没有合适的资源?快使用搜索试试~ 我知道了~
FCKeditor文件上传漏洞及利用-File-Upload-Vulnerability-in-FCKEditor1
需积分: 0 5 下载量 74 浏览量
2022-08-03
12:35:52
上传
评论
收藏 2.02MB PDF 举报
温馨提示

试读
16页
Exploiting PHP Upload Module ofBypassing File-type CheckExploiting PHP Upload Mo
资源详情
资源评论
资源推荐

Whitepaper
Exploiting PHP Upload Module of
FCKEditor
Bypassing File-type Check
Anant Kochhar
Utkarsh Bhatt
Sabyasachi Samanta

Exploiting PHP Upload Module of FCKEditor
3
TABLE OF CONTENTS
Abstract ..............................................................4
Introduction.........................................................4
Exploits ...............................................................4
The Attack Scenario ..............................................5
Vulnerable Versions ............................................ 15
Impact .............................................................. 15
Recommended Resolutions .................................. 15
About The Authors.............................................. 17
About SecurEyes ................................................ 17
Addendum* ....................................................... 17

Exploiting PHP Upload Module of FCKEditor
4
Abstract
The PHP file upload module in FCKEditor allows developers to offer file upload
functionality to end users. This paper describes a vulnerability which allows attackers
to bypass file-type checks in this module and upload malicious PHP code into the web
servers.
Introduction
FCKEditor (now CKeditor) is an open source WYSIWYG text editor from CKSource
that can be integrated into web applications, to give end users word processor like
interface. FCK stands for ‘Frederico Caldeira Knabben’, the creator of the project, and
the first version was released in 2003.
This editor supports many server side languages like ASP, ASP.NET, PHP etc. The PHP
upload module, for PHP web applications, has a vulnerability which allows remote
attackers to bypass file-type checks. This vulnerability was discovered during the
course of our website audit work.
The vulnerability affects FCKEditor versions 2.6.4 and below.
Note: A different recently discovered vulnerability in the ASP.NET connector file allows
attackers to upload malicious ASP code into vulnerable servers.
Exploits
FCKEditor has built-in ‘filemanager’ package, which allows developers to offer a file
upload and management module to web site end users. For PHP web applications, one
of the relevant files is ‘upload.php’, which is available at the following location:
<site name><fckeditor>/editor/filemanager/connectors/php/upload.php
This file allows end users to upload files into the web server. It has a built in file-type
checker which does not allow PHP files to be uploaded, but a new vulnerability allows
remote attackers to bypass this vulnerability.
Exploiting PHP Upload Module of FCKEditor
5
The Attack Scenario
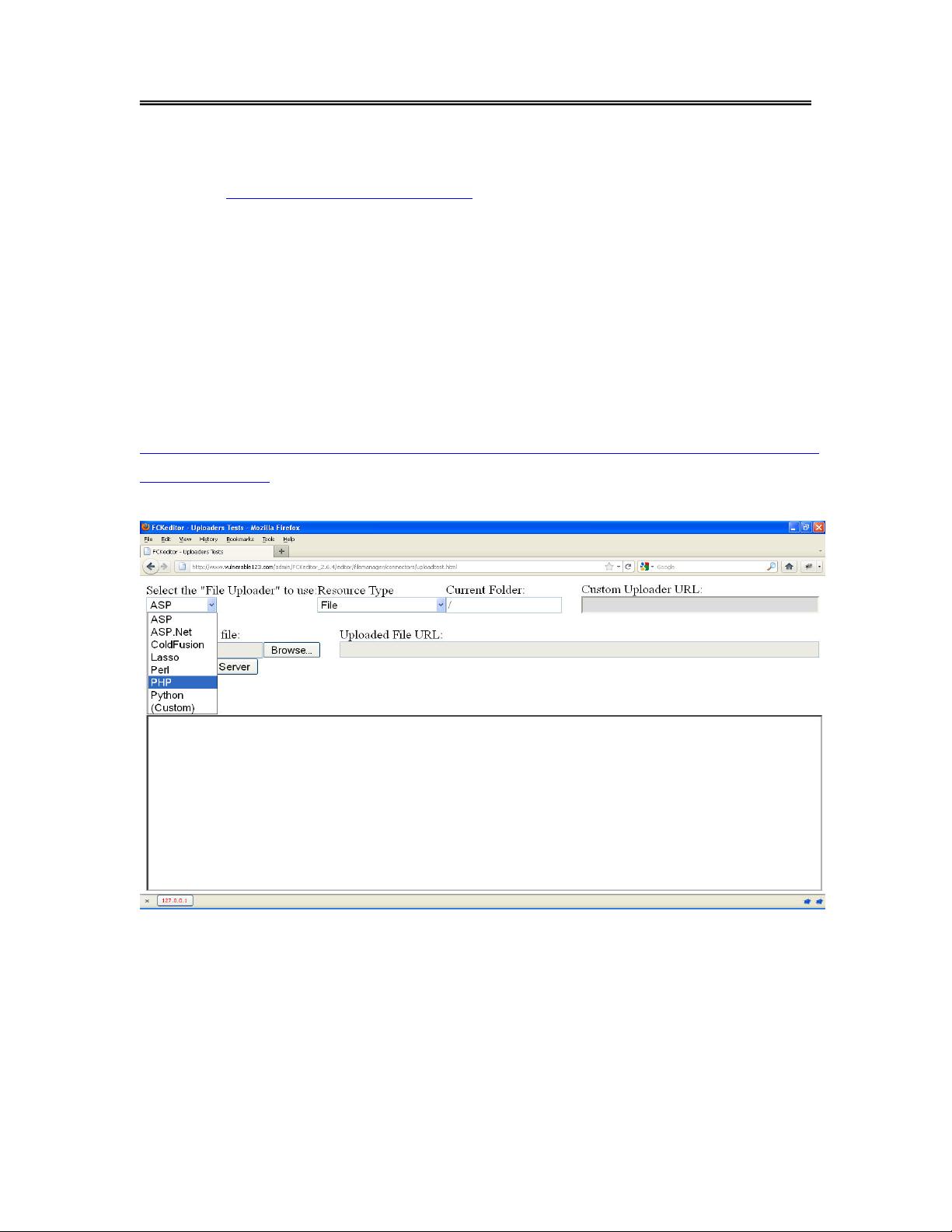
A website, http://www.vulnerable123.com, has integrated FCKEditor version 2.6.4.
For the sake of this proof-of-concept, it is assumed that the test page,
‘uploadtest.html’, packaged with FCKEditor, has not been removed. Also, assume
that there is no session-based access control check on any of the FCKEditor files,
including ‘upload.php’, allowing remote attackers to access them without
authentication.
An attacker browses to the File Upload test page at the URL:
http://www.vulnerable123.com/admin/FCKeditor_2.6.4/editor/filemanager/connectors
/uploadtest.html
He selects the ‘File Uploader’ as PHP, ‘Resource Type’ as File and selects a ‘.txt’ file.
剩余15页未读,继续阅读
乐居买房
- 粉丝: 20
- 资源: 311
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- 二叉树7-1-1.cpp
- android 9.0 原生模拟器 签名文件
- 技术面试最后反问面试官的话 校招面试非技术问题有哪些 非技术问题如何回答.png
- NB-IOT-BC26全网通模块Altium+ CADENCE +PADS三种格式(原理图SCH+PCB封装库)文件.zip
- 基于微信小程序开发的校园失物招领系统源码毕业设计(优质项目源码).zip
- 词向量是一种将自然语言中的单词转换为数值向量的技术,它能够捕捉词义和上下文信息
- nmap与masscan的简单使用
- MyBatis动态SQL.pdf
- 基于stm32单片机protues仿真的温湿度控制系统设计(仿真图、源代码)
- 词向量:自然语言处理的基石
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论0