没有合适的资源?快使用搜索试试~ 我知道了~
300-710 - SCNF co.pdf
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
0 下载量 81 浏览量
2022-07-10
13:57:57
上传
评论
收藏 643KB PDF 举报
温馨提示

试读
32页
300-710 - SCNF co.pdf
资源推荐
资源详情
资源评论

QUESTION 1
Which CLI command is used to control special handling of ClientHello messages?
A. system support ssl-client-hello-tuning
B. system support ssl-client-hello-display
C. system support ssl-client-hello-force-reset
D. system support ssl-client-hello-reset
Answer: A
QUESTION 2
Which command is typed at the CLI on the primary Cisco FTD unit to temporarily stop running
high-availability?
A. configure high-availability resume
B. configure high-availability disable
C. system support network-options
D. configure high-availability suspend
Answer: B
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/610/configuration/guide/fpmc-configguide-
v61/firepower_threat_defense_high_availability.html
QUESTION 3
Which command must be run to generate troubleshooting files on an FTD?
A. system support view-files
B. sudo sf_troubleshoot.pl
C. system generate-troubleshoot all
D. show tech-support
Answer: B
Explanation:
https://www.cisco.com/c/en/us/support/docs/security/sourcefire-defense-center/117663-technote-
SourceFire-00.html
QUESTION 4
When do you need the file-size command option during troubleshooting with packet capture?
A. when capture packets are less than 16 MB
B. when capture packets are restricted from the secondary memory
C. when capture packets exceed 10 GB
D. when capture packets exceed 32 MB
Answer: D
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/620/configuration/guide/fpmc-configguide-
v62/troubleshooting_the_system.html
QUESTION 5
What is a functionality of port objects in Cisco FMC?
A. to mix transport protocols when setting both source and destination port conditions in a rule
B. to represent protocols other than TCP, UDP, and ICMP
C. to represent all protocols in the same way
D. to add any protocol other than TCP or UDP for source port conditions in access control rules.
Answer: B
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/620/configuration/guide/fpmc-configguide-
v62/reusable_objects.html
QUESTION 6
Within Cisco Firepower Management Center, where does a user add or modify widgets?
A. dashboard
B. reporting
C. context explorer
D. summary tool
Answer: A
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-configguide-
v60/Using_Dashboards.html
QUESTION 7
A network engineer is configuring URL Filtering on Firepower Threat Defense. Which two port
requirements on the Firepower Management Center must be validated to allow communication
with the cloud service? (Choose two.)
A. outbound port TCP/443
B. inbound port TCP/80
C. outbound port TCP/8080
D. inbound port TCP/443
E. outbound port TCP/80
Answer: AE
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-configguide-
v60/SecurityInternet_Accessand_Communication_Ports.html
QUESTION 8
What is the maximum bit size that Cisco FMC supports for HTTPS certificates?
A. 1024
B. 8192
C. 4096
D. 2048
Answer: D
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/610/configuration/guide/fpmc-configguide-
v61/system_configuration.html
QUESTION 9
Which limitation applies to Cisco Firepower Management Center dashboards in a multidomain
environment?
A. Child domains can view but not edit dashboards that originate from an ancestor domain.
B. Child domains have access to only a limited set of widgets from ancestor domains.
C. Only the administrator of the top ancestor domain can view dashboards.
D. Child domains cannot view dashboards that originate from an ancestor domain.
Answer: D
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-configguide-
v60/Using_Dashboards.html
QUESTION 10
Which two statements about deleting and re-adding a device to Cisco FMC are true? (Choose
two.)
A. An option to re-apply NAT and VPN policies during registration is available, so users do not need
to re-apply the policies after registration is completed.
B. Before re-adding the device in Cisco FMC, you must add the manager back in the device.
C. No option to delete and re-add a device is available in the Cisco FMC web interface.
D. The Cisco FMC web interface prompts users to re-apply access control policies.
E. No option to re-apply NAT and VPN policies during registration is available, so users need to reapply
the policies after registration is completed.

Answer: DE
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-configguide-
v60/Device_Management_Basics.html
QUESTION 11
What is a behavior of a Cisco FMC database purge?
A. User login and history data are removed from the database if the User Activity check box is
selected.
B. Data can be recovered from the device.
C. The appropriate process is restarted.
D. The specified data is removed from Cisco FMC and kept for two weeks.
Answer: C
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/620/configuration/guide/fpmc-configguide-
v62/management_center_database_purge.pdf
5
QUESTION 12
Which two packet captures does the FTD LINA engine support? (Choose two.)
A. Layer 7 network ID
B. source IP
C. application ID
D. dynamic firewall importing
E. protocol
Answer: BE
Explanation:
https://www.cisco.com/c/en/us/support/docs/security/firepower-ngfw/212474-working-withfirepower-
threat-defense-f.html
QUESTION 13
Which two features of Cisco AMP for Endpoints allow for an uploaded file to be blocked? (Choose
two.)
A. application blocking
B. simple custom detection
C. file repository
D. exclusions
E. application whitelisting
Answer: AB
QUESTION 14
Which action should you take when Cisco Threat Response notifies you that AMP has identified a
file as malware?
A. Add the malicious file to the block list.
B. Send a snapshot to Cisco for technical support.
C. Forward the result of the investigation to an external threat-analysis engine.
D. Wait for Cisco Threat Response to automatically block the malware.
Answer: A
QUESTION 15
Which Cisco Advanced Malware Protection for Endpoints policy is used only for monitoring
endpoint actively?
A. Windows domain controller
B. audit
C. triage
D. protection
Answer: B

Explanation:
https://www.cisco.com/c/en/us/support/docs/security/amp-endpoints/214933-amp-for-endpointsGet
Latest & Actual 300-710 Exam's Question and Answers from Lead2pass.
deployment-methodology.html
QUESTION 16
What is a valid Cisco AMP file disposition?
A. non-malicious
B. malware
C. known-good
D. pristine
Answer: B
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-configguide-
v60/Reference_a_wrapper_Chapter_topic_here.html
QUESTION 17
In a Cisco AMP for Networks deployment, which disposition is returned if the cloud cannot be
reached?
A. unavailable
B. unknown
C. clean
D. disconnected
Answer: A
QUESTION 18
Which two remediation options are available when Cisco FMC is integrated with Cisco ISE?
(Choose two.)
A. dynamic null route configured
B. DHCP pool disablement
C. quarantine
D. port shutdown
E. host shutdown
Answer: CD
Explanation:
https://www.cisco.com/c/en/us/support/docs/security/identity-services-engine/210524-configurefirepower-
6-1-pxgrid-remediati.html
QUESTION 19
Which connector is used to integrate Cisco ISE with Cisco FMC for Rapid Threat Containment?
A. pxGrid
B. FTD RTC
C. FMC RTC
D. ISEGrid
Answer: A
QUESTION 20
What is the maximum SHA level of filtering that Threat Intelligence Director supports?
A. SHA-1024
B. SHA-4096
C. SHA-512
D. SHA-256
Answer: D
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/623/configuration/guide/fpmc-configguide-
v623/cisco_threat_intelligence_directortid_.html
QUESTION 21
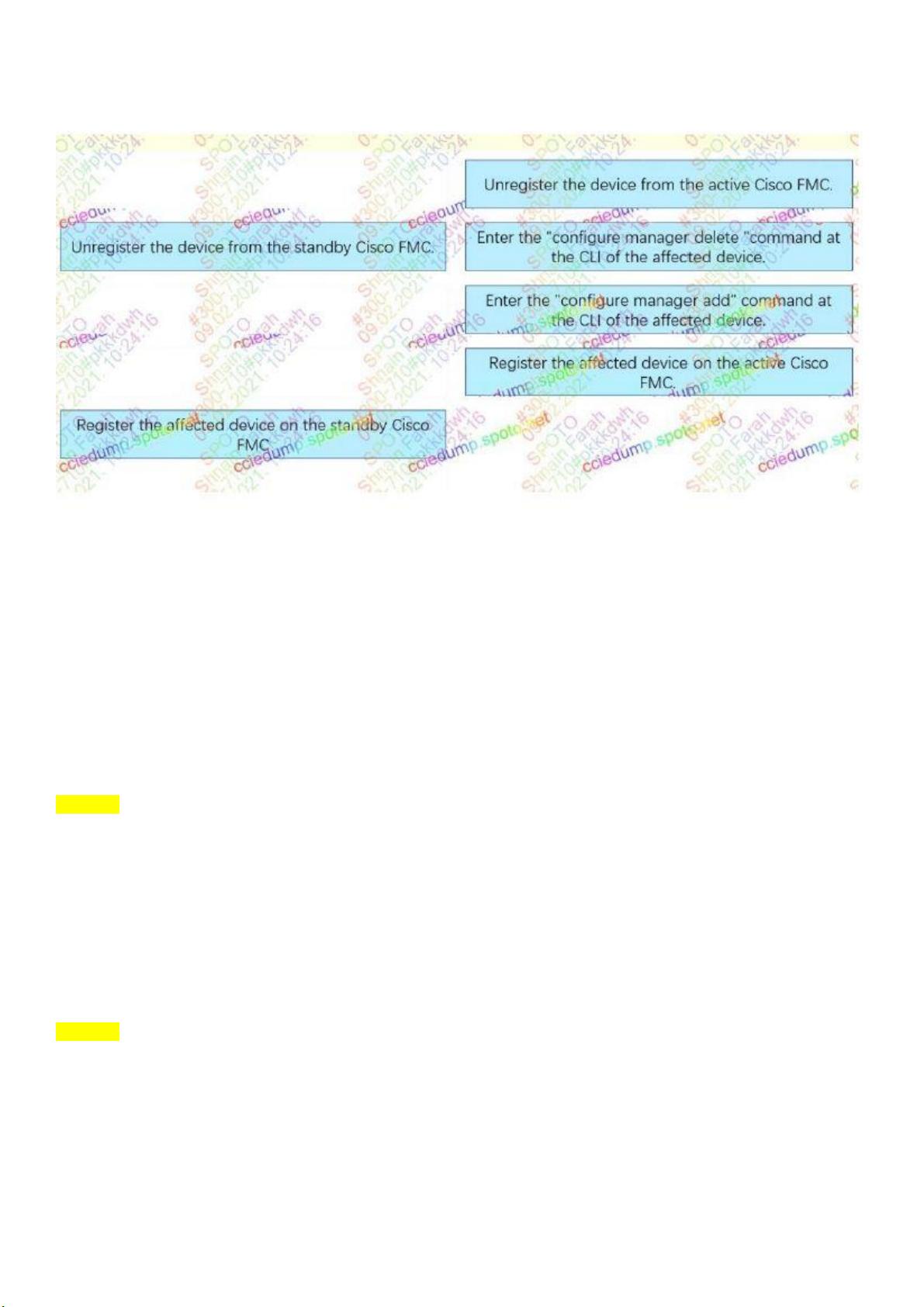
Drag and Drop Question
Drag and drop the steps to restore an automatic device registration failure on the standby Cisco
FMC from the left into the correct order on the right. Not all options are used.
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/firepower/620/configuration/guide/fpmc-configguide-
v62/firepower_management_center_high_availability.html#id_32288
QUESTION 22
With Cisco Firepower Threat Defence software, which interface mode do you configure to
Passively receive traffic that passes the appliance?
A. transparent
B. routed
C. passive
D. inline set
E. inline tap
Answer: C
QUESTION 23
Which description of a correlation policy configuration in the Cisco Firepower Management
Center is true?
A. The system displays correlation policies that are created on all of the domains in a multidomain
deployment
B. Deleting a response group deletes the responses of that group
C. You cannot add a host profile qualification to a correlation rule that is triggered by a malware
event
D. Correlation policy priorities override whitelist priorities
Answer: C
QUESTION 24
What is a result of enabling Cisco FTD clustering?
9
A. For the dynamic routing feature, if the master unit fails, the newly elected master unit maintains all
existing connections.
B. Integrated Routing and Bridging is supported on the master unit.
C. Site-to-site VPN functionality is limited to the master unit, and all VPN connections are dropped if
the master unit fails.
D. All Firepower appliances can support Cisco FTD clustering.
剩余31页未读,继续阅读
资源评论

优质网络系统领域创作者
- 粉丝: 2974
- 资源: 2408

下载权益

C知道特权

VIP文章

课程特权
开通VIP
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
