没有合适的资源?快使用搜索试试~ 我知道了~
北邮国院,middleware中间件期末复习,Block3-4
温馨提示

试读
61页
北邮国院,middleware中间件期末复习,Block3-4
资源推荐
资源详情
资源评论

!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
Block3
I
Security
concept
and
Web
Vulnerabilities
漏洞
D
Recap
Mid
ware
的
定义
a
software
layer
res
ding
on
top
of
the
operating
syste
that
connect
different
software
components
or
applications
Provides
interoperability
and
other
ser vices
like
the
distribution
of
functionality
scalability
load
balan
cin
and
fault
tolerance
Mid
ware
的
功能
application
specific
information
exchange
management
and
suppor t
2
Sucrity
concepts
Authentication
mechanisms
and
credential
management
Authorization
授权
and
access
control
manage
men
Shared
data
security
and
integrity
Secure
one
to
one
and
group
communication
Heterogeneous
security
environment
requirements

!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
9
9
suppor t
Secure
mobility
移动
性
management
Capability
能⼒
to
operate
in
device
wth
low
resources
Automatic
configuration
配置
and
management
of
these
facilities
⼯具
3
Web
Ser vices
Security
Concepts
Loosely
coupled
connectivity
松
散
耦合
连接
D
Using
htp
2
Multiple
clients
and
servers
interact
independently
3
Distributed
connections
Method
of
securing
web
services
Authentication
Ensuring
that
is
the
same
person
who
she
he
claims
to
be
如何
实现
强
身份
验证
⾄少
包括
上述
两
个
过程
1
something
one
has
eg
credentials
证件
2
something
one
knows
eg
password
3
something
one
is
eg.fingerprint
指纹

!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
Authorisation
授权
Access
control
granting
access
to
specific
resources
baced
on
an
authenticated
user's
entitlements
Confidentiality
Privacy
keeping
information
secretive
如何
实现
D
Encr ypt
the
content
of
a
message
Do
not
reveal
sending
and
receiving
par ties
identities
37
Use
public
key
infrastructures
PKI
for
encr yption
就
是
不但
要
加密
还
得
保证
收
发
⽅
身分
不
被
泄露
⽤
公
钥
Integr ity
Message
in
transit
should
not
be
altered
改变
如何
实现
D
Sender
should
digitally
sign
the
message
a
digital
signature
is
used
to
vali date
the
signature
2
timestamp
in
signature
prevent
from
replaying
aft
the
expira ti on
3
Exchanging
security
tokens
na
trusted
environment

!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
4
Layer
of
security
Transport
layer
security
Application
layer
security
D
complements
transport
level
security
2
is
based
on
XML
frameworks
a
Data
confidentiality
is
implemented
by
XML
Encr yption
b
Data
integrity
and
authenticity
ar e
implemented
by
XML
Signature
Middleware
layer
security
D
Middleware
layer
security
ensur es
that
the
communicating
security
layers
ar e
secur e
2
authentication
a
Single
Sign
On
s
so
systems
ar e
used
for
authentication
acr os s
the
layers
b
Virtual
organisation
membership
services
vous
are
used
for
authentication
authorisation
for
dife
rent
users
belonging
to
different
organisation
5
Web
Security
Vulnerabilities
脆弱
Web
security
Vulnerabilities
ar e
ar eas
of
weaknes s
in
web
security
that
hackers
or
intruders
expl oi t
access
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
!
ㄐ
1
to
systems
分类
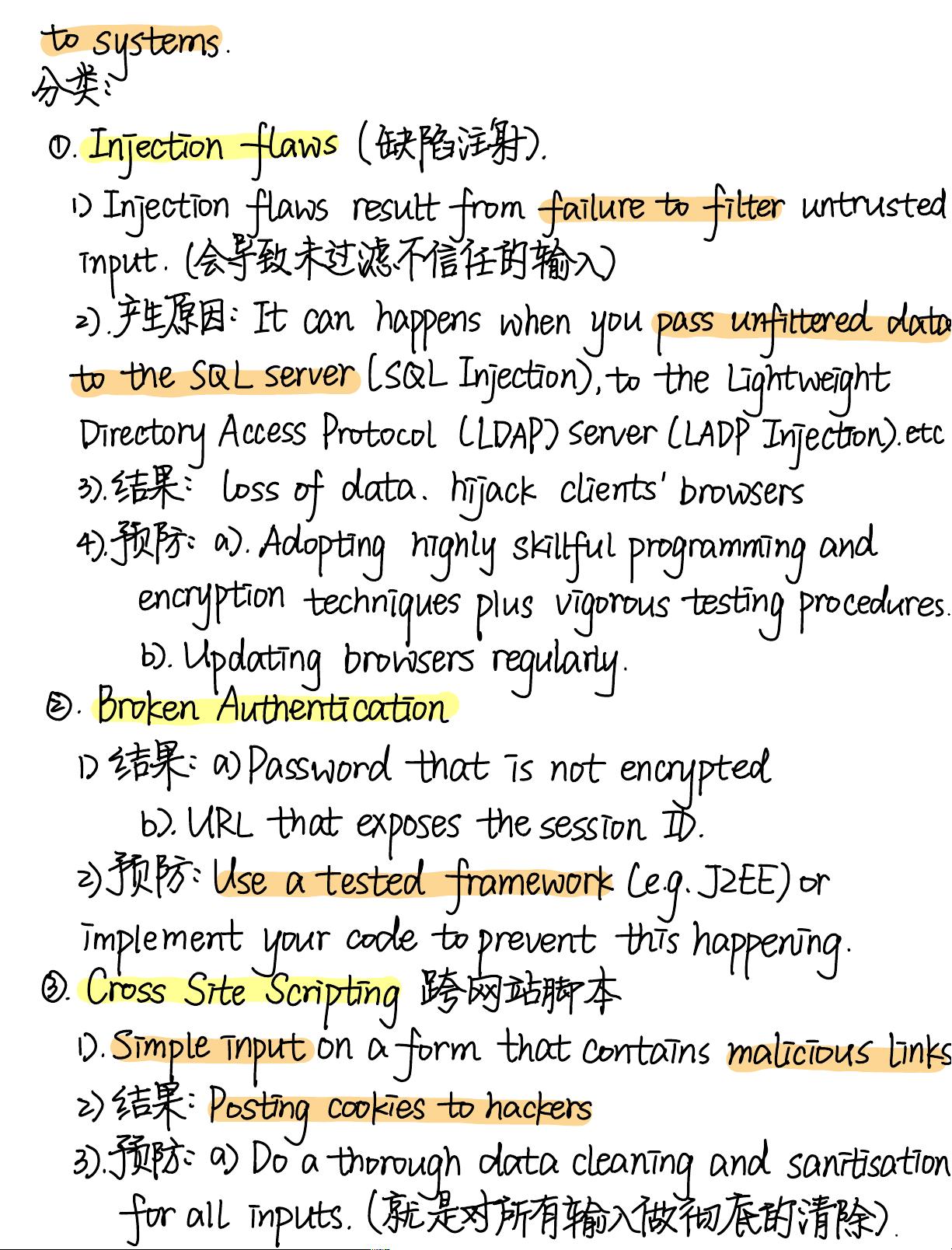
Injection
flaws
缺陷
注射
D
Injection
flaws
result
from
failure
to
filter
un
trust
e
input
会
导致
未
过滤
不
信任
的
输⼊
2
产⽣
原因
I
can
happens
when
you
pass
unfiltered
dā
to
the
SQL
server
SQL
Injection
to
the
Lightweight
Directory
Access
Protocol
LDAP
Server
LL
ADP
Injection
et
3
结果
loss
of
data
hjack
clients'browsers
4
预防
a
Adopting
highly
skillful
programming
and
encr yption
techniques
plus
vigorous
testing
procedure
b
Updating
browsers
regularly
Broken
Authentication
D
结果
a
Password
that
is
not
encr ypted
b
URL
that
exposes
the
session
ID
2
预防
Use
a
tested
framework
Leg.J
ZEE
or
implement
your
code
to
prevent
this
happening
Cross
Site
Scripting
跨
⽹站
脚本
D
Simple
input
on
a
form
that
contains
malicious
Lin
2
结果
Posting
cookies
to
hackers
3
预防
a
Do
a
thorough
data
cleaning
and
santsatio
for
all
inputs
就
是
对
所有
输⼊
做
彻底
的
清除
剩余60页未读,继续阅读
资源评论

 赵鸣漩2024-01-04orz
赵鸣漩2024-01-04orz
吕明易118
- 粉丝: 13
- 资源: 2
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
