Tofino Security
White Paper
Version 1.0
Published December 20, 2012
Understanding Deep Packet Inspection for SCADA
Security
Contents
Executive Summary .............................................................................................. 1
The Need for Better Security Technology .............................................................. 1
Some Firewall Basics ............................................................................................ 2
The Problem: SCADA/ICS Protocols Have No Granularity .................................... 2
The Solution: Deep Packet Inspection ................................................................... 3
DPI SCADA Security in the Real World ................................................................. 4
Why New Malware Demands DPI Technology ....................................................... 4
Deep Packet Inspection Provides Robust Security for SCADA ............................... 6
References ............................................................................................................ 6
Authors
Eric Byres, P. Eng., ISA Fellow,
CTO and VP of Engineering, Tofino Security.
eric.byres@belden.com
www.tofinosecurity.com

Tofino Security Understanding Deep Packet Inspection for SCADA Security
December 20, 2012 1
Executive Summary
The world’s manufacturing, energy and transportation infrastructures are currently facing a
serious security crisis. These critical systems are largely based on legacy SCADA and Industrial
Control System (ICS) products and protocols. Many of these products are decades old and
were never designed with security in mind.
Yet industry has also embraced new network technologies like Ethernet and TCP/IP, which
have enabled instant access to data throughout the organization, including the plant floor.
While this interlinking improves efficiency, it also significantly increases the exposure of these
control systems to external forces such as worms, viruses and hackers.
Given the 20 year life cycle common for industrial systems, it will be many years before more
secure ICS and SCADA devices and protocols are in widespread use. This leaves millions of
legacy control systems open to attack from even the most inexperienced hacker. If a hacker or
worm can get any control system access, it can exploit the protocol to disable or destroy most
industrial controllers.
The good news is that there is an effective and easy-to-deploy solution to this security crisis.
Using an advanced technology called “Deep Packet Inspection” (DPI), SCADA-aware firewalls
can offer fine-grained control of control system traffic. This white paper explains what DPI is
and how it compares to traditional IT firewalls. It then outlines how engineers can use DPI to
block the malicious or inappropriate traffic, while avoiding needless reliability impacts on the
control system. A case history illustrates how a seaway management company used Modbus
DPI firewalls to secure a mission critical canal system.
The Need for Better Security Technology
Over the past decade, industry has embraced network technologies like Ethernet and TCP/IP
for SCADA and process control systems. This has enabled companies to operate cost effectively
and implement more agile business practices through instant access to data throughout the
organization, including the plant floor.
While companies reap the benefits of these new technologies, many are also discovering the
inherent dangers that result from making control systems more accessible to a wider range of
users. Linking corporate systems together to provide access to managers, customers and
suppliers significantly increases the exposure of these systems to external forces such as
worms, viruses and hackers.
To make matters worse, network protocols used by SCADA and Industrial Control Systems
(ICS) were never designed with security in mind. If they offer any capability to restrict what
users can do over the network, it is primitive and easy to subvert. If an individual is allowed to
read data from a controller, then they can also shut down or reprogram the controller.
These issues are likely to remain with us for at least the next decade. Industrial control systems
are rarely replaced; their useful lives may be 10, 20 or more years. Similarly, the security
limitations of the SCADA and ICS protocols cannot be addressed through patches, as their
functionality is defined in established standards that take years to change.
It will be years before newer, more secure ICS and SCADA devices are in widespread use. This
leaves millions of legacy control systems open to attack from even the most inexperienced
hacker. If a hacker or worm can get any control system access, it can exploit the protocol to
disable or destroy most industrial controllers.
The good news is that there is a solution to this problem. It is easy to use. It doesn’t require the
complete replacement of billions of dollars of existing SCADA and ICS equipment. And it is
very effective.
Tofino Security Understanding Deep Packet Inspection for SCADA Security
December 20, 2012 2
The solution is a technology called “Deep Packet Inspection” (DPI) and it offers fine-grained
control of SCADA network traffic. This white paper explains what DPI is and how it is being
used to secure critical SCADA systems throughout the world.
Some Firewall Basics
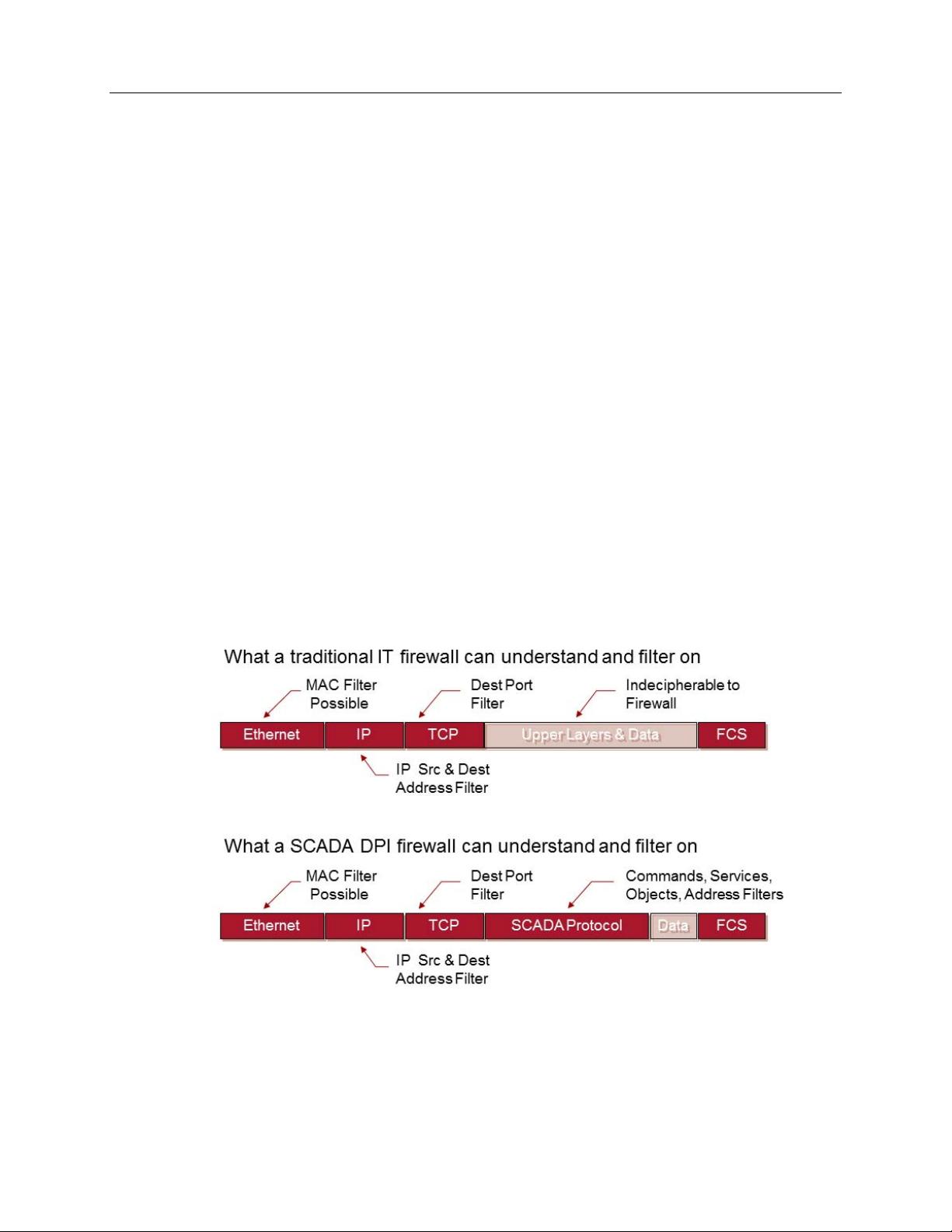
To understand how DPI works, it is important to understand how the traditional IT firewall
works. A firewall is a device that monitors and controls traffic flowing in or between networks.
It starts by intercepting the traffic passing through it and comparing each message to a
predefined set of rules (called Access Control Lists or ACLs). Any messages that do not match
the ACLs are prevented from passing through the firewall.
The traditional firewall allows ACLs to check three primary fields in a message
1
:
1. The address of the computer sending the message (i.e. the Source IP Address),
2. The address of the computer receiving the message (i.e. the Destination IP Address),
3. The application layer protocol contained by the IP message, as indicated in the
destination port number field (i.e. the Destination Port).
The source and destination address checks are easy to understand. These restrict traffic flows
to specific computers, based on their IP addresses. As long as the addresses remain the same,
the firewall can control which computers can interact.
The destination port number needs a bit more explanation. These ports are not physical ports
like an Ethernet or USB port, but instead are special numbers embedded in every TCP or UDP
message. They are used to identify the application protocol being carried in the message. For
example, the Modbus/TCP protocol uses port 502, while the web protocol, HTTP, uses port
80. These numbers are registered under the Internet Assigned Numbers Authority (IANA) and
are rarely ever changed.
To put this all together, imagine you only want to allow web traffic (i.e. HTTP traffic) from a
client at IP address 192.168.1.10 to a web server with an address of 192.168.1.20. Then you
would write an ACL rule something like:
“Allow Src=192.168.1.10 Dst=192.168.1.20 Port=HTTP”
You would load this ACL in the firewall and as long as all three criteria were met, the message
would be allowed through.
Or perhaps you want to block all Modbus traffic from passing through the firewall. You would
simply define a rule that blocks all packets containing 502 in the destination port field.
Seems simple, doesn’t it?
The Problem: SCADA/ICS Protocols Have No Granularity
The problem with this simple scheme is that it is very black and white. Using a traditional IT
firewall, one can either allow a certain protocol or block it. Fine-grained control of the protocol
is impossible.
This is an issue because the SCADA ICS protocols themselves have no granularity. From the
perspective of the port number, a data read message looks EXACTLY like a firmware update
message. If you allow data read messages, from an HMI to a PLC, to pass through a traditional
1
Technically speaking, there are other fields that the typical IT firewall can check, but these three fields account for 99% of all
firewall rules.
Tofino Security Understanding Deep Packet Inspection for SCADA Security
December 20, 2012 3
firewall, you are also allowing programming messages to pass through. This is a serious
security issue.
For example, in the spring of 2009 a US Government agency produced a report for major
energy companies that stated:
“A vulnerability has been identified and verified within the firmware upgrade process
used in control systems deployed in Critical Infrastructure and Key Resources (CIKR)…
development of a mitigation plan is required to protect the installed customer base and
the CIKR of the nation. Firmware Vulnerability Mitigation Steps [includes] blocking
network firmware upgrades with appropriate firewall rules.”
Unfortunately, the IT firewalls available on the market could not differentiate between the
different SCADA commands. As a result, “blocking network firmware upgrades with
appropriate firewall rules” results in the blocking of all SCADA traffic. Since the reliable flow
of SCADA traffic is critical to the average industrial facility, most engineers opted to let
everything pass and take their chances with security.
The Solution: Deep Packet Inspection
Clearly the firewall needs to dig deeper into the protocols to understand exactly what the
protocol is being used for. And that is exactly what Deep Packet Inspection does. After the
traditional firewall rules are applied, the firewall inspects the content contained in the TCP/IP
messages and applies more detailed rules. It is designed to understand the specific SCADA
protocols and then apply filters on fields and values that matter to control systems. Depending
on the protocol, these fields might include commands (such as Register Read vs. Register
Write), objects (such as a Motor Object), services (get vs. set) and PLC address ranges.
Figure 1: Comparing filtering options in a traditional firewall and a DPI
Firewall. A traditional firewall cannot understand the SCADA protocol and thus
can only allow or deny all SCADA messages as a group.















