# Checkov
[](https://bridgecrew.io/?utm_source=github&utm_medium=organic_oss&utm_campaign=checkov)
[](https://github.com/bridgecrewio/checkov/actions?query=workflow%3Abuild)
[](https://github.com/bridgecrewio/checkov/actions?query=workflow%3Acoverage)
[](https://www.checkov.io/documentation?utm_source=github&utm_medium=organic_oss&utm_campaign=checkov)
[](https://pypi.org/project/checkov/)
[](https://pepy.tech/project/checkov)

## **Table of contents**
- [Description](#description)
- [Features](#features)
- [Screenshots](#screenshots)
- [Getting Started](#getting-started)
- [Support](#support)
## Description
Checkov is a static code analysis tool for infrastructure-as-code. It scans cloud infrastructure provisioned using Terraform or cloudformation and detects security and compliance misconfigurations.
Checkov is written in Python and provides a simple method to write and manage policies. It follows the CIS Foundations benchmarks where applicable.
## Features
* [100+ built-in policies](docs/3.Scans/resource-scans.md) cover security and compliance best practices for AWS, Azure & Google Cloud.
* Scans Terraform and AWS CloudFormation configurations.
* Scans for [AWS credentials](docs/3.Scans/Credentials%20Scans.md) in EC2 Userdata, Lambda environment variables and Terrafrom providers
* Policies support evaluation of variables to their optional default value.
* Supports in-line suppression of accepted risks or false-positives to reduce recurring scan failures.
* Output currently available as CLI, JSON or JUnit XML.
## Screenshots
Scan results in CLI
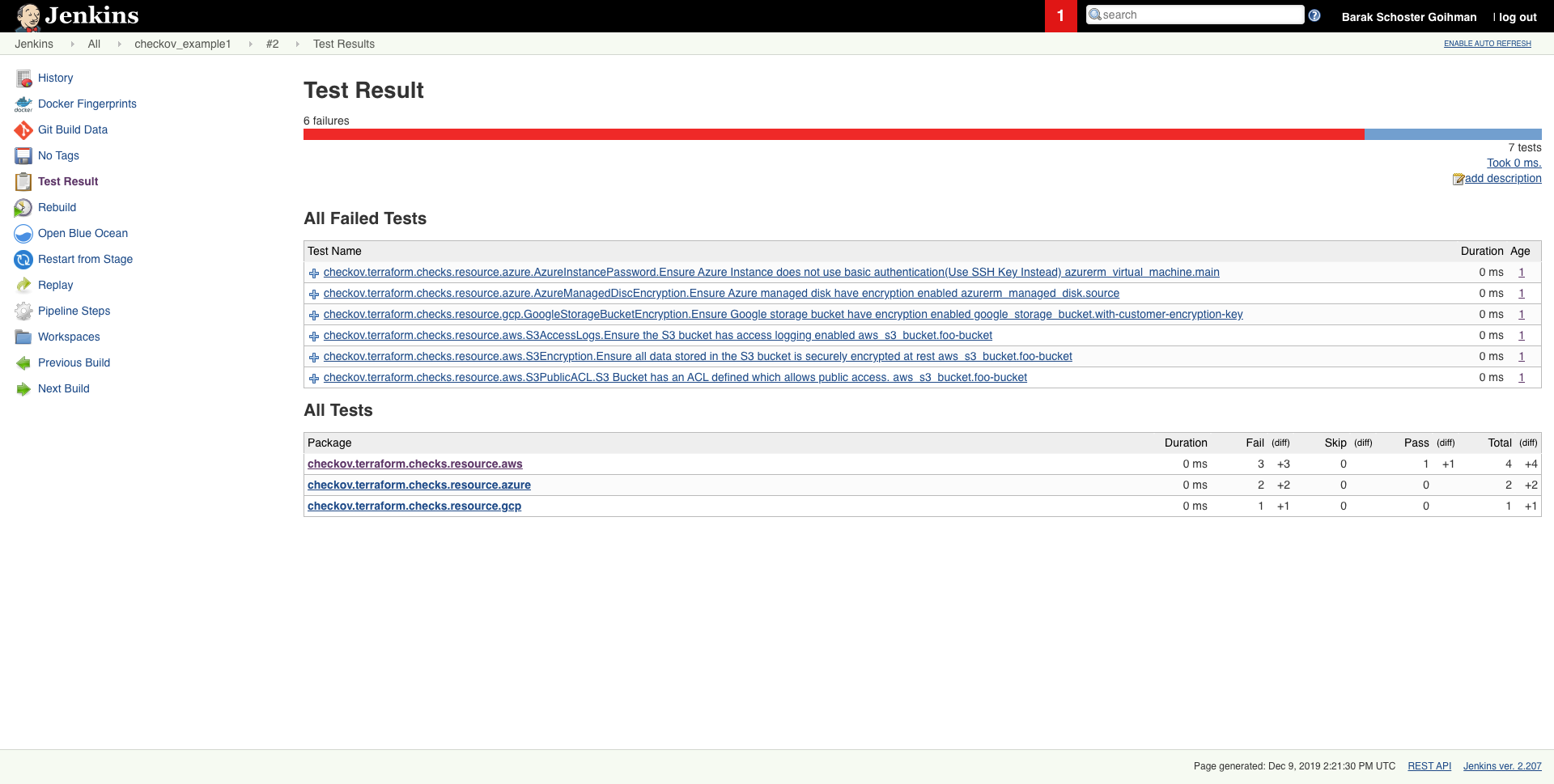
Scheduled scan result in Jenkins
## Getting started
### Installation
```sh
pip install checkov
```
or using homebrew (MacOS only)
```sh
brew tap bridgecrewio/checkov https://github.com/bridgecrewio/checkov
brew update
brew install checkov
```
### Configure an input folder
```sh
checkov -d /user/path/to/iac/code
```
Or a specific file
```sh
checkov -f /user/tf/example.tf
```
or
```sh
checkov -f /user/cloudformation/example.yml
```
### Scan result sample (CLI)
```sh
Passed Checks: 1, Failed Checks: 1, Suppressed Checks: 0
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/main.tf:
Passed for resource: aws_s3_bucket.template_bucket
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/../regionStack/main.tf:
Failed for resource: aws_s3_bucket.sls_deployment_bucket_name
```
Start using Checkov by reading the [Getting Started](docs/1.Introduction/Getting%20Started.md) page.
### Using Docker
```sh
docker pull bridgecrew/checkov
docker run -t -v /user/tf:/tf bridgecrew/checkov -d /tf
```
### Suppressing/Ignoring a check
Like any static-analysis tool it is limited by its analysis scope.
For example, if a resource is managed manually, or using subsequent configuration management tooling,
a suppression can be inserted as a simple code annotation.
#### Suppression comment format
To skip a check on a given Terraform definition block, apply the following comment pattern inside it's scope:
`checkov:skip=<check_id>:<suppression_comment>`
* `<check_id>` is one of the [available check scanners](../3.Scans/resource-scans.md)
* `<suppression_comment>` is an optional suppression reason to be included in the output
#### Example
The following comment skip the `CKV_AWS_20` check on the resource identified by `foo-bucket`, where the scan checks if an AWS S3 bucket is private.
In the example, the bucket is configured with a public read access; Adding the suppress comment would skip the appropriate check instead of the check to fail.
```hcl-terraform
resource "aws_s3_bucket" "foo-bucket" {
region = var.region
#checkov:skip=CKV_AWS_20:The bucket is a public static content host
bucket = local.bucket_name
force_destroy = true
acl = "public-read"
}
```
The output would now contain a ``SKIPPED`` check result entry:
```bash
...
...
Check: "S3 Bucket has an ACL defined which allows public access."
SKIPPED for resource: aws_s3_bucket.foo-bucket
Suppress comment: The bucket is a public static content host
File: /example_skip_acl.tf:1-25
...
```
## Alternatives
For Terraform compliance scanners check out [tfsec](https://github.com/liamg/tfsec), [Terrascan](https://github.com/cesar-rodriguez/terrascan) and [Terraform AWS Secure Baseline](https://github.com/nozaq/terraform-aws-secure-baseline).
For CloudFormation scanning check out [cfripper](https://github.com/Skyscanner/cfripper/) and [cfn_nag](https://github.com/stelligent/cfn_nag).
## Contributing
Contribution is welcomed!
Start by reviewing the [contribution guidelines](CONTRIBUTING.md). After that, take a look at a [good first issue](https://github.com/bridgecrewio/checkov/issues?q=is%3Aissue+is%3Aopen+label%3A%22good+first+issue%22).
Looking to contribute new checks? Learn how to write a new check (AKA policy) [here](docs/5.Contribution/New-Check.md)
## Support
[Bridgecrew](https://bridgecrew.io) builds and maintains Checkov to make policy-as-code simple and accessible.
Start with our [Documentation](https://bridgecrewio.github.io/checkov/) for quick tutorials and examples.
If you need direct support you can contact us at info@bridgecrew.io
没有合适的资源?快使用搜索试试~ 我知道了~
温馨提示

共169个文件
py:159个
txt:4个
pkg-info:2个
资源分类:Python库 所属语言:Python 资源全名:checkov-1.0.242.tar.gz 资源来源:官方 安装方法:https://lanzao.blog.csdn.net/article/details/101784059
资源推荐
资源详情
资源评论
收起资源包目录
 Python库 | checkov-1.0.242.tar.gz (169个子文件)
Python库 | checkov-1.0.242.tar.gz (169个子文件)  setup.cfg 38B
setup.cfg 38B checkov 90B
checkov 90B checkov.cmd 1KB
checkov.cmd 1KB README.md 6KB
README.md 6KB PKG-INFO 8KB
PKG-INFO 8KB PKG-INFO 8KB
PKG-INFO 8KB cfn_json.py 13KB
cfn_json.py 13KB node.py 7KB
node.py 7KB runner.py 7KB
runner.py 7KB cfn_yaml.py 7KB
cfn_yaml.py 7KB base_parser.py 6KB
base_parser.py 6KB const_variable_evaluation.py 5KB
const_variable_evaluation.py 5KB report.py 5KB
report.py 5KB runner.py 5KB
runner.py 5KB record.py 4KB
record.py 4KB base_check_registry.py 4KB
base_check_registry.py 4KB setup.py 3KB
setup.py 3KB base_variable_evaluation.py 3KB
base_variable_evaluation.py 3KB SecurityGroupRuleDescription.py 3KB
SecurityGroupRuleDescription.py 3KB main.py 2KB
main.py 2KB parser.py 2KB
parser.py 2KB CloudfrontDistributionEncryption.py 2KB
CloudfrontDistributionEncryption.py 2KB base_check.py 2KB
base_check.py 2KB SecurityGroupUnrestrictedIngress22.py 2KB
SecurityGroupUnrestrictedIngress22.py 2KB __init__.py 2KB
__init__.py 2KB GoogleCloudSqlDatabasePublicallyAccessible.py 2KB
GoogleCloudSqlDatabasePublicallyAccessible.py 2KB ElasticsearchNodeToNodeEncryption.py 2KB
ElasticsearchNodeToNodeEncryption.py 2KB EKSPublicAccessCIDR.py 2KB
EKSPublicAccessCIDR.py 2KB SecurityGroupUnrestrictedIngress3389.py 2KB
SecurityGroupUnrestrictedIngress3389.py 2KB SecurityGroupUnrestrictedIngress22.py 2KB
SecurityGroupUnrestrictedIngress22.py 2KB GoogleBigQueryDatasetPublicACL.py 1KB
GoogleBigQueryDatasetPublicACL.py 1KB ALBListenerHTTPS.py 1KB
ALBListenerHTTPS.py 1KB GoogleCloudDNSKeySpecsRSASHA1.py 1KB
GoogleCloudDNSKeySpecsRSASHA1.py 1KB docs_generator.py 1KB
docs_generator.py 1KB CloudfrontDistributionEncryption.py 1KB
CloudfrontDistributionEncryption.py 1KB LaunchConfigurationEBSEncryption.py 1KB
LaunchConfigurationEBSEncryption.py 1KB ECRPolicy.py 1KB
ECRPolicy.py 1KB S3Encryption.py 1KB
S3Encryption.py 1KB ElasticacheReplicationGroupEncryptionAtTransitAuthToken.py 1KB
ElasticacheReplicationGroupEncryptionAtTransitAuthToken.py 1KB GoogleContainerClusterClientCertificateEnabled.py 1KB
GoogleContainerClusterClientCertificateEnabled.py 1KB GoogleComputeFirewallUnrestrictedIngress3389.py 1KB
GoogleComputeFirewallUnrestrictedIngress3389.py 1KB GoogleComputeFirewallUnrestrictedIngress22.py 1KB
GoogleComputeFirewallUnrestrictedIngress22.py 1KB ALBListenerHTTPS.py 1KB
ALBListenerHTTPS.py 1KB ElasticsearchNodeToNodeEncryption.py 1KB
ElasticsearchNodeToNodeEncryption.py 1KB DynamodbRecovery.py 1KB
DynamodbRecovery.py 1KB AzureInstancePassword.py 1KB
AzureInstancePassword.py 1KB ElasticacheReplicationGroupEncryptionAtTransit.py 1KB
ElasticacheReplicationGroupEncryptionAtTransit.py 1KB runner_registry.py 1KB
runner_registry.py 1KB ElasticsearchEncryption.py 1KB
ElasticsearchEncryption.py 1KB ElasticacheReplicationGroupEncryptionAtRest.py 1KB
ElasticacheReplicationGroupEncryptionAtRest.py 1KB credentials.py 1KB
credentials.py 1KB ElasticacheReplicationGroupEncryptionAtTransitAuthToken.py 1KB
ElasticacheReplicationGroupEncryptionAtTransitAuthToken.py 1KB EKSControlPlaneLogging.py 1KB
EKSControlPlaneLogging.py 1KB EKSPublicAccess.py 1KB
EKSPublicAccess.py 1KB ECRPolicy.py 1KB
ECRPolicy.py 1KB variable_context_parser.py 1KB
variable_context_parser.py 1KB GoogleStorageBucketEncryption.py 1KB
GoogleStorageBucketEncryption.py 1KB GoogleCloudSqlDatabaseRequireSsl.py 1KB
GoogleCloudSqlDatabaseRequireSsl.py 1KB GoogleContainerNodePoolAutoUpgradeEnabled.py 1KB
GoogleContainerNodePoolAutoUpgradeEnabled.py 1KB AdminPolicyDocument.py 1KB
AdminPolicyDocument.py 1KB GoogleContainerNodePoolAutoRepairEnabled.py 1KB
GoogleContainerNodePoolAutoRepairEnabled.py 1KB GoogleContainerClusterNetworkPolicyEnabled.py 1KB
GoogleContainerClusterNetworkPolicyEnabled.py 1KB SecurityGroupRuleDescription.py 1KB
SecurityGroupRuleDescription.py 1KB KinesisStreamEncryptionType.py 1KB
KinesisStreamEncryptionType.py 1KB CloudtrailLogValidation.py 1KB
CloudtrailLogValidation.py 1KB registry.py 1KB
registry.py 1KB StorageAccountsTransportEncryption.py 1KB
StorageAccountsTransportEncryption.py 1KB EC2Credentials.py 1KB
EC2Credentials.py 1KB GoogleContainerClusterMonitoringEnabled.py 1KB
GoogleContainerClusterMonitoringEnabled.py 1KB GoogleContainerClusterDisableLegacyAuth.py 1KB
GoogleContainerClusterDisableLegacyAuth.py 1KB GoogleCloudDNSSECEnabled.py 1KB
GoogleCloudDNSSECEnabled.py 1KB StarActionPolicyDocument.py 1KB
StarActionPolicyDocument.py 1KB LambdaEnvironmentCredentials.py 1KB
LambdaEnvironmentCredentials.py 1KB EBSEncryption.py 1KB
EBSEncryption.py 1KB RDSPubliclyAccessible.py 1KB
RDSPubliclyAccessible.py 1KB AzureManagedDiscEncryption.py 1KB
AzureManagedDiscEncryption.py 1KB PasswordPolicyLowercaseLetter.py 1KB
PasswordPolicyLowercaseLetter.py 1KB PasswordPolicyUppercaseLetter.py 1KB
PasswordPolicyUppercaseLetter.py 1KB GoogleComputeMinTLSVersion.py 1KB
GoogleComputeMinTLSVersion.py 1KB PasswordPolicyLength.py 1KB
PasswordPolicyLength.py 1KB PasswordPolicyExpiration.py 1KB
PasswordPolicyExpiration.py 1KB GKEClusterLogging.py 1KB
GKEClusterLogging.py 1KB CloudtrailEncryption.py 1KB
CloudtrailEncryption.py 1KB S3PublicACL.py 1KB
S3PublicACL.py 1KB PasswordPolicyReuse.py 1KB
PasswordPolicyReuse.py 1KB SagemakerEncryption.py 1KB
SagemakerEncryption.py 1KB PasswordPolicySymbol.py 1KB
PasswordPolicySymbol.py 1KB PasswordPolicyNumber.py 1KB
PasswordPolicyNumber.py 1KB IAMPolicyAttachedToGroupOrRoles.py 1018B
IAMPolicyAttachedToGroupOrRoles.py 1018B SQSQueueEncryption.py 1005B
SQSQueueEncryption.py 1005B SNSTopicEncryption.py 1004B
SNSTopicEncryption.py 1004B locals_context_parser.py 1001B
locals_context_parser.py 1001B CloudtrailEncryption.py 955B
CloudtrailEncryption.py 955B S3AccessLogs.py 943B
S3AccessLogs.py 943B base_resource_value_check.py 921B
base_resource_value_check.py 921B S3MFADelete.py 894B
S3MFADelete.py 894B GoogleCloudSqlBackupConfiguration.py 893B
GoogleCloudSqlBackupConfiguration.py 893B ECRImmutableTags.py 849B
ECRImmutableTags.py 849B ElasticacheReplicationGroupEncryptionAtTransit.py 754B
ElasticacheReplicationGroupEncryptionAtTransit.py 754B ElasticacheReplicationGroupEncryptionAtRest.py 744B
ElasticacheReplicationGroupEncryptionAtRest.py 744B共 169 条
- 1
- 2
资源评论

挣扎的蓝藻
- 粉丝: 13w+
- 资源: 15万+
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
