没有合适的资源?快使用搜索试试~ 我知道了~
资源详情
资源评论
资源推荐
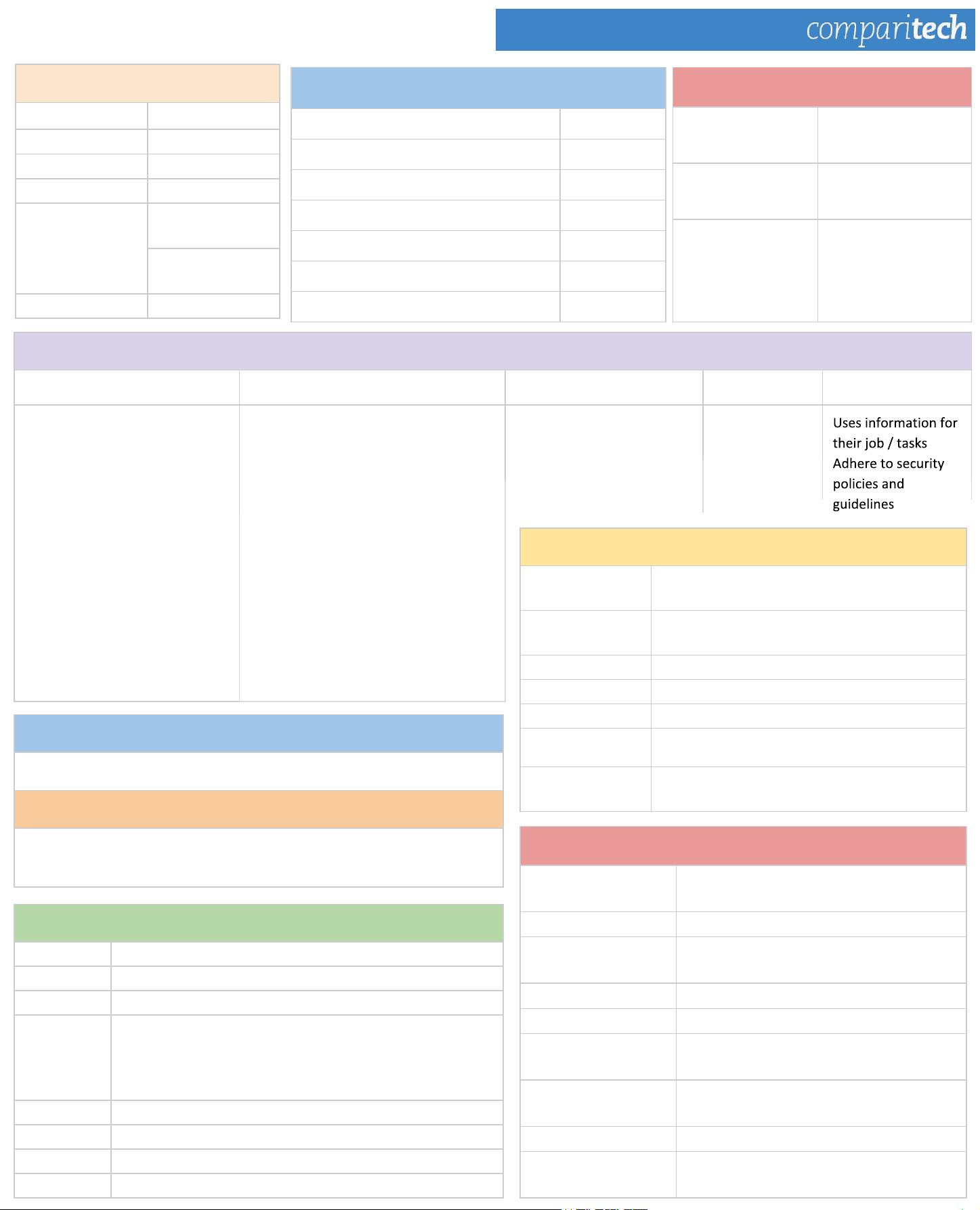
CISSP Cheat Sheet Series
Domain 2: Asset Security
Data Classification Criteria
Value - Usefulness - Age - Association
Classification Levels
Military Sector Private Sector
Top Secret Sensitive
Secret Confidential
Confidential Private
Sensitive but
unclassified
Company
restricted
Company
confidential
Unclassified Public
Data Ownership
Data Ownership Data Custodian Systems Owners Administrators End User
Top level/Primary responsibility for
data
Define level of classification
Define controls for levels of
classification
Define baseline security standards
Impact analysis
Decide when to destroy
information
Grant permissions on daily basis
Ensure compliance with data policy and
data ownership guidelines
Ensure accessibility, maintain and
monitor security
Data archive
Data documentation
Take regular backups , restore to check
validations
Ensure CIA
Conduct user authorization
Implement security controls
Apply Security Controls
Grant permission
for data handling
Typical Data Retention Durations
Business documents
7 years
Invoices
5 years
Accounts Payable / Receivable
7 years
Human Resources - Hired 7 years
Human Resources - Unhired 3 years
Tax records 4 years
Legal correspondence Permanently
Data Remanence
Sanitizing
Series of processes that removes data,
completely
Degaussing
Erase form magnetic tapes etc to ensure not
recoverable
Erasing Deletion of files or media
Overwriting Writing over files, shredding
Zero fill Overwrite all data on drives with zeros
Destruction Physical destruction of data hardware device
Encryption
Make data unreadable without special keys or
algorithm
Data Security Controls
Data in Use Scoping & tailoring
Data at Rest Encryption
Data in Motion
Secure protocols e.g.
https
Security Policies, Standards & Guidelines
Regulatory Required by law and industrial standards
Advisory Not compulsory, but advisable
Informative As guidance to others
Information
Policy
Define best practices for information handling and usage
-Security policies: Technical details of the policies
i.e. SYSTEM security policy: lists hardware / software in
use and steps for using policies
Standards Define usage levels
Guidelines Non-compulsory standards
Procedures Steps for carrying out tasls and policies
Baseline Minimum level of security
Standards
NIST
National Institute of Standards
Technology
NIST SP 800 Series Computer security in a variety of areas
800-14 NIST SP
Securing Information Technology
systems
800-18 NIST Develop security plans
800-27 NIST SP Baseline for achieving security
800-88 NIST
Guidelines for sanitation and disposition,
prevents data remanence
800-137
Continuous monitoring program: define,
establish, implement, analyze and report
800-145 Cloud computing standards
FIPS
Federal Information Processing
Standards
Data Retention Policies
The State of Florida Electronic Records and Records Management Practices,
2010
The European Documents Retention Guide, 2012
sunflowerlq
- 粉丝: 0
- 资源: 6
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功


评论0