没有合适的资源?快使用搜索试试~ 我知道了~
伯克利大学的计算机网络课程期中考试试卷。
资源推荐
资源详情
资源评论
University of California at Berkeley
College of Engineering
Department of Electrical Engineering and Computer Sciences
EE122
MIDTERM EXAMINATION
Thursday, 11 October 2012
Scott Shenker
INSTRUCTIONS—READ THEM NOW! This examination is CLOSED BOOK/CLOSED NOTES. You will
not require a calculator, iPhone®, laptop computer, or other calculation aid. Please put them away right
now! You MAY use one 8.5”x11” double-sided crib sheet, packed with notes, formulas, and diagrams (but
no smaller than 8pt font). All work should be done on the attached pages, and there are four blank pages
at the end for you to use as scratch paper. Don’t be scared off by the number of questions; many of them
are simple warm-up exercises, and you should have plenty of time to finish them all.
In general, if something is unclear, write down your assumptions as part of your answer. If your
assumptions are reasonable, we will endeavor to grade the question based on them. If necessary, of
course, you may raise your hand, and a TA or the instructor will come to you. Please try not to disturb the
students taking the examination around you.
Please write your SID on each page!
Name – Please Print!
(Signature)
SID
Discussion Section (Day/Time)
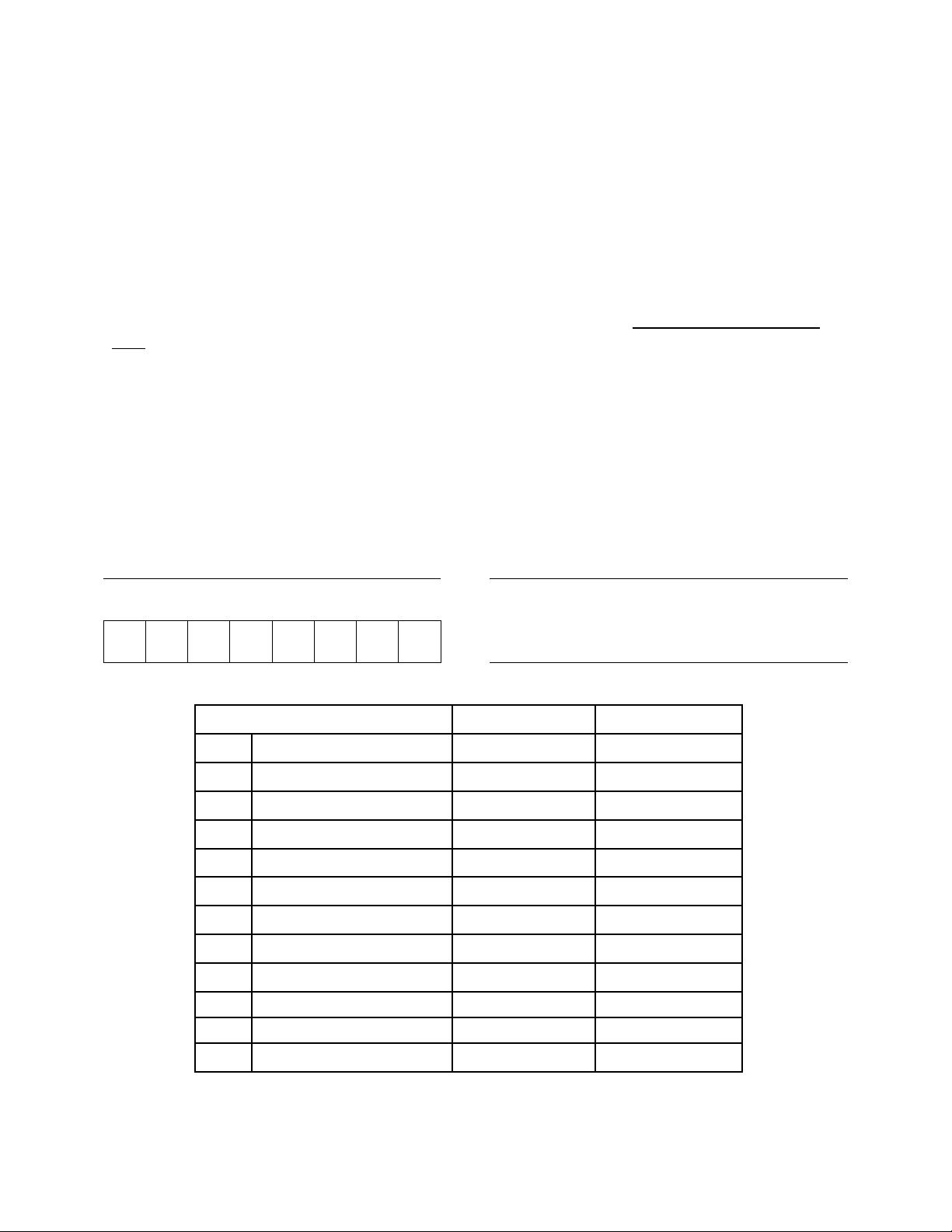
Question
Possible Points
Points Obtained
1
True or False
20
2
General Multiple-Choice
20
3
TCP Basics
10
4
Sequence of Messages
15
5
The Real World
6
6
Timer Values
8
7
Addressing
14
8
Learning Switch
12
9
DNS
4
10
Sliding Window
10
Bonus Questions
0.00001
Total
119.0001

SID
EE122 Midterm
October 11, 2012
- 2 -
Fun Facts to Remember
The IP header, without options, is 20 bytes
The TCP header, without options, is 20 bytes
The UDP header is 8 bytes.
1 TB = 10
12
bytes; 1 GB is 10
9
bytes; 1 MB is 10
6
bytes
1Gbps is 10
9
bits/sec; 1Mbps is 10
6
bits/sec
1 msec is 10
-3
seconds

SID
EE122 Midterm
October 11, 2012
- 3 -
1. True or False [20 points]
Pick one and only one answer for each statement (indicate by circling)
1.
T F
Poisoned reverse is used to ensure that packets flooded on a spanning tree do
not loop infinitely.
2.
T F
The fact that fragmentation reassembly is performed at end-hosts is a good
example of the end-to-end-principle.
3.
T F
Layering dictates that functionality should not be implemented in the network,
even if doing so leads to a significant performance improvement.
4.
T F
Fate sharing suggests that state should be stored on the entities that depend on
that state.
5.
T F
A reliable transport protocol must send packets in sequential order
6.
T F
Distance Vector involves global computation and local state, whereas Link State
Routing involves local computation and global state.
7.
T F
If your browser opens up two TCP connections to the same server, the server
can tell them apart because their arriving packets use different source transport
ports.
8.
T F
On a fast (100Gbps) cross-country link, propagation delay is usually the most
significant component of the end-to-end delay.
9.
T F
The size of an IPv4 packet header is always 20 bytes.
10.
T F
The size of an IPv4 packet header is usually 20 bytes.
11.
T F
Poisoned Reverse completely solves the Count-to-Infinity problem.
12.
T F
Routers only implement the physical, data-link and network layers
13.
T F
Hosts only implement the transport and application layers
14.
T F
DNS typically uses UDP rather than TCP
15.
T F
Everyone agrees on a single interpretation of the End-to-End Principle
16.
T F
A car carrying a 1TB disk from Berkeley to Stanford in an hour carries 1TB faster
than a 10Gbps link between Berkeley and Stanford.
17.
T F
Each TCP packet has a TCP header that either includes the sequence number
or the ACK number, but never includes both.
18.
T F
The UDP packet header has a sequence number field but no ACK field.
19.
T F
Packet switching uses bandwidth more efficiently than circuit switching
20.
T F
Circuit switching requires routers to remember each connection

SID
EE122 Midterm
October 11, 2012
- 4 -
2. General Multiple-Choice [20 points]
Pick one and only one answer for each question (indicate by circling)
1. The appropriate layer for implementing reliable transfer is:
a. The physical layer
b. The data link layer
c. The network layer
d. The transport layer
e. The application layer
2. A router running distance-vector routing knows:
a. Nothing
b. The entire network’s topology
c. The distance to destinations through its immediate neighbors
3. A router running link-state routing knows:
a. Nothing
b. The entire network’s topology
c. Only the distance to destinations through its immediate neighbors
4. Which of these fields does an IP router need to modify before sending a packet to the
next hop?
a. Source Address
b. Destination Address
c. Protocol
d. TTL
e. None of the above
5. Which of these fields in the IP header protect against corruption of the data payload?
a. TTL
b. Fragmentation flags
c. Protocol
d. Checksum
e. None of the above
6. Which of these fields does the UDP packet header have?
a. Source address
b. Destination address
c. Checksum
d. Protocol
e. None of the above

SID
EE122 Midterm
October 11, 2012
- 5 -
7. Which of these fields is present in IPv4, but not in IPv6?
a. Source Address
b. Destination Address
c. Fragmentation flags
d. Protocol/Next Header
e. None of the above
8. Which of these fields is present in IPv6, but not in IPv4?
a. Flow Identifier
b. Destination Address
c. Destination port
d. Protocol/Next Header
e. Checksum
9. Which one of the following apply to MAC addresses?
a. May be assigned dynamically
b. Used in the physical layer
c. Used in the data link layer
d. Used in the network layer
e. Hierarchical
10. Which one of the following apply to IP addresses?
a. May be assigned dynamically
b. Burned into the device
c. Used in the physical layer
d. Used in the data link layer
e. Always globally unique
11. Consider an IP packet (without options) with total length 1500 bytes. The packet is split
into fragments by a network that can only handle IP packets of up to 500 bytes. Which
set of IP packet lengths could describe the set of fragments?
a. 500, 500, 500
b. 400, 400, 400, 300
c. 420, 420, 420, 300
d. 500, 500, 500, 80
e. None of the above
12. Assuming circuit switching, if the network has allocated exactly enough bandwidth to
handle the application’s peak bandwidth P, and the application has average bandwidth
A, the level of utilization of that application’s circuit is given by (where / denotes division):
a. A/P
b. P/A
c. (P - A)/A
d. (P - A)/P
剩余25页未读,继续阅读
资源评论

小菜鸟bird
- 粉丝: 6
- 资源: 11
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

