没有合适的资源?快使用搜索试试~ 我知道了~
资源推荐
资源详情
资源评论

TCG
TCG Trusted Network
Communications
IF-M Segmentation
Specification Version 1.0
Revision 5
04 April 2016
Published
Contact: admin@trustedcomputinggroup.org
TCG Published
Copyright © TCG 2016

TCG Copyright 2016 IF-M Segmentation
Specification Version 1.0
Revision 5 Page ii of 44 04 April 2016
Copyright
©
2016 Trusted Computing Group, Incorporated.
Disclaimer
THIS SPECIFICATION IS PROVIDED "AS IS" WITH NO WARRANTIES WHATSOEVER, INCLUDING
ANY WARRANTY OF MERCHANTABILITY, NONINFRINGEMENT, FITNESS FOR ANY PARTICULAR
PURPOSE, OR ANY WARRANTY OTHERWISE ARISING OUT OF ANY PROPOSAL, SPECIFICATION
OR SAMPLE. Without limitation, TCG disclaims all liability, including liability for infringement of any
proprietary rights, relating to use of information in this specification and to the implementation of this
specification, and TCG disclaims all liability for cost of procurement of substitute goods or services, lost
profits, loss of use, loss of data or any incidental, consequential, direct, indirect, or special damages,
whether under contract, tort, warranty or otherwise, arising in any way out of use or reliance upon this
specification or any information herein.
No license, express or implied, by estoppel or otherwise, to any TCG or TCG member intellectual property
rights is granted herein.
Except that a license is hereby granted by TCG to copy and reproduce this specification for internal
use only.
Contact the Trusted Computing Group at www.trustedcomputinggroup.org for information on specification
licensing through membership agreements.
Any marks and brands contained herein are the property of their respective owners.
TCG Copyright 2016 IF-M Segmentation
Specification Version 1.0
Revision 5 Page iii of 44 04 April 2016
Acknowledgements
The TCG wishes to thank all those who contributed to this specification. This document builds on
considerable work done in the various working groups in the TCG.
Adrien Raffin
AMOSSYS
Henk Birkholz
Fraunhofer
Gerald Maunier
Gemalto
Graeme Proudler
Hewlett Packard Laboratories
Ira McDonald
High North
Andreas Steffen
HSR University of Applied Sciences Rapperswil
Yi Zhang
Huawei
Atul Shah (TNC Co-Chair)
Microsoft
Charles Schmidt (Editor)
MITRE
Steve Hanna
Infineon Technologies
Lisa Lorenzin (TNC Co-Chair)
Pulse Secure
Cliff Kahn
Pulse Secure
Mike Boyle
US Department of Defense
Jessica Fitzgerald-McKay
US Department of Defense
Jonathan Hersack
US Department of Defense
Chris Salter
US Department of Defense
Andrew Cathrow
Verisign

TCG Copyright 2016 IF-M Segmentation
Specification Version 1.0
Revision 5 Page iv of 44 04 April 2016
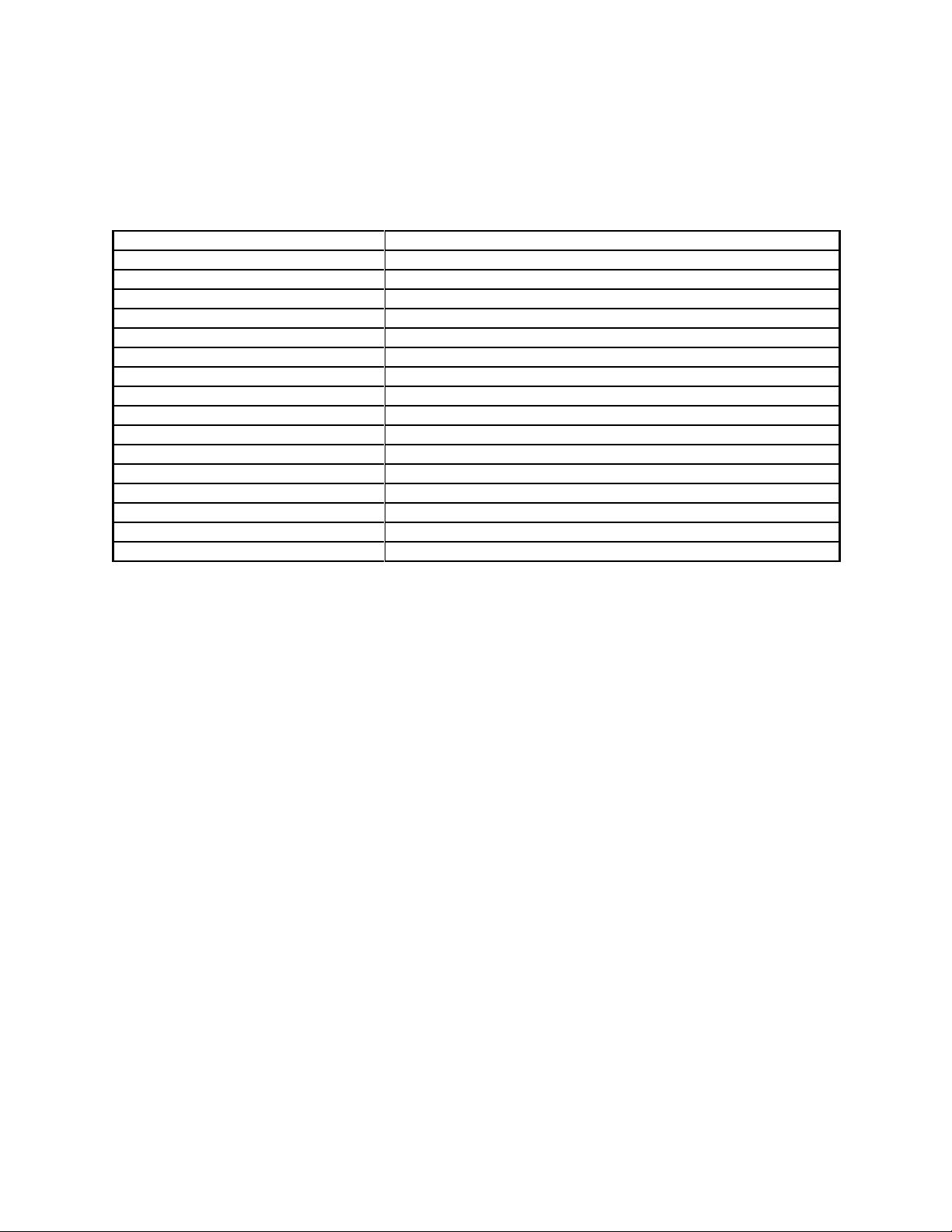
Table of Contents
1 Introduction ............................................................................................................ 1
1.1 Scope and Audience ..................................................................................................................... 1
1.2 Keywords ....................................................................................................................................... 3
1.3 Definitions ...................................................................................................................................... 3
2 Background ............................................................................................................ 4
2.1 Role of IF-M Segmentation ........................................................................................................... 4
2.2 Supported Use Cases ................................................................................................................... 4
2.2.1 Support Limits on Message Sizes below the Maximum Allowed Size ...................................... 4
2.2.2 Support Sending Messages Piecemeal .................................................................................... 4
2.2.3 IF-M Use Cases ........................................................................................................................ 5
2.3 Non-supported Use Cases ............................................................................................................ 5
2.3.1 Unilateral Imposition of Segmentation Contracts ...................................................................... 5
2.3.2 Support for Non-Exclusive Delivery .......................................................................................... 5
2.3.3 Support for Contract Initiation or Modification by Contracted Party .......................................... 5
2.4 Specification Requirements .......................................................................................................... 5
2.5 Non-Requirements ........................................................................................................................ 6
2.6 Assumptions .................................................................................................................................. 6
2.7 IF-M Segmentation Diagram Conventions .................................................................................... 6
3 IF-M Segmentation Exchanges and Processing .................................................. 8
3.1 The Segmentation Contract .......................................................................................................... 8
3.2 Establishing a Segmentation Contract .......................................................................................... 9
3.2.1 IF-M Segmentation Attributes and the IF-TNCCS IF-M Subtype ............................................ 10
3.2.2 Limits on Segmentation Contract Sizes .................................................................................. 10
3.2.3 Allowing Segmented Message Exchanges ............................................................................. 11
3.3 Modifying a Segmentation Contract ............................................................................................ 11
3.4 Terminating a Segmentation Contract ........................................................................................ 12
3.5 Applying a Segmentation Contract ............................................................................................. 12
3.5.1 Sending Messages .................................................................................................................. 13
3.5.2 Segmented Message Exchanges ........................................................................................... 16
3.5.3 Violations of Segmentation Contracts ..................................................................................... 19
3.6 Multi-Component Parties ............................................................................................................. 20
3.7 Error Handling ............................................................................................................................. 22
3.7.1 Errors that Cancel Segmentation Contracts ........................................................................... 22
3.7.2 Errors that Cancel Segmented Message Exchanges ............................................................. 22
3.7.3 Reaching Limits on Supported IF-M Segmentation Activities ................................................. 22
3.7.4 Errors in the Base Message Delivered by a Segmented Message Exchange ....................... 23
3.7.5 IF-M Segmentation Attributes and Externally Defined IF-M Errors ......................................... 23
4 IF-M Segmentation Message and Attributes ...................................................... 25
4.1 IF-M Subtype (AKA IF-M Component Type) ............................................................................... 25
4.2 IF-TNCCS and IF-M Messages ................................................................................................... 25
4.3 IF-M Attribute Header .................................................................................................................. 26
4.4 IF-M Segmentation Attribute Overview ....................................................................................... 26
4.5 IF-M Segmentation Attribute Enumeration .................................................................................. 27
4.6 Segmentation Contract Request ................................................................................................. 28
4.7 Segmentation Contract Response .............................................................................................. 29
4.8 Segment Envelope ...................................................................................................................... 30
4.9 Next Segment.............................................................................................................................. 32
4.10 Cancel ......................................................................................................................................... 33
4.11 Oversized Message .................................................................................................................... 34
4.12 Contract Exemption ..................................................................................................................... 35
4.13 IF-M Error as Used by IF-M Segmentation ................................................................................. 36
4.13.1 TNC_IFM_SEG_CONTRACT_REJECTED Information ..................................................... 37

TCG Copyright 2016 IF-M Segmentation
Specification Version 1.0
Revision 5 Page v of 44 04 April 2016
4.13.2 TNC_IFM_NO_NEXT_SEGMENT, TNC_IFM_UNEXPECTED_SEGMENT,
TNC_IFM_NO_SUCH_MESSAGE, and TNC_IFM_SEG_VIOLATION Information ........................... 39
5 Security Considerations ...................................................................................... 41
5.1 Impractical Size Limits ................................................................................................................ 41
5.2 Withholding Segments ................................................................................................................ 41
6 Privacy Considerations ....................................................................................... 43
7 References ............................................................................................................ 44
7.1 Normative References ................................................................................................................ 44
7.2 Informative References ............................................................................................................... 44
剩余48页未读,继续阅读
资源评论


书香度年华
- 粉丝: 1w+
- 资源: 383
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

