
Using certificate transparency streams to
hunt down phishing sites
Sean Gallagher
@thepacketrat
IT/NatSec Editor, Ars Technica

Certificate data ,
and why it's great
for OSINT
▪ More phishing sites are using SSL certs, other
tools to evade filters
▪ LetsEncrypt is free, programmatic, as is cPanel
– which auto-cert registers new domains
▪ While DNS holds domain names of sites, don't
identify malicious domains in DNS until they
go active.
▪ Phishing domains may have already switched
by the time activity is detected.
▪ Certificate data can be scanned actively to
discover phishing sites before they go live,
and used to proactively collect forensic data
on kits, etc. while the sites are still being set
up.

Certificate
Transparency
Logs
▪ Were created to help track the validity of
SSL certificates issued by the major
certificate authorities
▪ Data helps detect mistakenly issued
certificates, stolen or otherwise
maliciously acquired certs, among other
things.
▪ Each CA logs each new certificate, flags
revocations, etc.

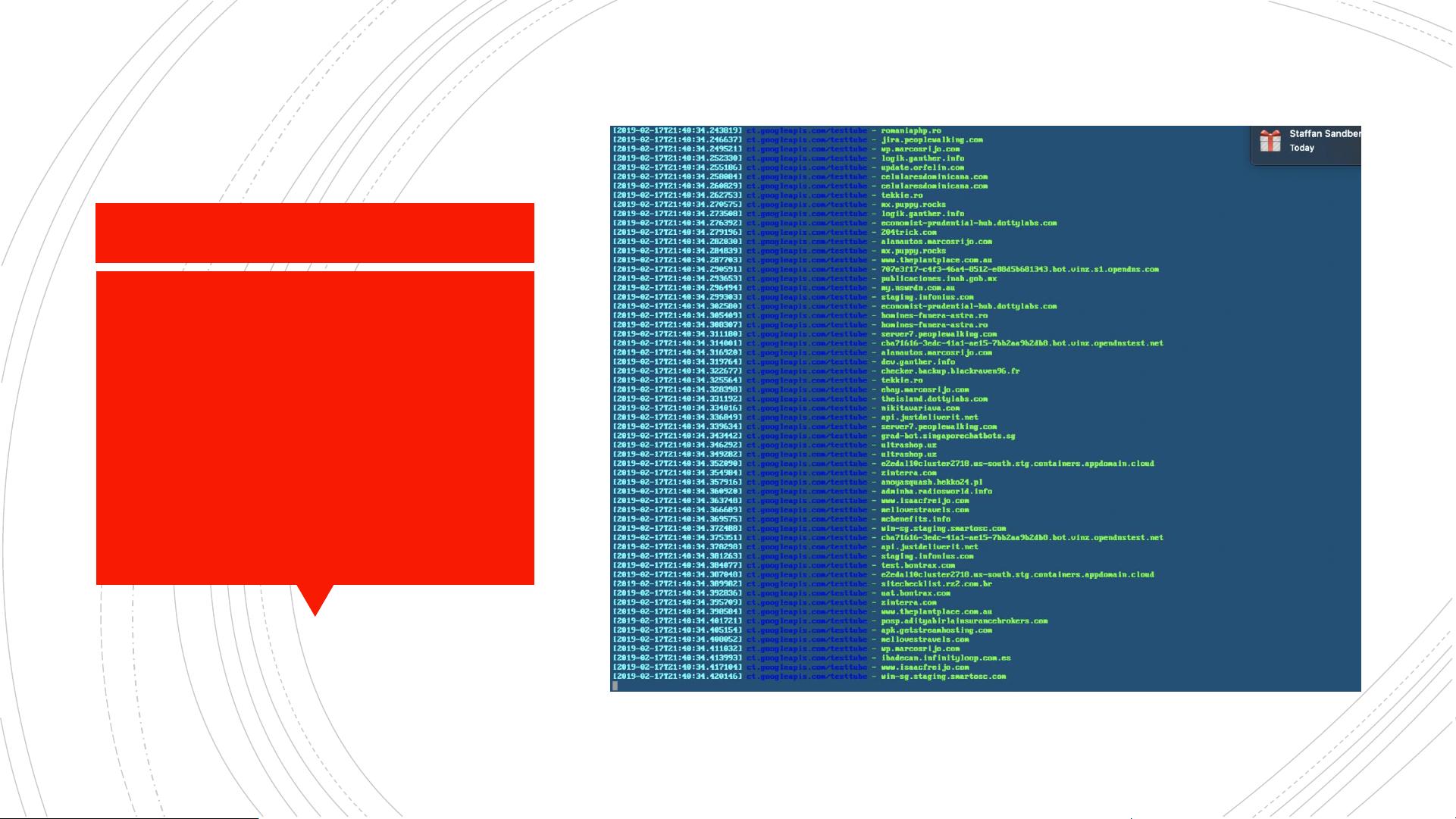
The
”Certstream"
▪ Service created by Ryan Sears of Cali Dog
Security that generates a near-realtime data feed
from all of the major certificate authorities'
transparency logs.
▪ Data is published over a web socket, can be
directly accessed via a command line interface
published in pip ( pip install certstream)
▪ Gives you a timestamp for an event, the source
url for the log it came from, and the domain
associated with the certificate.
▪ This by itself, with a little grepping with regular
expressions, or minor coding, could be used to
hunt for threats spoofing specific domain name
patterns.
The
Certstream















