没有合适的资源?快使用搜索试试~ 我知道了~
本人参与OCP考试时所找到的资源,如果能够认真学习好本文档,考过042的课程不会有任何问题
资源推荐
资源详情
资源评论

1. Which three pieces of information are considered while deciding the size of the undo tablespace in your
database? (Choose three.)
A) the size of an undo block
B) the size of the redo log files
C) undo blocks generated per second
D) the size of the database buffer cache
E) the value of the UNDO_RETENTION parameter
2. You executed the STARTUP MOUNT command to start your database. For which database operation do you
need to start the database in the MOUNT state?
A) renaming the control files
B) dropping a user in your database
C) enabling or disabling redo log archiving
D) dropping a tablespace in your database
E) re-creating the control files, after you lost all the control files in your database
3. You want to create a new optimized database for your transactional production environment to be used by a
financial application. While creating the database, you want the Oracle software to take care of all basic
settings to optimize the database performance. Which method would you use to achieve this objective?
A) Use the CREATE DATABASE.. command to create the database with Oracle-managed files.
B) Use the Database Configuration Assistant (DBCA) to create the database with Oracle-managed files.
C) Use Enterprise Manager to create a new database with the Online Transaction Processing (OLTP) option.
D) Use Database Configuration Assistant (DBCA) to create the database with Transaction Processing template.
E) Use the CREATE DATABASE.. command to create the database with Automatic Storage
Management (ASM) file system.
4. Which three statements are true about the stages of database startup? (Choose three.)
A) Data files and redo log files can be renamed at the MOUNT stage.
B) Control files are read at the OPEN stage for the location of data files.
C) Control files are required to bring the database to the NOMOUNT stage.
D) Data files and redo log files are made available to users at the OPEN stage.
E) Data files and online redo log files are checked for consistency while opening the database.
5. A constraint in a table is defined with the INITIALLY IMMEDIATE clause. You executed the ALTER TABLE
command with the ENABLE VALIDATE option to enable the constraint that was disabled. What are the two
effects of this command? (Choose two.)
A) It fails if any existing row violates the constraint.
B) It does not validate the existing data in the table.
C) It enables the constraint to be enforced at the end of each transaction.
D) It prevents insert, update, and delete operations on the table while the constraint is in the process of being enabled.
6. You received complaints about the degradation of SQL query performance. You identified top SQL queries
that consume time. What would be your next step to find out recommendations about statistics collection and
restructuring of the SQL statement to improve query performance?
A) run Segment Advisor
B) run SQL Tuning Advisor on top SQL statements
C) run the Automatic Workload Repository (AWR) report
D) run the Automatic Database Diagnostic Monitor (ADDM) on top SQL statements
7. The UNDO_RETENTION parameter in your database is set to 1000 and undo retention is not guaranteed.
Which statement regarding retention of undo data is correct?
A) Undo data becomes obsolete after 1,000 seconds.
B) Undo data gets refreshed after every 1,000 seconds.
C) Undo data will be stored permanently after 1,000 seconds.
D) Committed undo data would be retained for 1,000 seconds if free undo space is available.
E) Undo data will be retained in the UNDO tablespace for 1,000 seconds, then it gets moved to the TEMPORARY
tablespace to provide read consistency.
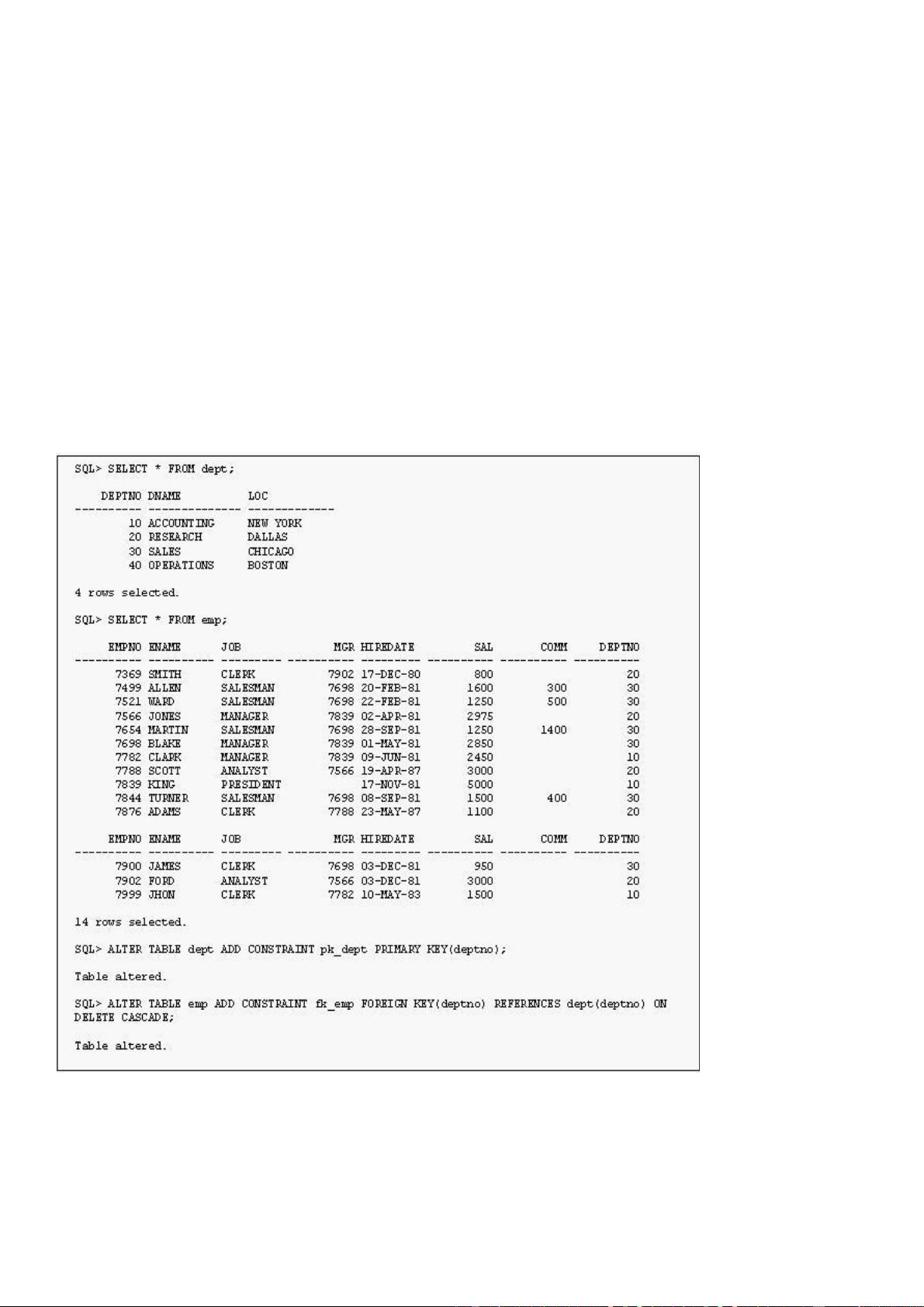
8. View the Exhibit.
Which statement regarding the dept and emp tables is true?
A) When you delete a row from the emp table, you would receive a constraint violation error.
B) When you delete a row from the dept table, you would receive a constraint violation error.
C) When you delete a row from the emp table, automatically the corresponding rows are deleted from the dept table.
D) When you delete a row from the dept table, automatically the corresponding rows are deleted from the emp table.
E) When you delete a row from the dept table, automatically the corresponding rows are updated with null values in the
emp table.
F) When you delete a row from the emp table, automatically the corresponding rows are updated with null values in the
dept table.

9. Which three statements are correct about temporary tables? (Choose three.)
A) Indexes and views can be created on temporary tables.
B) Both the data and the structure of temporary tables can be exported.
C) Temporary tables are always created in a user's temporary tablespace.
D) The data inserted into a temporary table in a session is available to other sessions.
E) Data manipulation language (DML) locks are never acquired on the data of temporary tables.
10. Which statement regarding the contents of the V$PARAMETER view is true?
A) displays only the list of default values
B) displays only the list of all basic parameters
C) displays the currently in effect parameter values
D) displays only the list of all advanced parameters
E) displays the list of all the parameter files of a database
F) displays the current contents of the server parameter file
11. According to your backup strategy, you performed an incremental level 0 backup of your database. Which
statement regarding this backup is true?
A) The backup is similar to image copy.
B) The backup contains all used data blocks.
C) The backup contains only unused data blocks.
D) The backup contains all data blocks changed since the last incremental level 1 backup.
12. Which step do you need to perform to enable a user with the SYSDBA privilege to log in as SYSDBA in
iSQL*Plus?
A) The user must be granted the database administrator (DBA) privilege.
B) The user must be listed in the password file for the authentication.
C) No special setup is needed for the user to connect as SYSDBA in iSQL*Plus.
D) Set up a user in the Oracle Application Server Containers for J2EE (OC4J) user manager, and grant the webDba
role to the user.
13. Because of a power outage, instance failure has occurred. From what point in the redo log does recovery
begin and where does it end?
A) current redo log and inactive redo log
B) checkpoint position to end of redo log
C) beginning of redo log to end of redo log
D) all redo logs before the point of last commit
E) beginning of redo log to checkpoint position
14. Which two statements are true regarding the database in ARCHIVELOG mode? (Choose two.)
A) You have to shut down the database to perform the backups.
B) Archiving information is written to the data files and redo log files.
C) You can perform complete database backups without closing the database.
D) Online redo log files have to be multiplexed before putting the database in ARCHIVELOG mode.
E) All the previous database backups become invalid after you configure the database to ARCHIVELOG mode.
15. User Scott has updated the salary of one of the employees in the EMPLOYEES table and has not
committed the transaction. What are the two types of locks that this scenario would lead to? (Choose two.)
A) null lock on the row being updated
B) null lock on the table containing the row
C) ROW SHARE lock for the row being updated
D) ROW EXCLUSIVE lock for the row being updated
E) shared row-exclusive lock for the row being updated
F) a shareable table lock for the table containing the row
G) exclusive table-level lock for the table containing the row
16. You notice this warning in the alert log file:
ORA-19815: WARNING: db_recovery_file_dest_size of 3221225472 bytes is 100.00% used, and has 0
remaining bytes available.
What would you do to reclaim the used space in the Flash Recovery Area?
A) Back up the Flash Recovery Area.
B) Increase the retention time for the files.
C) Decrease the retention time for the files.
D) Manually delete all the archived log files from the Flash Recovery Area by using operating system (OS) commands.
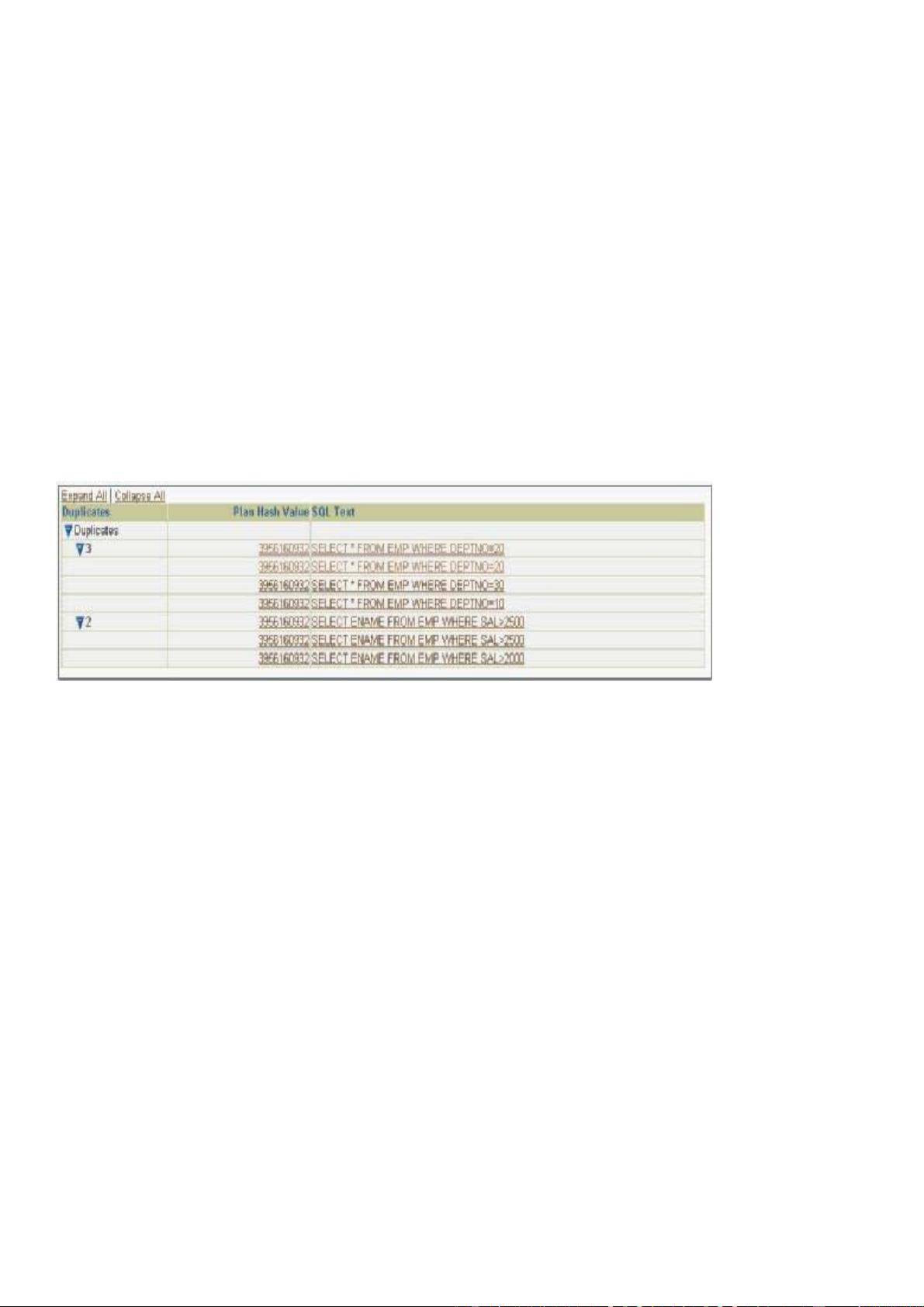
17. View the Exhibit and examine the output.
Which statement describes the conclusion?
A) The users should use bind variables instead of literals in the query.
B) The dictionary cache is consuming more space than the library cache.
C) The shared pool size should be increased to accommodate the SQL statements.
D) Preparing indexes on the tables used in the SQL statements would improve the library cache performance.
18. Which two operations require undo data? (Choose two.)
A) committing a transaction
B) rolling back a transaction
C) recovering from failed transactions
D) recording a transaction to redo log files
E) rolling forward during instance recovery
19. Your database is configured in NOARCHIVELOG mode. All the control files have been lost due to a hard
disk failure but the data files are not lost. You have the closed whole database backup available to you. Which
two statements are true in this scenario? (Choose two.)
A) The instance aborts.
B) The database cannot be recovered.
C) The database can be recovered by restoring the control files from the backup.
D) The database remains opened and you have to shut it down with the ABORT option.
E) The database can be restored till the point of the last closed whole database backup.
20. Which is the correct description of the significance of the ORACLE_HOME environmental variable?
A) It specifies the directory containing the Oracle software.
B) It specifies the directory containing the Oracle-Managed Files.
C) It specifies the directory for database files, if not specified explicitly.

D) It specifies the base directory of Optimal Flexible Architecture (OFA) .
21. While running the Oracle Universal Installer on a Unix platform to install Oracle
Database 10g software, you are prompted to run orainstRoot.sh script. What does this script accomplish?
A) It creates the pointer file.
B) It creates the base directory.
C) It creates the Inventory pointer file.
D) It creates the Oracle user for installation.
E) It modifies the Unix kernel parameters to match Oracle's requirement.
22. You find that the database performance degrades while you backup the PROD database using Recovery
Manager (RMAN). The PROD database is running in shared server mode. The database instance is currently
using 60% of total operating system memory. You suspect the shared pool fragmentation to be the reason.
Which action would you consider to overcome the performance degradation?
A) Configure Java Pool to cache the java objects.
B) Configure Streams Pool to enable parallel processing.
C) Increase Shared Pool size to cache more PL/SQL objects.
D) Increase Database Buffer Cache size to increase cache hits.
E) Configure Large Pool to be used by RMAN and shared server.
F) Increase the total System Global Area (SGA) size to increase memory hits.
23. Your database is started with SPFILE. You want the database instance to be dynamically registered with a
listener L2 with the following details:
Protocol: TCP
Host: indl151e
Port: 1525
Which is the correct order of the steps that you would follow to achieve this?
1. Set the LOCAL_LISTENER parameter to L2 dynamically.
2. Make an entry for L2 in tnsnames.ora on the database server.
3. Restart L2.
4. Modify the listener.ora file to add the instance name in SID_LIST of L2.
A) 1, 2, 4, 3
B) 1, 2, 3; 4 is not required.
C) 2, 1; 3 and 4 are not required.
D) 1, 2; 3 and 4 are not required.
24. The junior DBA in your organization has accidentally deleted the alert log file. What will you do to create
new alert log file?
A) Create the new text file file as ALERT.LOG.
B) You have to recover the alert log file from the valid backup.
C) Change the value for the BACKGROUND_DUMP_DEST parameter.
D) No action required.The file would be created automatically by the instance.
25. A user complains that he gets the following error message repeatedly after executing some SQL
statements. The error message forces the user to log off from and log on to the database to continue his work.
ORA-02392: exceeded session limit on CPU usage, you are being logged off
Which action would you take to increase the session limit on CPU usage?
A) Modify the profile assigned to the user.
B) Modify the roles assigned to the users.
C) Modify the object privileges assigned to the user.
D) Modify the system privileges assigned to the users.
剩余42页未读,继续阅读
资源评论

davixiong
- 粉丝: 0
- 资源: 4
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功

