没有合适的资源?快使用搜索试试~ 我知道了~
温馨提示

试读
29页
向云计算和远程工作的转变增加了 SASE 需求,以实现从任何设备的安全访问。安全和风险管理领导者必须将网络和安全融合到一两个明确合作的 SASE 供应商产品中,并淘汰遗留的边界系统。 安全访问服务边缘 (SASE) 框架为混合劳动力以及设备、分支机构以及企业应用程序和服务的分散部署提供了统一的连接和安全方法。 传统的网络和安全解决方案不足以满足现代应用程序和网络的需求,给网络和安全管理员带来了复杂性,并为用户带来了糟糕且不一致的体验。 组织可以通过创建与现有 IT 技能、供应商合同和硬件更新周期相一致的战略路线图来加速 SASE 的采用。 组织的目标是通过以下三种方式之一融合和采用 SASE:单供应商 SASE、双供应商 SASE 或托管 SASE。
资源推荐
资源详情
资源评论

Gartner, Inc. | G00792299 Page 1 of 21
2024 Strategic Roadmap for SASE Convergence
Published 15 December 2023 - ID G00792299 - 31 min read
By Analyst(s): John Watts, Andrew Lerner, Neil MacDonald
Initiatives: Infrastructure Security; Build and Optimize Cybersecurity Programs; I&O
Platforms
The shift to cloud computing and remote work increases SASE
demand to enable secure access from any device. Security and
risk management leaders must converge networking and security
into one or two explicitly partnered SASE vendor offerings and
retire legacy perimeter systems.
Overview
Key Findings
Recommendations
Security and risk management (SRM) leaders responsible for infrastructure security
should include the following activities in their SASE roadmap:
Secure access service edge (SASE) frameworks enable a unified approach to
connectivity and security for a hybrid workforce and decentralized deployment of
devices, branches, and enterprise applications and services.
■
Legacy networking and security solutions are inadequate for modern applications
and networks, creating complexity for network and security administrators, and poor
and inconsistent experiences for users.
■
Organizations can accelerate SASE adoption by creating a strategic roadmap
aligned with existing IT skills, vendor contracts and hardware refresh cycles.
■
Organizations have a goal to converge and adopt SASE in one of three ways: single-
vendor SASE, dual-vendor SASE or managed SASE.
■
Engage with stakeholders with goals to modernize branch office connectivity, pursue
a zero trust strategy, or secure and connect hybrid workers.
■
This research note is restricted to the personal use of chenlizhen@qianxin.com.
Gartner, Inc. | G00792299 Page 2 of 21
Introduction
Traditionally, most network and security architectures were designed with the enterprise
data center as the focal point for access and security needs, supporting users that were
relatively static. However, digital business has driven requirements for new digital
capabilities — such as cloud and edge computing, and work-from-anywhere initiatives —
which have, in turn, inverted access requirements from forcing end users to connect to a
managed network for security to securing their access regardless of their location.
Gartner’s 2023 Cloud End-User Behavior research shows that more than 50% of all
applications now reside outside of an on-premises network and data center.
1
Network security designs based on a collection of perimeter security appliances are ill-
suited to address the dynamic anywhere, anytime needs of a modern digital business and
its hybrid digital workforce.
The legacy perimeter must transform into a set of user- and application-centric converged
capabilities, managed from the cloud and enforced when and where an enterprise needs
them — that is, a converged set of dynamically created, policy-based network and security
controls converged into a SASE framework.
At the same time, enterprises are increasingly pursuing zero trust strategies, but finding
meaningful implementations of zero trust principles challenging. Delivering a zero trust
security posture is an integral part of a SASE architecture and integral to emerging SASE
offerings. Zero trust networking models replace implicit trust with continuously assessed
risk/trust levels (see Quick Answer: Explaining Zero Trust Security Approaches to Tech
Executives). Zero trust architectures adapt the amount of explicit trust granted for
interactions as the context surrounding the interactions changes while still applying
security inspection to all traffic and data.
Select converged SASE offerings with single pass inspection of traffic, flexible
inspection points and routing, and customized logging to meet performance,
simplicity and compliance requirements.
■
Consolidate existing networking and security contracts, and engage networking and
security engineers before any technology evaluations to minimize duplicate spend.
■
Create a shortlist and evaluation criteria aligned with the preferred deployment
option, and conduct a pilot before any purchase to validate key functional
requirements and use cases.
■
This research note is restricted to the personal use of chenlizhen@qianxin.com.
Gartner, Inc. | G00792299 Page 3 of 21
The need to agilely support digital business transformation efforts with a zero trust
security posture while keeping complexity manageable is a significant driver for the SASE
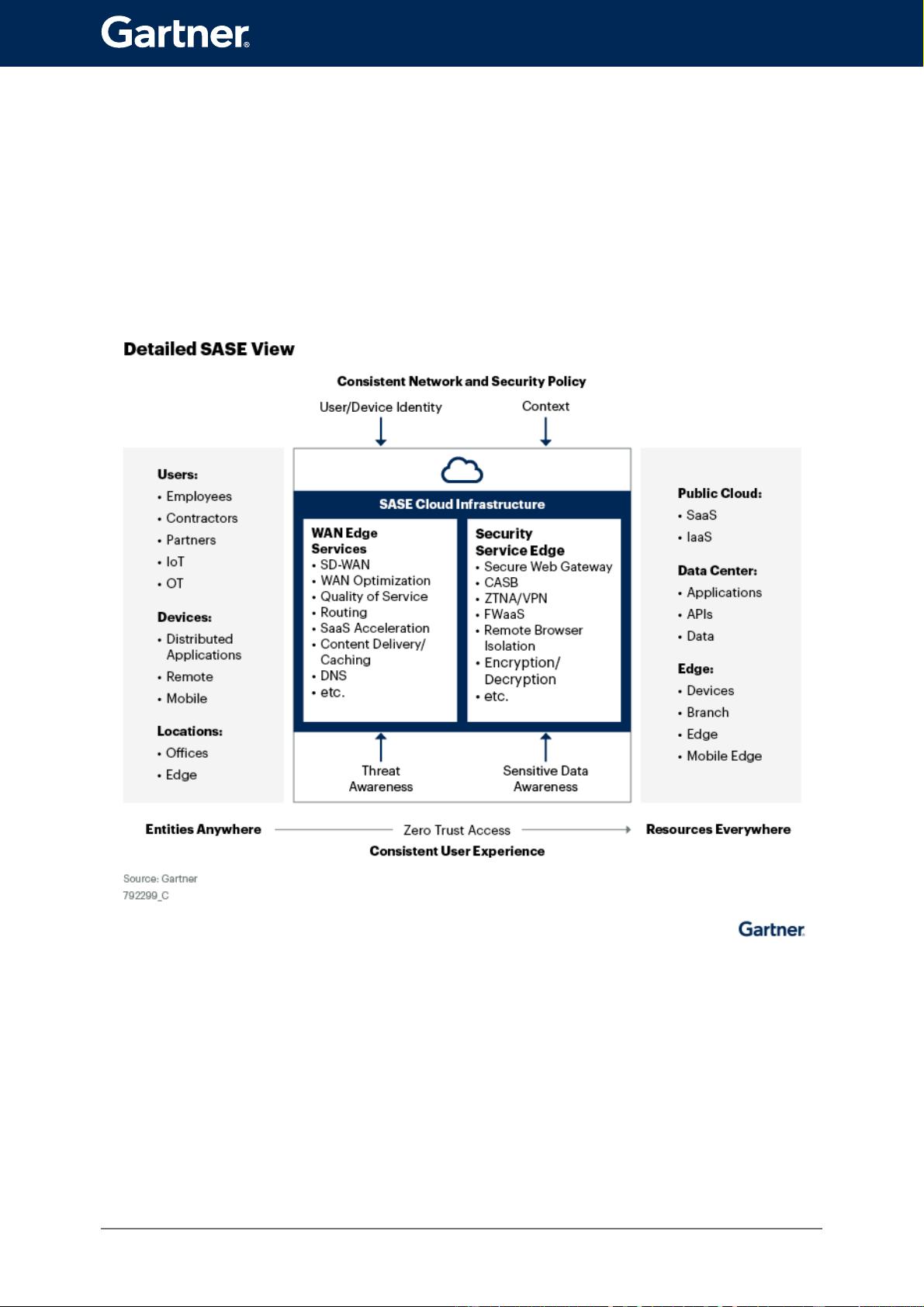
market, primarily delivered as a cloud-based service. The SASE architecture (see Figure 1)
converges network, most notably, SD-WAN, and network security service edge services,
most notably secure web gateway (SWG), cloud access security broker (CASB) and zero
trust network access (ZTNA).
Figure 1: Detailed SASE View
This research note is restricted to the personal use of chenlizhen@qianxin.com.

Gartner, Inc. | G00792299 Page 4 of 21
Since defining the SASE market in 2019, industry and client interest in SASE has exploded,
primarily driven by existing enterprise needs not being met by existing vendors. SASE
continued sustained interest from Gartner clients, with a 10% increase in inquiries during
the second half of 2022 into the first half of 2023 over the prior 12 months. In response to
customer demand, vendors have been rapidly coming to market with new solutions.
Gartner’s Forecast Analysis: Secure Access Service Edge, Worldwide predicts the total
addressable market (TAM) of this market to be $25 billion in 2027 with a five-year (2021
through 2026) compound annual growth rate (CAGR) of 29%. In the last 18 months, there
have been several significant vendor acquisitions and announcements to build out a
complete SASE portfolio, including multiple managed SASE offerings (see Note 1), and we
predict more of these activities are to come.
In the 2024 Gartner CIO and Technology Executive Survey, 39% of respondents said they
had deployed or will deploy SASE within 24 months.
2
However, enterprise transition to a
complete SASE framework will take time. The reality is that enterprises have existing
investments in hardware and software with time and value remaining. Hardware refresh
cycles at branch offices average four to seven years. Relationships and staff expertise
with incumbent vendor offerings is another factor. Moreover, most larger enterprises have
separate network security and network operations teams, further complicating SASE
adoption.
Finally, many vendors claim to offer a SASE product but don’t deliver all of the required
and recommended SASE capabilities (see Note 2). Gartner tracks four separate markets
where buyers begin their SASE transformation journey and purchasing decisions (see
Where Do I Start With SASE Evaluations: SD-WAN, SSE, Single-Vendor SASE, or Managed
SASE?). Not all of a vendor’s SASE capabilities are at the same level of functionality and
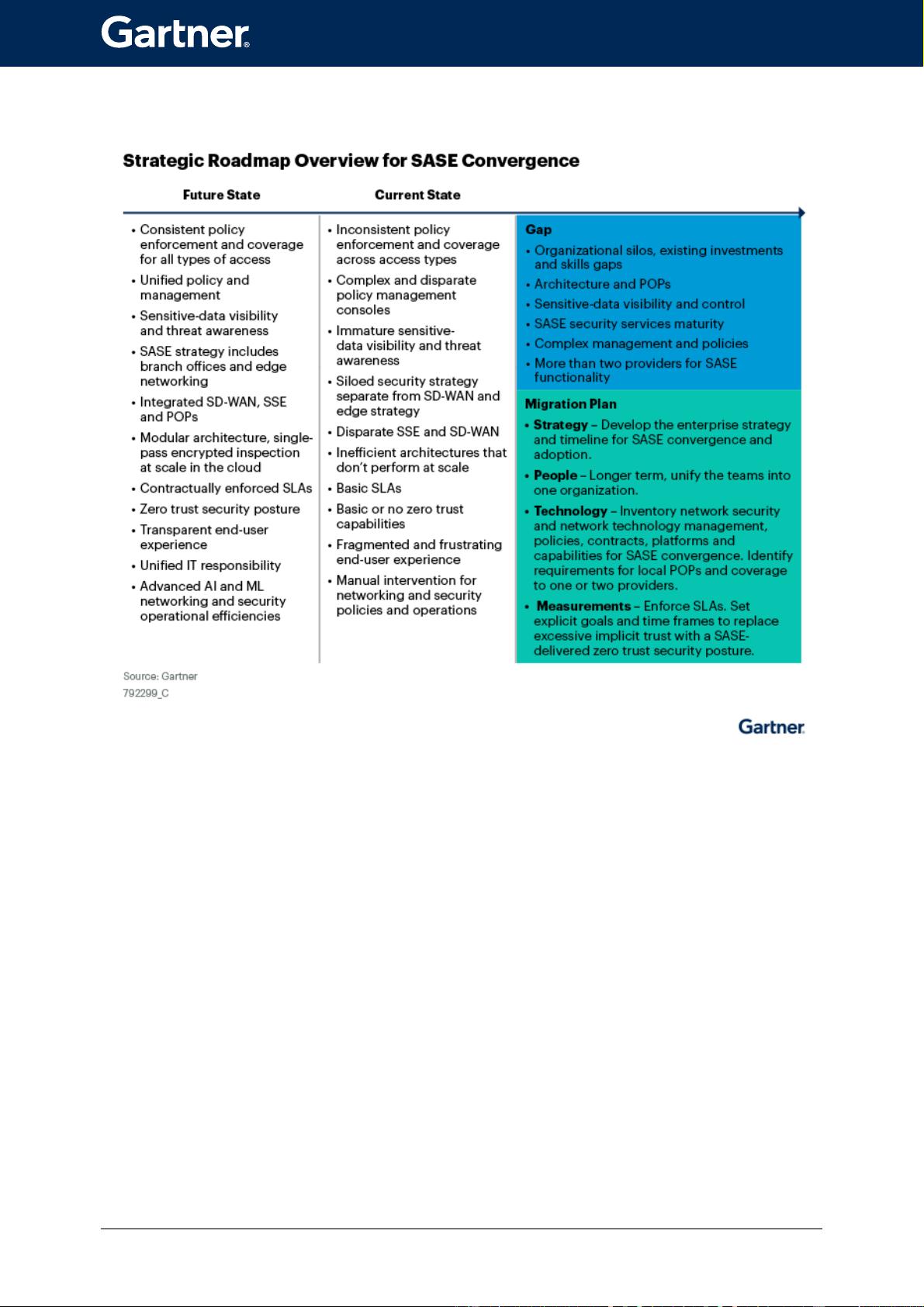
maturity. We analyzed the gaps between the future and current state of SASE offerings in
the market to enable SRM leaders with a strategic roadmap, a migration plan and
implementation advice for SASE adoption over the next several years (see Figure 2).
This research note is restricted to the personal use of chenlizhen@qianxin.com.
Gartner, Inc. | G00792299 Page 5 of 21
Figure 2: Strategic Roadmap Overview for SASE Convergence
Gartner
Future State
Your users and edge devices can be located anywhere, and most of your users’ network
access is via the internet to applications and services, which are no longer stand-alone nor
on-premises. Even on your internal network, a zero trust security posture treats the network
as untrusted. Users, branch offices and edge devices need secure access to your data and
applications that are spread everywhere throughout the cloud and data centers. SASE
offerings deliver and protect this future state (i.e., 2025 and beyond; see Table 1).
This research note is restricted to the personal use of chenlizhen@qianxin.com.
剩余28页未读,继续阅读
资源评论

lurenjia404
- 粉丝: 1400
- 资源: 111
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
