没有合适的资源?快使用搜索试试~ 我知道了~
Gartner发布安全运营中心(SOC)模型指南
需积分: 5 3 下载量 5 浏览量
2023-11-16
15:29:35
上传
评论
收藏 253KB PDF 举报
温馨提示

试读
12页
Gartner发布安全运营中心(SOC)模型指南:SOC的四个主要目标、所需的技术能力和运营团队 为组织选择正确的安全运营中心模型不仅仅是雇用团队或服务提供商的问题。在选择某种形式的混合模型之前,安全和风险管理领导者必须仔细考虑运营责任并了解风险。 主要发现 对于大多数组织来说,仅由内部员工扩展为安全运营中心 (SOC)即使不是不可能,也是很困难的。 一些 SOC 任务是战略性的,例如由高级调查员、事件响应经理和红队测试员角色执行的任务。它们通常最好由了解业务需求和安全问题的内部员工来执行。 其他 SOC 任务是战术性的,例如构建常见攻击的检测内容。它们通常最好由更大的外部团队来执行,这样可以更高效、更大规模、更长时间地完成这些任务。 与安全服务提供商合作的组织通常认为他们的提供商正在实现既未签订合同也不属于其责任的目标。
资源推荐
资源详情
资源评论

Gartner, Inc. | G00787022
Page 1 of 12
SOC Model Guide
Published 18 October 2023 - ID G00787022 - 11 min read
By Analyst(s): Eric Ahlm, Mitchell Schneider, Pete Shoard
Initiatives: Security Operations; Build and Optimize Cybersecurity Programs; Meet Daily
Cybersecurity Needs
Choosing the right security operations center model for an
organization is not just a matter of hiring a team or a service
provider. Security and risk management leaders must carefully
consider operational responsibility and understand the risks,
before probably choosing a form of hybrid model.
Overview
Key Findings
Recommendations
When designing a SOC, security and risk management (SRM) leaders should:
Scaling up a security operations center (SOC) with only internal staff is difficult, if
not impossible, for most organizations.
■
Some SOC tasks are strategic, such as those performed by the roles of senior
investigator, incident response manager and red team tester. They are often best
performed by in-house staff who understand the business’s needs and the security
issues.
■
Other SOC tasks are tactical, such as building detection content for common
attacks. They are generally best performed by a larger external team, which can do
them more efficiently, on a bigger scale, and for longer periods.
■
Organizations working with security service providers commonly assume their
provider is fulfilling objectives that are neither contracted for nor part of its
responsibility.
■
Use their threat detection needs as requirements when building a SOC model.
■
This research note is restricted to the personal use of chenlizhen@qianxin.com.

Gartner, Inc. | G00787022
Page 2 of 12
Introduction
Building a SOC is a journey, one that never ends, as the requirements continuously
change. It takes continuous growth and analysis to ensure a SOC’s performance does not
decline and its costs do not go over budget.
Opting for a hybrid SOC is one way to help grow capabilities, while managing scale and
cost. A hybrid SOC is one in which more than one team, both insourced and outsourced,
plays a role in the activities required for proper SOC operation. The question of which
teams, roles, jobs and activities are best kept in-house or outsourced is complex. Building
a SOC model helps you answer it and ensure a hybrid SOC is well-balanced.
A SOC model defines a strategy for variation in the use of internal teams and external
service providers when running a SOC. It ensures all roles required to operate a SOC are
allocated to those best suited to discharge the associated responsibilities.
An effective SOC model lets SRM leaders allocate resources based on business priorities,
available skill sets and budget; a mix of insourcing and outsourcing is the most common
approach. A SOC model allows for strategic decisions, such as making generic SOC tasks
key targets for outsourcing, while staffing more sensitive functions internally. There are
also some tasks that are so specialized that having people on the payroll to perform them
will be hard for most organizations to justify.
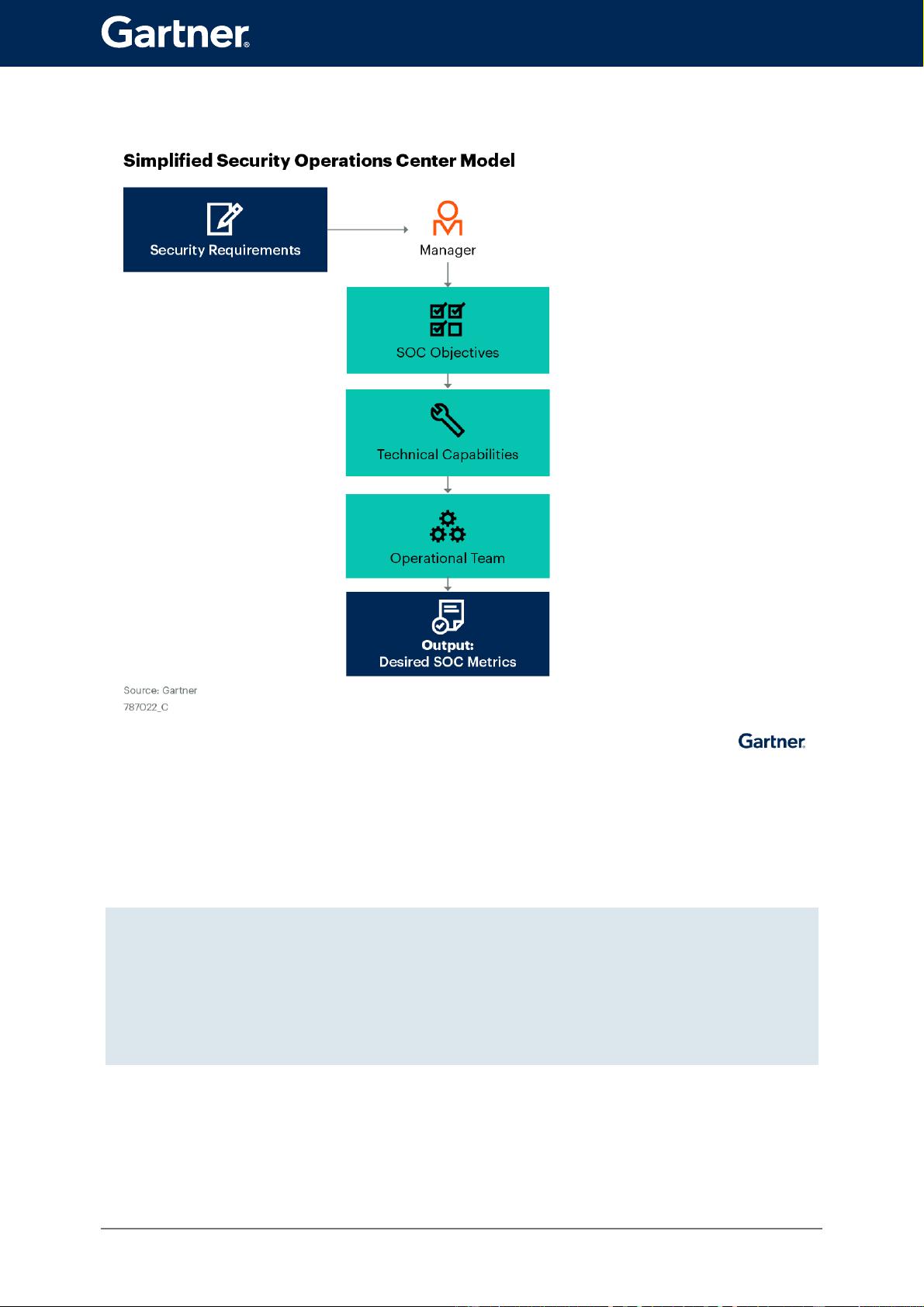
Figure 1 shows a simplified SOC model. A manager must assess the SOC’s objectives and
the technical capabilities required to fulfill them. Technical capabilities will require people
with specific talents and abilities. How the operational team is formulated will directly
impact the SOC’s overall performance.
Build a SOC model that strikes the best balance of internal teams working on
strategic objectives and service providers working on tactical objectives.
■
Use service providers for roles best performed on a large scale or that require specific
threat knowledge, operational techniques or tool administration skills.
■
Use internal staff for roles involving both security knowledge and business
operations, such as senior investigator, incident response manager and red team
tester.
■
This research note is restricted to the personal use of chenlizhen@qianxin.com.
Gartner, Inc. | G00787022
Page 3 of 12
Figure 1: Simplified Security Operations Center Model
SRM leaders often call Gartner to talk about problems with their SOC service providers or
the overall scale of their SOC and its performance. But often the problem is not the
provider. Instead, it is that the client lacks a SOC model or has one that is incomplete.
In many cases, the root cause of clients’ dissatisfaction with SOC
services is not their service provider. It is that they have no model
strategy for the SOC’s operation.
This research note is restricted to the personal use of chenlizhen@qianxin.com.
剩余11页未读,继续阅读
资源评论

lurenjia404
- 粉丝: 1663
- 资源: 113
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
