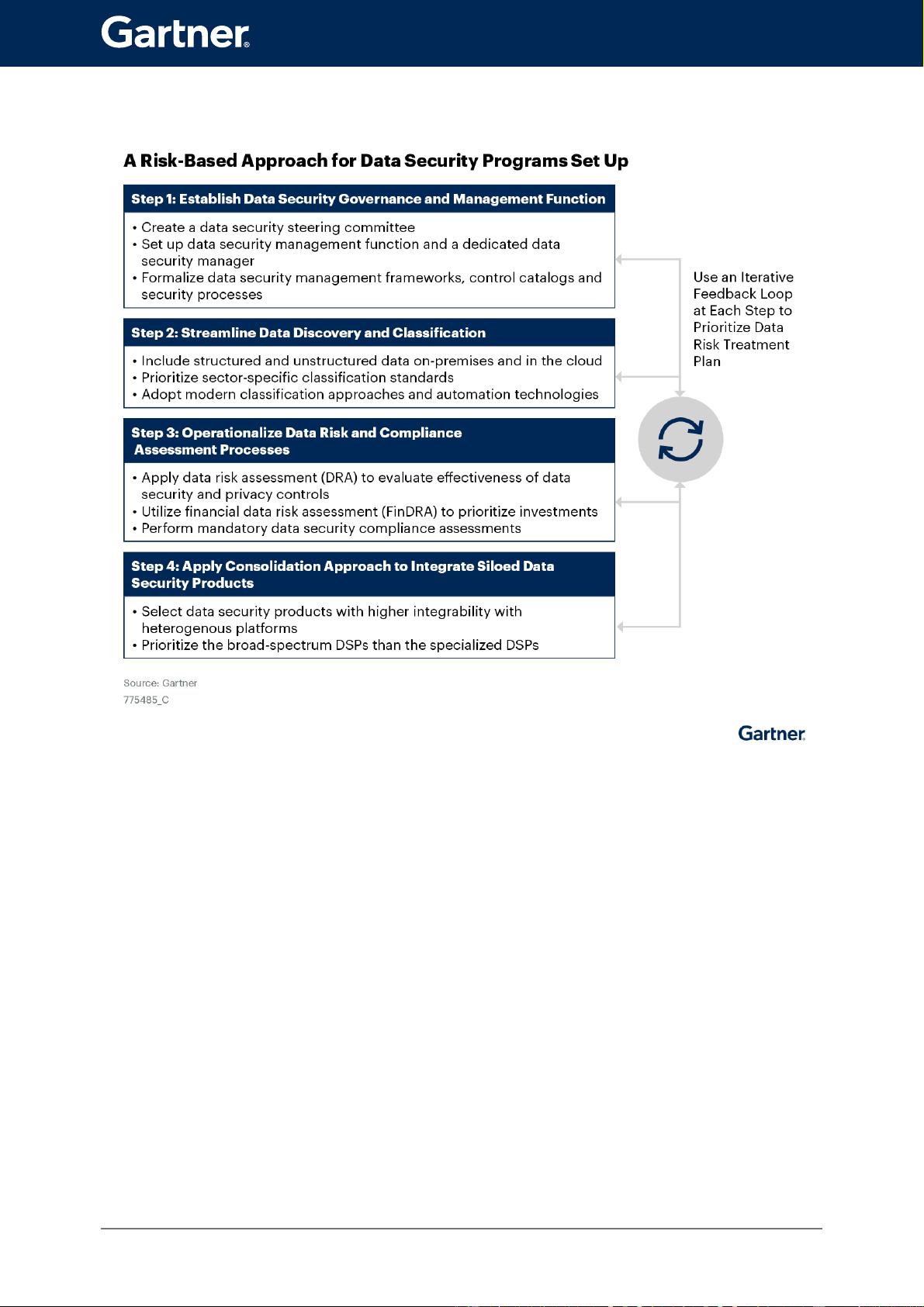
在中国开展业务或与中国相关的组织面临着越来越多的数据安全风险和法规。安全和风险管理领导者必须采用风险优先的数据安全计划和投资,以响应监管要求,以增强数据驱动的数字创新能力。 跨组织职能的分散的数据安全举措和不协调的利益相关者责任阻碍了组织实现企业规模的一致数据安全治理(DSG)。 数据发现和分类是 DSG 的基础,并且在大多数组织中都是通过手动流程实施的。然而,这既不具有可扩展性,也不有效。 随着组织数据处理活动的动态发展,时间点数据风险评估(DRA)通常不足以满足风险识别和处理方面多样化且不断变化的合规要求。 本地和云中应用程序和数据存储之间的数据移动不断增加,导致安全和风险管理 ( SRM )领导者难以实现统一的数据可见性和安全控制。 ### Gartner发布的中国数据安全与风险管理领导者指南:关键知识点概览 #### 一、背景与挑战 当前,对于在中国境内开展业务或者与中国市场有紧密联系的企业来说,面临着日益严峻的数据安全风险与法律法规的要求。这些组织的安全与风险管理领导者需采取风险优先的数据安全规划与投资策略,以确保符合当地法律要求的同时,提升数据驱动下的数字创新能力和业务安全性。 #### 二、现状分析与问题所在 1. **数据安全治理分散化**: - 在很多企业内部,数据安全的管理和实施呈现出明显的分散状态。 - 不同部门之间的职责划分模糊不清,缺乏有效的协调机制。 - 这种状况使得企业难以实现全面且一致的数据安全管理。 2. **数据发现与分类的手动操作**: - 大多数企业在进行数据发现和分类时依赖于人工操作。 - 手动方式不仅效率低下,而且无法应对大规模数据处理的需求。 - 缺乏自动化工具的支持,增加了数据管理的难度。 3. **时间点数据风险评估不足**: - 对于数据风险的评估往往基于某个时间点的情况。 - 这种静态评估方式难以适应数据处理活动的动态变化。 - 随着数据处理活动的不断发展,这种评估方式已经无法满足多样化且不断变化的合规要求。 4. **跨环境数据流动增加带来的挑战**: - 无论是本地还是云端的应用程序和数据存储之间,数据的流动越来越频繁。 - 这种趋势加大了安全管理的难度,尤其是对于实现统一的数据可见性和控制方面。 - 安全与风险管理领导者面临如何有效监控和保护这些数据的巨大挑战。 #### 三、建议与对策 1. **构建统一的数据安全治理体系**: - 强调跨部门间的协作与沟通,明确各方的责任和权限。 - 推动建立一个统一的数据安全治理框架,以提高整体数据安全管理的有效性。 2. **引入自动化工具进行数据发现与分类**: - 利用先进的技术手段,如人工智能和机器学习等,实现数据发现和分类的自动化。 - 减少人工干预,提高效率,确保数据管理工作的准确性。 3. **实施持续性的数据风险评估**: - 采用实时监测技术和持续性的风险评估方法,及时发现并应对潜在的风险。 - 通过动态调整风险管理策略,以适应数据处理活动的变化。 4. **加强跨环境数据流动的安全控制**: - 针对本地和云端环境中的数据流动,制定严格的访问控制策略。 - 实施加密、身份验证等多种安全措施,保障数据在传输过程中的安全。 #### 四、战略规划假设 - 到2025年,预计超过50%的大型跨国公司在中国市场或与中国市场有关联的业务中,将设立专门的数据安全职位,配备具备本地法律专业知识和语言能力的人才,以更好地应对中国市场相关的数据保护需求。 - 同样到2025年,预计将有30%的企业对其重要的业务数据采取更高级别的保护措施。 面对当前复杂多变的数据安全环境,中国境内的企业和组织亟需采取更加系统化、自动化的数据安全管理策略,以应对不断升级的安全威胁和监管要求。通过上述建议的实施,可以帮助企业构建更为稳健的数据安全体系,促进其长期可持续发展。




剩余24页未读,继续阅读

- 粉丝: 4921
- 资源: 167
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜最新资源


 信息提交成功
信息提交成功