# Chisel
[](https://godoc.org/github.com/jpillora/chisel) [](https://github.com/jpillora/chisel/actions?workflow=CI)
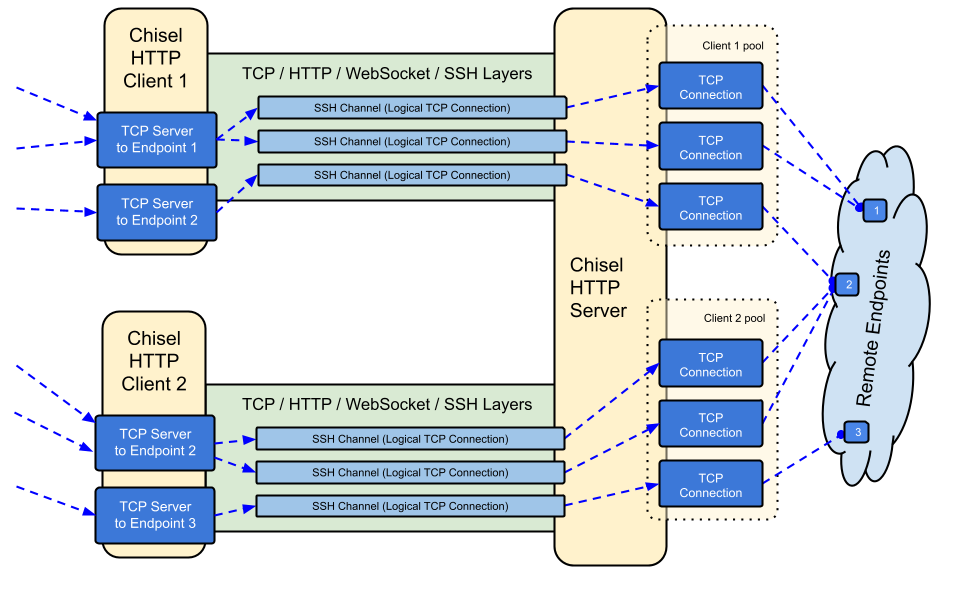
Chisel is a fast TCP/UDP tunnel, transported over HTTP, secured via SSH. Single executable including both client and server. Written in Go (golang). Chisel is mainly useful for passing through firewalls, though it can also be used to provide a secure endpoint into your network.
## Table of Contents
- [Features](#features)
- [Install](#install)
- [Demo](#demo)
- [Usage](#usage)
- [Contributing](#contributing)
- [Changelog](#changelog)
- [License](#license)
## Features
- Easy to use
- [Performant](./test/bench/perf.md)\*
- [Encrypted connections](#security) using the SSH protocol (via `crypto/ssh`)
- [Authenticated connections](#authentication); authenticated client connections with a users config file, authenticated server connections with fingerprint matching.
- Client auto-reconnects with [exponential backoff](https://github.com/jpillora/backoff)
- Clients can create multiple tunnel endpoints over one TCP connection
- Clients can optionally pass through SOCKS or HTTP CONNECT proxies
- Reverse port forwarding (Connections go through the server and out the client)
- Server optionally doubles as a [reverse proxy](http://golang.org/pkg/net/http/httputil/#NewSingleHostReverseProxy)
- Server optionally allows [SOCKS5](https://en.wikipedia.org/wiki/SOCKS) connections (See [guide below](#socks5-guide))
- Clients optionally allow [SOCKS5](https://en.wikipedia.org/wiki/SOCKS) connections from a reversed port forward
- Client connections over stdio which supports `ssh -o ProxyCommand` providing SSH over HTTP
## Install
### Binaries
[](https://github.com/jpillora/chisel/releases) [](https://github.com/jpillora/chisel/releases)
See [the latest release](https://github.com/jpillora/chisel/releases/latest) or download and install it now with `curl https://i.jpillora.com/chisel! | bash`
### Docker
[](https://hub.docker.com/r/jpillora/chisel/) [](https://microbadger.com/images/jpillora/chisel)
```sh
docker run --rm -it jpillora/chisel --help
```
### Fedora
The package is maintained by the Fedora community. If you encounter issues related to the usage of the RPM, please use this [issue tracker](https://bugzilla.redhat.com/buglist.cgi?bug_status=NEW&bug_status=ASSIGNED&classification=Fedora&component=chisel&list_id=11614537&product=Fedora&product=Fedora%20EPEL).
```sh
sudo dnf -y install chisel
```
### Source
```sh
$ go install github.com/jpillora/chisel@latest
```
## Demo
A [demo app](https://chisel-demo.herokuapp.com) on Heroku is running this `chisel server`:
```sh
$ chisel server --port $PORT --proxy http://example.com
# listens on $PORT, proxy web requests to http://example.com
```
This demo app is also running a [simple file server](https://www.npmjs.com/package/serve) on `:3000`, which is normally inaccessible due to Heroku's firewall. However, if we tunnel in with:
```sh
$ chisel client https://chisel-demo.herokuapp.com 3000
# connects to chisel server at https://chisel-demo.herokuapp.com,
# tunnels your localhost:3000 to the server's localhost:3000
```
and then visit [localhost:3000](http://localhost:3000/), we should see a directory listing. Also, if we visit the [demo app](https://chisel-demo.herokuapp.com) in the browser we should hit the server's default proxy and see a copy of [example.com](http://example.com).
## Usage
<!-- render these help texts by hand,
or use https://github.com/jpillora/md-tmpl
with $ md-tmpl -w README.md -->
<!--tmpl,code=plain:echo "$ chisel --help" && go run main.go --help | sed 's#0.0.0-src (go1\..*)#X.Y.Z#' -->
``` plain
$ chisel --help
Usage: chisel [command] [--help]
Version: X.Y.Z
Commands:
server - runs chisel in server mode
client - runs chisel in client mode
Read more:
https://github.com/jpillora/chisel
```
<!--/tmpl-->
<!--tmpl,code=plain:echo "$ chisel server --help" && go run main.go server --help | cat | sed 's#0.0.0-src (go1\..*)#X.Y.Z#' -->
``` plain
$ chisel server --help
Usage: chisel server [options]
Options:
--host, Defines the HTTP listening host – the network interface
(defaults the environment variable HOST and falls back to 0.0.0.0).
--port, -p, Defines the HTTP listening port (defaults to the environment
variable PORT and fallsback to port 8080).
--key, An optional string to seed the generation of a ECDSA public
and private key pair. All communications will be secured using this
key pair. Share the subsequent fingerprint with clients to enable detection
of man-in-the-middle attacks (defaults to the CHISEL_KEY environment
variable, otherwise a new key is generate each run).
--authfile, An optional path to a users.json file. This file should
be an object with users defined like:
{
"<user:pass>": ["<addr-regex>","<addr-regex>"]
}
when <user> connects, their <pass> will be verified and then
each of the remote addresses will be compared against the list
of address regular expressions for a match. Addresses will
always come in the form "<remote-host>:<remote-port>" for normal remotes
and "R:<local-interface>:<local-port>" for reverse port forwarding
remotes. This file will be automatically reloaded on change.
--auth, An optional string representing a single user with full
access, in the form of <user:pass>. It is equivalent to creating an
authfile with {"<user:pass>": [""]}. If unset, it will use the
environment variable AUTH.
--keepalive, An optional keepalive interval. Since the underlying
transport is HTTP, in many instances we'll be traversing through
proxies, often these proxies will close idle connections. You must
specify a time with a unit, for example '5s' or '2m'. Defaults
to '25s' (set to 0s to disable).
--backend, Specifies another HTTP server to proxy requests to when
chisel receives a normal HTTP request. Useful for hiding chisel in
plain sight.
--socks5, Allow clients to access the internal SOCKS5 proxy. See
chisel client --help for more information.
--reverse, Allow clients to specify reverse port forwarding remotes
in addition to normal remotes.
--tls-key, Enables TLS and provides optional path to a PEM-encoded
TLS private key. When this flag is set, you must also set --tls-cert,
and you cannot set --tls-domain.
--tls-cert, Enables TLS and provides optional path to a PEM-encoded
TLS certificate. When this flag is set, you must also set --tls-key,
and you cannot set --tls-domain.
--tls-domain, Enables TLS and automatically acquires a TLS key and
certificate using LetsEncrypt. Setting --tls-domain requires port 443.
You may specify multiple --tls-domain flags to serve multiple domains.
The resulting files are cached in the "$HOME/.cache/chisel" directory.
You can modify this path by setting the CHISEL_LE_CACHE variable,
or disable caching by setting this variable to "-". You can optionally
provide a certificate notification email by setting CHISEL_LE_EMAIL.
--tls-ca, a path to a PEM encoded CA certificate bundle or a directory
holding multiple PEM encode CA certificate bundle files, which is used to
validate client connections. The provided CA certificates will be used
instead of the system roots. This is commonly used to implement mutual-TLS.
--pid Ge
没有合适的资源?快使用搜索试试~ 我知道了~
chisel - 通过HTTP传输的TCP隧道.zip

共61个文件
go:45个
yml:3个
md:3个
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 139 浏览量
2023-07-18
20:06:40
上传
评论
收藏 66KB ZIP 举报
温馨提示
chisel - 通过HTTP传输的TCP隧道.zip
资源推荐
资源详情
资源评论
收起资源包目录
 chisel - 通过HTTP传输的TCP隧道.zip (61个子文件)
chisel - 通过HTTP传输的TCP隧道.zip (61个子文件)  chisel-master
chisel-master  go.mod 732B
go.mod 732B .github
.github  dependabot.yml 319B
dependabot.yml 319B workflows
workflows  ci.yml 2KB
ci.yml 2KB goreleaser.yml 754B
goreleaser.yml 754B go.sum 4KB
go.sum 4KB Makefile 2KB
Makefile 2KB LICENSE 1KB
LICENSE 1KB client
client  client_test.go 2KB
client_test.go 2KB client.go 8KB
client.go 8KB client_connect.go 3KB
client_connect.go 3KB Dockerfile 447B
Dockerfile 447B test
test  e2e
e2e  auth_test.go 1KB
auth_test.go 1KB udp_test.go 2KB
udp_test.go 2KB tls_test.go 3KB
tls_test.go 3KB base_test.go 1KB
base_test.go 1KB setup_test.go 3KB
setup_test.go 3KB socks_test.go 152B
socks_test.go 152B cert_utils_test.go 6KB
cert_utils_test.go 6KB proxy_test.go 132B
proxy_test.go 132B bench
bench  perf.md 2KB
perf.md 2KB userfile 7B
userfile 7B main.go 4KB
main.go 4KB .gitignore 325B
.gitignore 325B server
server  server_handler.go 4KB
server_handler.go 4KB server.go 6KB
server.go 6KB server_listen.go 3KB
server_listen.go 3KB example
example  reverse-tunneling-authenticated.md 3KB
reverse-tunneling-authenticated.md 3KB fly.toml 199B
fly.toml 199B Flyfile 110B
Flyfile 110B users.json 151B
users.json 151B README.md 16KB
README.md 16KB main.go 14KB
main.go 14KB share
share  compat.go 2KB
compat.go 2KB version.go 221B
version.go 221B ccrypto
ccrypto  determ_rand.go 799B
determ_rand.go 799B keys.go 853B
keys.go 853B cio
cio  pipe.go 739B
pipe.go 739B logger.go 1KB
logger.go 1KB stdio.go 173B
stdio.go 173B cos
cos  common.go 530B
common.go 530B pprof.go 239B
pprof.go 239B signal.go 972B
signal.go 972B signal_windows.go 219B
signal_windows.go 219B cnet
cnet  connstats.go 461B
connstats.go 461B meter.go 3KB
meter.go 3KB conn_ws.go 1KB
conn_ws.go 1KB http_server.go 2KB
http_server.go 2KB conn_rwc.go 699B
conn_rwc.go 699B tunnel
tunnel  tunnel.go 4KB
tunnel.go 4KB tunnel_in_proxy.go 3KB
tunnel_in_proxy.go 3KB wg.go 465B
wg.go 465B tunnel_in_proxy_udp.go 5KB
tunnel_in_proxy_udp.go 5KB tunnel_out_ssh_udp.go 3KB
tunnel_out_ssh_udp.go 3KB udp.go 608B
udp.go 608B tunnel_out_ssh.go 2KB
tunnel_out_ssh.go 2KB settings
settings  config.go 409B
config.go 409B remote_test.go 3KB
remote_test.go 3KB users.go 3KB
users.go 3KB remote.go 6KB
remote.go 6KB user.go 488B
user.go 488B env.go 786B
env.go 786B共 61 条
- 1
资源评论

AbelZ_01
- 粉丝: 885
- 资源: 5441
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
