没有合适的资源?快使用搜索试试~ 我知道了~
2018美赛O奖论文F题-F87280-How much is your privacy information-解密.pdf
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 31 浏览量
2024-03-17
21:50:41
上传
评论
收藏 1.64MB PDF 举报
温馨提示

试读
31页
美国大学生数学竞赛获奖论文,历届,单项文件,内容丰富,大学生数学,数学竞赛,参考资料,极具参考价值
资源推荐
资源详情
资源评论
For office use only
T1
T2
T3
T4
Team Control Number
87280
Problem Chosen
F
For office use only
F1
F2
F3
F4
2018 ICM
How much is your privacy information?
Summary Sheet
For ensuring the stability of the society, we establish a system of privacy pricing.
Task1, according to the personal characteristics and information field, we choose 26
indexes to measure privacy price, and divide them into 5 categories according to the degree
of correlation.
Task2, we price the privacy. The present value method is used to quantify the value of
privacy. We use the Analytic Hierarchy Process and Gradient Boosting Decision Tree,
through the Python language to calculate the coefficients of the parameters. Then we establish
Gauss mixture model to evaluate the information related value. Finally, the simulation of 500
people's privacy information is selected to verify the feasibility of the model.
Task3, we give the pricing method, introduce the demand elasticity coefficient, and
analyze that the privacy information is more flexible. Then the life cycle changes in a long
time range are predicted.
Task4, with the development of the times, the risk factor will be changed. We add
dynamic factors and use Matlab to fit the change function of the risk coefficient.
Task5, the value of privacy will increase with age and then stabilize at a certain level. We
find out the relationship between PI, IP and PP in the privacy market through a number of
literature searches.
Task6, we use small world model and dynamic game theory to do simulation and
prediction, and find that the privacy of individuals and groups will be largely leaked with the
development of market.
Task7, the impact of data leakage is long tail. The agency can use the actuarial model to
calculate the total amount of compensation to the individual.
Task8, we put forward some suggestions to the government on the basis of the model.
Finally, we perform a sensitivity test to verify the stability of the model.

Team # 87280
Page 1 of 20
I
Introduction
With the development of social informatization, the commercialization of privacy becomes
an important issue. Therefore, we need to establish a privacy pricing system to maintain the
stable and healthy development of the information sales market. Our tasks are as follows:
Task 1: considering the level of risk can pass personal information and data fields
classifying model, considering the different characteristics of category information, find the
best balance of classification accuracy and simplicity.
Task 2: the question to think about the integrity of personal information, uniqueness,
scarcity, according to the value of different factors, finally comprehensive assessment of the
value of personal information.
Task 3: consider the information value, risk value, and the impact of information integrity
on the final information pricing.
Task 4: consider the assumptions and constraints of the pricing model, judge the
relationship between information privacy and human rights, and adjust the model to make it
universal in the dynamic environment.
Task 5: consider the influence of age factors on the risk-benefit ratio of the population,and
consider the similarities and differences between PI and PP and IP.
Task 6: make sure each individual data sharing information leakage caused by the network
effect, and to consider whether the information network effect will affect the value of the
personal information system, and to have the same privacy risks related to personnel, thesale
of their personal information should be restricted.
Task 7: consider the impact of large-scale PI leakage on data vendors, acquirers, and
information value systems. And consider whether the responsibility for data disclosure should
be responsible for information disclosure.
Task 8: organize the above questions into proposals.
II
Categorize individuals into sub-groups (Task 1)
2.1 A brief introduction to personal privacy pricing
Personal privacy is a basic resource, if it is used reasonably, it will help to promote the
information social development. Culnan[1] find that, if private used by business are not
known to individuals, they will increase their concerns about privacy disclosure. Hagel and
others’ [2] research shows, some people tend to pay more attention to privacy, the reason is
that they want to get compensation for information leakage. Adjei[3]thinks that, people will
be willing to provide personal information to get paid if their personal profits outweigh the
risks.
Thus, it can be seen that, on the premise of the sound pricing system of personal privacy
most people are willing to obtain certain compensation or compensation through the sale of
personal privacy. So the appropriate pricing system should be set up.

Team # 87280
Page 2 of 20
2.1.1
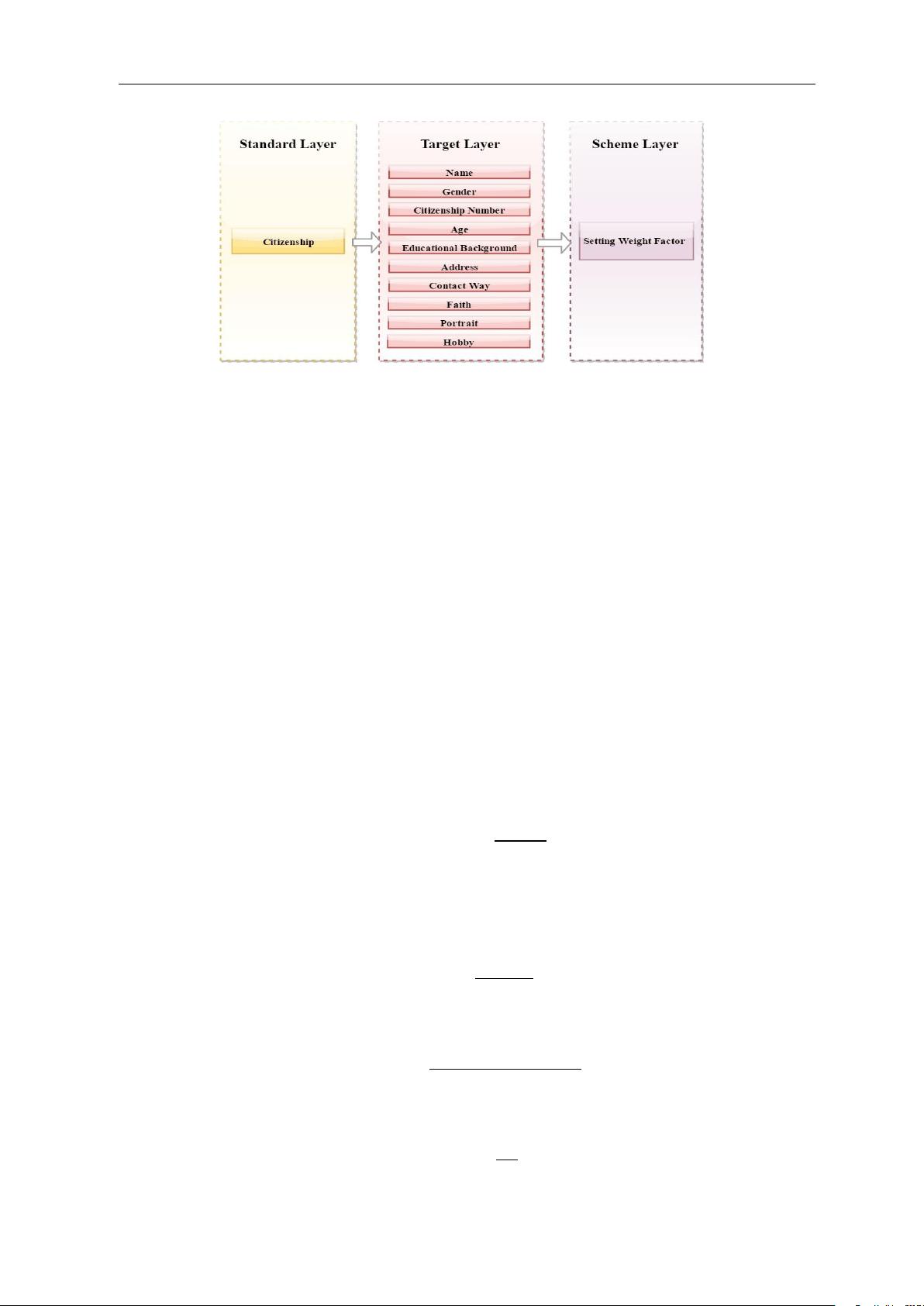
The establishment and evaluation of personal privacy information archives
The classification of personal privacy information can help research and excavate the real
value contained in information, and the value of information can be further evaluated by
studying the correlation degree. Therefore, we chose 26 indicators based on the principle of
personal information classification and the actual situation of this subject. It includes personal
attributes, financial transactions, social networks, personal assets and health care. This paper
classifies personal privacy into two aspects: individual characteristics and information field.
The indicators and their classification are shown in Figure 2-1.
Figure 2-1: Classification
The reasons for the selection of personal privacy information in five aspects are analyzed
as follows:
Citizenship:They belong to the range of attribute information and are objective
information that can be used to identify specific individuals.
Social Contact: Because of the unique social attributes of human beings, it has an
important research value in the field of information, which is generated in the process of
life with the other spider web information.
Finance: It reflects the situation of individual financial trade and has great value for
information mining.
Health/Medical: It has certain significance to the study of social medical treat- ment
service system, and reflects the various situations of the individual body.
Personal Assets
:
It reflects the personal economic status, which is valuable for public
interest, such as national economic analysis, and corporate profits, and it can create
economic benefits.

Team # 87280
Page 3 of 20
j
j
III
Privacy Cost Model
(
Task2
)
3.1 Brief Introduction
The cost of privacy is a comprehensive pricing of the value of privacy, and we consider
three components.
The first is the expected value of income, and we divide five two - level parameters into
two categories.
Difficult to quantify: As citizenship, we empower each parameter by analytic hierarchy
process[4].
Quantify: The other 16 parameters can be quantified by using the present value method
of income in accounting. Then the coefficient of each parameter is calculated by the machine
learning method of the Gradient Boosting Decision Tree(GBDT)[5].
The second aspect is the risk value of privacy. Because the value of risk is not easy to
measure, we use probability theory to estimate the average deviation degree of expected
revenue and get the expected risk reward[6].
The third aspect is information related value. The cost of privacy depends not only on the
integrity of information, but also on the relevance. For example, the value of only the name
should be lower compared with the value of the name attached to the person. We set up a
Gauss mixed model to study the relationship between the correlation value and the relevant
value of information[7].
3.2 Model Building
3.2.1 Expected Value of Income
The expected value of income is
:
26
I
j
C
j
j
1
Where:
I
:
Expected total income value
:
The value coefficient of the
j
th
parameter,
C
j
:The expected return value of the j
th
parameter
Step1:The empowerment of civil identity information by AHP
The related factors of citizenship quantification are decomposed into objectives,
guidelines, programs and so on. Based on this, qualitative and quantitative analysis is carried
out. The analytic hierarchy process is like Figure 3–1
:
j
Team # 87280
Page 4 of 20
n
n
Figure 3–1: The Structure of AHP
Construct a comparison matrix
By consulting relevant information and combining with the reality of life, we analyze the
relationship and importance of 10 indicators in citizenship, and build pair wise comparison
matrix.
Hierarchical single order
The elements of each column of the judgement matrix are normalized, and the general
terms of the elements are:
A
ij
=A
ij
A
ij
i,j=1
Using sum and product method are used to calculate and add the judgement matrix of
each column after the normalization. The W
i
is obtained.
W
i
=
B
ij
i,j=1
The element of the W
i
is the sort weight value of the relative importance of the same
level factor to a certain factor of the upper level factor. For W (W , W ,..., W )
T
,In the
1 2 n
process of normalization, the approximate solution of the eigenvector is obtained. Calculating
the maximum eigenvalue of the judgment matrix
max
max
n
i
1
(AW)
i
n
W
i
After that, we can make sure that the rank ordering is consistent with the consistency
check. The so-called consistency check is the allowable range of A.
Pairwise comparison matrix consistency test
The consistency index of the pairwise comparison matrix is Consistency Index (C.I.),
CI
max
n
n
1
To measure the size of CI, a random consistency index RI is introduced. The method is:
construct 500 pairwise comparison matrices randomly, and get the consistency index
RI
CI
1
CI
2
... CI
500
500
The ratio of the consistency index CI. to the same order mean random consistency index
R.I. is called the random consistency ratio Consistency Ratio(CR)。
CR
CI
RI
剩余30页未读,继续阅读
资源评论

阿拉伯梳子
- 粉丝: 1655
- 资源: 5735
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
