
Features
• Secure authentication and validation device
• Integrated capability for both host and client operations
• Superior SHA-256 hash algorithm, HMAC option
• Best–in-class, 256-bit key length; storage for up to 16 keys
• Guaranteed unique 72-bit serial number
• Internal, high-quality random number generator
• 4.5K-bit EEPROM for keys and data
• 512 OTP bits for fixed information
• Multiple I/O options
− High-speed, single-pin interface
− 1MHz I
2
C interface
• 2.0V – 5.5V supply voltage range
• 1.8V – 5.5V communications
• <150nA sleep current
• Extended, multi-level hardware security
• Optional integrated temperature sensor
• 8-lead SOIC, 8-lead TSSOP, 3-lead SOT23, 8-pad UDFN, and
3-pad contact packages
Applications
• Anti-clone protection for accessories, daughter cards, and consumables
• Secure boot validation, software anti-piracy
• Network and computer access control
• Key exchange for encrypted downloads
• Authenticated/encrypted communications for control networks
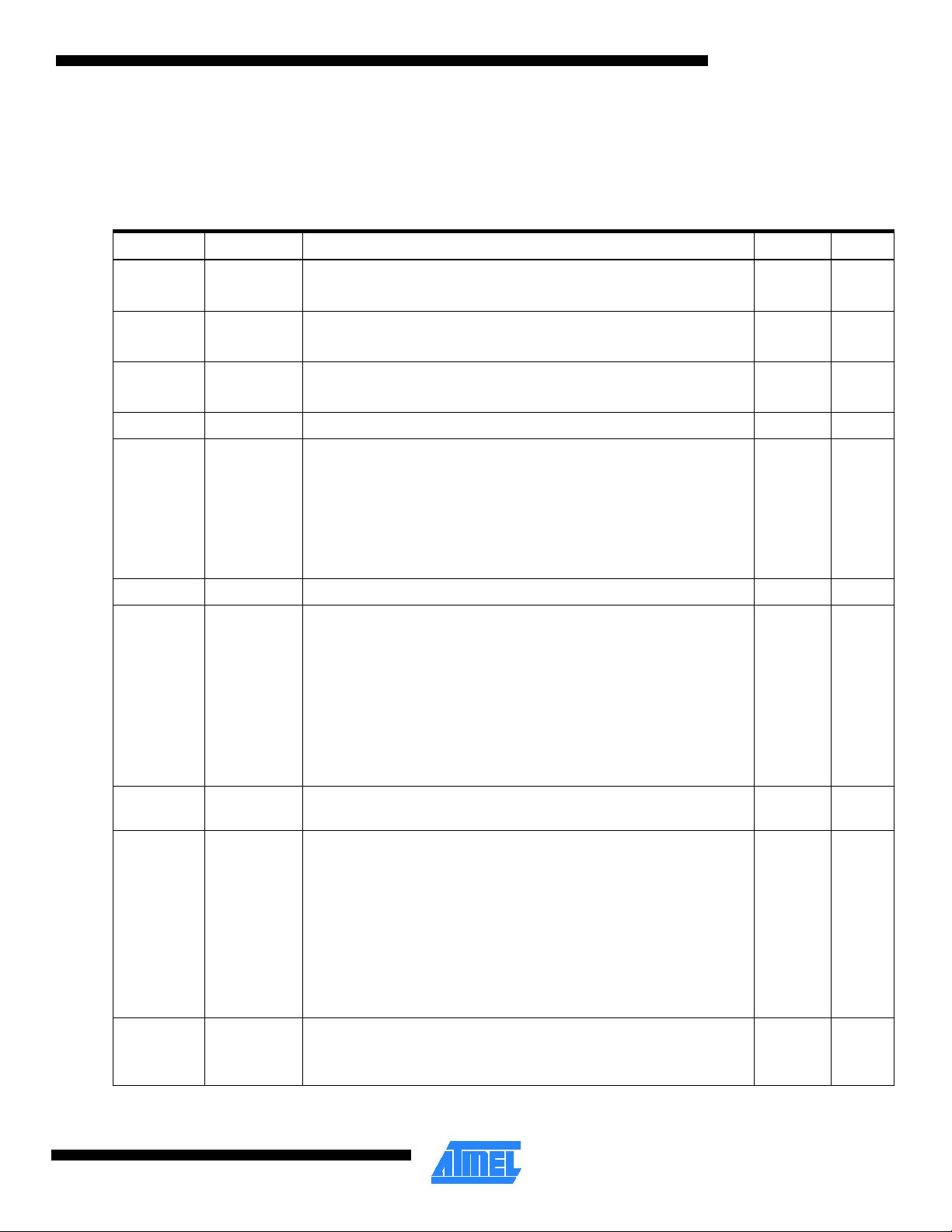
Figure 1. Pin configurations
Pin name Function
VCC
SCL
SDA GND
4
3
2
1
5
6
7
8
8-lead UDFN
Bottom view
NC
NC
NC
GND
1
2
3
4
8
7
6
5
8-lead SOIC
VCC
NC
SCL
SDA
SDA Serial data
SCL Serial clock input
GND Ground
VCC Power supply
3
2
1
GND
VCC
SDA
3-lead SOT23
Atmel
CryptoAuthentication™
Atmel ATSHA204
Authentication Chip
8740B
−
CRYPTO
−
5/11

2 Atmel ATSHA204
8740B−CRYPTO−5/11
1. Introduction
The following sections introduce the features and functions of the Atmel
®
ATSHA204 authentication chip.
1.1. Applications
The ATSHA204 is a member of the Atmel CryptoAuthentication™ family of high-security hardware authentication devices. It has
a flexible command set that allows use for many applications, including the following:
• Anti-counterfeiting
Validate that a removable, replaceable, or consumable client is authentic. Example clients could be printer ink tanks,
electronic daughter cards, or other spare parts. It can also be used to validate a software/firmware module or memory
storage element.
• Protection for firmware or media
Validate code stored in flash memory at boot to prevent unauthorized modifications (aka secure boot), encrypt
downloaded media files, and uniquely encrypt code images to be usable on a single system only.
• Session key exchange
Securely and easily exchange stream encryption keys for use by an encryption/decryption engine in the system
microprocessor to manage such things as a confidential communications channel or an encrypted download.
• Secure data storage
Store secret keys for use by crypto accelerators in standard microprocessors. Can also be used to store small quantities
of data necessary for configuration, calibration, ePurse value, consumption data, or other secrets. Programmable
protection up through encrypted/authenticated reads and writes.
• User password checking
Validate user entered passwords without letting the expected value become known, map simple passwords to complex
ones, and securely exchange password values with remote system.
1.2. Chip Features
The ATSHA204 includes an electrically erasable programmable read-only memory (EEPROM) array that can be used for
storage of keys, miscellaneous read/write, read-only or secret data, consumption logging, and security configuration. Access to
the various sections of memory can be restricted in a variety of ways and the configuration then locked to prevent changes. See
Section 2.1, “EEPROM organization,” for more details on the EEPROM organization.
The ATSHA204 features a wide array of defensive mechanisms specifically designed to prevent physical attacks on the chip
itself or logical attacks on the data transmitted between the chip and the system. See Section 3.4, “Security Features,” for more
details. Hardware restrictions on the ways in which keys are used or generated, described in Section 3.3, “Key values,” provide
further defense against certain styles of attack.
Access to the chip is through a standard I
2
C interface at speeds up to 1M-bit/sec (See Section 6 for details on this interface). It
is compatible with standard serial EEPROM I
2
C interface specifications. The chip also supports a single-wire interface that can
reduce the number of GPIOs required on the system processor and/or reduce the number of pins on connectors. The single-
wire interface is described in more detail in Section 5, “Single-wire Interface.”
Using either the I
2
C or single-wire interface, multiple ATSHA204 chips can share the same bus, which saves processor GPIO
usage in systems with multiple clients such as different color ink tanks or multiple spare parts. See Section 4.2, “Sharing the
Interface,” and Section 8.10, “Pause Command,” for more details on the way in which this is implemented.
Each ATSHA204 ships with a guaranteed unique 72-bit serial number. Using the cryptographic protocols supported by the chip,
a host system or remote server can prove that the serial number is both authentic and not a copy. Serial numbers are often
stored in a standard serial EEPROM, but these can be easily copied, and there is no way for the host to know if the serial
number is authentic or a clone.

Atmel ATSHA204
3
8740B−CRYPTO−5/11
The Atmel ATSHA204 can generate high-quality random numbers and employ them for any purpose, including as part of the
crypto protocols of this chip. Because each 256-bit random number is guaranteed to be unique from all numbers ever generated
on this or any other chip, their inclusion in the protocol calculation ensures that replay attacks (re-transmitting a previously
successful transaction) always fail. Further information is found in Section 3.4.2, “Random Number Generator,” and Section
8.11, “Random Command.”
System integration is eased with a wide supply voltage range (2.0V through 5.5V) and an ultra-low sleep current of <100nA.
Complete DC parametrics are found in Section 7, which describes multiple package options, including a tiny SOT23 package
with a footprint of only 2.5mm x 3mm. See Section 11, “Package Drawings,” for more details and ordering codes.
See Section 9, “Compatibility,” for information regarding compatibility with the Atmel AT88SA102S and Atmel AT88SA10HS,
previous members of the Atmel CryptoAuthentication family.
1.3. Cryptographic Operation
The ATSHA204 supports a standard challenge-response protocol to simplify programming. At its most basic, the host system
sends a challenge to the chip in the client, which combines that challenge with a secret key via the MAC command from the
system, described in Section 8.8, “MAC Command,” and sends the response back to the system. The chip uses a cryptographic
hash algorithm for the combination, which prevents an observer on the bus from deriving the value of the secret key, but allows
the recipient to verify that the response is correct by performing the same calculation (combining the challenge with the secret)
with a stored copy of the secret.
Due to the flexible command set of the ATSHA204, however, this basic operation can be expanded in many ways. Using the
GenDig command (Section 8.5, “GenDig Command”) the values in other slots can be included in the response digest, which
provides an effective way of proving that a data read really did come from the chip, as opposed to being inserted by a man-in-
the-middle attacker. This same command can be used to combine two keys with the challenge, which is useful when there are
multiple layers of authentication to be performed.
The DeriveKey command (Section 8.3, “DeriveKey Command”) implements a key rolling scheme. Depending on the command
mode parameter, the resulting operation can be similar to that implemented in a remote-controlled garage door opener. Each
time the key is used, the current value of the key is cryptographically combined with a value specific to that system, and the
result forms the key for the next cryptographic operation. Even if an attacker gets the value of one key, that key will be gone
forever with the next use.
DeriveKey can also be used to generate new random keys that might be valid only for a particular host ID, for a particular time
period, or for some other restricted environment. Each generated key is different from any other key ever generated on any
chip. By “activating” a host-client pair in the field in this manner, a clone of a single client would not work on any other host.
In a host-client configuration where the host (for instance, a mobile phone) needs to verify a client (for instance, an OEM
battery), there is a need to store the secret in the host in order to validate the response from the client. The CheckMac
command (Section 8.2, “CheckMac Command”) allows the chip to securely store the client secret and hide the correct response
value from the pins, returning only a yes/no answer to the system.
Where a user-entered password is a requirement, the CheckMac command also provides a way to both verify the password
without exposing it on the communications bus as well as map the password to a stored value that can have much higher
entropy. See Section 3.3.6 for more details.
Finally, the hash combination of a challenge and secret key can be kept on the chip and XORed with the contents of a slot to
implement an encrypted read (Section 8.12, “Read Command”) , or it can be XORed with encrypted input data to implement an
encrypted write (Section
8.14, “Write Command”).
Each of these operations can be protected against replay attacks by including a random nonce (Section 8.9, “Nonce
Command,”) in the calculation.
All security functions are implemented using the industry-standard SHA-256 secure hash algorithm, which is part of the latest
set of high-security cryptographic algorithms recommended by various governments and cryptographic experts. Section 3.1,
“SHA-256,” includes a reference to the algorithm details. If desired, the SHA-256 algorithm can also be included in an HMAC
sequence (See Section 3.2, “HMAC/SHA-256,” and Section 8.6, “HMAC Command”). The ATSHA204 employs full-sized, 256-
bit secret keys to prevent any kind of exhaustive attack.

4 Atmel ATSHA204
8740B−CRYPTO−5/11
2. Chip Organization
The chip contains the following memory blocks:
• EEPROM
• SRAM
2.1. EEPROM organization
The EEPROM contains a total of 5312 bits, and is divided into the following zones:
• Data
A 512-byte (4K-bit) zone split into 16 general-purpose, read-only, or read/write memory slots of 32 bytes (256 bits) each
that can be used to store keys, calibration data, model number, or other information related to the item to which the Atmel
ATSHA204 chip is attached. The nomenclature slot[YY] indicates the 32-byte value stored in slot yy of the data zone.
• Configuration
An 88-byte (704-bit) zone that contains serial number and other ID information as well as access permission information
for each slot of the data memory. The nomenclature SN[a:b] indicates a range of bytes within a field of the configuration
section.
• OTP
A 64-byte (512-bit) zone of one-time programmable (OTP) bits. Prior to locking the OTP zone, the bits may be freely
written using the standard Write command. The OTP zone can be used to store read-only data. The nomenclature
OTP[bb] indicates a byte within the OTP zone, while OTP[aa:bb] indicates a range of bytes.
Within this document, the terms “slot” and “block” are used interchangeably to mean a single, 256-bit (32-byte) area of a
particular memory zone. The different zones are broken down as follows:
• Data section
16 slots (512 bytes/32 bytes = 16)
• Configuration section
Three blocks (88 bytes/32 bytes = 3).
The 88 bytes are accessible from within a three-block address space.
• OTP section
Two blocks (64 bytes/32 bytes = 2)
Each slot or block has potentially different access permissions. Note that the industry SHA-256 documentation uses the term
“block” to indicate a 512-bit section of the message input. In addition, the I/O section of this document uses the term “block” to
indicate a variable-length aggregate element transferred between the system and the chip.
Many sections of this document refer to a keyID, which is equivalent to the slot number for those slots designated to hold key
values. Key #1 (sometimes referred to as key[1]) is stored in Slot[1], and so on. While all 16 slots can potentially hold keys,
those slots for which clear reads are permitted would not normally be used as keys by the crypto commands.
In this specification, the nomenclature mode:b indicates bit b of the parameter mode.
On shipment from Atmel, the EEPROM contains factory test data that can be used for fixed-value board testing. This data must
be overwritten with the desired contents prior to locking the configuration and/or data sections of the chip. See the Atmel
website for the document containing the specific shipment values.
Atmel ATSHA204
5
8740B−CRYPTO−5/11
2.1.1. Configuration Zone
The 88 bytes in the configuration zone contain manufacturing identification data, general chip and system configuration, and
access restriction control values for the slots within the data zone. The values of these bytes can always be obtained using the
Read command. The bytes of this zone are arranged as shown in Table 2-1.
Table 2-1. Configuration zone
Byte # Name Description Write Read
0 3 SN[0:3]
Part of the serial number value
See the section below, “Special Memory Values in the Config Zone”
Never Always
4 7 RevNum
Chip revision number.
See the section below, “Special Memory Values in the Config Zone”
Never Always
8 12 SN[4:8]
Part of the serial number value.
See the section below, “Special Memory Values in the Config Zone”
Never Always
13 Reserved Set by Atmel. Never Always
14 I2C_Enable
Bit 0:
0 = the chip operates in single-wire interface mode
1 = the chip operates in I2C interface mode
Bits 1-7 are ignored:
These bits are set at the Atmel factory, depending on the part
number, and cannot be changed
Never Always
15 Reserved Set by Atmel Never Always
16 I2C_Address
Bit 0: Ignored
Bits 1-7: For I2C interface parts, the most-significant seven bits of this
byte form the device address value to which this chip will respond. Bits
1,2, and 4-7 are ignored for single-wire interface parts.
Bit 3 (TTLenable):
1 = the I/O levels are VCC referenced
0 = the I/O levels use a fixed reference
See Section 7.4.2 for more information
If config
unlocked
Always
17 TempOffset
Temperature sensor calibration on parts including this feature.
Available for general use otherwise.
If config
unlocked
Always
18 OTPmode
0xAA (Read-only mode) = Writes to the OTP zone are forbidden when
the OTP zone is locked. Reads of all words are permitted.
0x55 (Consumption mode) = Not supported at this time. Contact Atmel
for more information.
0x00 (Legacy mode) = When the OTP zone is locked, writes to the
OTP zone, reads of words 0 and 1, and 32-byte reads are all forbidden.
See Section 9 for more information on compatibility with the Atmel
AT88SA102S device.
All other values of OTPmode are reserved, and should not be used.
If config
unlocked
Always
19 SelectorMode
If 0, then Selector can always be written with UpdateExtra. If non-zero,
Selector can only be written if it currently has a value of zero.
See Section 8.13 for more details.
If config
unlocked
Always

















- 1
- 2
前往页