
Payment Card Industry (PCI)
PIN Transaction Security (PTS)
Point of Interaction (POI)
Modular Derived Test Requirements
Version 3.1
October 2011

Payment Card Industry PTS POI Derived Test Requirements v3.1 October 2011
Copyright 2011 PCI Security Standards Council LLC Page ii
© PCI Security Standards Council LLC 2011
This document and its contents may not be used, copied, disclosed, or distributed for any purpose except
in accordance with the terms and conditions of the Non-Disclosure Agreement executed between the PCI
Security Standards Council LLC and your company. Please review the Non-Disclosure Agreement before
reading this document.
Payment Card Industry PTS POI Derived Test Requirements v3.1 October 2011
Copyright 2011 PCI Security Standards Council LLC Page iii
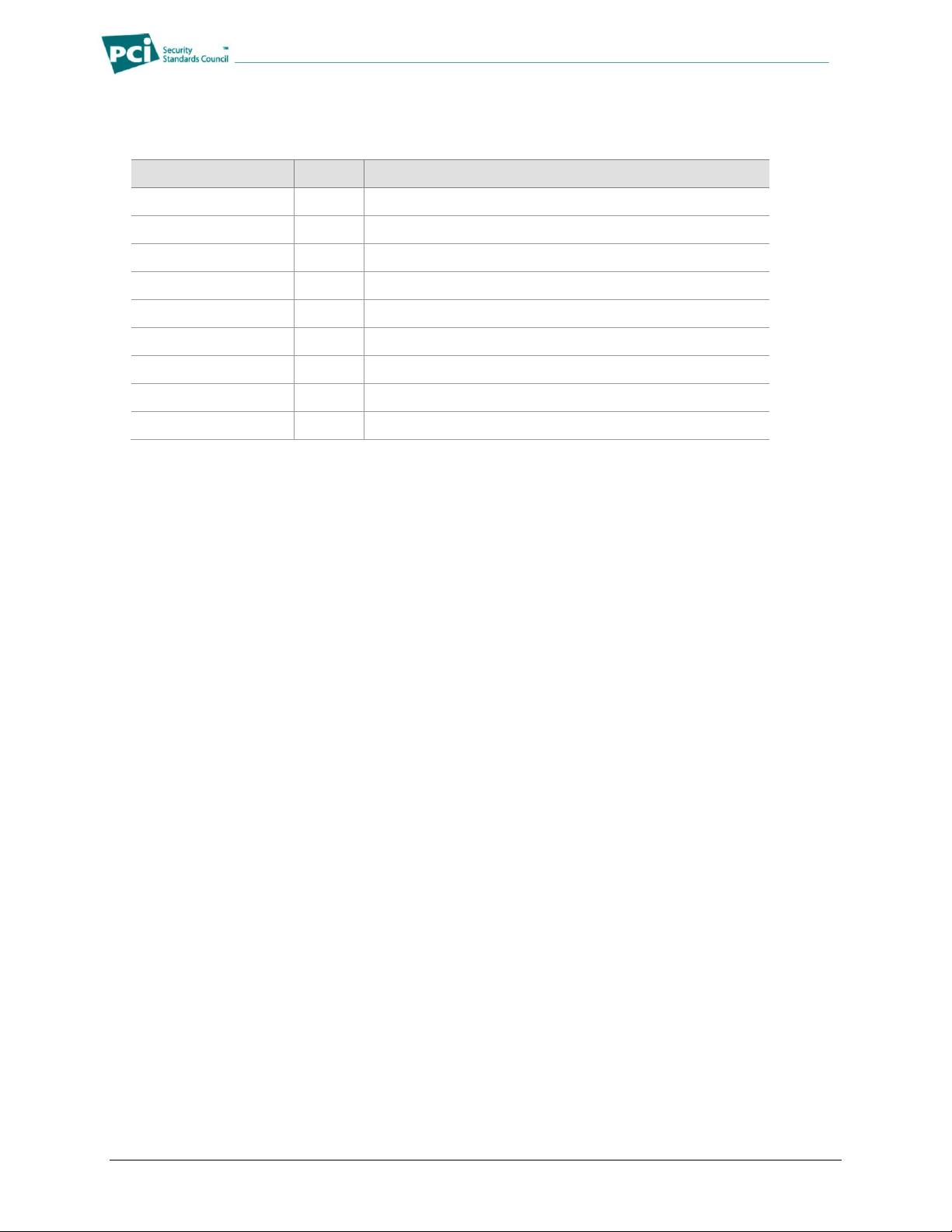
Document Changes
Date
Version
Description
February 2010
3.x
Initial Request-for-Comment Version
April 2010
3.0
Initial public release
October 2011
3.1
Clarifications and errata, updates for non-PIN POIs

Payment Card Industry PTS POI Derived Test Requirements v3.1 October 2011
Copyright 2011 PCI Security Standards Council LLC Page iv
Table of Contents
Document Changes ................................................................................................................................... iii
Introduction .............................................................................................................................................. vii
DTR Module 1: Core Requirements ........................................................................................................... 1
Core Physical Security Derived Test Requirements ............................................................................... 1
DTR A1.1 Tamper-Detection Mechanisms ..................................................................................... 1
DTR A1.2 Independent Security Mechanisms................................................................................ 3
DTR A2 Response to Internal Access ......................................................................................... 4
DTR A3 Robustness Under Changing Environmental and Operational Conditions.................... 6
DTR A4 Protection of Sensitive Functions or Information ........................................................... 7
DTR A5 Audible Tones During PIN Entry .................................................................................... 8
DTR A6 Monitoring During PIN Entry .......................................................................................... 9
DTR A7 Determining Keys Analysis .......................................................................................... 10
DTR A8 Altering User Interface Prompts Cost Analysis ............................................................ 11
DTR A9 Visual Observation Deterrents ..................................................................................... 12
DTR A10 Magnetic-Stripe Reader ............................................................................................... 13
DTR A11 Component Protections against Removal ................................................................... 14
Core Logical Security Derived Test Requirements ............................................................................... 16
DTR B1 Self-Test ....................................................................................................................... 16
DTR B2 Logical Anomalies ........................................................................................................ 18
DTR B3 Firmware Certification .................................................................................................. 19
DTR B4 Firmware Updates........................................................................................................ 20
DTR B5 Differentiation of Entered PIN ...................................................................................... 21
DTR B6 Clearing of Internal Buffers .......................................................................................... 22
DTR B7 Protection of Sensitive Services .................................................................................. 23
DTR B8 Sensitive Services Limits ............................................................................................. 25
DTR B9 Random Numbers ........................................................................................................ 26
DTR B10 Exhaustive PIN Determination ..................................................................................... 27
DTR B11 Key Management ......................................................................................................... 28
DTR B12 Encryption Algorithm Test ............................................................................................ 33
DTR B13 Encryption or Decryption of Arbitrary Data Within the Device ..................................... 34
DTR B14 Clear-Text Key Security ............................................................................................... 35
DTR B15 Transaction Controls .................................................................................................... 36
DTR B16.1 Prompts Under Control of the Cryptographic Unit ....................................................... 37
DTR B16.2 Cryptographically Based Controls ............................................................................... 39
DTR B17 Application Separation ................................................................................................. 41
DTR B18 Minimal Configuration .................................................................................................. 42
DTR B19 Component Integration Documentation ....................................................................... 43
Online PIN Security Derived Test Requirements ................................................................................... 44
DTR C1 Key Substitution ........................................................................................................... 44
Offline PIN Security Derived Test Requirements ................................................................................... 45
DTR D1 Penetration Protection ................................................................................................. 45
DTR D2 ICC Reader Slot Visibility ............................................................................................. 47
DTR D3 ICC Reader Construction (Wires) ................................................................................ 48
DTR D4 PIN Protection During Transmission Between Device and ICC Reader ..................... 49

Payment Card Industry PTS POI Derived Test Requirements v3.1 October 2011
Copyright 2011 PCI Security Standards Council LLC Page v
DTR Module 2: POS Terminal Integration Requirements ...................................................................... 54
POS Terminal Integration Derived Test Requirements ......................................................................... 54
DTR E1 Target of Evaluation (TOE) Identification .................................................................... 54
DTR E2.1 Integration of PIN Entry Functions ............................................................................... 55
DTR E2.2 Overlay Attack Protection ............................................................................................ 56
DTR E3.1 Integration Vulnerabilities ............................................................................................ 57
DTR E3.2 Protection Against Card Trapping ................................................................................ 58
DTR E3.3 PIN Entry Interface Segregation .................................................................................. 59
DTR E3.4 User Interface Consistency .......................................................................................... 60
DTR E3.5 Control of any Numeric Interface ................................................................................. 62
DTR E4.1 Protection against Removal ......................................................................................... 63
DTR E4.2 Unauthorized Removal – Integration Documentation .................................................. 65
DTR E4.3 Unauthorized Removal - Embedded Devices .............................................................. 66
DTR Module 3: Open Protocols Requirements ...................................................................................... 67
IP and Link Layer Derived Test Requirements....................................................................................... 67
DTR F1 Option Identification ..................................................................................................... 67
DTR F2 Vulnerability Assessment ............................................................................................. 68
DTR F3 Security Guidelines ...................................................................................................... 69
DTR F4 Default Configuration ................................................................................................... 70
IP Protocols Derived Test Requirements ............................................................................................... 71
DTR G1 IP Protocol Identification .............................................................................................. 71
DTR G2 Vulnerability Assessment ............................................................................................. 72
DTR G3 Security Guidance........................................................................................................ 73
DTR G4 IP Protocols Configuration ........................................................................................... 74
Security Protocols Derived Test Requirements..................................................................................... 75
DTR H1 Security Protocol Identification .................................................................................... 75
DTR H2 Vulnerability Assessment ............................................................................................. 76
DTR H3 Security Guidance........................................................................................................ 77
DTR H4 Security Protocol Configuration ................................................................................... 78
DTR H5 Guidelines for Use of Keys and Certificates ................................................................ 79
DTR H6 Data Confidentiality ...................................................................................................... 80
DTR H7 Data Integrity ................................................................................................................ 81
DTR H8 Server Authentication .................................................................................................. 82
DTR H9 Message Replay And Exceptions ................................................................................ 83
DTR H10 Random Generator ...................................................................................................... 84
IP Services Derived Test Requirements ................................................................................................. 85
DTR I1 Service Identification .................................................................................................... 85
DTR I2 Vulnerability Assessment ............................................................................................. 86
DTR I3 Security Guidance........................................................................................................ 87
DTR I4 IP Services Configuration ............................................................................................ 88
DTR I5 Session Management .................................................................................................. 89
DTR I6 IP Service Integrity ....................................................................................................... 90
Security Management Derived Test Requirements ............................................................................... 91
DTR J1 Security Guidelines ...................................................................................................... 91
DTR J2 Security Maintenance Measures ................................................................................. 92
DTR J3 Vulnerability Disclosure ............................................................................................... 93
DTR J4 Platform Mechanism Update Guidelines ..................................................................... 94















