没有合适的资源?快使用搜索试试~ 我知道了~
ITRC-2023年度数据泄露报告
0 下载量 15 浏览量
2024-01-28
00:13:17
上传
评论
收藏 2.5MB PDF 举报
温馨提示

试读
41页
ITRC_2023年度数据泄露报告
资源推荐
资源详情
资源评论
JANUARY 2024

Table of Contents
A Letter from the CEO 02
Consumer & Business Resources 23
At-a-Glance Summary 05
Year-Over-Year 10
Top 10 Compromises in 2023 13
Total Annual Compromises
Since 2005 13
Compromises and Victims 10
Sensitive vs Non-Sensitive Data 11
Actionable vs Non-Actionable
Notices 12
2023 Analysis 09
Full Year 2023 26
Total Compromises, 2005-Present 25
Trends, 2018 – 2023 35
Data Map 38
Public Company vs Other Entity
Trends 37
Methodology 40
Q1 27
Total Compromises 35
By Sector 36
Q2 29
Attack Vectors 35
Q3 31
Top 5 Industries 36
Q4 33
Appendix 24
Uniform Breach Notices 19
Increased Due Diligence 21
Digital Credentials & Facial
Comparison Systems 20
Breach Alert for Business 22
Solutions 18
Trend 1: Supply Chain Attacks Grow 15
Trend 2: Data Breach Notice System
Flaws Emerge 16
Trends 14
Glossary of Terms 04
Executive Summary 06
© IDENTITY THEFT RESOURCE CENTER 2024 | IDTHEFTCENTER.ORG
1

A Letter from the CEO
On July 1, 2003, the world’s rst
law that required consumers to
be notied their personal
information had been
compromised in a data breach
went into effect in California.
The law only applied to
residents of the Golden State
and it was primarily aimed at
the risk of the time – the
exposure of personal
information stored in ling
cabinets and on disks and
drives. Dumpster diving and
stolen laptops were the top
sources of breaches.
While many businesses were aware of the new
law and the need to inform California residents
of a loss of their personally identiable
information (PII), most consumers were not.
Especially outside California.
That all changed in 2005 when a Georgia-based
company sent letters to a small group of
California consumers alerting them that their
PII had been obtained by a group of organized
criminals posing as legitimate businesses. On
Valentine’s Day, “Data Breach Notice” appeared
in the popular lexicon for the rst time.
That original notice not only generated intense
interest in California, but around the world.
Major media outlets in the U.S. and Europe
covered the story each day for 30 days and
Congress held a series of hearings on the topic
of data breaches. Soon, consumers outside
California were informed they, too, may have
been the victim of the data breach in
recognition that criminals and data did not
recognize state lines.
By the end of 2005, 156 other organizations had
issued breach notices tracked by the ITRC and
a handful of states adopted a California-style
breach notice law. Fast forward to 2018 when
the nal two states adopted breach notice
requirements, following the lead of 90 other
countries, all U.S. territories, and the District of
Columbia.
However, Congress did not enact a federal
breach notice law. Even in the wake of a single
2017 data breach linked to a Nation/State that
compromised the personal information of nearly
every adult in the U.S. and millions of adults in
other countries. The result was a patchwork of
state laws and federal regulations with different
denitions of PII, triggers for a notice, methods
of notication, time frames for issuing a notice,
and penalties for failing to issue a notice.
In the years between 2005 and 2018,
technology advanced and identity criminals’
skills improved. Paper documents in le cabinets
accessible in locked rooms were replaced by
cloud environments accessible via the internet.
Identity criminals shifted from lone individuals
hacking for fun and street cred in their parents’
basement to highly sophisticated groups
operating out of glass and stone towers in
far-away lands. Hollywood shows us people in
hoodies while the real identity criminals ash
cash, drive Lambos and operate call centers.
© IDENTITY THEFT RESOURCE CENTER 2024 | IDTHEFTCENTER.ORG
2
Eva Velasquez, CEO
Identity Theft Resource Center
January 2024
First, we must acknowledge the signicant
impact of Supply Chain Attacks and the effect
they have on all organizations. A single supply
chain attack can directly or indirectly impact
hundreds or thousands of businesses that rely on
the same vendor. Stronger reporting
requirements can help warn other vulnerable
businesses of the risk associated with a similar
attack. Increased due diligence when it comes to
vendors and data protection are also in order.
Second, the two-decade old legislative and
regulatory framework designed to alert
consumers to breaches is broken. A Supply Chain
Attack victim from 2020 conrmed in 2023 what
was suspected for years: Businesses under or
non-report breaches. We need to bring a level of
uniformity to the breach notice process to help
protect both consumers and business.
The sheer scale of the 2023 data compromises
is overwhelming. Just the increase from the past
record high to 2023’s number is larger than the
annual number of events from 2005 until 2020
(except for 2017). But, we cannot let
complacency, frustration, or weariness lead us
to surrender the ght to protect identity crime
victims. We’re not about to give-up or give-in and
we hope you will join us as we seek to start a
different conversation about protecting
identities in 2024.
Off-the-shelf hacker tools lowered the barrier
to entry for launching attacks and the wealth
of personal information available from data
breaches and identity scams made it easy to
impersonate an individual or business using
social engineering. This was the environment in
2021 that created the highest number of data
compromises ever tracked by the ITRC – 1,860
1
events impacted an estimated ~300M victims.
The highest, that is, until 2023.
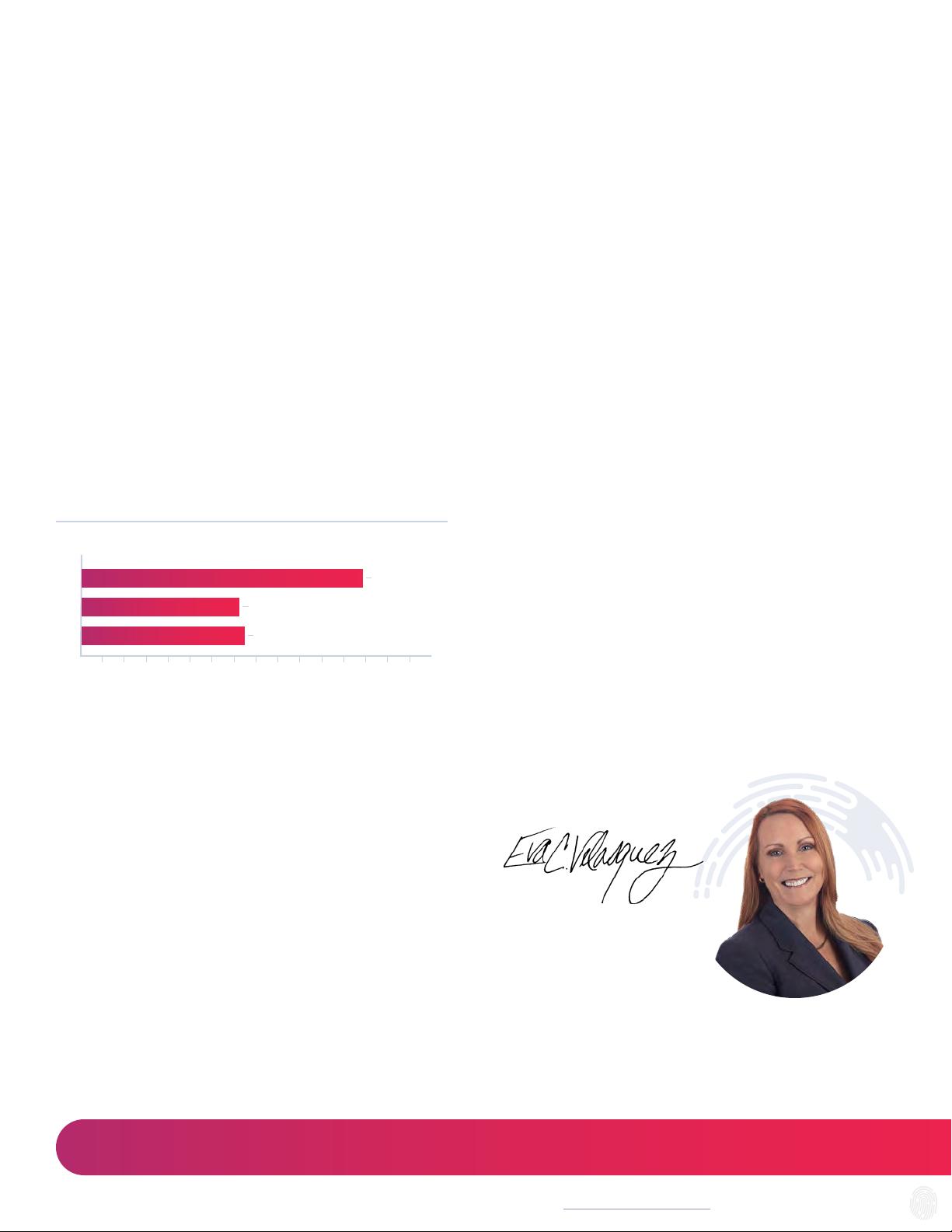
In the pages that follow you’ll see the new
record high: 3,205 publicly reported data
compromises that impacted an estimated
353,027,892 individuals. That’s a 72 percent
(72%) increase in events over the previous
high-water mark and 78 percent (78%) over
2022.
See Figure 1
Each year we are asked “why the increase in
events?” and “what can be done to protect
against a data breach?” There’s never any one
reason why compromises go up or down just as
there are no actions that are 100 percent
effective in stopping breaches or the identity
crimes that result. We do believe there are
trends that need to be highlighted and actions
that need to be considered if we are to slow or
stop the pace of data breaches and exposures.
1
Audits of 2021 and 2022 compromises resulted in a reduction in the total number of data compromises for those years due to breaches originally reported as separate
events later being updated as related events. The total number of compromises in full-year 2021 has been adjusted downward by two (2) events to 1,860 and full-year
2022 adjusted downward by one (1) event to 1,801.
Figure 1 | Total Compromises, Year over Year
0 2,250 4,0001,750 3,0001,250 2,5001,000750500250 2,000 3,250 3,7503,5001,500 2,750
2021
300,607,163 Victims
1,860
2022
425,212,090 Victims
1,801
2023
353,027,892 Victims
3,205
Compromises
© IDENTITY THEFT RESOURCE CENTER 2024 | IDTHEFTCENTER.ORG
3

Glossary of Terms
One of the issues that leads to confusion around
data compromises is the fact there is no single
denition or set of terms used to describe a
data breach that requires a notice in the U.S.
Since data breach notices are largely creatures
of state law, there are as many denitions and
trigger events as there are states, territories
and federal districts. Adding to the confusion,
Federal government agencies also have their
own set of terms and requirements for issuing a
data breach notice, many of which have recently
changed or are in the process of changing. (See
SEC, FTC and FCC rule changes announced in
2023.)
Since 2020, the ITRC has published the
denitions we use in compiling and publishing
this report. We have updated our terms for the
2023 report.
Data Compromise – The overall term used
to refer to events where personal
information is accessible by unauthorized
individuals and/or for unintended
purposes. This includes data breaches, data
exposures, and data leaks.
Identity Theft – Taking personally
identiable information (PII) as protected
by state or federal laws.
Identity Fraud – Using stolen personally
identiable information (PII).
Data Breach – When unauthorized
individuals access and/or remove
personal information from the place where
is it stored.
Identity Crimes – The overall term for a
wide variety of state and federal criminal
acts that are related to the theft and/or
misuse of personal information.
Data Exposure – When personal
information is available for access and/or
removal from the place where it is stored,
but there is no evidence the information
has been accessed by unauthorized
individuals. This typically involves
cloud-based data storage where
cybersecurity protections are incorrectly
congured or have not been applied.
Data Leak – When personal information
that is publicly available or willingly shared
on social media and represents no or low
risk when viewed as individual records;
however, when aggregated, the sheer
volume of personal information available in
a single database creates risk to the data
subjects and value for identity criminals
who specialize in social engineering and
phishing. When these databases are left
unprotected or otherwise made publicly
available, the ITRC classies these events
as Data Leaks.
© IDENTITY THEFT RESOURCE CENTER 2024 | IDTHEFTCENTER.ORG
4
剩余40页未读,继续阅读
资源评论

网络研究观
- 粉丝: 7452
- 资源: 2322
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
