没有合适的资源?快使用搜索试试~ 我知道了~
HPE MSA 106020602062 Storage Arrays Best Practices MSA存储最佳实践
需积分: 0 1 下载量 108 浏览量
2023-04-18
15:45:38
上传
评论
收藏 826KB PDF 举报
温馨提示

试读
23页
HPE MSA 1060 2060 2062 Storage Arrays Best Practices MSA存储最佳实践
资源推荐
资源详情
资源评论

Technical white paperTechnical white paper
HPE MSA 1060/2060/2062 Storage
Arrays
Best practices

Technical white paper
Contents
Executive summary.............................................................................................................................................................................................................................................................................................................. 3
Intended audience..........................................................................................................................................................................................................................................................................................................3
Connectivity best practices...........................................................................................................................................................................................................................................................................................3
Naming hosts ......................................................................................................................................................................................................................................................................................................................3
iSCSI.............................................................................................................................................................................................................................................................................................................................................3
MPIO............................................................................................................................................................................................................................................................................................................................................5
Maintaining supported configurations......................................................................................................................................................................................................................................................... 6
Best practices for maintaining system health.............................................................................................................................................................................................................................................. 6
Users ........................................................................................................................................................................................................................................................................................................................................... 6
Firmware..................................................................................................................................................................................................................................................................................................................................7
System monitoring .........................................................................................................................................................................................................................................................................................................9
Background scrubbing ...............................................................................................................................................................................................................................................................................................9
Data protection...............................................................................................................................................................................................................................................................................................................10
Periodic health checks.............................................................................................................................................................................................................................................................................................11
Storage best practices....................................................................................................................................................................................................................................................................................................11
Disk drives...........................................................................................................................................................................................................................................................................................................................11
Choosing disk group types..................................................................................................................................................................................................................................................................................12
Sparing ...................................................................................................................................................................................................................................................................................................................................13
Tiering.....................................................................................................................................................................................................................................................................................................................................16
Single vs. dual pools...................................................................................................................................................................................................................................................................................................18
Thin provisioning..........................................................................................................................................................................................................................................................................................................19
Full disk encryption.....................................................................................................................................................................................................................................................................................................20
Capacity expansion.....................................................................................................................................................................................................................................................................................................21
Volume mapping...........................................................................................................................................................................................................................................................................................................21
Summary.....................................................................................................................................................................................................................................................................................................................................23
Resources, contacts, or additional links....................................................................................................................................................................................................................................................23
Technical white paper Page 3
Executive summary
This paper provides guidance on configuring HPE MSA storage arrays to meet recommended best practices from Hewlett Packard
Enterprise. These recommendations help maximize application availability and performance, as well as improve system security. The paper is
not a user guide but complements other official documentation that explains MSA storage technology and how to configure array settings.
This best practices document focuses on providing clear recommendations and does not provide detailed information on the technologies it
references. Technology details in the best practices documents for previous generation arrays have migrated between the HPE MSA Gen6
Virtual Storage Technical Reference Guide and technology-specific documents found in the HPE Support Center.
Intended audience
This paper is for those tasked with the installation, configuration, and ongoing maintenance of HPE MSA storage systems. Additionally, this
paper will also assist technical sales staff in designing optimal solutions.
Connectivity best practices
Connectivity is the fundamental connection between devices. This section covers topics regarding the management network, data network,
and path management software.
Naming hosts
Best practices for naming hosts include:
•
Best practice
: Group initiators (IDs) as hosts and define friendly names for them.
– System default: None
– Detail: The default HPE MSA Storage Management Utility (SMU) (web-based user interface) behavior is to not allow the mapping of a
volume to a host without first creating a host of one or more initiators. Initiator names such as the World Wide Port Name (WWPN),
which is applicable to Fibre Channel and SAS, and the iSCSI Qualified Name (IQN), which is applicable to iSCSI, are composed of long
alphanumeric strings that are difficult to remember or recognize. Because it is possible to map volumes to initiators directly from within
the CLI, Hewlett Packard Enterprise recommends providing port-based naming, which follows meaningful device inventory naming
within an organization.
– Example: Host name: dl380_gen10_1
ID #1 Nickname: 10009cdc7172690a → dl380_gen10_1_port_0
ID #2 Nickname: 10009cdc71726909 → dl380_gen10_1_port_1
iSCSI
Best practices for configuring an iSCSI connection include:
•
Best practice
: Use three network ports per host.
– System default: None
Detail: To ensure isolation between management and application traffic, Hewlett Packard Enterprise recommends using separate
networks for management and iSCSI traffic. Additionally, at least two physical connections should provide connectivity to the data
networks. Actual network topography may vary depending on the use of VLANs and network switch virtualization.
Note
A host does not require connectivity to either management port to access data.
Technical white paper Page 4
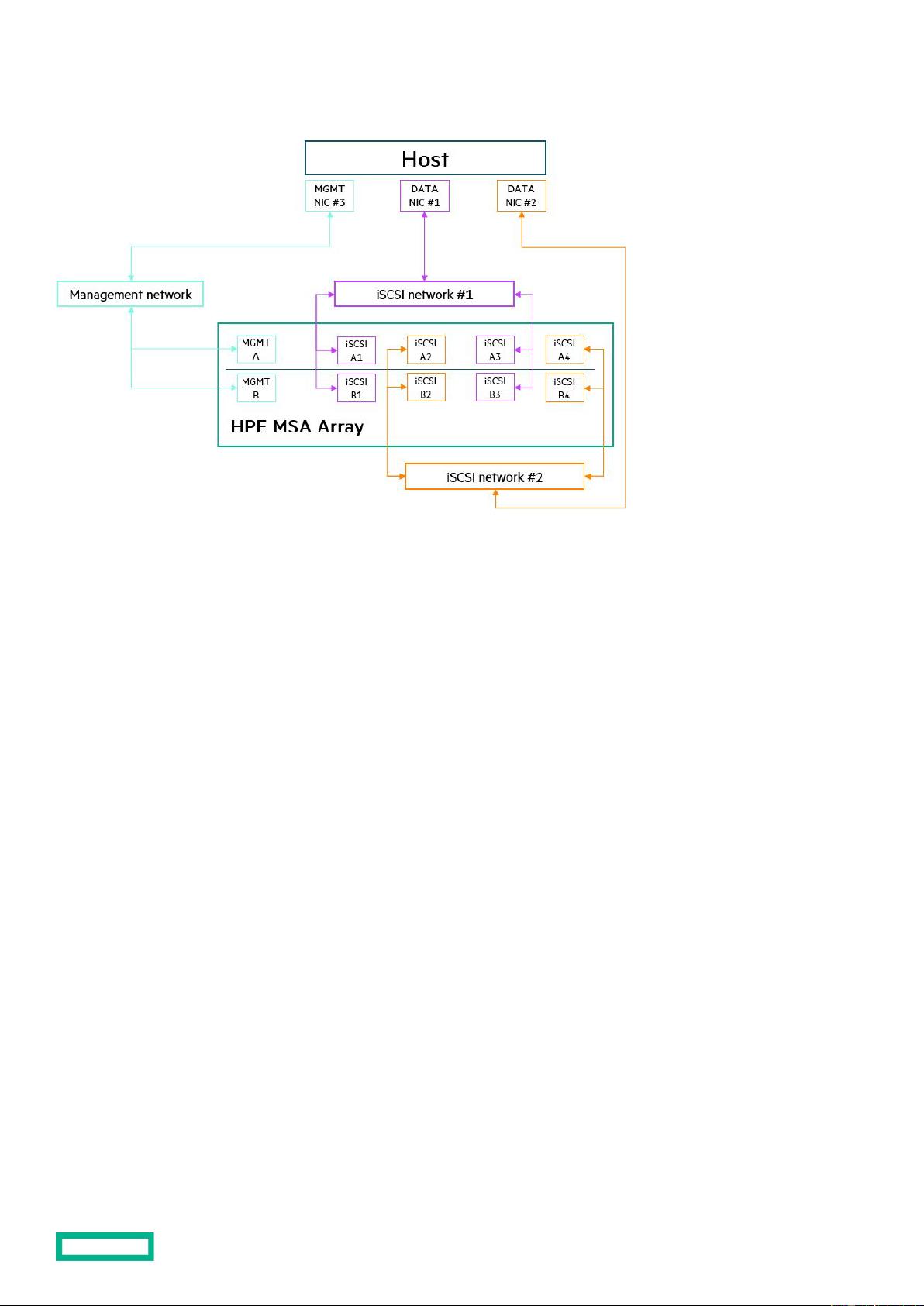
Figure 1. A sample iSCSI network topography
• Best practice: Use at least two isolated data networks when more than four array host ports are in use.
– System default: None
–
Detail
: To both maximize performance and minimize application disruption, Hewlett Packard Enterprise recommends not configuring
more than eight paths to a volume. The more paths configured, the longer the failover time can be when active paths are lost. Using
two networks limits an initiator to a maximum of eight paths to a volume (four active/optimized, four active/unoptimized).
– Example:
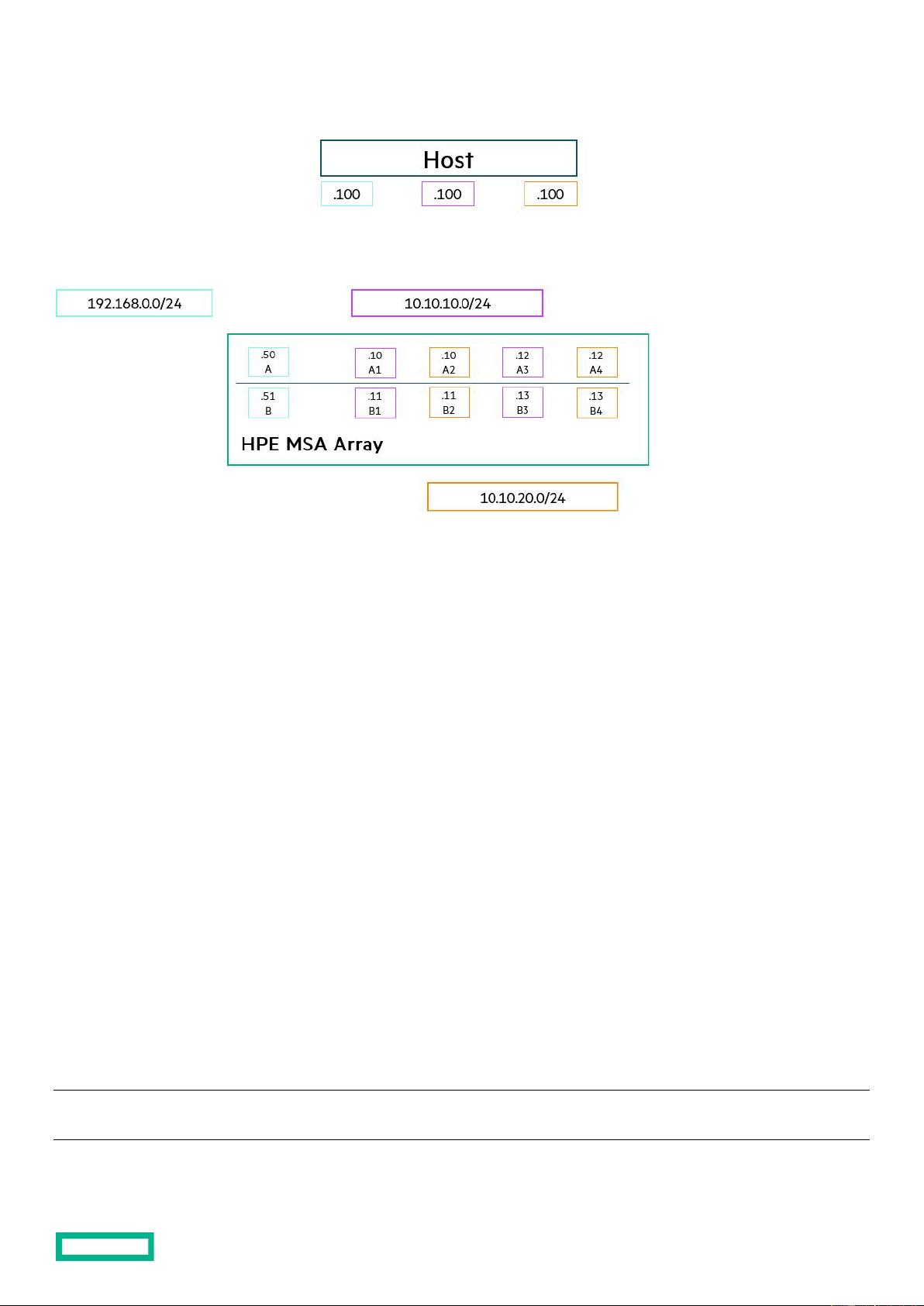
Controller A, Port 1 (A1): 10.10.10.10/24
Controller B, Port 1 (B1): 10.10.10.11/24
Controller A, Port 2 (A2): 10.10.20.10/24
Controller B, Port 2 (B2): 10.10.20.11/24
Controller A, Port 2 (A3): 10.10.10.12/24
Controller B, Port 2 (B3): 10.10.10.13/24
Controller A, Port 2 (A4): 10.10.20.12/24
Controller B, Port 2 (B4): 10.10.20.13/24
Host data NIC
1
#1: 10.10.10.100/24
Host data NIC #2: 10.10.20.100/24
1
Network interface card
Technical white paper Page 5
Figure 2. Example of iSCSI network subnet assignments
• Best practice: Set all devices on the same network to use jumbo frames when configured for an HPE MSA array.
– System default
: Disabled (MTU = 1,400)
– Detail
: Jumbo frames increase the maximum payload per Ethernet frame and can improve end-to-end performance. However, all
devices within the data path must also use jumbo frames to avoid packet fragmentation or loss. HPE MSA arrays advertise a jumbo
frame payload of 8,900 bytes. Sending devices usually agree with the MTU advertised by the receiver. If a device is unable to adjust its
MTU automatically, do so manually.
– Example
: Issuing this command in the MSA CLI enables jumbo frames:
set iscsi-parameters jumbo-frames enabled
MPIO
Best practices for configuring an MPIO connection include:
•
Best practice
: Install and configure multipath software on connected hosts.
– System default: Not installed
– Detail: Multipath software provides load balancing and tolerance to link failure between a host and a storage array. Without multipath
software, a volume mapped to a host appears as multiple physical disks, each with a single path. With multipath software, a volume can
appear as a single physical disk that has multiple paths. A path is a connection between an initiator (host bus adapter [HBA] port or
iSCSI software initiator) and a target (MSA array host port). When there are multiple active paths to the owning controller/pool for a
given volume, multipath software can improve performance by distributing traffic evenly among those paths.
– Example: Issuing the following commands in Windows Server PowerShell to enable MPIO with the HPE MSA 2060 storage array:
Install-WindowsFeature –name MultiPath-io
mpclaim –n –I –d “HPE MSA 2060 FC”
Note
There are five spaces between “HPE” and “MSA” in the sample command.
剩余22页未读,继续阅读
资源评论

lxf123416
- 粉丝: 0
- 资源: 7
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
