOS administrator guide for more information.
Configure RPZs.
Deployment Instructions
Configure Local RPZ.
1. Log into the Infoblox GUI.
剩余20页未读,继续阅读
资源评论

Mr.Sun_
- 粉丝: 1910
- 资源: 45
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
