没有合适的资源?快使用搜索试试~ 我知道了~
AWS Certified Developer Exam (DVA-C01) 题库
需积分: 0 0 下载量 195 浏览量
2024-02-26
13:25:57
上传
评论
收藏 134KB PDF 举报
温馨提示

试读
13页
AWS Certified Developer Exam (DVA-C01) 题库Examshoot公开版
资源推荐
资源详情
资源评论

Wish You PASS The Exam \(@^O^@)/
1/94Thank you for choosing ExamShoot.com product!
AWS DVA C02 Exam Questions
Question: 1
A developer is deploying a new application to Amazon Elastic Container Service (Amazon ECS). The developer
needs to securely store and retrieve different types of variables. These variables include authentication
information for a remote API, the URL for the API, and credentials. The authentication information and API URL
must be available to all current and future deployed versions of the application across development, testing, and
production environments.
How should the developer retrieve the variables with the FEWEST application changes?
Answer: A
A: Update the application to retrieve the variables from AWS Systems Manager Parameter Store. Use unique
paths in Parameter Store for each variable in each environment. Store the credentials in AWS Secrets
Manager in each environment.
B: Update the application to retrieve the variables from AWS Key Management Service (AWS KMS). Store the
API URL and credentials as unique keys for each environment.
C: Update the application to retrieve the variables from an encrypted file that is stored with the application.
Store the API URL and credentials in unique files for each environment.
D: Update the application to retrieve the variables from each of the deployed environments. Define the
authentication information and API URL in the ECS task definition as unique names during the deployment
process.
Question: 2
A company uses AWS Lambda functions and an Amazon S3 trigger to process images into an S3 bucket. A
development team set up multiple environments in a single AWS account.
After a recent production deployment, the development team observed that the development S3 buckets invoked
the production environment Lambda functions. These invocations caused unwanted execution of development S3
files by using production Lambda functions. The development team must prevent these invocations. The team
must follow security best practices.
Which solution will meet these requirements?
Answer: B
A: Update the Lambda execution role for the production Lambda function to add a policy that allows the
execution role to read from only the production environment S3 bucket.
B: Move the development and production environments into separate AWS accounts. Add a resource policy to
each Lambda function to allow only S3 buckets that are within the same account to invoke the function.
C: Add a resource policy to the production Lambda function to allow only the production environment S3
bucket to invoke the function.
D: Move the development and production environments into separate AWS accounts. Update the Lambda
execution role for each function to add a policy that allows the execution role to read from the S3 bucket that
is within the same account.
Question: 3
A developer is creating an application. New users of the application must be able to create an account and
register by using their own social media accounts.
Wish You PASS The Exam \(@^O^@)/
2/94Thank you for choosing ExamShoot.com product!
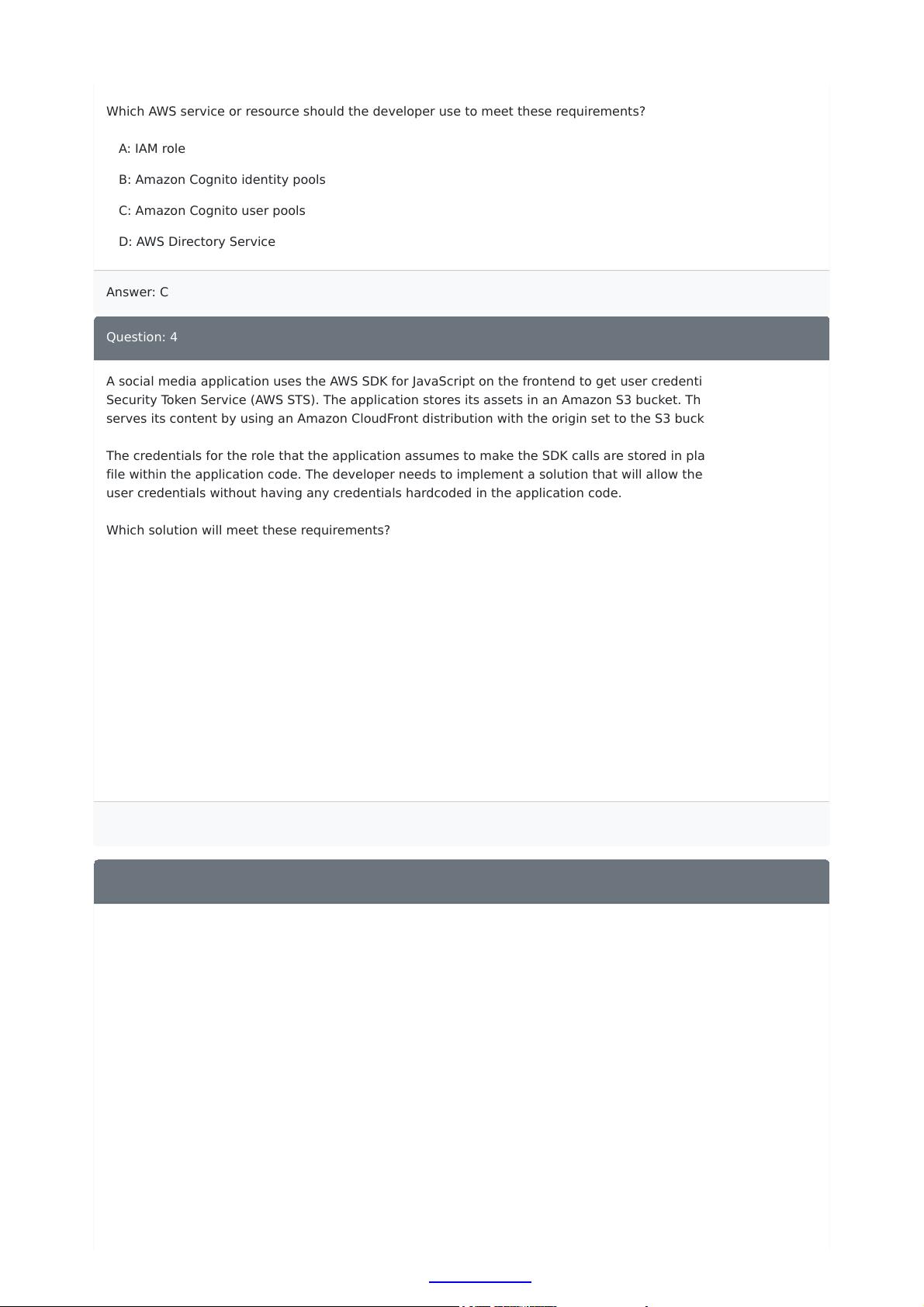
Which AWS service or resource should the developer use to meet these requirements?
Answer: C
A: IAM role
B: Amazon Cognito identity pools
C: Amazon Cognito user pools
D: AWS Directory Service
Question: 4
A social media application uses the AWS SDK for JavaScript on the frontend to get user credentials from AWS
Security Token Service (AWS STS). The application stores its assets in an Amazon S3 bucket. The application
serves its content by using an Amazon CloudFront distribution with the origin set to the S3 bucket.
The credentials for the role that the application assumes to make the SDK calls are stored in plaintext in a JSON
file within the application code. The developer needs to implement a solution that will allow the application to get
user credentials without having any credentials hardcoded in the application code.
Which solution will meet these requirements?
Answer: A
A: Add a Lambda@Edge function to the distribution. Invoke the function on viewer request. Add permissions
to the function's execution role to allow the function to access AWS STS. Move all SDK calls from the frontend
into the function.
B: Add a CloudFront function to the distribution. Invoke the function on viewer request. Add permissions to
the function's execution role to allow the function to access AWS STS. Move all SDK calls from the frontend
into the function.
C: Add a Lambda@Edge function to the distribution. Invoke the function on viewer request. Move the
credentials from the JSON file into the function. Move all SDK calls from the frontend into the function.
D: Add a CloudFront function to the distribution. Invoke the function on viewer request. Move the credentials
from the JSON file into the function. Move all SDK calls from the frontend into the function.
Question: 5
An ecommerce website uses an AWS Lambda function and an Amazon RDS for MySQL database for an order
fulfillment service. The service needs to return order confirmation immediately.
During a marketing campaign that caused an increase in the number of orders, the website's operations team
noticed errors for “too many connections” from Amazon RDS. However, the RDS DB cluster metrics are healthy.
CPU and memory capacity are still available.
What should a developer do to resolve the errors?
A: Initialize the database connection outside the handler function. Increase the max_user_connections value
on the parameter group of the DB cluster. Restart the DB cluster.
B: Initialize the database connection outside the handler function. Use RDS Proxy instead of connecting
directly to the DB cluster.
C: Use Amazon Simple Queue Service (Amazon SQS) FIFO queues to queue the orders. Ingest the orders into
the database. Set the Lambda function's concurrency to a value that equals the number of available
database connections.

Wish You PASS The Exam \(@^O^@)/
3/94Thank you for choosing ExamShoot.com product!
Answer: B
D: Use Amazon Simple Queue Service (Amazon SQS) FIFO queues to queue the orders. Ingest the orders into
the database. Set the Lambda function's concurrency to a value that is less than the number of available
database connections.
Question: 6
A company stores its data in data tables in a series of Amazon S3 buckets. The company received an alert that
customer credit card information might have been exposed in a data table on one of the company's public
applications. A developer needs to identify all potential exposures within the application environment.
Which solution will meet these requirements?
Answer: B
A: Use Amazon Athena to run a job on the S3 buckets that contain the affected data. Filter the findings by
using the SensitiveData:S3Object/Personal finding type.
B: Use Amazon Macie to run a job on the S3 buckets that contain the affected data. Filter the findings by
using the SensitiveData:S3Object/Financial finding type.
C: Use Amazon Macie to run a job on the S3 buckets that contain the affected data. Filter the findings by
using the SensitiveData:S3Object/Personal finding type.
D: Use Amazon Athena to run a job on the S3 buckets that contain the affected data. Filter the findings by
using the SensitiveData:S3Object/Financial finding type.
Question: 7
A software company is launching a multimedia application. The application will allow guest users to access
sample content before the users decide if they want to create an account to gain full access. The company wants
to implement an authentication process that can identify users who have already created an account. The
company also needs to keep track of the number of guest users who eventually create an account.
Which combination of steps will meet these requirements? (Choose two.)
Answer: BD
A: Create an Amazon Cognito user pool. Configure the user pool to allow unauthenticated users. Exchange
user tokens for temporary credentials that allow authenticated users to assume a role.
B: Create an Amazon Cognito identity pool. Configure the identity pool to allow unauthenticated users.
Exchange unique identity for temporary credentials that allow all users to assume a role.
C: Create an Amazon CloudFront distribution. Configure the distribution to allow unauthenticated users.
Exchange user tokens for temporary credentials that allow all users to assume a role.
D: Create a role for authenticated users that allows access to all content. Create a role for unauthenticated
users that allows access to only the sample content.
E: Allow all users to access the sample content by default. Create a role for authenticated users that allows
access to the other content.
Question: 8
A company is updating an application to move the backend of the application from Amazon EC2 instances to a
serverless model. The application uses an Amazon RDS for MySQL DB instance and runs in a single VPC on AWS.
剩余12页未读,继续阅读
资源评论

customservice
- 粉丝: 225
- 资源: 12
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
