没有合适的资源?快使用搜索试试~ 我知道了~
NSE4-6学习文档手册.pdf
1.该资源内容由用户上传,如若侵权请联系客服进行举报
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
2.虚拟产品一经售出概不退款(资源遇到问题,请及时私信上传者)
版权申诉
温馨提示

试读
60页
NSE4_6学习文档手册.pdf
资源推荐
资源详情
资源评论

6.4 update
Number: 000-000
Passing Score
: 800
Time Limit
: 120 min
File Version
: 1.0

Exam A
QUESTION 1
Which two statements are true when FortiGate is in transparent mode? (Choose two.)
A. By default, all interfaces are part of the same broadcast domain.
B. The existing network IP schema must be changed when installing a transparent mode FortiGate in the
network.
C. Static routes are required to allow traffic to the next hop.
D. FortiGate forwards frames without changing the MAC address.
Correct Answer: AD
Section: (none)
Explanation
Explanation/Reference:
QUESTION 2
What inspection mode does FortiGate use if it is configured as a policy-based next-generation firewall
(NGFW)?
A. Full Content inspection
B. Proxy-based inspection
C. Certificate inspection
D. flow-based inspection
Correct Answer: D
Section: (none)
Explanation
Explanation/Reference:
QUESTION 3
Which two statements about IPsec authentication on FortiGate are correct? (Choose two.)
A. For a stronger authentication, you can also enable extended authentication (XAuth) to request the
remote peer to provide a username and password
B. FortiGate supports pre-shared key and signature as authentication methods.
C. Enabling XAuth results in a faster authentication because fewer packets are exchanged.
D. A Certificate is not required on the remote peer when you set the signature as the authentication
method.
Correct Answer: AB
Section: (none)
Explanation
Explanation/Reference:
QUESTION 4
Which scanning technique on FortiGate can be enabled only on the CLI?
A. Heuristics scan
B. Trojan scan

C.
A
ntivirus scan
D. Ransomware scan
Correct Answer: A
Section: (none)
Explanation
Explanation/Reference:
QUESTION 5
Which two policies must be configured to allow traffic on a policy-based next-generation firewall (NGFW)
FortiGate? (Choose two.)
A. Firewall policy
B. Policy rule
C. Security policy
D. SSL inspection and authentication policy
Correct Answer: CD
Section: (none)
Explanation
Explanation/Reference:
QUESTION 6
You have enabled logging on your FortiGate device for Event logs and all Security logs, and you have set
up logging to use the FortiGate local disk. What is the
default behavior when the local disk is full?
A. Logs are overwritten and the only warning is issued when log disk usage reaches the threshold of 95%.
B. No new log is recorded until you manually clear logs from the local disk.
C. Logs are overwritten and the first warning is issued when log disk usage reaches the threshold of 75%.
D. No new log is recorded after the warning is issued when log disk usage reaches the threshold of 95%.
Correct Answer: C
Section: (none)
Explanation
Explanation/Reference:
QUESTION 7
Refer to the exhibit, which contains a Performance SLA configuration.
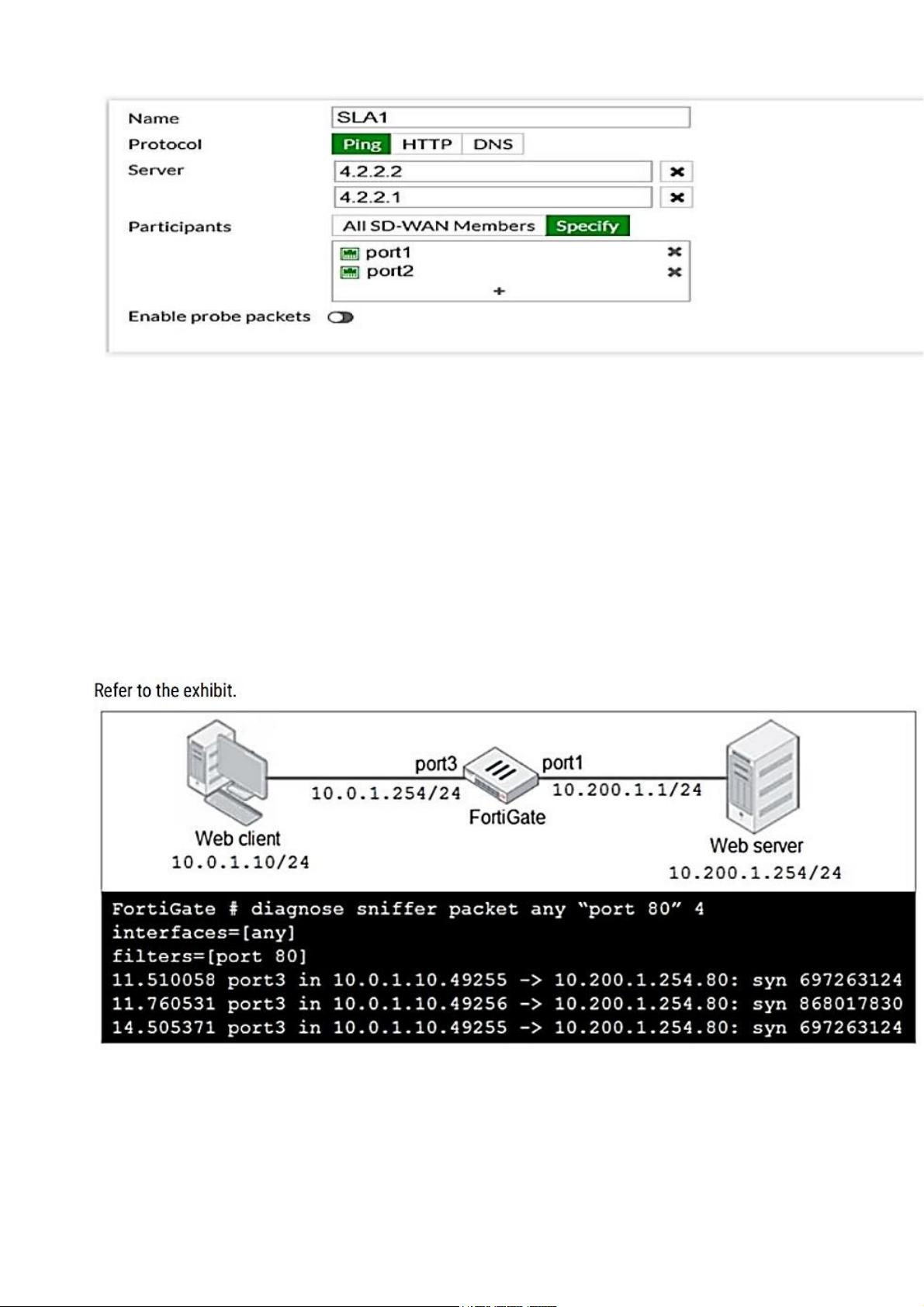
An administrator has configured a performance SLA on FortiGate, which failed to generate any traffic.
Why is FortiGate not generating any traffic for the performance SLA?
A. There may not be a static route to route the performance SLA traffic.
B. You need to turn on the Enable probe packets switch.
C. The Ping protocol is not supported for the public servers that are configured.
D. Participants configured are not SD-WAN members.
Correct Answer: B
Section: (none)
Explanation
Explanation/Reference:
QUESTION 8
In the network shown in the exhibit, the web client cannot connect to the HTTP web server. The
administrator runs the FortiGate built-in sniffer and
gets the output as shown in the exhibit.
What should the administrator do next to troubleshoot the problem?
A. Run a sniffer on the web server.
B. Capture the traffic using an external sniffer connected to port1.

C. Execute another sniffer in the FortiGate, this time with the filter host 10.0.1.10
D. Execute a debug flow.
Correct Answer: D
Section: (none)
Explanation
Explanation/Reference:
QUESTION 9
Refer to the exhibit to view the application control profile.
Users who use Apple FaceTime video conferences are unable to set up meetings.
In this scenario, which statement is true?
A. Apple FaceTime belongs to the custom monitored filter.
B. The category of Apple FaceTime is being monitored.
C. Apple FaceTime belongs to the custom blocked filter.
D. The category of Apple FaceTime is being blocked.
Correct Answer: C
剩余59页未读,继续阅读
资源评论

 weixin_437798282023-08-30资源内容详细全面,与描述一致,对我很有用,有一定的使用价值。
weixin_437798282023-08-30资源内容详细全面,与描述一致,对我很有用,有一定的使用价值。
资料库01
- 粉丝: 293
- 资源: 2359

下载权益

C知道特权

VIP文章

课程特权
开通VIP
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
