没有合适的资源?快使用搜索试试~ 我知道了~
密码学手册之密码学概论
需积分: 0 2 下载量 200 浏览量
2015-05-05
14:40:37
上传
评论
收藏 335KB PDF 举报
温馨提示

试读
49页
详细介绍了密码学的基本思想,密码技术的基本应用,这部分的知识从总体上介绍了密码技术。
资源推荐
资源详情
资源评论

This is a Chapter from the Handbook of Applied Cryptography, by A. Menezes, P. van
Oorschot, and S. Vanstone, CR C Press, 1996.
For further information, see www.cacr.math.uwaterloo.ca/hac
CRC Press has granted the following specific permissions for the electronic vers ion of this
book:
Permission is granted to retrieve, print and store a single copy of this chapter for
personal use. This permission does not extend to binding multiple chapters of
the book, photocopying or producing copies for other than personal use of the
person creating the copy, or making electronic copies available for retrieval by
others without prior permissi on in writing from CRC Press.
Except where over-ridden by the specific permission abo ve, the standard copyright notice
from CRC Press applies to this electronic v ersion:
Neither this book nor any part may be reproduced or transmitted in any form or
by any means, electronic or mechanical, including photocopying, microfilming,
and recording, or by any information storage or retrieval system, without prior
permission in writing from the publisher.
The consent of CR C Press does not extend to copying for general distribution,
for promotion, for creating new works, or for resale. Specific permission must be
obtained in writing from CRC Press for such copying.
c
1997 by CRC Press, Inc.

Chapter
1
Overview of Cryptography
Contents in Brief
1.1 Introduction ............................. 1
1.2 Information security and cryptography .............. 2
1.3 Background on functions ...................... 6
1.4 Basic terminology and concepts ................... 11
1.5 Symmetric-key encryption ..................... 15
1.6 Digital signatures .......................... 22
1.7 Authentication and identification .................. 24
1.8 Public-key cryptography ...................... 25
1.9 Hash functions ........................... 33
1.10 Protocols and mechanisms ..................... 33
1.11 Key establishment, management, and certification ......... 35
1.12 Pseudorandom numbers and sequences .............. 39
1.13 Classes of attacks and security models ............... 41
1.14 Notes and further references .................... 45
1.1 Introduction
Cryptographyhas a long and fascinating history. The most complete non-technical account
of the subject is Kahn’s The Codebreakers. This book traces cryptography from its initial
and limited use by the Egyptians some 4000 years ago, to the twentieth century where it
played a crucial role in the outcome of both world wars. Completed in 1963, Kahn’s book
coversthoseaspects of thehistory which were most significant (up to thattime) to thedevel-
opment of the subject. The predominant practitioners of the art were those associated with
the military, the diplomatic service and government in general. Cryptography was used as
a tool to protect national secrets and strategies.
The proliferationof computersand communications systems in the 1960s brought with
it a demand from the private sector for means to protect information in digital form and to
provide security services. Beginning with the work of Feistel at IBM in the early 1970sand
culminating in 1977 with the adoption as a U.S. Federal Information Processing Standard
for encrypting unclassified information, DES, the Data Encryption Standard, is the most
well-known cryptographic mechanism in history. It remains the standard means for secur-
ing electronic commerce for many financial institutions around the world.
Themoststrikingdevelopmentinthe historyofcryptographycamein1976whenDiffie
and Hellman published New Directions in Cryptography. This paper introduced the revolu-
tionary concept of public-key cryptographyand also provided a new and ingeniousmethod
1
2 Ch. 1 Overview of Cryptography
for key exchange, the security of which is based on the intractability of the discrete loga-
rithm problem. Although the authors had no practical realization of a public-key encryp-
tion scheme at the time, the idea was clear and it generated extensive interest and activity
in the cryptographic community. In 1978 Rivest, Shamir, and Adleman discovered the first
practical public-key encryption and signature scheme, now referred to as RSA. The RSA
scheme is based on another hard mathematical problem, the intractability of factoring large
integers. This application of a hard mathematical problem to cryptography revitalized ef-
forts to find more efficient methods to factor. The 1980s saw major advances in this area
but none which rendered the RSA system insecure. Another class of powerful and practical
public-key schemes was found by ElGamal in 1985. These are also based on the discrete
logarithm problem.
One of the most significant contributions provided by public-key cryptography is the
digital signature. In 1991 the first international standard for digital signatures (ISO/IEC
9796) was adopted. It is based on the RSA public-key scheme. In 1994 the U.S. Govern-
ment adopted the Digital Signature Standard, a mechanism based on the ElGamal public-
key scheme.
The search for new public-keyschemes, improvementsto existing cryptographicmec-
hanisms, and proofs of security continues at a rapid pace. Various standards and infrastruc-
tures involving cryptographyare being put in place. Security products are being developed
to address the security needs of an information intensive society.
The purpose of this book is to give an up-to-date treatise of the principles, techniques,
and algorithms of interest in cryptographic practice. Emphasis has been placed on those
aspects which are most practical and applied. The reader will be made aware of the basic
issues and pointed to specific related research in the literature where more indepth discus-
sions can be found. Due to the volume of material which is covered, most results will be
stated without proofs. This also serves the purpose of not obscuring the very applied nature
of the subject. This book is intended for both implementers and researchers. It describes
algorithms, systems, and their interactions.
Chapter 1 is a tutorial on the many and various aspects of cryptography. It does not
attempt to convey all of the details and subtleties inherent to the subject. Its purpose is to
introducethe basicissuesandprinciplesand topointthe reader toappropriatechaptersin the
book for more comprehensive treatments. Specific techniques are avoided in this chapter.
1.2 Information security and cryptography
The concept of information will be taken to be an understood quantity. To introduce cryp-
tography, an understandingof issues related to information security in general is necessary.
Information security manifests itself in many ways according to the situation and require-
ment. Regardless of who is involved, to one degree or another, all parties to a transaction
must have confidencethat certain objectivesassociated with informationsecurity have been
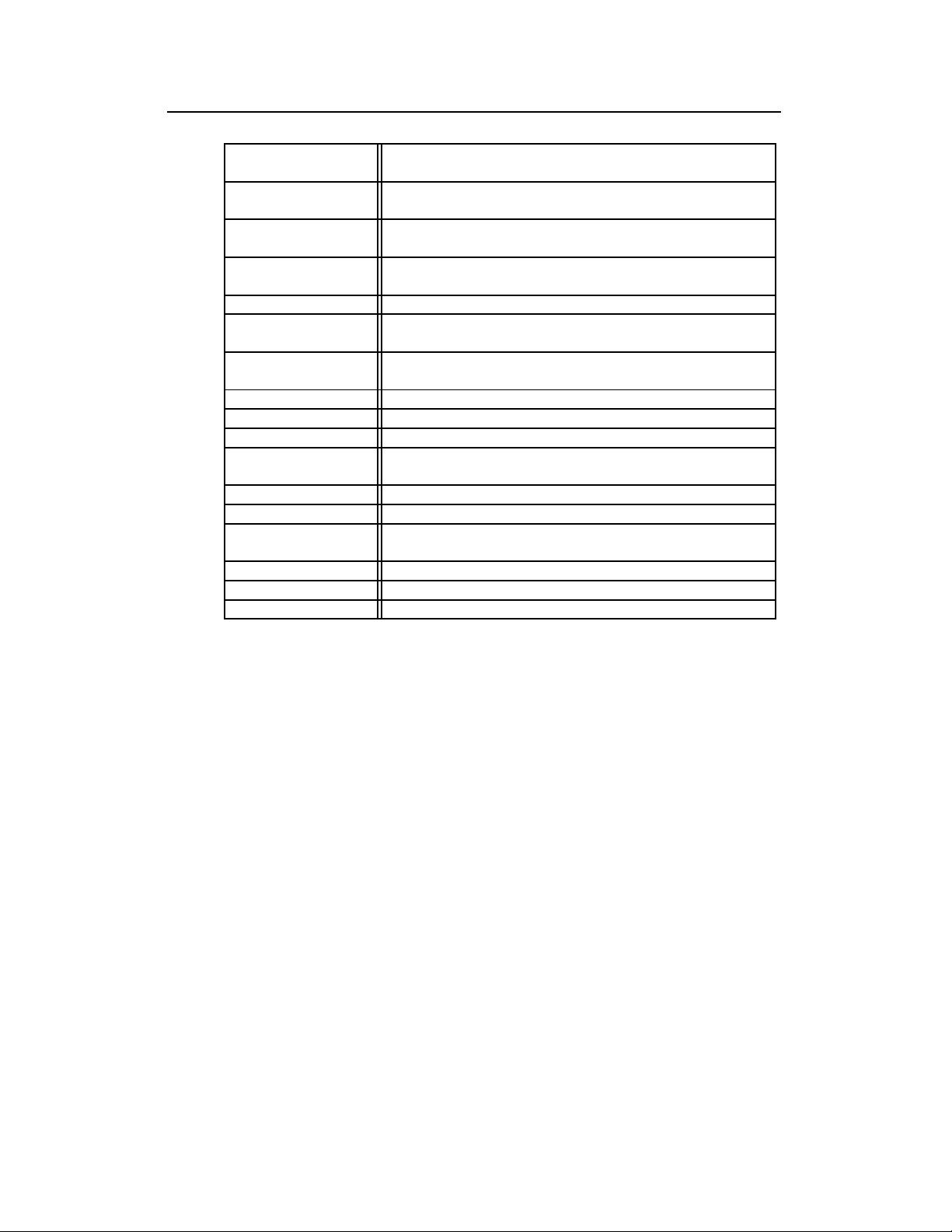
met. Some of these objectives are listed in Table 1.1.
Over the centuries, an elaborate set of protocols and mechanisms has been created to
deal with information security issues when the information is conveyed by physical doc-
uments. Often the objectives of information security cannot solely be achieved through
mathematical algorithms and protocols alone, but require procedural techniques and abid-
ance of laws to achieve the desired result. For example, privacy of letters is provided by
sealed envelopes delivered by an accepted mail service. The physical security of the en-
velope is, for practical necessity, limited and so laws are enacted which make it a criminal
c
1997 by CRC Press, Inc. — See accompanying notice at front of chapter.
§
1.2 Information security and cryptography 3
privacy
or confidentiality
keeping information secret from all but those who are autho-
rized to see it.
data integrity ensuring information has not been altered by unauthorized or
unknown means.
entity authentication
or identification
corroboration of the identity of an entity (e.g., a person, a
computer terminal, a credit card, etc.).
message
authentication
corroborating the source of information; also known as data
origin authentication.
signature a means to bind information to an entity.
authorization conveyance, to another entity, of official sanction to do or be
something.
validation a means to provide timeliness of authorization to use or ma-
nipulate information or resources.
access control restricting access to resources to privileged entities.
certification endorsement of information by a trusted entity.
timestamping recording the time of creation or existence of information.
witnessing verifying the creationor existence of information by an entity
other than the creator.
receipt acknowledgement that information has been received.
confirmation acknowledgement that services have been provided.
ownership a means to provide an entity with the legal right to use or
transfer a resource to others.
anonymity concealing the identity of an entity involved in some process.
non-repudiation preventing the denial of previous commitments or actions.
revocation retraction of certification or authorization.
Table 1.1:
Some information security objectives.
offense to open mail for which one is not authorized. It is sometimes the case that security
is achieved not through the information itself but through the physical document recording
it. For example, papercurrencyrequires special inks and material to prevent counterfeiting.
Conceptually, the way informationis recorded has not changed dramaticallyover time.
Whereas information was typically stored and transmitted on paper, much of it now re-
sides on magnetic media and is transmitted via telecommunications systems, some wire-
less. What has changed dramatically is the ability to copy and alter information. One can
make thousands of identical copies of a piece of information stored electronically and each
is indistinguishable from the original. With information on paper, this is much more diffi-
cult. What is needed then for a society where information is mostly stored and transmitted
in electronic form is a means to ensure information security which is independent of the
physical medium recording or conveying it and such that the objectives of information se-
curity rely solely on digital information itself.
One of the fundamental tools used in information security is the signature. It is a build-
ing block for manyother services such as non-repudiation, data origin authentication, iden-
tification, and witnessing, to mention a few. Having learned the basics in writing, an indi-
vidual is taught how to produce a handwritten signature for the purpose of identification.
At contract age the signature evolves to take on a very integral part of the person’s identity.
This signature is intended to be unique to the individual and serve as a means to identify,
authorize, and validate. With electronic information the concept of a signature needs to be
Handbook of Applied Cryptography by A. Menezes, P. van Oorschot and S. Vanstone.

4 Ch. 1 Overview of Cryptography
redressed; it cannot simply be something unique to the signer and independent of the in-
formation signed. Electronic replication of it is so simple that appending a signature to a
document not signed by the originator of the signature is almost a triviality.
Analogues of the “paper protocols” currently in use are required. Hopefully these new
electronic based protocols are at least as good as those they replace. There is a unique op-
portunity for society to introduce new and more efficient ways of ensuring information se-
curity. Much can be learned from the evolutionof the paper based system, mimicking those
aspects which have served us well and removing the inefficiencies.
Achieving information security in an electronic society requires a vast array of techni-
cal and legal skills. There is, however, no guarantee that all of the information security ob-
jectives deemed necessary can be adequatelymet. The technical means is providedthrough
cryptography.
1.1 Definition Cryptography is the study of mathematical techniques related to aspects of in-
formation security such as confidentiality, data integrity, entity authentication, and data ori-
gin authentication.
Cryptography is not the only means of providing information security, but rather one set of
techniques.
Cryptographic goals
Of all the information security objectives listed in Table 1.1, the following four form a
frameworkuponwhichtheotherswill be derived: (1)privacyor confidentiality (§1.5, §1.8);
(2) data integrity (§1.9); (3) authentication (§1.7); and (4) non-repudiation (§1.6).
1. Confidentiality is a service used to keep the content of information from all but those
authorized to have it. Secrecy is a term synonymouswith confidentiality and privacy.
There are numerous approaches to providing confidentiality, ranging from physical
protection to mathematical algorithms which render data unintelligible.
2. Data integrity is a service which addresses the unauthorized alteration of data. To
assure data integrity, one must have the ability to detect data manipulation by unau-
thorized parties. Data manipulation includes such things as insertion, deletion, and
substitution.
3. Authenticationis a service relatedto identification. This function applies to bothenti-
ties andinformationitself. Twopartiesenteringinto acommunicationshouldidentify
each other. Informationdeliveredover a channel shouldbe authenticatedas to origin,
date of origin, data content, time sent, etc. For these reasons this aspect of cryptog-
raphy is usually subdivided into two major classes: entity authentication and data
origin authentication. Data origin authentication implicitly provides data integrity
(for if a message is modified, the source has changed).
4. Non-repudiationis a servicewhich preventsanentity from denyingpreviouscommit-
ments or actions. When disputes arise due to an entity denying that certain actions
were taken, a means to resolve the situation is necessary. For example, one entity
may authorize the purchase of property by another entity and later deny such autho-
rization was granted. A procedure involving a trusted third party is needed to resolve
the dispute.
A fundamental goal of cryptography is to adequately address these four areas in both
theory and practice. Cryptography is about the prevention and detection of cheating and
other malicious activities.
This book describes a number of basic cryptographictools (primitives) used to provide
information security. Examples of primitives include encryption schemes (§1.5 and §1.8),
c
1997 by CRC Press, Inc. — See accompanying notice at front of chapter.
剩余48页未读,继续阅读
资源评论

ccecwangluo
- 粉丝: 1
- 资源: 3
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
