
OSQuery Application Security Assessment
Facebook
October 23, 2015 – Version 1.3
Prepared for
Mike Arpaia
Prepared by
Raphael Salas
Andrew Rahimi
Robert Seacord

©2016 – NCC Group
Prepared by NCC Group Security Services, Inc. for Facebook. Portions of this document and the templates used in its production
are the property of NCC Group and cannot be copied (in full or in part) without NCC Group's permission.
While precautions have been taken in the preparation of this document, NCC Group the publisher, and the author(s) assume no
responsibility for errors, omissions, or for damages resulting from the use of the information contained herein. Use of NCC Group's
services does not guarantee the security of a system, or that computer intrusions will not occur.
2 | Facebook osquery
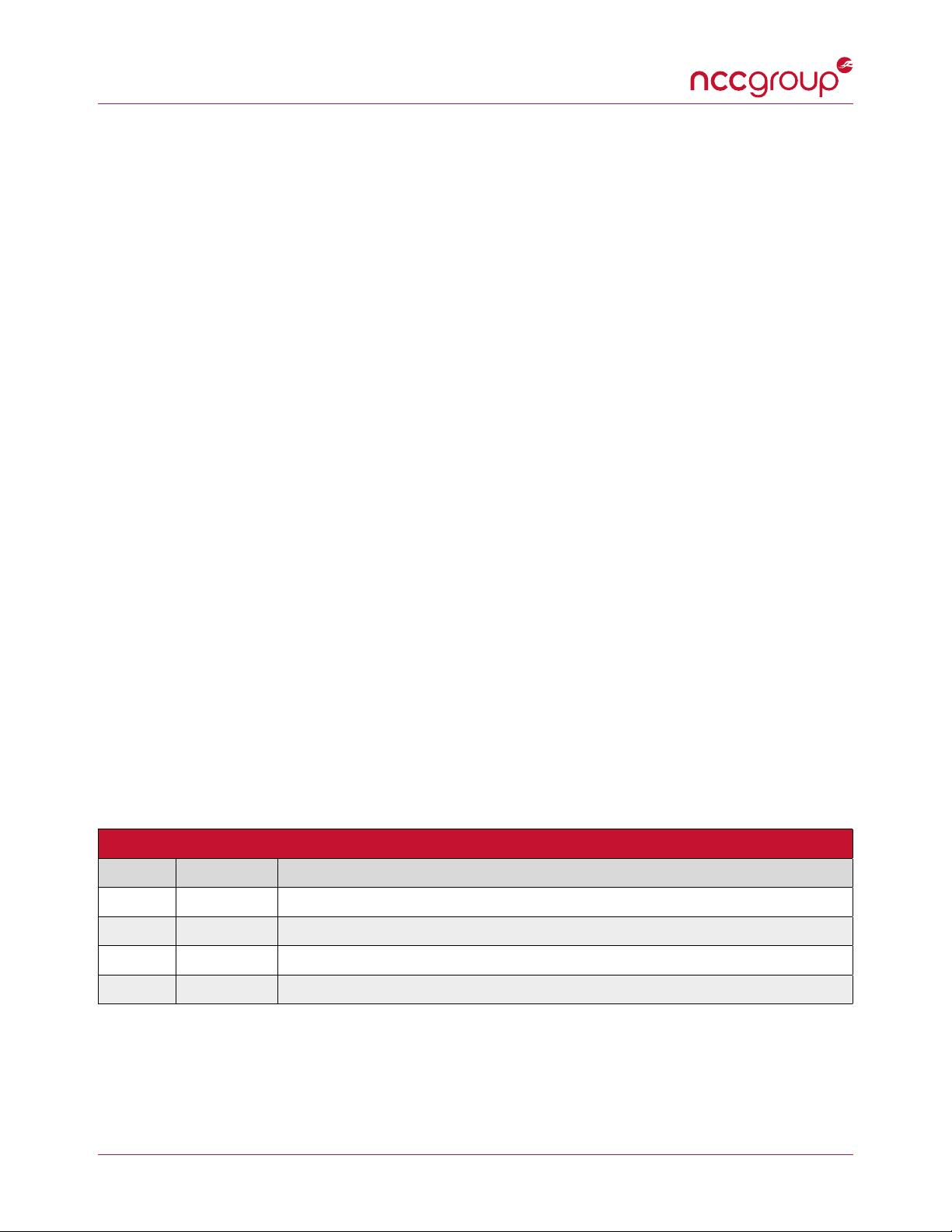
Document Change Log
Version Date Change
1.0 2015-10-23 Distributed report to Facebook.
1.1 2015-11-05 Incorporated discussions during readout regarding exploitability of key findings.
1.2 2016-01-18 Preparing for public release after rounds of additional peer review.
1.3 2016-01-25 Public release.
3 | Facebook osquery

Executive Summary
Synopsis
Facebook engaged NCC Group to conduct a security
assessment of the osquery instrumentation framework.
This assessment was conducted by 3 consultants during
the weeks of October 12
th
and October 19
th
, 2015.
The entire application was in scope, as sourced from
the project's official GitHub page. The Facebook team
requested that formal status meetings be foregone in
exchange for active collaboration between Facebook
and NCC Group via email and GitHub. This resulted
in several issues being fixed in real-time alongside the
disclosure process.
Scope
NCC Group's assessment included osquery core and
plugin interfaces, focusing on the following main attack
surfaces:
• Data Collection: An analysis of the set of osquery
tables used to represent operating system state
information, including the plugin interface allowing
table implementation via the Thrift API.
• Kernel Integration: A review of OS X specific function-
ality exposed to the osqueryd daemon through the
included kernel extension.
• Transport Security: A review of the osqueryd plugin
interface that exposes its subsystems remotely over
authenticated TLS endpoints.
• Database Security: A review of the RocksDB instance
used to house and cache information about the
system.
• Configuration Parsing & Secure Defaults: Code review
of plugins that read and parse configuration from disk,
command line, or remote servers.
Testing was performed on the Git revision 4d0cd46
dated 10/09/2015.
Key Findings
The assessment discovered the following key findings:
• A Time-of-Check Time-of-Use TOCTOU issue in the
osquery::readFile function used throughout the
framework allowing an attacker to cause osquery to
read arbitrary files where the attacker may not have
sufficient permissions to do so.
• A parsing issue where the configuration parser ex-
pects a ``query" JSON key resulting in osqueryd
aborting due to an unhandled exception. This can be
triggered remotely via the TLS configuration plugin
to cause denial of service, provided an attacker gains
access to an authenticated TLS endpoint.
• Comparisons between integers of different signs
and unsigned integer wrap-around throughout the
osquery code.
Non-security findings are listed in Appendix F.
Limitations
While NCC Group was able to review the majority of
the targeted components, the assessment of individual
tables was inconsistent. Table implementations are
specific to the various operating systems supported
by osquery making complete coverage across all sup-
ported platforms impractical in the time provided. Due
to time constraints, NCC Group prioritized the assess-
ment of common table functionality across supported
platforms, with most testing performed on the Ubuntu
14.04 LTS Vagrant VM and OS X 10.10.3 (Yosemite)
configurations. Consequently, details specific to other
Linux distributions such as CentOS and FreeBSD table
implementations only received a cursory review.
Strategic Recommendations
Consider implementing a least-privilege model, where
privileges are temporarily dropped before performing
I/O operations on behalf of an unprivileged user. For
example, user-owned files should be accessed with
the effective privileges of the user to avoid allowing
unprivileged users to operate on restricted files.
Enforce coding guidelines and fix violations. Do not
disable warnings such as differing signedness compar-
isons and continue to test sanitized versions, adding
additional sanitizers. Instrumented executables should
be tested more aggressively to identify potential issues
at runtime.
Extend read limitations across tables, particularly those
that are OS specific. For instance, size checking
against read limitations in the Safari Extensions table
can prevent decompression bombs that can negatively
impact the result of a query. Consistently applying
limitations can prevent this and other conditions where
unprivileged users can interfere with normal operation.
Maintain and test an updated build chain. NCC
Group was able to leverage the updated Clang 3.7
compiler to identify numerous defects that had not been
previously detected by Clang 3.5. Facebook should
also ensure that the latest versions of tools and software
components, such as Thrift, are used in the product.
4 | Facebook osquery
Project Dashboard
Target Metadata
Name osquery
Type Daemon
Language C++
Environment Testing (Vagrant-provisioned)
Engagement Data
Type Application Security Assessment
Method Code-assisted
Dates 2015-10-12 to 2015-10-23
Consultants 3
Level of
effort 6 person-weeks
Targets
osquery Source Code https://github.com/facebook/osquery — Reference commit: 4d0cd46
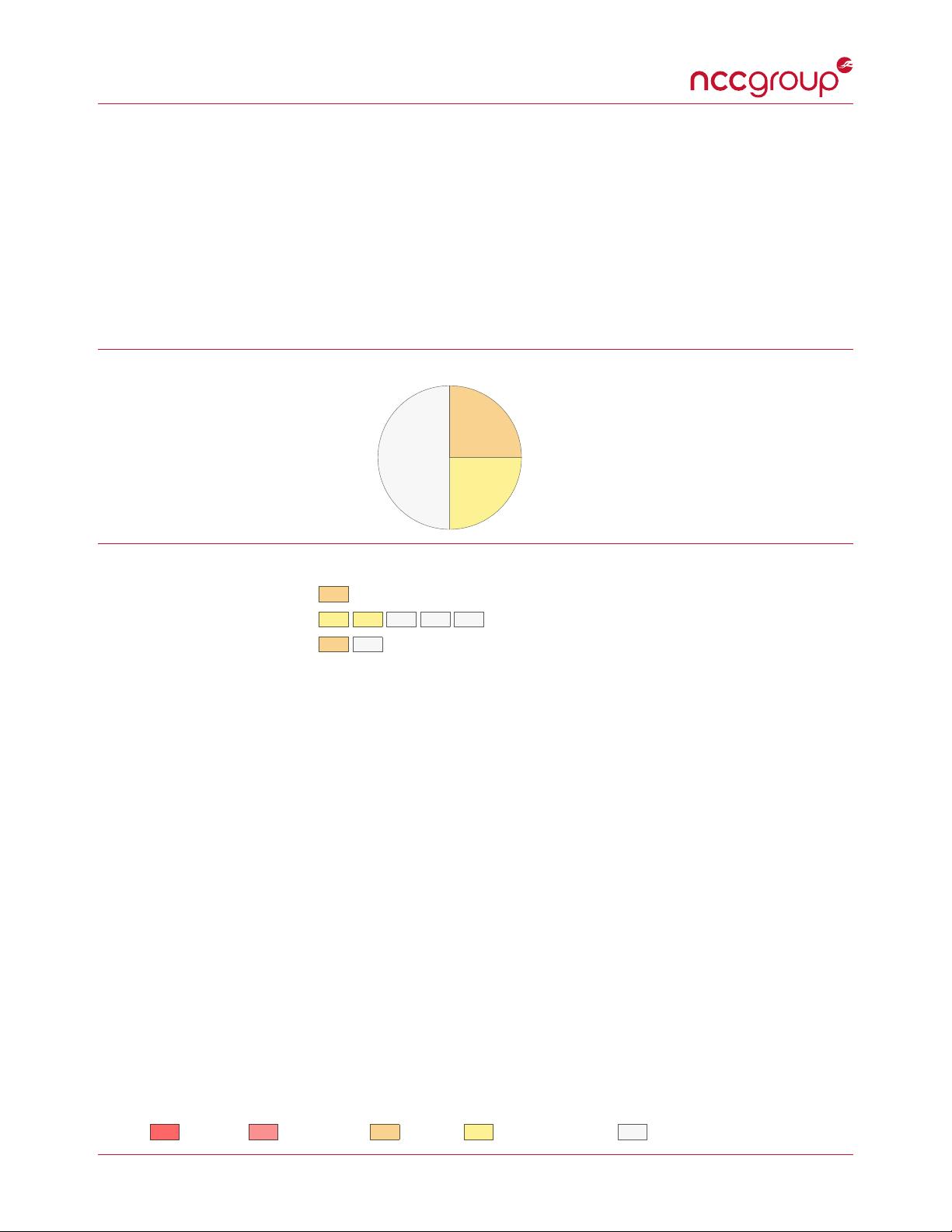
Vulnerability Breakdown
Critical Risk issues 0
High Risk issues 0
Medium Risk issues 2
Low Risk issues 2
Informational issues 4
Total issues 8
Category Breakdown
Data Exposure
1
Data Validation
5
Denial of Service
2
Key
Critical High Medium Low Informational
5 | Facebook osquery
















