Copyright 2004-2010, Tenable Network Security, Inc.
2
Table of Contents
TABLE OF CONTENTS ........................................................................................................................................ 2
INTRODUCTION ................................................................................................................................................... 3
NESSUS UI OVERVIEW .................................................................................................................................... 3
DESCRIPTION ............................................................................................................................................................ 3
SUPPORTED PLATFORMS .......................................................................................................................................... 4
INSTALLATION ..................................................................................................................................................... 4
OPERATION ............................................................................................................................................................ 4
OVERVIEW ................................................................................................................................................................. 4
Connect to Nessus GUI ................................................................................................................................. 4
POLICY OVERVIEW .................................................................................................................................................... 6
CREATING A POLICY ................................................................................................................................................. 7
General................................................................................................................................................................ 7
Credentials ....................................................................................................................................................... 11
Plugins ............................................................................................................................................................... 14
Preferences ...................................................................................................................................................... 17
IMPORTING AND COPYING POLICIES..................................................................................................................... 30
CREATING AND LAUNCHING A SCAN ..................................................................................................................... 30
REPORTS ................................................................................................................................................................. 32
Browse .............................................................................................................................................................. 32
Report Filters .................................................................................................................................................. 35
Compare ........................................................................................................................................................... 38
Upload & Download ...................................................................................................................................... 39
.nessus File Format ...................................................................................................................................... 41
Delete ................................................................................................................................................................ 41
USERS...................................................................................................................................................................... 41
OTHER NESSUS CLIENTS .............................................................................................................................. 42
UNIX COMMAND LINE INTERFACE ......................................................................................................................... 42
Converting a Report ..................................................................................................................................... 43
Command Line using .nessus Files ........................................................................................................ 44
Scan Command .............................................................................................................................................. 45
SECURITYCENTER ................................................................................................................................................... 45
ABOUT TENABLE NETWORK SECURITY ................................................................................................ 47
Copyright 2004-2010, Tenable Network Security, Inc.
3
Introduction
This document describes how to use Tenable Network Security’s Nessus user interface
(UI). Please share your comments and suggestions with us by emailing them to
support@tenablesecurity.com.
The Nessus UI is a web-based interface to the Nessus vulnerability scanner. To use the
client, you must have an operational Nessus scanner deployed and be familiar with its use.
Standards and Conventions
Throughout the documentation, filenames, daemons and executables are indicated with a
courier bold font such as gunzip, httpd and /etc/passwd.
Command line options and keywords will also be printed with the courier bold font.
Command line options may or may not include the command line prompt and output text
from the results of the command. Often, the command being run will be boldfaced to
indicate what the user typed. Below is an example running of the Unix pwd command.
# pwd
/opt/sc3/daemons
#
Important notes and considerations are highlighted with this symbol and grey text
boxes.
Tips, examples and best practices are highlighted with this symbol and white on
blue text.
Nessus UI Overview
Description
Nessus is a product developed and maintained by Tenable Network Security to provide an
optimized Graphical User Interface (GUI) to the Nessus scanner. The client may be used
from any system on the network to interface with deployed Nessus scanners. As of Nessus
4.2, The UI is a newly created web-based interface made up of a simple HTTP server and
web client, requiring no software installation apart from the Nessus Server. As of Nessus 4,
all platforms draw from the same code base eliminating most platform specific bugs and
allowing for faster deployment of new features. The primary features are:
Generates .nessus files that Tenable products will use as the standard for
vulnerability data and scan policy.
A policy session, list of targets and the results of several scans can all be stored in a
single .nessus file that can be easily exported. Please refer to the Nessus File
Format guide for more details.
The GUI displays scan results in real-time so you do not have to wait for a scan to
complete to view results.
Provides unified interface to the Nessus scanner regardless of base platform. The
same functionalities exist on Mac OS X, Windows and Linux.
Copyright 2004-2010, Tenable Network Security, Inc.
4
Scans will continue to run on the server even if you are disconnected for any reason.
Nessus scan reports can be uploaded via the Nessus UI and compared to other
reports.
Supported Platforms
Since the Nessus UI is a web-based client, it can run on any platform with a web browser.
The Nessus web-based user interface is best experienced using Microsoft Internet
Explorer 7 and 8, Mozilla Firefox 3.5.x or Apple Safari.
Installation
Starting with Nessus 4.2, user management of the Nessus server is conducted through a
web interface and it is no longer necessary to use a standalone NessusClient. The
standalone NessusClients will still connect and operate the scanner, but they will not be
updated.
Refer to the Nessus 4.2 Installation Guide for instructions on installing Nessus. No additional
software installation is required.
Operation
Overview
Nessus provides a simple, yet powerful interface for managing vulnerability-scanning
activity.
Connect to Nessus GUI
To launch the Nessus GUI, perform the following:
Open a web browser of your choice.
Enter https://[server IP]:8834/ in the navigation bar.
Be sure to connect to the user interface via HTTPS, as unencrypted HTTP
connections are not supported.
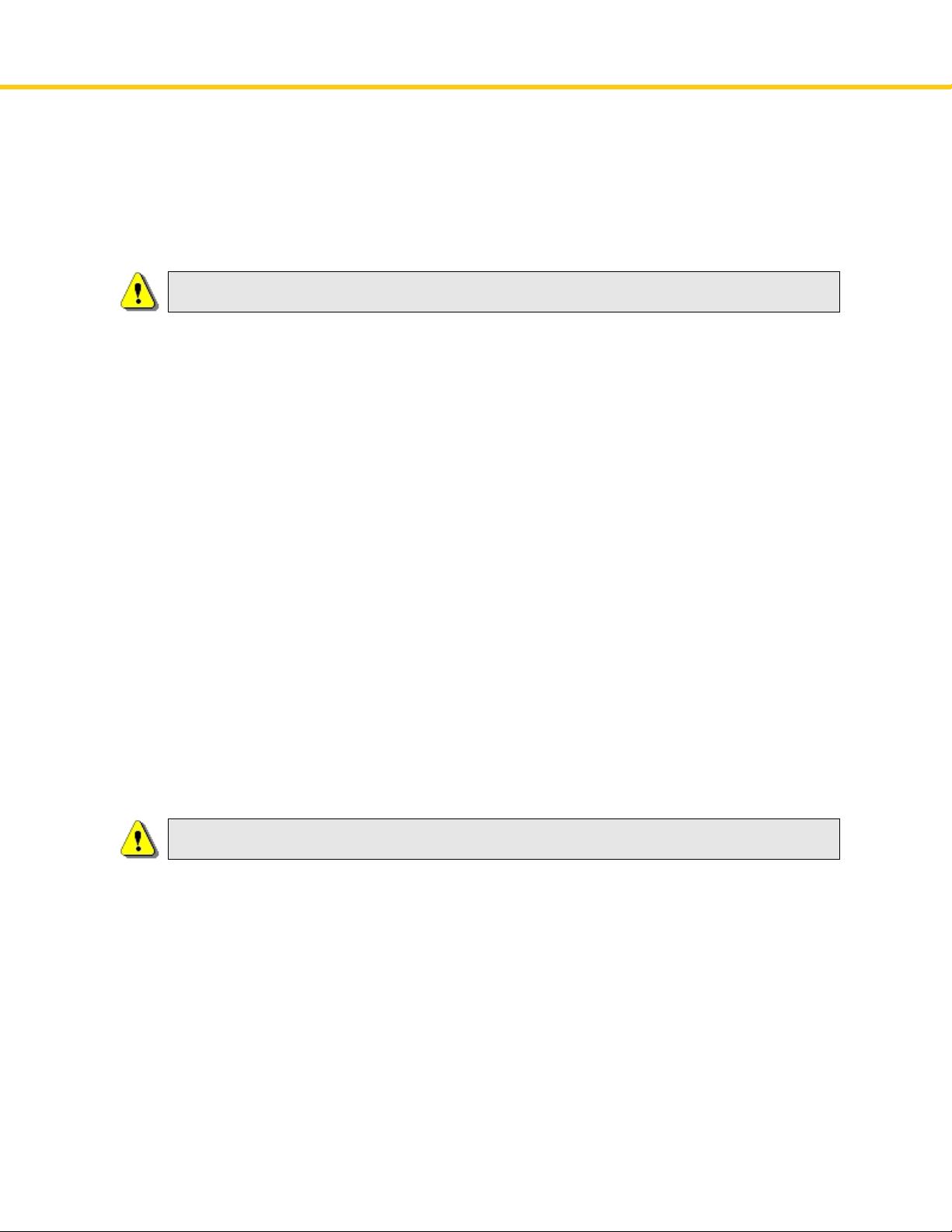
The first time you attempt to connect to the Nessus user interface, most web browsers will
display an error indicating the site is not trusted due to the self-signed SSL certificate:
Copyright 2004-2010, Tenable Network Security, Inc.
5
Users of Microsoft Internet Explorer can click on “Continue to this website (not
recommended)” to load the Nessus user interface. Firefox 3.x users can click on “I
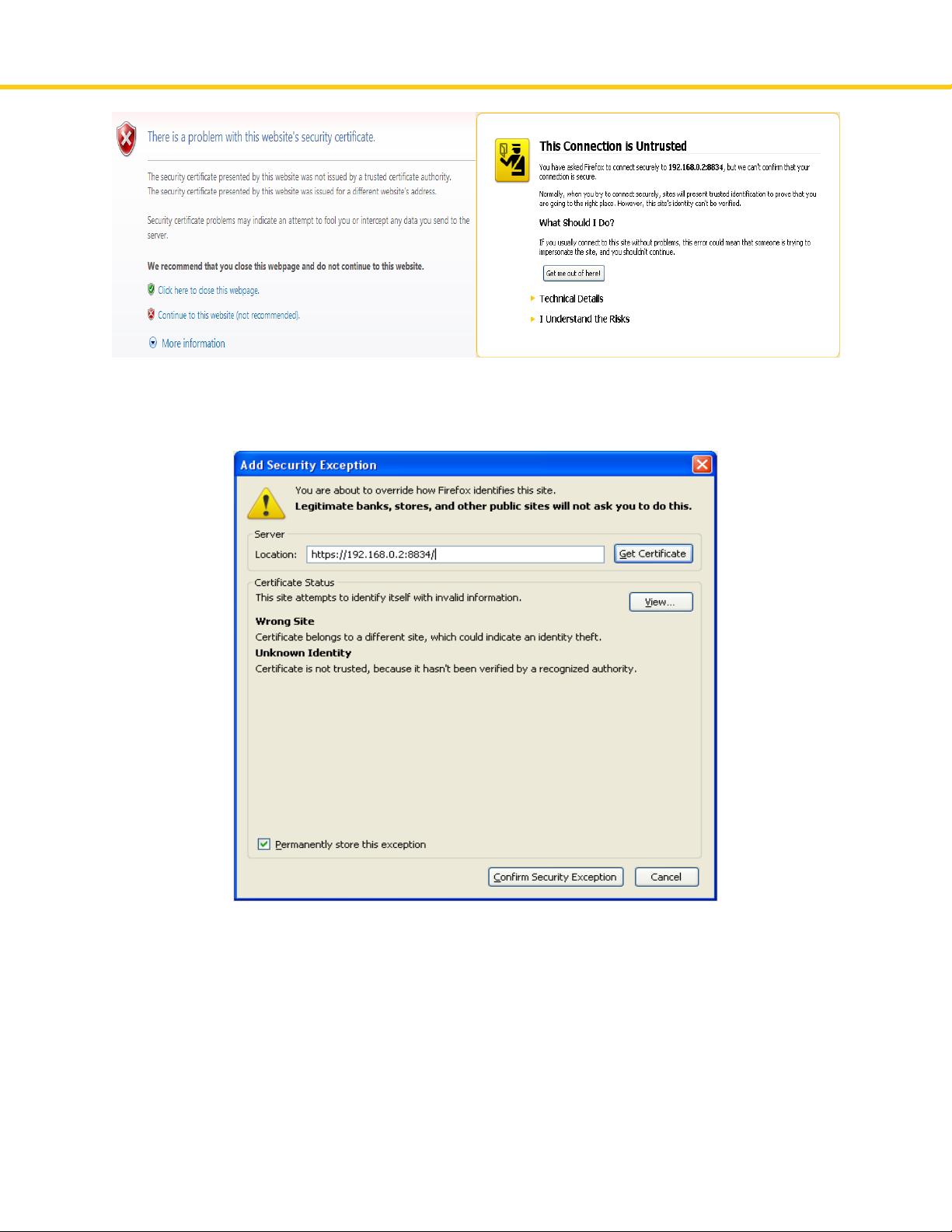
Understand the Risks” and then “Add Exception…” to bring up the site exception dialog box:
Verify the “Location:” bar reflects the URL to the Nessus server and click on “Confirm
Security Exception”. For information on installing a custom SSL certificate, consult the
Nessus Installation Guide.
After your browser has confirmed the exception, a splash screen will be displayed as
follows: