没有合适的资源?快使用搜索试试~ 我知道了~
资源推荐
资源详情
资源评论

TCG
TCG Trusted Network
Communications
TNC IF-T: Binding to TLS
Specification Version 2.0
Revision 8
27 February 2013
Published
Contact:
admin@trustedcomputinggroup.org
TCG PUBLISHED
Copyright © TCG 2005-2013

TNC IF-T: Binding to TLS TCG Copyright
Specification Version 2.0
Revision 8 Published Page ii of 42
TCG PUBLISHED
Copyright
©
2005-2013 Trusted Computing Group, Incorporated.
Disclaimer
THIS SPECIFICATION IS PROVIDED "AS IS" WITH NO WARRANTIES WHATSOEVER, INCLUDING
ANY WARRANTY OF MERCHANTABILITY, NONINFRINGEMENT, FITNESS FOR ANY PARTICULAR
PURPOSE, OR ANY WARRANTY OTHERWISE ARISING OUT OF ANY PROPOSAL, SPECIFICATION
OR SAMPLE. Without limitation, TCG disclaims all liability, including liability for infringement of any
proprietary rights, relating to use of information in this specification and to the implementation of this
specification, and TCG disclaims all liability for cost of procurement of substitute goods or services, lost
profits, loss of use, loss of data or any incidental, consequential, direct, indirect, or special damages,
whether under contract, tort, warranty or otherwise, arising in any way out of use or reliance upon this
specification or any information herein.
No license, express or implied, by estoppel or otherwise, to any TCG or TCG member intellectual property
rights is granted herein.
Except that a license is hereby granted by TCG to copy and reproduce this specification for internal
use only.
Contact the Trusted Computing Group at www.trustedcomputinggroup.org for information on specification
licensing through membership agreements.
Any marks and brands contained herein are the property of their respective owners.
TNC IF-T: Binding to TLS TCG Copyright
Specification Version 2.0
Revision 8 Published Page iii of 42
TCG PUBLISHED
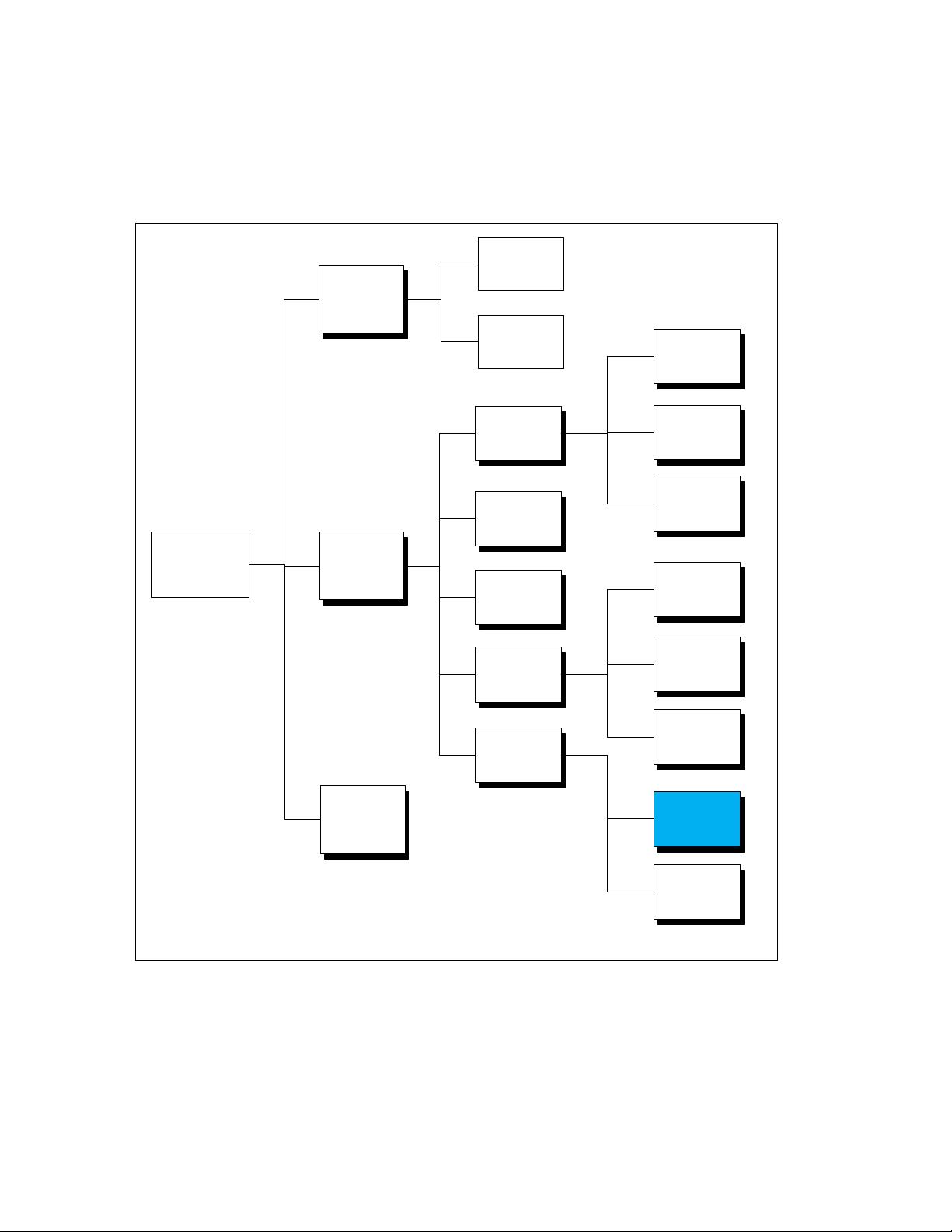
TNC Document Roadmap
TNC
Architecture
IF
-IMC
IF-
IMV
APIs
Assessment
Protocols
IF-MAP
IF-
M
IF
-
IMV
Protocol
IF
-PEP
IF-TNCCS
IF-T
IF
-M
Protocol
PTS
Protocol
SCAP
Messages
XML
TLV
SoH
TLS
Tunneled
EAP
Methods
TNC IF-T: Binding to TLS TCG Copyright
Specification Version 2.0
Revision 8 Published Page iv of 42
TCG PUBLISHED
Acknowledgement
The TCG wishes to thank all those who contributed to this specification. This document builds on
considerable work done in the various working groups in the TCG.
Special thanks to the TCG participants contributing to this document:
Name
Affiliation
David Louin
AMOSSYS
Scott Kelly
Aruba Networks
Padma Krishnaswamy
Battelle Memorial Institute
Jeffery Dion
Boeing
Steven Venema
Boeing
Nancy Cam-Winget
Cisco Systems
Scott Pope
Cisco Systems
Peter Wrobel
CESG
Mark Townsend
Enterasys
Ronald Marx
Fraunhofer Institute for Secure Information Technology
Sung Lee
Fujitsu Limited
Mauricio Sanchez
Hewlett-Packard
Ira McDonald
High North
Ren Lanfang
Huawei
Dr. Jiwei Wei
Huawei
Han Yin
Huawei
Stuart Bailey
Infoblox
James Tan
Infoblox
David Vigier
Infoblox
Kent Landfield
Intel Corporation
Ravi Sahita
Intel Corporation
Josh Howlett
JANET (UK)
Steve Hanna (Editor, TNC-WG co-chair)
Juniper Networks
Clifford Kahn
Juniper Networks
PJ Kirner
Juniper Networks
Lisa Lorenzin
Juniper Networks
Tom Price
Lumeta
Matt Webster
Lumeta
Atul Shah (TNC-WG co-chair)
Microsoft Corporation
Paul Sangster (Editor)
Symantec
Charles Schmidt
The MITRE Corporation
Brad Upson
University of New Hampshire InterOperability Lab
Jessica Fitzgerald-McKay
US National Security Agency
Lauren Giroux
US National Security Agency

TNC IF-T: Binding to TLS TCG Copyright
Specification Version 2.0
Revision 8 Published Page v of 42
TCG PUBLISHED
Table of Contents
1 Scope and Audience .............................................................................................. 6
1.1 Interoperable with IETF PT-TLS ...................................................................................................... 6
1.2 IETF Terminology Mapping to TNC ................................................................................................. 6
2 Background ............................................................................................................ 8
2.1 Purpose of IF-T ................................................................................................................................ 8
2.2 Supported Use Cases ...................................................................................................................... 8
2.3 Non-supported Use Cases ............................................................................................................... 9
2.4 Requirements ................................................................................................................................. 10
2.5 Non-Requirements ......................................................................................................................... 11
2.6 Assumptions ................................................................................................................................... 11
2.7 Keywords ....................................................................................................................................... 12
2.8 Network Communications Diagram Conventions .......................................................................... 12
3 Network Connected Endpoint Assessments ..................................................... 13
3.1 Benefits .......................................................................................................................................... 13
3.2 Securing the TCP/IP Session with TLS ......................................................................................... 13
3.3 No Change to Base TLS Protocol .................................................................................................. 14
3.4 Parallel Enumerated Values .......................................................................................................... 14
4 IF-T Over TLS Protocol ........................................................................................ 16
4.1 TCP Port Usage ............................................................................................................................. 16
4.2 Preventing MITM Attacks with Channel Bindings .......................................................................... 16
4.3 IF-T Message Flow ........................................................................................................................ 16
4.3.1 Cause of an Assessment ...................................................................................................... 16
4.3.2 Issues with Server Initiated TLS Sessions ............................................................................ 17
4.3.3 Establish or Re-Use TLS Session ......................................................................................... 17
4.3.4 IF-T Message Exchange ....................................................................................................... 17
4.3.5 TLS Requirements ................................................................................................................ 20
4.4 IF-T Message Format ..................................................................................................................... 20
4.5 IF-T Message Types ...................................................................................................................... 22
4.6 IF-T Version Negotiation ................................................................................................................ 26
4.6.1 Version Request Message .................................................................................................... 26
4.6.2 Version Response Message ................................................................................................. 27
4.7 Client Authentication using SASL .................................................................................................. 28
4.7.1 SASL Authentication Requirements ...................................................................................... 28
4.7.2 SASL Use in IF-T Binding to TLS .......................................................................................... 28
4.7.3 SASL Authentication Flow ..................................................................................................... 29
4.7.4 Aborting SASL Authentication ............................................................................................... 29
4.7.5 Integration with SASL Framework ......................................................................................... 29
4.7.6 SASL Channel Bindings ........................................................................................................ 29
4.7.7 SASL Mechanisms Message ................................................................................................ 30
4.7.8 SASL Mechanism Selection Message .................................................................................. 30
4.7.9 SASL Authentication Data Message ..................................................................................... 31
4.7.10 SASL Result Message .......................................................................................................... 31
4.8 IF-T Error Message ........................................................................................................................ 32
5 Security Considerations ...................................................................................... 36
5.1 Trust Relationships and Countermeasures.................................................................................... 37
6 Privacy Considerations ....................................................................................... 38
7 References ............................................................................................................ 39
7.1 Normative References ................................................................................................................... 39
7.2 Informative References .................................................................................................................. 40
剩余41页未读,继续阅读
资源评论


书香度年华
- 粉丝: 1w+
- 资源: 383
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

