Volume 3, No. 4, April 2012
Journal of Global Research in Computer Science
RESEARCH PAPER
Available Online at www.jgrcs.info
© JGRCS 2010, All Rights Reserved 39
ENHANCEMENT OF RC6 (RC6_EN) BLOCK CIPHER ALGORITHM AND
COMPARISON WITH RC5 & RC6
Vikas Tyagi
1
, Shrinivas Singh
2
1
Student,Computer Science , Subharti University Meerut (India)
itengg.vikas@gmail.com
2
Computer Science , Subharti University Meerut (India)
shri0123@gmail.com
Abstract: In this paper, we present an enhanced version of RC6 Block Cipher Algorithm (RC6_En – RC6 enhanced version), which is a
symmetric encryption algorithm [1] designed for 256-bit plain text block. RC6 uses four (w-bit) registers for storing plain text and for data-
dependent rotations [2, 3], but this enhanced version (RC6_En) uses eight (w-bit) register that helps to increase the performance as well as
improve security. Its salient feature includes two-variable algebraic expression modulo 2
w
and 2 Box-Type operations, Box-Type I & Box-Type
II. Each Box-Type operation uses two (w-bit) registers. Box-Type I works much like two registers (A & B or C & D) operation in RC6 but in
Box-Type II bitwise exclusive-or is swapped by integer addition modulo 2
w
used in Box-Type I and vice-versa, it improves Diffusion in each
round. This enhanced version needs 2r+4 additive round-keys and uses every round-key twice for encrypting the file. This enhanced version
performs better with respect to RC5[4, 5] and RC6[2, 3] when file size is larger.
Keywords: Cryptography, Data Security, Block cipher, Symmetric encryption.
INTRODUCTION
In cryptography, the use of the symmetric key encryption is
common to ensure data integrity. Symmetric key encryption
code can be divided into the block cipher and stream one
[1][6]. RC6 is a symmetric key block cipher derived
from RC5. It was designed by Ron Rivest, Matt Robshaw,
Ray Sidney and Yiqun Lisa Yin to meet the requirements of
the Advanced Encryption Standard (AES) [7] competition.
The algorithm was one of the five finalists and was also
submitted to the NESSIE [8] and CRYPTREC [9] projects.
It is a proprietary algorithm, patented by RSA Security [10].
Details of RC6:
Like RC5, RC6 is a fully parameterized family of
encryption algorithms. A version of RC6 is more accurately
specified as RC6-w/r/b where the word size is w bits,
encryption consists of a nonnegative number of rounds r and
b denotes the length of the encryption key in bytes. Since
the AES submission is targeted at w = 32 and r = 20, we
shall use RC6 as shorthand to refer to such versions. When
any other value of w or r is intended in the text, the
parameter values will be specified as RC6-w/r. Of particular
relevance to the AES effort will be the versions of RC6 with
16-, 24- and 32-byte keys. For all variants, RC6-w/r/b
operates on units of four w-bit words using the following
basic operations [2].
The operations used in RC6 are defined as followings.
A+B integer addition modulo 2
w
A-B integer subtraction modulo 2
w
A⊕B bitwise exclusive-or of w-bit words
A*B integer multiplication modulo 2
w
A
<<<
B rotation of the w-bit word A to the left by
the amount given by the least significant lg w
bits of B
A
>>>
B rotation of the w-bit word A to the right
by the amount given by the least significant lg w
bits of B
f(x) = x(2x+1)mod 2
w
RC6 is very similar to RC5 in structure, using data-
dependent rotations [3], addition modulo 2
w
and
XOR operations; in fact, RC6 could be viewed as
interweaving two parallel RC5 encryption processes.
However, RC6 does use an extra multiplication operation
not present in RC5 in order to make the rotation dependent
on every bit in a word and not just the least significant few
bits. The base-two logarithm of w will be denoted by lg w
[10].
Encryption and Decryption:
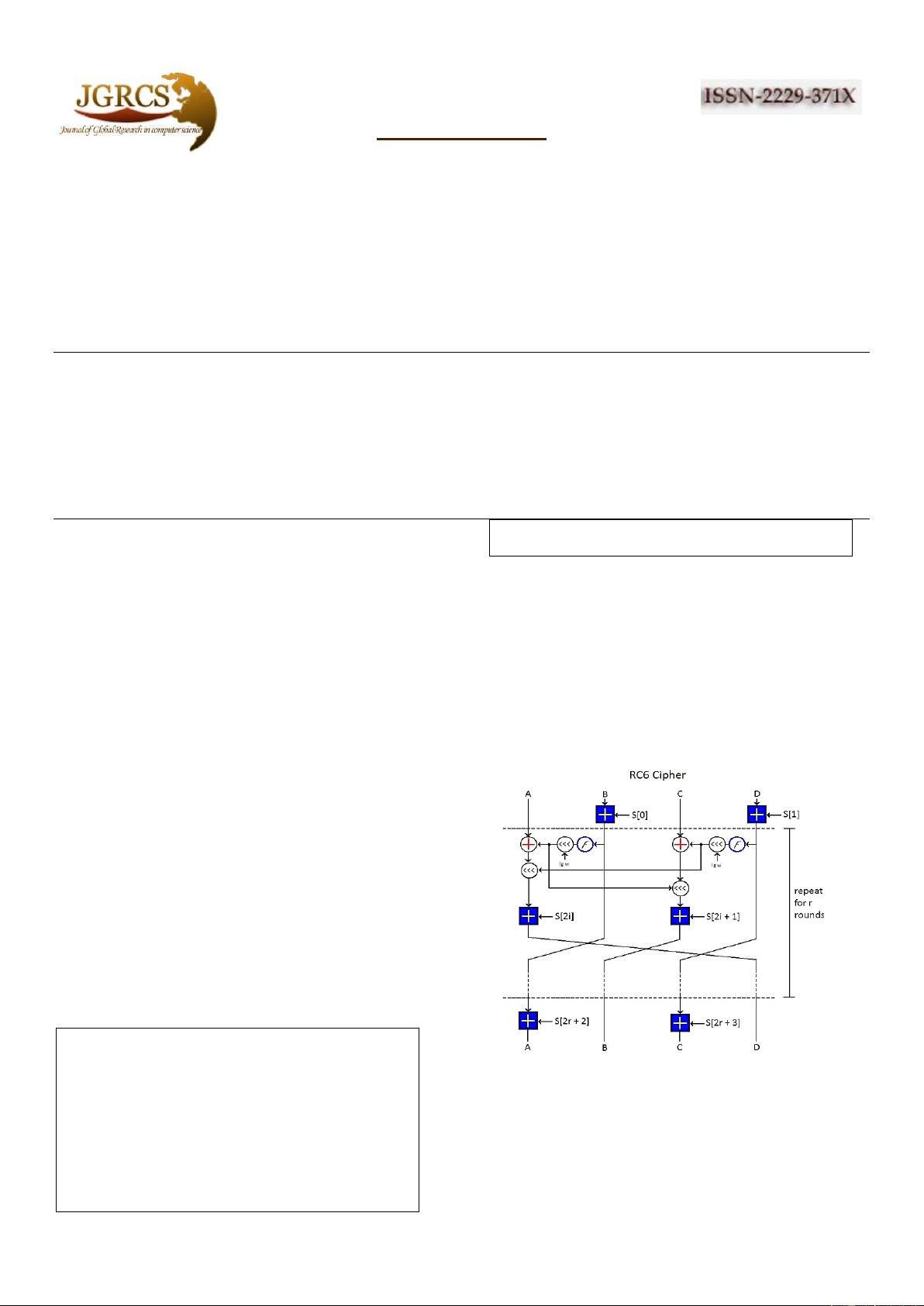
Figure 1: RC6 Block Cipher
RC6 works with four w-bit registers A, B, C, D which
contain the initial input plain-text as well as the output
cipher-text at the end of encryption. The first byte of
plaintext or cipher-text is placed in the least-significant byte
of A, the last byte of plaintext or cipher-text is placed into
the most-significant byte of D [2]. Pseudo code of
encryption and decryption is given below; at first we load