没有合适的资源?快使用搜索试试~ 我知道了~
Gartner发布2024年网络安全预测 :IAM 和数据安全相结合,解决长期存在的挑战
需积分: 5 3 下载量 73 浏览量
2023-12-15
10:08:31
上传
评论
收藏 267KB PDF 举报
温馨提示

试读
15页
安全和风险管理领导者需要采用可组合的数据安全视图。这项研究预测,将数据安全创新应用于痛点和高级用例将有助于组织将其数据用于几乎任何用例。 在所有云服务模型中,数据安全以及身份和访问管理 (IAM) 的责任均由最终客户承担。 由于这两个学科作为客户管理的最重要的安全控制而脱颖而出,因此它们越来越重叠和交织。 利用数据安全和 IAM 之间日益增加的重叠仍然具有挑战性,因为这两个以前孤立的学科都有自己的标志性技能和术语。
资源推荐
资源详情
资源评论

Gartner, Inc. | G00787796
Page 1 of 15
Predicts 2024: IAM and Data Security Combine to
Solve Long-Standing Challenges
Published 29 November 2023 - ID G00787796 - 16 min read
By Analyst(s): Joerg Fritsch, Andrew Bales, Nathan Harris, Homan Farahmand
Initiatives: Security of Applications and Data; Meet Daily Cybersecurity Needs
Security and risk management leaders need to adopt a
composable view of data security. This research predicts that
applying data security innovations to pain points and advanced
use cases will help SRM leaders’ organizations to leverage their
data for almost any use case.
Additional Perspectives
Overview
Key Findings
Invest Implications: Predicts 2024: IAM and Data Security Combine to Solve Long-
Standing Challenges
(06 December 2023)
■
The responsibility for data security and identity and access management (IAM)
stays with the end customer in all cloud service models.
■
As these two disciplines stand out as the most significant security controls managed
by customers, they are increasingly overlapping and intertwining.
■
Leveraging the increasing overlap between data security and IAM stays challenging
because both formerly siloed disciplines have their own signature skills and
terminology.
■
This research note is restricted to the personal use of [email protected].

Gartner, Inc. | G00787796
Page 2 of 15
Recommendations
Strategic Planning Assumption(s)
Through 2026, organizations adopting top data practices within their IAM program will
realize 40% improvement in time-to-value delivery for IAM and data security program
objectives.
By 2027, organizations faced with AI and data security requirements will standardize on
policy-based access controls to unlock the value from more than 70% of their data.
By 2027, 70% of organizations will combine data loss prevention and insider risk
management (IRM) disciplines with IAM context to identify suspicious behavior more
effectively.
Optimize your IAM technology portfolio by including critical data management
capabilities and practices in the core requirements for IAM solutions.
■
Implement data access controls that address important policy management and
enforcement requirements, and integrate with popular data catalogs, by
consolidating siloed data centric controls into your data security platform (DSP).
■
Ensure flexible, scalable and risk-based access by identifying what contextual data
is available from which sources, and by defining dynamic, context-aware policies.
■
Identify data risk and identity risk, and use them in tandem as the primary directive
for strategic data security within the organization.
■
This research note is restricted to the personal use of [email protected].
Gartner, Inc. | G00787796
Page 3 of 15
Analysis
What You Need to Know
Data security and IAM existed as distinct disciplines within the realm of cybersecurity.
However, as an increasing number of organizations leverage cloud services, including the
most popular SaaS offerings, a notable shift has occurred. Many companies now entrust
significant security controls, such as those governing storage, applications and networks,
to their chosen cloud service providers (CSPs).
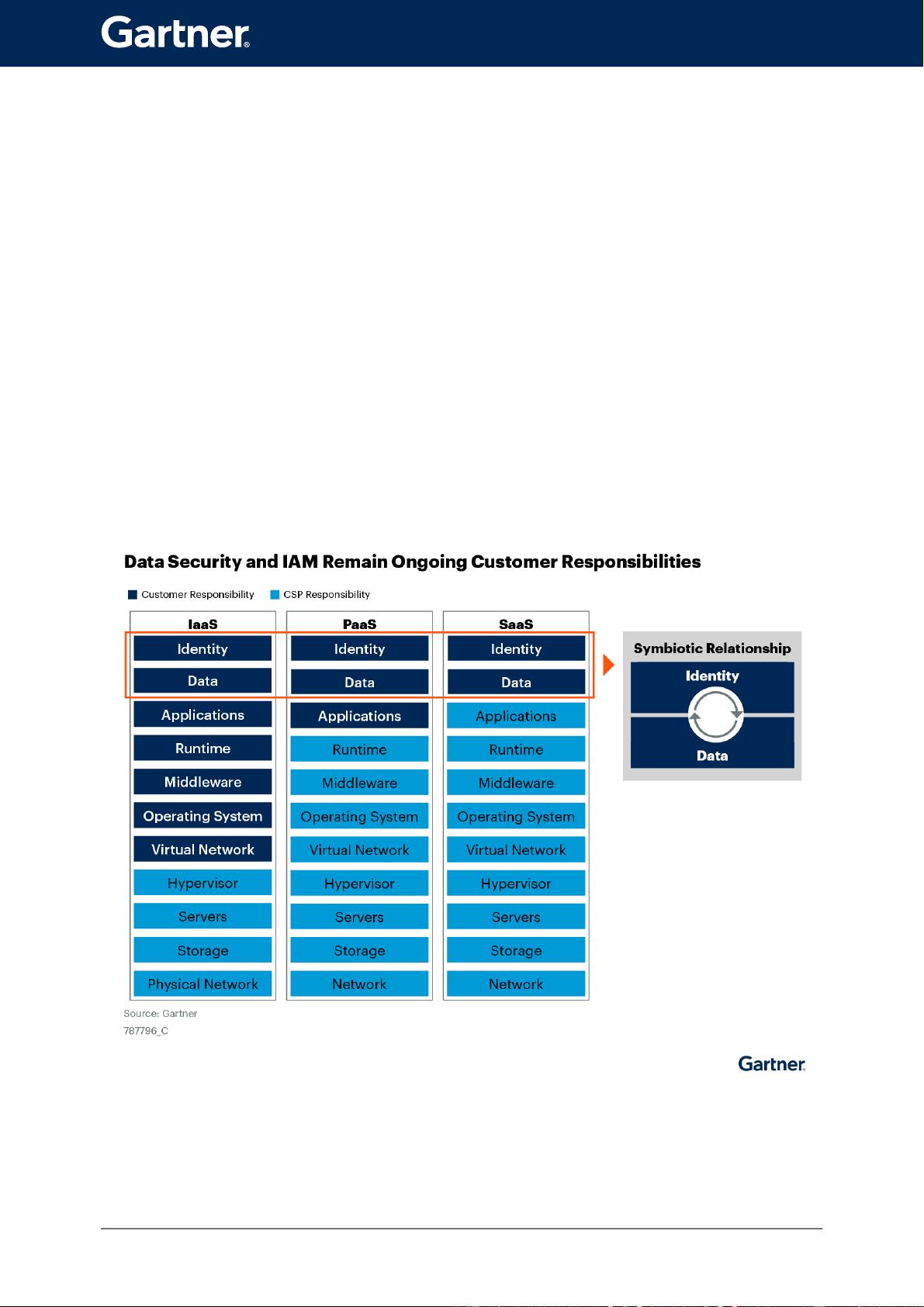
Figure 1 illustrates the security handoff points for infrastructure as a service (IaaS),
platform as a service (PaaS) and SaaS cloud models. The handoff point moves up the
stack across the models. IaaS offers the most control, with the commensurate security
responsibility left to customers. SaaS offers the least control, with the CSP taking on most
of the security responsibility.
Figure 1: Data Security and IAM Remain Ongoing Customer Responsibilities
This research note is restricted to the personal use of [email protected].
剩余14页未读,继续阅读
资源评论

lurenjia404
- 粉丝: 1886
- 资源: 119
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
