[](#)
[](https://bridgecrew.io/?utm_source=github&utm_medium=organic_oss&utm_campaign=checkov)
[](https://github.com/bridgecrewio/checkov/actions?query=workflow%3Abuild)
[](https://github.com/bridgecrewio/checkov/actions?query=event%3Apush+branch%3Amaster+workflow%3Asecurity)
[](https://github.com/bridgecrewio/checkov/actions?query=workflow%3Acoverage)
[](https://www.checkov.io/1.Welcome/What%20is%20Checkov.html?utm_source=github&utm_medium=organic_oss&utm_campaign=checkov)
[](https://pypi.org/project/checkov/)
[](#)
[](#)
[](https://pepy.tech/project/checkov)
[](https://slack.bridgecrew.io/?utm_source=github&utm_medium=organic_oss&utm_campaign=checkov)
**Checkov** is a static code analysis tool for infrastructure-as-code.
It scans cloud infrastructure provisioned using [Terraform](https://terraform.io/), Terraform plan, [Cloudformation](https://aws.amazon.com/cloudformation/), [Kubernetes](https://kubernetes.io/), [Dockerfile](https://www.docker.com/), [Serverless](https://www.serverless.com/) or [ARM Templates](https://docs.microsoft.com/en-us/azure/azure-resource-manager/templates/overview) and detects security and compliance misconfigurations using graph-based scanning.
Checkov also powers [**Bridgecrew**](https://bridgecrew.io/?utm_source=github&utm_medium=organic_oss&utm_campaign=checkov), the developer-first platform that codifies and streamlines cloud security throughout the development lifecycle. Bridgecrew identifies, fixes, and prevents misconfigurations in cloud resources and infrastructure-as-code files.
<a href="https://www.bridgecrew.cloud/login/signUp/?utm_campaign=checkov-github-repo&utm_source=github.com&utm_medium=get-started-button" title="Try_Bridgecrew">
<img src="https://dabuttonfactory.com/button.png?t=Try+Bridgecrew&f=Open+Sans-Bold&ts=26&tc=fff&hp=45&vp=20&c=round&bgt=unicolored&bgc=662eff" align="right" width="120">
</a>
<a href="https://docs.bridgecrew.io?utm_campaign=checkov-github-repo&utm_source=github.com&utm_medium=read-docs-button" title="Docs">
<img src="https://dabuttonfactory.com/button.png?t=Read+the+Docs&f=Open+Sans-Bold&ts=26&tc=fff&hp=45&vp=20&c=round&bgt=unicolored&bgc=662eff" align="right" width="120">
</a>
## **Table of contents**
- [Features](#features)
- [Screenshots](#screenshots)
- [Getting Started](#getting-started)
- [Disclaimer](#disclaimer)
- [Support](#support)
## Features
* [Over 1000 built-in policies](docs/5.Policy%20Index/all.md) cover security and compliance best practices for AWS, Azure and Google Cloud.
* Scans Terraform, Terraform Plan, CloudFormation, Kubernetes, Dockerfile, Serverless framework and ARM template files.
* Supports Context-awareness policies based on in-memory graph-based scanning.
* Supports Python format for attribute policies and YAML format for both attribute and composite policies.
* Detects [AWS credentials](docs/2.Basics/Scanning%20Credentials%20and%20Secrets.md) in EC2 Userdata, Lambda environment variables and Terraform providers.
* [Identifies secrets](https://bridgecrew.io/blog/checkov-secrets-scanning-find-exposed-credentials-in-iac/) using regular expressions, keywords, and entropy based detection.
* Evaluates [Terraform Provider](https://registry.terraform.io/browse/providers) settings to regulate the creation, management, and updates of IaaS, PaaS or SaaS managed through Terraform.
* Policies support evaluation of [variables](docs/2.Basics/Handling%20Variables.md) to their optional default value.
* Supports in-line [suppression](docs/2.Basics/Suppressing%20and%20Skipping%20Policies.md) of accepted risks or false-positives to reduce recurring scan failures. Also supports global skip from using CLI.
* [Output](docs/2.Basics/Reviewing%20Scan%20Results.md) currently available as CLI, JSON, JUnit XML and github markdown and link to remediation [guides](https://docs.bridgecrew.io/docs/aws-policy-index).
## Screenshots
Scan results in CLI
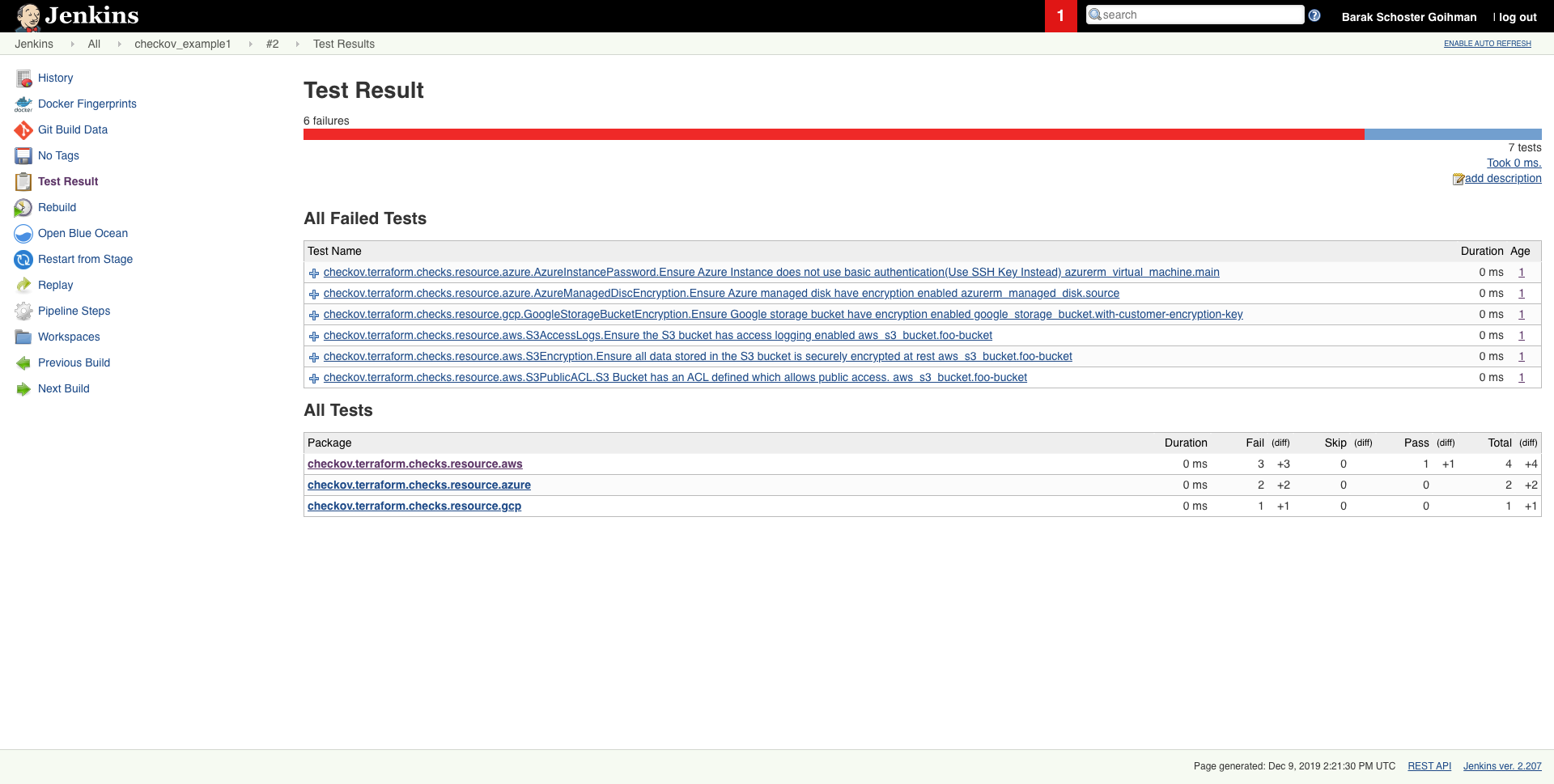
Scheduled scan result in Jenkins
## Getting started
### Requirements
* Python >= 3.7 (Data classes are available for Python 3.7+)
* Terraform >= 0.12
### Installation
```sh
pip3 install checkov
```
Installation on Alpine:
```sh
pip3 install --upgrade pip && pip3 install --upgrade setuptools
pip3 install checkov
```
Installation on Ubuntu 18.04 LTS:
Ubuntu 18.04 ships with Python 3.6. Install python 3.7 (from ppa repository)
```sh
sudo apt update
sudo apt install software-properties-common
sudo add-apt-repository ppa:deadsnakes/ppa
sudo apt install python3.7
sudo apt install python3-pip
sudo python3.7 -m pip install -U checkov #to install or upgrade checkov)
```
or using homebrew (MacOS only)
```sh
brew install checkov
```
or
```sh
brew upgrade checkov
```
### Upgrade
if you installed checkov with pip3
```sh
pip3 install -U checkov
```
### Configure an input folder or file
```sh
checkov --directory /user/path/to/iac/code
```
Or a specific file or files
```sh
checkov --file /user/tf/example.tf
```
Or
```sh
checkov -f /user/cloudformation/example1.yml -f /user/cloudformation/example2.yml
```
Or a terraform plan file in json format
```sh
terraform init
terraform plan -out tf.plan
terraform show -json tf.plan > tf.json
checkov -f tf.json
```
Note: `terraform show` output file `tf.json` will be single line.
For that reason all findings will be reported line number 0 by checkov
```sh
check: CKV_AWS_21: "Ensure all data stored in the S3 bucket have versioning enabled"
FAILED for resource: aws_s3_bucket.customer
File: /tf/tf.json:0-0
Guide: https://docs.bridgecrew.io/docs/s3_16-enable-versioning
```
If you have installed `jq` you can convert json file into multiple lines with the following command:
```sh
terraform show -json tf.plan | jq '.' > tf.json
```
Scan result would be much user friendly.
```sh
checkov -f tf.json
Check: CKV_AWS_21: "Ensure all data stored in the S3 bucket have versioning enabled"
FAILED for resource: aws_s3_bucket.customer
File: /tf/tf1.json:224-268
Guide: https://docs.bridgecrew.io/docs/s3_16-enable-versioning
225 | "values": {
226 | "acceleration_status": "",
227 | "acl": "private",
228 | "arn": "arn:aws:s3:::mybucket",
```
Alternatively, specify the repo root of the hcl files used to generate the plan file, using the `--repo-root-for-plan-enrichment` flag, to enrich the output with the appropriate file path, line numbers, and codeblock of the resource(s). An added benefit is that check suppressions will be handled accordingly.
```sh
checkov -f tf.json --repo-root-for-plan-enrichment /user/path/to/iac/code
```
### Scan result sample (CLI)
```sh
Passed Checks: 1, Failed Checks: 1, Suppressed Checks: 0
Check: "Ensure all data stored in the S3 bucket is securely encrypted at rest"
/main.tf:
Passed for resource: aws_s3_bucket.template_bucket
Check: "Ensure all data stored in the S3 bu
没有合适的资源?快使用搜索试试~ 我知道了~
温馨提示

共955个文件
py:944个
txt:4个
pkg-info:2个
资源分类:Python库 所属语言:Python 资源全名:checkov-2.0.364.tar.gz 资源来源:官方 安装方法:https://lanzao.blog.csdn.net/article/details/101784059
资源推荐
资源详情
资源评论
收起资源包目录
 Python库 | checkov-2.0.364.tar.gz (955个子文件)
Python库 | checkov-2.0.364.tar.gz (955个子文件)  setup.cfg 38B
setup.cfg 38B checkov 216B
checkov 216B checkov.cmd 1KB
checkov.cmd 1KB LICENSE 11KB
LICENSE 11KB README.md 16KB
README.md 16KB PKG-INFO 17KB
PKG-INFO 17KB PKG-INFO 17KB
PKG-INFO 17KB resources_types.py 51KB
resources_types.py 51KB parser.py 36KB
parser.py 36KB platform_integration.py 26KB
platform_integration.py 26KB local_graph.py 26KB
local_graph.py 26KB main.py 19KB
main.py 19KB runner.py 17KB
runner.py 17KB renderer.py 16KB
renderer.py 16KB runner.py 14KB
runner.py 14KB report.py 14KB
report.py 14KB local_graph.py 14KB
local_graph.py 14KB cfn_json.py 13KB
cfn_json.py 13KB cfn_json.py 12KB
cfn_json.py 12KB tf_plan_json.py 12KB
tf_plan_json.py 12KB parser.py 12KB
parser.py 12KB evaluate_terraform.py 12KB
evaluate_terraform.py 12KB runner.py 12KB
runner.py 12KB runner.py 12KB
runner.py 12KB utils.py 12KB
utils.py 12KB parser_utils.py 11KB
parser_utils.py 11KB context_parser.py 10KB
context_parser.py 10KB cfn_utils.py 9KB
cfn_utils.py 9KB base_parser.py 9KB
base_parser.py 9KB module.py 9KB
module.py 9KB base_check_registry.py 8KB
base_check_registry.py 8KB context_parser.py 8KB
context_parser.py 8KB blocks.py 8KB
blocks.py 8KB runner.py 8KB
runner.py 8KB runner_registry.py 8KB
runner_registry.py 8KB runner.py 8KB
runner.py 8KB runner.py 7KB
runner.py 7KB node.py 7KB
node.py 7KB node.py 7KB
node.py 7KB node.py 7KB
node.py 7KB generic_resource_encryption.py 7KB
generic_resource_encryption.py 7KB cfn_yaml.py 7KB
cfn_yaml.py 7KB safe_eval_functions.py 7KB
safe_eval_functions.py 7KB cfn_yaml.py 7KB
cfn_yaml.py 7KB suppressions_integration.py 6KB
suppressions_integration.py 6KB plan_runner.py 6KB
plan_runner.py 6KB record.py 6KB
record.py 6KB checks_parser.py 6KB
checks_parser.py 6KB parser_functions.py 6KB
parser_functions.py 6KB plan_parser.py 6KB
plan_parser.py 6KB base_resource_value_check.py 5KB
base_resource_value_check.py 5KB RootContainers.py 5KB
RootContainers.py 5KB multi_signature.py 5KB
multi_signature.py 5KB runner.py 5KB
runner.py 5KB secrets.py 4KB
secrets.py 4KB base_resource_value_check.py 4KB
base_resource_value_check.py 4KB RootContainersHighUID.py 4KB
RootContainersHighUID.py 4KB base_registry.py 4KB
base_registry.py 4KB base_registry.py 4KB
base_registry.py 4KB complex_connection_solver.py 4KB
complex_connection_solver.py 4KB AbsSecurityGroupUnrestrictedIngress.py 4KB
AbsSecurityGroupUnrestrictedIngress.py 4KB fixes_integration.py 4KB
fixes_integration.py 4KB base_resource_value_check.py 4KB
base_resource_value_check.py 4KB docs_generator.py 4KB
docs_generator.py 4KB Seccomp.py 4KB
Seccomp.py 4KB base_check.py 4KB
base_check.py 4KB base_runner.py 4KB
base_runner.py 4KB NSGRulePortAccessRestricted.py 4KB
NSGRulePortAccessRestricted.py 4KB wrapper.py 3KB
wrapper.py 3KB baseline.py 3KB
baseline.py 3KB connection_exists_solver.py 3KB
connection_exists_solver.py 3KB base_variable_evaluation.py 3KB
base_variable_evaluation.py 3KB registry_loader.py 3KB
registry_loader.py 3KB base_attribute_solver.py 3KB
base_attribute_solver.py 3KB context_parser.py 3KB
context_parser.py 3KB base_resource_negative_value_check.py 3KB
base_resource_negative_value_check.py 3KB runner_filter.py 3KB
runner_filter.py 3KB blocks.py 3KB
blocks.py 3KB GoogleCloudPostgreSqlLogMinMessage.py 3KB
GoogleCloudPostgreSqlLogMinMessage.py 3KB PostgreSQLServerLogCheckpointsEnabled.py 3KB
PostgreSQLServerLogCheckpointsEnabled.py 3KB docker_image_scanning_integration.py 3KB
docker_image_scanning_integration.py 3KB type_forcers.py 3KB
type_forcers.py 3KB registry.py 3KB
registry.py 3KB base_resource_negative_value_check.py 3KB
base_resource_negative_value_check.py 3KB registry.py 3KB
registry.py 3KB loader.py 3KB
loader.py 3KB setup.py 3KB
setup.py 3KB S3ProtectAgainstPolicyLockout.py 3KB
S3ProtectAgainstPolicyLockout.py 3KB graph_manager.py 3KB
graph_manager.py 3KB ElasticsearchNodeToNodeEncryption.py 3KB
ElasticsearchNodeToNodeEncryption.py 3KB get_git.py 3KB
get_git.py 3KB BaseCloudsplainingIAMCheck.py 3KB
BaseCloudsplainingIAMCheck.py 3KB custom_policies_integration.py 3KB
custom_policies_integration.py 3KB base_connection_solver.py 2KB
base_connection_solver.py 2KB ext_argument_parser.py 2KB
ext_argument_parser.py 2KB GoogleCloudSqlServerContainedDBAuthentication.py 2KB
GoogleCloudSqlServerContainedDBAuthentication.py 2KB versions_parser.py 2KB
versions_parser.py 2KB EC2PublicIP.py 2KB
EC2PublicIP.py 2KB GoogleCloudSqlServerCrossDBOwnershipChaining.py 2KB
GoogleCloudSqlServerCrossDBOwnershipChaining.py 2KB DockerSocketVolume.py 2KB
DockerSocketVolume.py 2KB共 955 条
- 1
- 2
- 3
- 4
- 5
- 6
- 10
资源评论

挣扎的蓝藻
- 粉丝: 13w+
- 资源: 15万+
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
