没有合适的资源?快使用搜索试试~ 我知道了~
NIST正式发布网络安全框架 2.0最终版:相比之前两个版本的六大重大变化
需积分: 5 1 下载量 150 浏览量
2024-02-29
15:03:50
上传
评论
收藏 803KB PDF 举报
温馨提示
2月26日美国国家标准与技术研究院 (NIST) 正式发布了更新后的网络安全框架 (CSF),这是其降低网络安全风险的里程碑式指导文件。新的 2.0 版本专为所有行业部门和组织类型而设计,从最小的学校和非营利组织到最大的机构和公司,无论其网络安全的复杂程度如何。 (详细信息和相关资源下载可以访问:https://www.nist.gov/cyberframework)
资源推荐
资源详情
资源评论
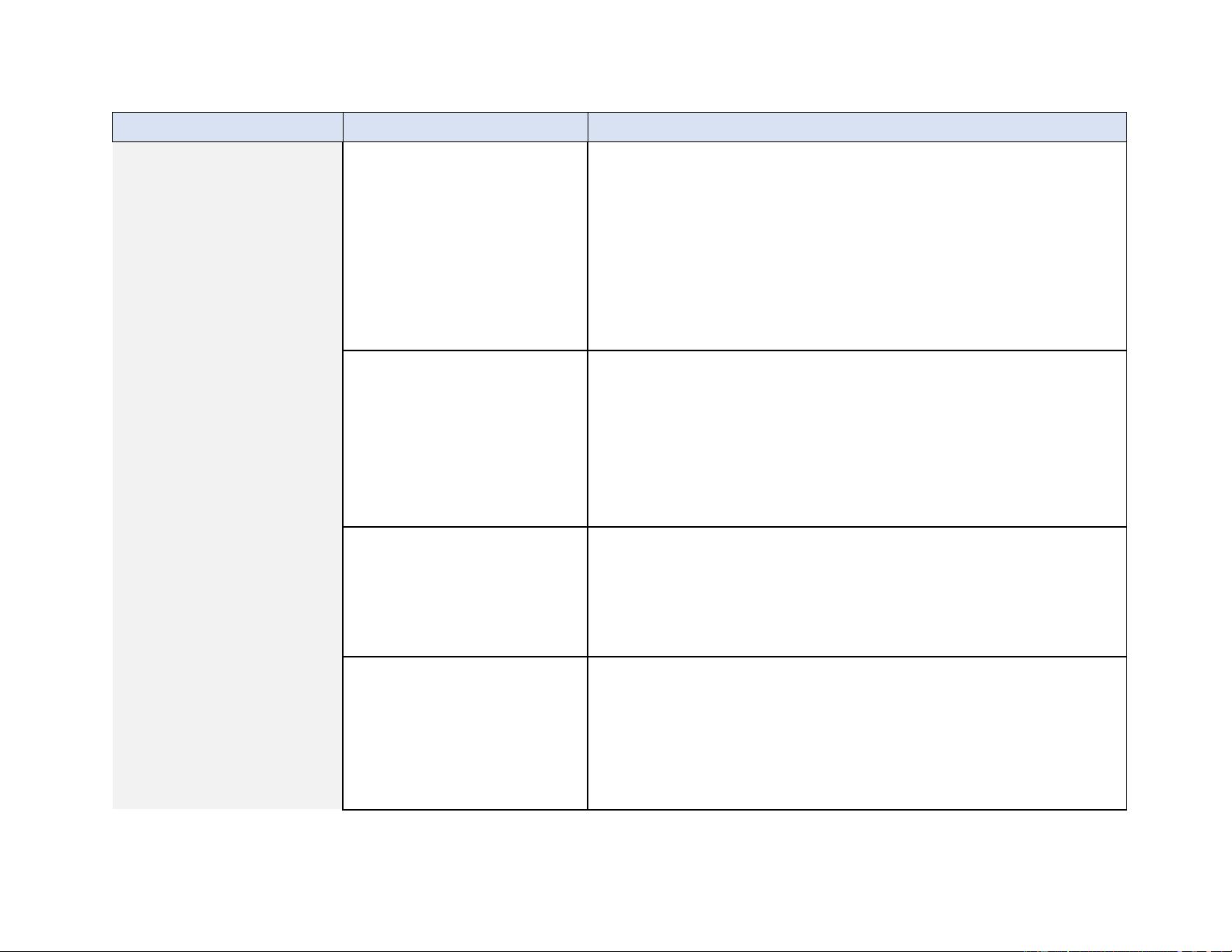
NIST CSF 2.0 Implementation Examples
1
NIST CSF 2.0 Implementation Examples
February 26, 2024
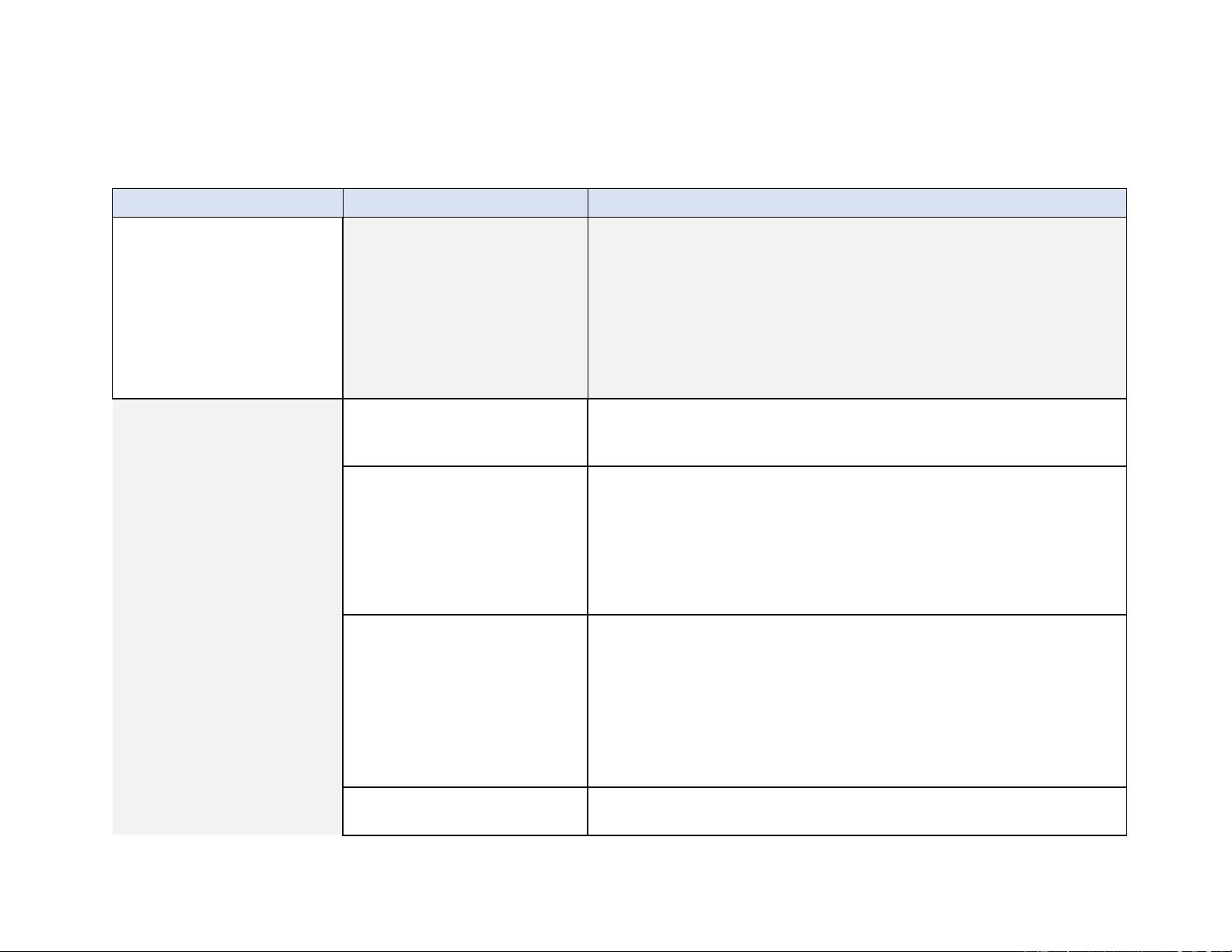
Category
Subcategory
Implementation Examples
Organizational Context (GV.OC):
The circumstances — mission,
stakeholder expectations,
dependencies, and legal,
regulatory, and contractual
requirements — surrounding the
organization’s cybersecurity risk
management decisions are
understood
GV.OC-01: The organizational
mission is understood and informs
cybersecurity risk management
Ex1: Share the organization’s mission (e.g., through vision and mission
statements, marketing, and service strategies) to provide a basis for identifying
risks that may impede that mission
GV.OC-02: Internal and external
stakeholders are understood, and
their needs and expectations
regarding cybersecurity risk
management are understood and
considered
Ex1: Identify relevant internal stakeholders and their cybersecurity-related
expectations (e.g., performance and risk expectations of officers, directors, and
advisors; cultural expectations of employees)
Ex2: Identify relevant external stakeholders and their cybersecurity-related
expectations (e.g., privacy expectations of customers, business expectations of
partnerships, compliance expectations of regulators, ethics expectations of
society)
GV.OC-03: Legal, regulatory, and
contractual requirements regarding
cybersecurity — including privacy
and civil liberties obligations — are
understood and managed
Ex1: Determine a process to track and manage legal and regulatory requirements
regarding protection of individuals’ information (e.g., Health Insurance Portability
and Accountability Act, California Consumer Privacy Act, General Data Protection
Regulation)
Ex2: Determine a process to track and manage contractual requirements for
cybersecurity management of supplier, customer, and partner information
Ex3: Align the organization’s cybersecurity strategy with legal, regulatory, and
contractual requirements
GV.OC-04: Critical objectives,
capabilities, and services that
Ex1: Establish criteria for determining the criticality of the organization's
capabilities and services as viewed by internal and external stakeholders
NIST CSF 2.0 Implementation Examples
2
Category
Subcategory
Implementation Examples
stakeholders depend on or expect
from the organization are
understood and communicated
Ex2: Determine (e.g., from a business impact analysis) assets and business
operations that are vital to achieving mission objectives and the potential impact
of a loss (or partial loss) of such operations
Ex3: Establish and communicate resilience objectives (e.g., recovery time
objectives) for delivering critical capabilities and services in various operating
states (e.g., under attack, during recovery, normal operation)
GV.OC-05: Outcomes, capabilities,
and services that the organization
depends on are understood and
communicated
Ex1: Create an inventory of the organization’s dependencies on external
resources (e.g., facilities, cloud-based hosting providers) and their relationships to
organizational assets and business functions
Ex2: Identify and document external dependencies that are potential points of
failure for the organization’s critical capabilities and services, and share that
information with appropriate personnel
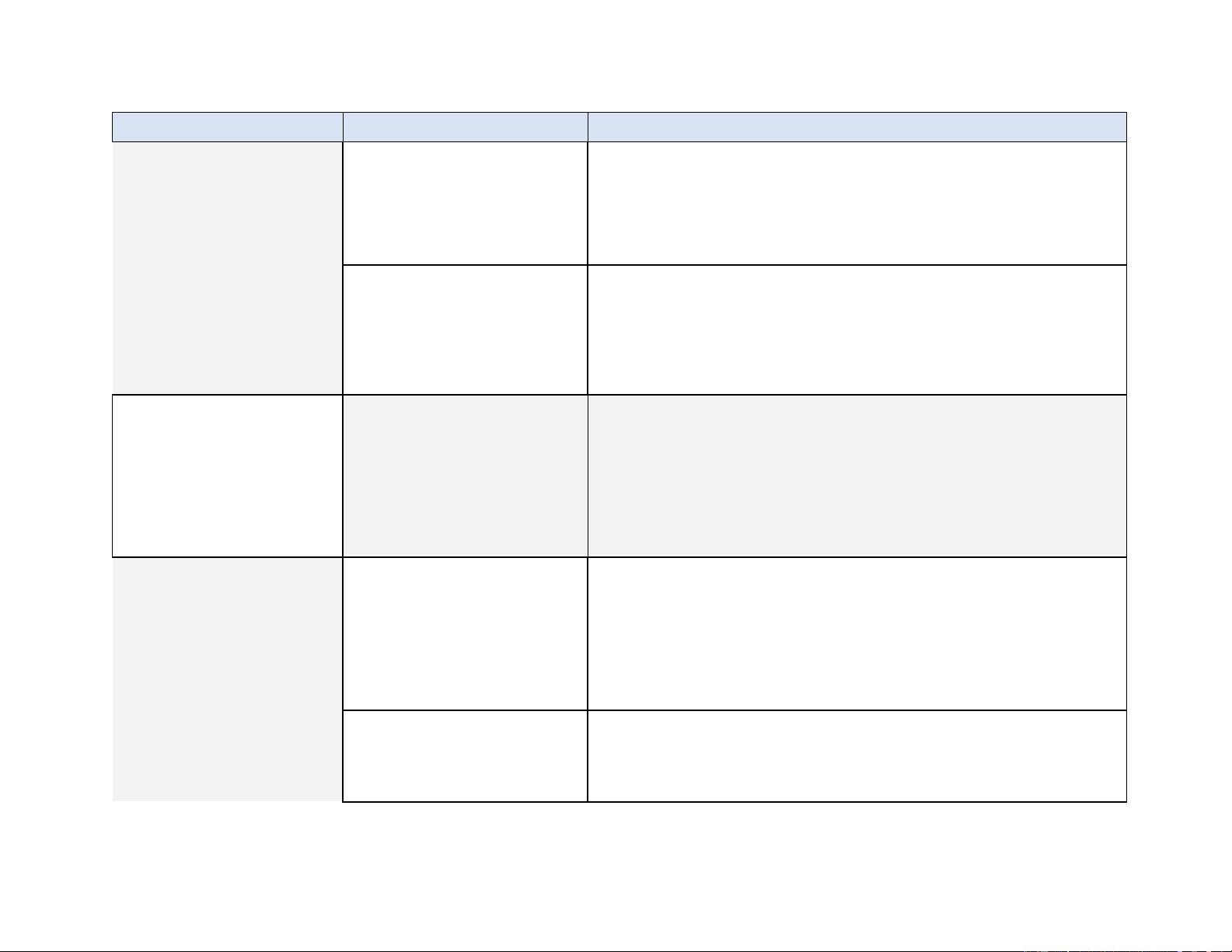
Risk Management Strategy
(GV.RM): The organization’s
priorities, constraints, risk
tolerance and appetite
statements, and assumptions are
established, communicated, and
used to support operational risk
decisions
GV.RM-01: Risk management
objectives are established and
agreed to by organizational
stakeholders
Ex1: Update near-term and long-term cybersecurity risk management objectives
as part of annual strategic planning and when major changes occur
Ex2: Establish measurable objectives for cybersecurity risk management (e.g.,
manage the quality of user training, ensure adequate risk protection for industrial
control systems)
Ex3: Senior leaders agree about cybersecurity objectives and use them for
measuring and managing risk and performance
GV.RM-02: Risk appetite and risk
tolerance statements are
established, communicated, and
maintained
Ex1: Determine and communicate risk appetite statements that convey
expectations about the appropriate level of risk for the organization
Ex2: Translate risk appetite statements into specific, measurable, and broadly
understandable risk tolerance statements
NIST CSF 2.0 Implementation Examples
3
Category
Subcategory
Implementation Examples
Ex3: Refine organizational objectives and risk appetite periodically based on
known risk exposure and residual risk
GV.RM-03: Cybersecurity risk
management activities and
outcomes are included in
enterprise risk management
processes
Ex1: Aggregate and manage cybersecurity risks alongside other enterprise risks
(e.g., compliance, financial, operational, regulatory, reputational, safety)
Ex2: Include cybersecurity risk managers in enterprise risk management planning
Ex3: Establish criteria for escalating cybersecurity risks within enterprise risk
management
GV.RM-04: Strategic direction that
describes appropriate risk response
options is established and
communicated
Ex1: Specify criteria for accepting and avoiding cybersecurity risk for various
classifications of data
Ex2: Determine whether to purchase cybersecurity insurance
Ex3: Document conditions under which shared responsibility models are
acceptable (e.g., outsourcing certain cybersecurity functions, having a third party
perform financial transactions on behalf of the organization, using public cloud-
based services)
GV.RM-05: Lines of communication
across the organization are
established for cybersecurity risks,
including risks from suppliers and
other third parties
Ex1: Determine how to update senior executives, directors, and management on
the organization’s cybersecurity posture at agreed-upon intervals
Ex2: Identify how all departments across the organization — such as
management, operations, internal auditors, legal, acquisition, physical security,
and HR — will communicate with each other about cybersecurity risks
GV.RM-06: A standardized method
for calculating, documenting,
categorizing, and prioritizing
cybersecurity risks is established
and communicated
Ex1: Establish criteria for using a quantitative approach to cybersecurity risk
analysis, and specify probability and exposure formulas
Ex2: Create and use templates (e.g., a risk register) to document cybersecurity
risk information (e.g., risk description, exposure, treatment, and ownership)
Ex3: Establish criteria for risk prioritization at the appropriate levels within the
enterprise
Ex4: Use a consistent list of risk categories to support integrating, aggregating,
and comparing cybersecurity risks
GV.RM-07: Strategic opportunities
(i.e., positive risks) are
characterized and are included in
Ex1: Define and communicate guidance and methods for identifying
opportunities and including them in risk discussions (e.g., strengths, weaknesses,
opportunities, and threats [SWOT] analysis)
Ex2: Identify stretch goals and document them
NIST CSF 2.0 Implementation Examples
4
Category
Subcategory
Implementation Examples
organizational cybersecurity risk
discussions
Ex3: Calculate, document, and prioritize positive risks alongside negative risks
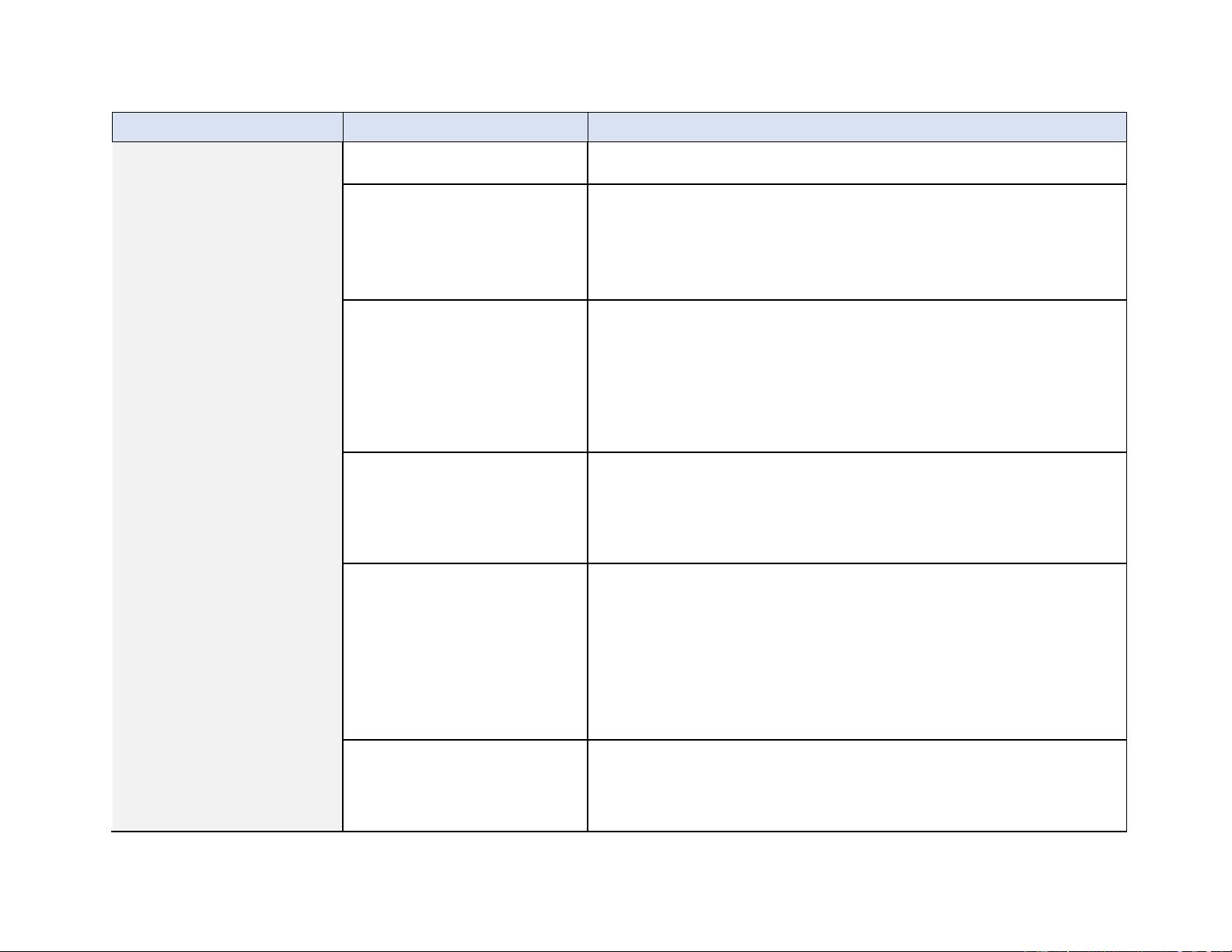
Cybersecurity Supply Chain Risk
Management (GV.SC): Cyber
supply chain risk management
processes are identified,
established, managed,
monitored, and improved by
organizational stakeholders
GV.SC-01: A cybersecurity supply
chain risk management program,
strategy, objectives, policies, and
processes are established and
agreed to by organizational
stakeholders
Ex1: Establish a strategy that expresses the objectives of the cybersecurity supply
chain risk management program
Ex2: Develop the cybersecurity supply chain risk management program, including
a plan (with milestones), policies, and procedures that guide implementation and
improvement of the program, and share the policies and procedures with the
organizational stakeholders
Ex3: Develop and implement program processes based on the strategy,
objectives, policies, and procedures that are agreed upon and performed by the
organizational stakeholders
Ex4: Establish a cross-organizational mechanism that ensures alignment between
functions that contribute to cybersecurity supply chain risk management, such as
cybersecurity, IT, operations, legal, human resources, and engineering
GV.SC-02: Cybersecurity roles and
responsibilities for suppliers,
customers, and partners are
established, communicated, and
coordinated internally and
externally
Ex1: Identify one or more specific roles or positions that will be responsible and
accountable for planning, resourcing, and executing cybersecurity supply chain
risk management activities
Ex2: Document cybersecurity supply chain risk management roles and
responsibilities in policy
Ex3: Create responsibility matrixes to document who will be responsible and
accountable for cybersecurity supply chain risk management activities and how
those teams and individuals will be consulted and informed
Ex4: Include cybersecurity supply chain risk management responsibilities and
performance requirements in personnel descriptions to ensure clarity and
improve accountability
NIST CSF 2.0 Implementation Examples
5
Category
Subcategory
Implementation Examples
Ex5: Document performance goals for personnel with cybersecurity risk
management-specific responsibilities, and periodically measure them to
demonstrate and improve performance
Ex6: Develop roles and responsibilities for suppliers, customers, and business
partners to address shared responsibilities for applicable cybersecurity risks, and
integrate them into organizational policies and applicable third-party agreements
Ex7: Internally communicate cybersecurity supply chain risk management roles
and responsibilities for third parties
Ex8: Establish rules and protocols for information sharing and reporting
processes between the organization and its suppliers
GV.SC-03: Cybersecurity supply
chain risk management is
integrated into cybersecurity and
enterprise risk management, risk
assessment, and improvement
processes
Ex1: Identify areas of alignment and overlap with cybersecurity and enterprise
risk management
Ex2: Establish integrated control sets for cybersecurity risk management and
cybersecurity supply chain risk management
Ex3: Integrate cybersecurity supply chain risk management into improvement
processes
Ex4: Escalate material cybersecurity risks in supply chains to senior management,
and address them at the enterprise risk management level
GV.SC-04: Suppliers are known and
prioritized by criticality
Ex1: Develop criteria for supplier criticality based on, for example, the sensitivity
of data processed or possessed by suppliers, the degree of access to the
organization’s systems, and the importance of the products or services to the
organization’s mission
Ex2: Keep a record of all suppliers, and prioritize suppliers based on the criticality
criteria
GV.SC-05: Requirements to address
cybersecurity risks in supply chains
are established, prioritized, and
integrated into contracts and other
types of agreements with suppliers
and other relevant third parties
Ex1: Establish security requirements for suppliers, products, and services
commensurate with their criticality level and potential impact if compromised
Ex2: Include all cybersecurity and supply chain requirements that third parties
must follow and how compliance with the requirements may be verified in default
contractual language
Ex3: Define the rules and protocols for information sharing between the
organization and its suppliers and sub-tier suppliers in agreements
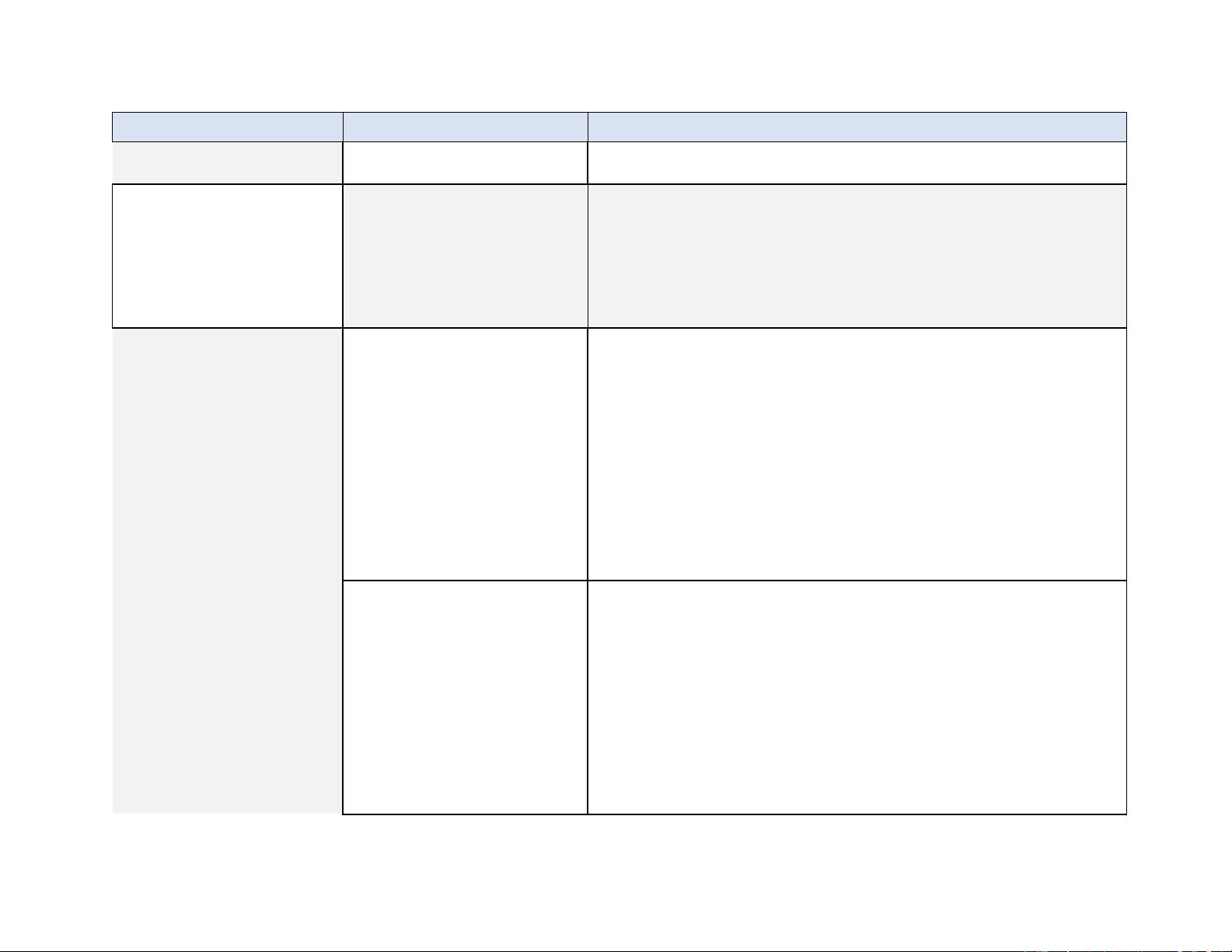
剩余29页未读,继续阅读
资源评论

lurenjia404
- 粉丝: 3369
- 资源: 145
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功