MAY 2018 43
Corporate cloud-computing services
provide on-demand, high-performance,
and ecient computational power and
considerable cost reduction. Despite
these benets, cloud computing comes
with certain challenges. Mobile and
broadband bandwidth and eciency
will be a major bottleneck when the
smart homes and smart cars of the
next decade upload vast amounts of
data from hundreds of sensors to cloud
processors. These cloud-based models
will also impose major energy con-
straints on edge devices.
Privacy issues are another important
threat posed by cloud-based systems—
users risk exposing their sensitive
data by sharing it and allowing service
providers to harvest, analyze, or mon-
etize their data. For example, a major-
ity of cloud-based mobile applications
are free, relying on information har-
vesting from their users’ personal data
for targeted advertising. This prac-
tice has a number of privacy implica-
tions and resource impacts for users.
1
Cloud-based machine-learning algo-
rithms can provide benecial services
(for example, health or image-based
search applications), but their reliance
on excessive data collection can have
consequences that are unknown to the
user (for example, face recognition for
targeted social advertising).
Recently, edge computing has been
proposed as a solution to these chal-
lenges by locating the processing
power in edge nodes that are nearer to
the end user—similar to fog computing
at the network edge. In this way, delay-
sensitive data can be analyzed on the
edge nodes and cloud services can be
leveraged for more delay-tolerant tasks.
However, an analytics service or app
provider might not be keen on sharing
their valuable data-processing mod-
els. It is not always possible to assume
that the feasibility of local processing
(for example, a deployed deep-learning
model on an edge device such as a
smartphone or a computer) is a via-
ble solution even if the task duration,
memory, and processing requirements
are not important for the user or if tasks
can be performed when users are not
actively using their devices (for exam-
ple, while the device is being charged).
One could suggest that fully cryp-
tographic–based algorithms are the
ideal solution; however, the complex-
ity of encryption methods can be high
for many IoT applications, especially
those relying on machine-learning
models or modules that need to be con-
tinuously available or online (such as
multimedia applications or sensors
in a self-driving vehicle). This can be
more severe for deep models, which
are nonlinear, complex functions.
These are dicult to estimate with
polynomial functions, which are an
essential component of homomorphic
encryption–based methods.
2
On one hand, complete data ooad-
ing to cloud services can have imme-
diate or future scalability and privacy
risks; on the other hand, techniques
relying on performing complete ana-
lytics at the user end come with their
own resource constraints (such as
storage and bandwidth constraints,
energy limitations, or computational
costs) and user experience penalties.
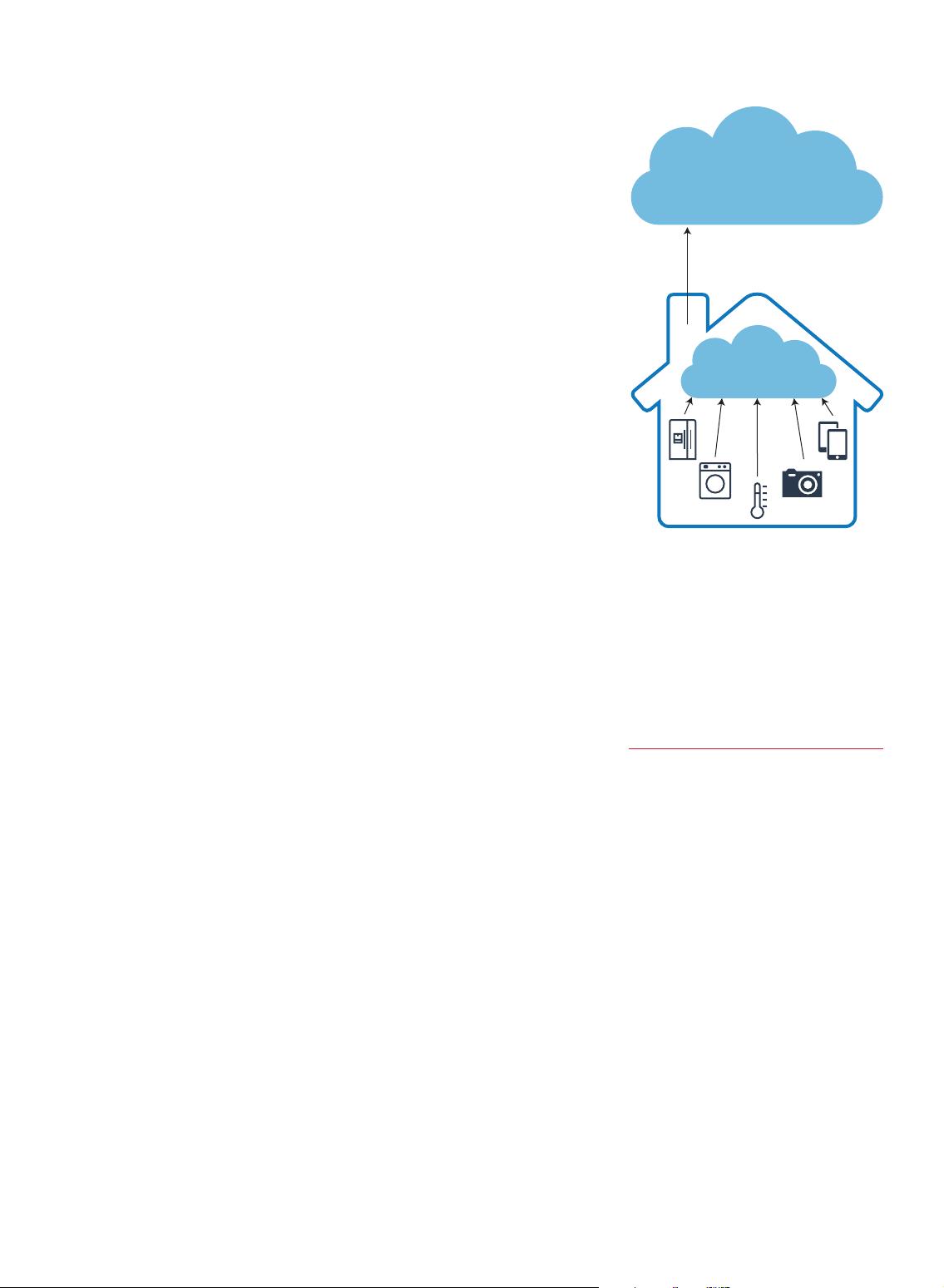
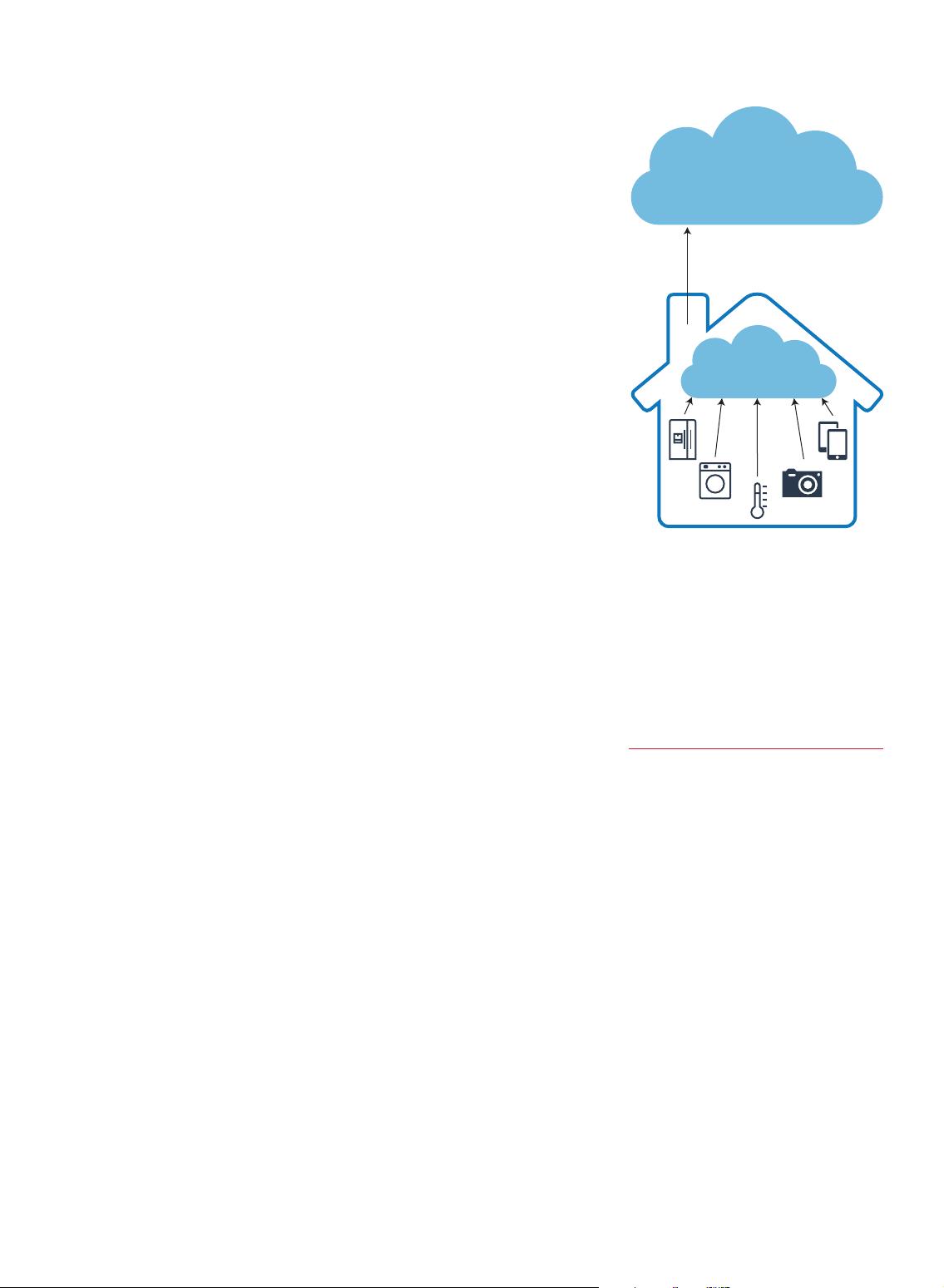
In this article, we present a hybrid
edge-to-cloud architecture where data
processing is accomplished collabo-
ratively between private edge data-
processing units and cloud services.
In this way, we can leverage edge pre-
processing while addressing privacy
concerns and allowing the end user
to benet from cloud-processing e-
ciency. A schematic view of this frame-
work is shown in Figure 1.
Our work focuses on achieving a
compromise between resource-hungry
local analytics on a private edge node
and data-hungry and privacy-invasive
cloud-based services. The least-
necessary amount of processing takes
place on the edge node, which pre-
serves privacy, while the rest of the
processing occurs in the cloud. Our
main objective is to separate the fea-
ture extraction and inference phases;
the former takes place locally, while
the latter takes place in the cloud.
With this approach, sensitive infor-
mation can be removed from the data
during the feature-extraction phase
on the edge node, while reducing
data-transmission rates to the cloud.
The extracted features are transferred
to the cloud server for post-processing,
and the user then receives the results
from the cloud.
Cloud processing
Edge processing
Features
FIGURE . Hybrid edge-to-cloud
framework for privacy-preserving machine
learning. User data is collected and
processed locally on private edge nodes
to preserve sensitive information. The
representation of data that is independent
of sensitive information is sent to a
cloud datacenter for applying complex
inferences.
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 
 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜

 信息提交成功
信息提交成功
评论0