没有合适的资源?快使用搜索试试~ 我知道了~
Ti-SIP-Protocol-Structure
需积分: 10 7 下载量 110 浏览量
2009-09-08
09:14:30
上传
评论
收藏 280KB PDF 举报
温馨提示

试读
21页
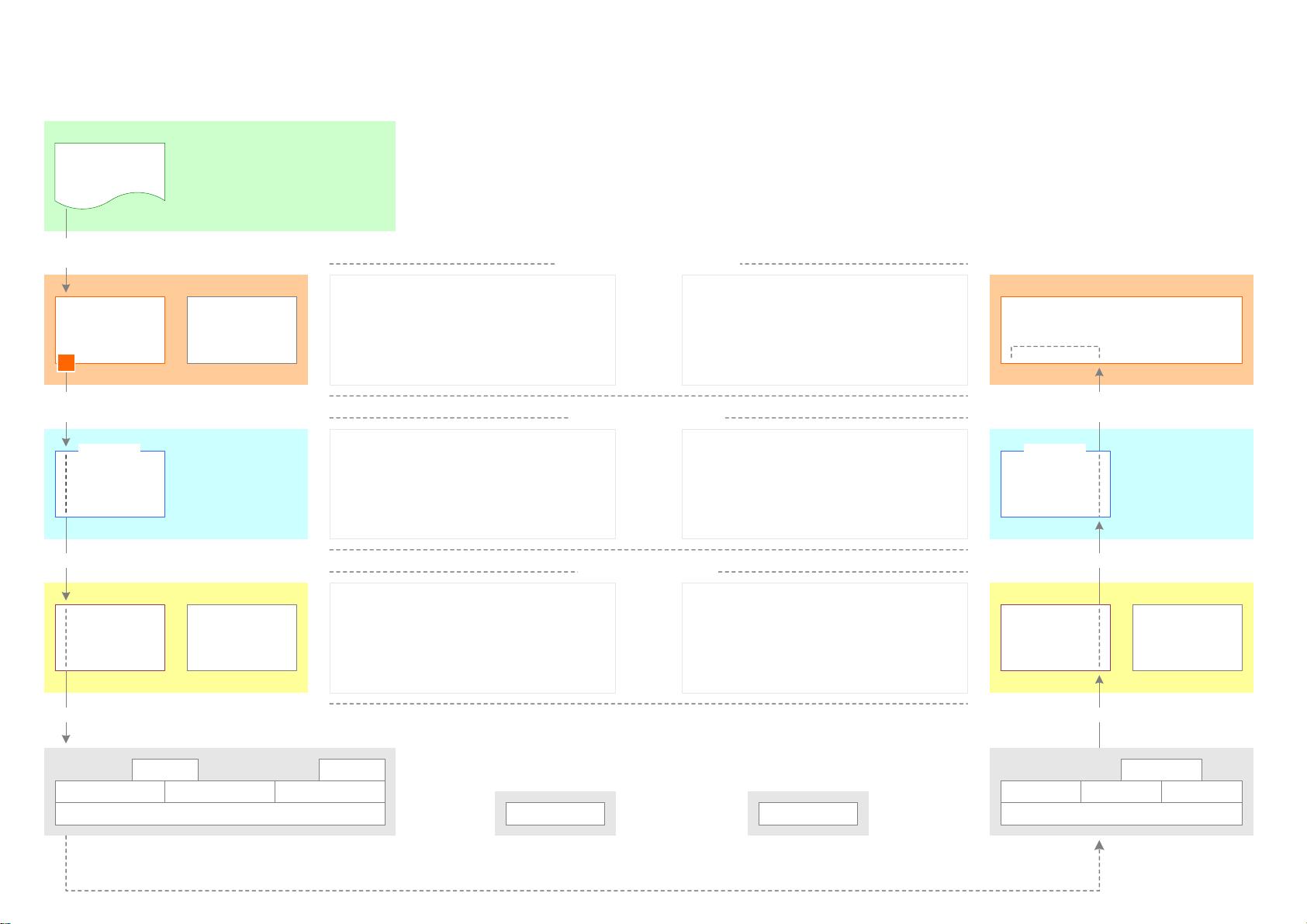
This example illustrates, as a slide show, the structure of the SIP protocol, as outlined in chapter 5 of RFC 3261
资源推荐
资源详情
资源评论

SIP Protocol Structure
through an Example
http://www.tech-invite.com
V2.2 – Nov 26, 2007
Initiating
UA
Proxy 1
(Stateful)
INVITE
100 Trying
INVITE
ACK
100 Trying
180 Ringing
180 Ringing
180 Ringing
200 OK
200 OK
200 OK
Copyright © 2005-2008 Joël Repiquet. All Rights Reserved. 21 pages
Proxy 3
(Stateful)
Responding
UA
Proxy 2
(Stateless)
INVITE
180 Ringing
200 OK
INVITE
407 Proxy
Authorization
Required
INVITE
ACK
ACK
ACK
BYE
BYE
BYE
200 OK
200 OK
200 OK
Media Session
This example illustrates, as a slide show, the
structure of the SIP protocol, as outlined in chapter
5 of RFC 3261:
"The lowest layer is the transport layer. It defines
how a client sends requests and receives responses
and how a server receives requests and sends
responses over the network. All SIP elements
contain a transport layer.
The second layer is the transaction layer. A
transaction is a request sent by a client transaction
(using the transport layer) to a server transaction,
along with all responses to that request sent from
the server transaction back to the client. Any task
that a user agent client (UAC) accomplishes takes
place using a series of transactions. Stateless
proxies do not contain a transaction layer.
The layer above the transaction layer is called the
transaction user (TU). Each of the SIP entities,
except the stateless proxy, is a transaction user."
Note: we set aside the syntax and encoding as the
lowest layer.
In this example, the rejection of the first INVITE
request, followed by a valid INVITE request,
enables the analysis of the processing of the ACK
for these two situations.
It is assumed that both Proxy 1 and Proxy 3
stateful proxy servers are in the final signalling
path because they requested it in the INVITE
requests they routed on.
1
2
3
5
4
4
4
5
4
6
6
6
6
7
7
7
7
8
8
8
x
x
x
y
y
y
TCPSCTP
TLS
IP
UDP
RTP
TCP SCTP
TLS
IP
UDP
IP IP
server
transaction
server
transport
client
transport
proxy core
UAS
core
UAC
core
client
transaction
client
transport
INVITE
request
request
Initiating UA
receive
request
Proxy 1
(Stateful)
Open
Session
INVITE
request
SDP
Offer
send
server
transport
Client Transport:
- before sending the request: insert the
'sent-by' parameter in the Via header field
Server Transport:
- when receiving the request: by
examining the 'sent-by' parameter in the
top Via header field, match it to the
relevant server transaction and add the
"received" parameter
The new "INVITE" client transaction
(state="calling") is identified by the CSeq
header field and the "branch" parameter of
the Via header field. T1 timer is started (if
UDP) before passing message request to
transport.
The UAC (User Agent Client) TU:
- creates the initial INVITE request
- creates a new client transaction (in the
transaction layer) and passes it the INVITE
message, plus the IP address, port and
transport
The new "INVITE" server transaction
(state="proceeding") is created by the
proxy core (not acting as TU). The server
transaction transmits the INVITE request
to the TU and somehow knows that this TU
will generate a response within 200ms: it
does not send back a 100 Trying response.
The proxy core TU first validates the
INVITE request. It cannot authenticate the
originator because no credentials are
provided. It rejects the request by sending
back (see next slide) a 407 (Proxy
Authentication Required) response.
INV/br-a0 INV/br-a1
SIP Transport Layer
SIP Transaction Layer
SIP Transaction User (TU)
1
SIP Protocol Structure through an Example (1)
http://www.tech-invite.com
Copyright © 2005-2008 Joël Repiquet. All Rights Reserved.

TCP SCTP
TLS
IP
UDPTCPSCTP
TLS
IP
UDP
RTP
server
transaction
server
transport
client
transport
proxy core
UAS
core
UAC
core
client
transaction
client
transport
ACK
(request)
Initiating UA
receive
request
Proxy 1
(Stateful)
ACK
response
send
server
transport
Client Transport:
- when receiving the response: match it to
the relevant client transaction by
examining 'sent-by' parameter in top Via
header field
- before sending the (ACK) request: insert
'sent-by' parameter in Via header field
Server Transport:
- before sending the response: retrieve
IP@ & port from 'sent-by' and "received"
- when receiving the (ACK) request: by
examining 'sent-by' parameter in top Via
header field, match it to relevant server
transaction + add "received" parameter
When receiving the 407 response, the
client transitions to state="completed",
passes the response up to the TU,
generates an ACK, and passes it to
transport. D timer started. When D timer
fires, the client transaction is destroyed.
The UAC analyses the response and
prepares a new INVITE request.
The server transaction enters the
"completed" state and passes the 407
response to transport.
When ACK (request) is received: passes to
"confirmed" state and starts I timer. When
I timer fires, the server transaction is
destroyed.
The proxy core TU:
sends back a 407 (Proxy Authentication
Required) response
INV/br-a0 INV/br-a0
SIP Transport Layer
SIP Transaction Layer
SIP Transaction User (TU)
receive
response
407
response
407
response
2
response
send
3
SIP Protocol Structure through an Example (2)
http://www.tech-invite.com
Copyright © 2005-2008 Joël Repiquet. All Rights Reserved.
IP IP

TCP SCTP
TLS
IP
UDPTCPSCTP
TLS
IP
UDP
RTP
server
transaction
server
transport
client
transport
proxy core
UAS
core
UAC
core
client
transaction
client
transport
INVITE
request
request
Initiating UA
receive
request
Proxy 1
(Stateful)
INVITE
request
receive
response
100
(Trying)
100 (Trying)
response
sendsend
server
transport
The new "INVITE" client transaction
(state="calling") is identified by CSeq
header field and "branch" parameter of Via
header field. T1 timer started (if UDP)
before passing message request to
transport. When receiving 1xx response:
state="proceeding" and T1 reset.
The UAC (User Agent Client) TU:
(1) creates the new INVITE request
containing the correct credentials
(2) creates a new client transaction and
passes it the INVITE message, plus the IP
address, port and transport
The new "INVITE" server transaction
(identified by CSeq header field and
"branch" parameter of Via header field) is
created by proxy core (not acting as TU).
The server transaction sends back a 100
Trying response and transmits the INVITE
request to proxy core (acting as TU).
The proxy core TU:
(1) validates the request
(2) determines the target for the request
(3) forwards the request (see next slide)
towards the target
INV/br-a1 INV/br-a1
4
SIP Transport Layer
SIP Transaction Layer
SIP Transaction User (TU)
Client & Server Transport main behavior, whatever the system:
Server: (1) when receiving a request: by examining
'sent-by' parameter in top Via header field, match it
to relevant server transaction + add "received"
parameter; (2) before sending a response: retrieve
IP@ and port from 'sent-by' and "received"
Client: (1) before sending a request: insert
'sent-by' parameter in Via header field
(2) when receiving a response: match it to
relevant client transaction by examining
'sent-by' parameter in top Via header field
SIP Protocol Structure through an Example (3)
http://www.tech-invite.com
Copyright © 2005-2008 Joël Repiquet. All Rights Reserved.
IP IP
5

TCP SCTP
TLS
IP
UDPTCP SCTP
TLS
IP
UDPTCP SCTP
TLS
IP
UDP
proxy core
server
transaction
client
transport
server
transport
server
transport
client
transport
client
transport
server
transport
proxy core
server
transaction
client
transaction
Proxy 1
(Stateful)
Proxy 3
(Stateful)
proxy core
receive
request
INVITE
request
request
send
Proxy 2
(Stateless)
send
receive
INVITE
request
request
request
receive
send
response
100 (Trying)
response
INV/br-x10 INV/br-x10INV/br-a1
For forwarding the INVITE
request, the proxy core
creates a new client
transaction
The proxy core TU:
(1) validates the request
(2) determines the target for
the request
(3) forwards the request (see
next slide) towards the
target
There is no Transaction
Management with a stateless
proxy
SIP Protocol Structure through an Example (4)
http://www.tech-invite.com
Copyright © 2005-2008 Joël Repiquet. All Rights Reserved.
IP IP
4
5
剩余20页未读,继续阅读
资源评论

leezen
- 粉丝: 0
- 资源: 5
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
