没有合适的资源?快使用搜索试试~ 我知道了~
Testing Approaches for Network Traffic based on Linux .pdf
需积分: 3 0 下载量 187 浏览量
2023-08-05
16:17:52
上传
评论
收藏 1.22MB PDF 举报
温馨提示

试读
18页
Testing Approaches for Network Traffic based on Linux .pdf
资源推荐
资源详情
资源评论

See discussions, stats, and author profiles for this publication at: https://www.researchgate.net/publication/323536718
A Novel DDoS Floods Detection and Testing Approaches for Network Traffic
based on Linux Techniques
ArticleinInternational Journal of Advanced Computer Science and Applications · January 2018
DOI: 10.14569/IJACSA.2018.090248
CITATIONS
7
READS
913
5 authors, including:
Some of the authors of this publication are also working on these related projects:
Visual Saliency detection View project
Drones4Safety View project
Muhammad Tahir
Dalian University of Technology
26 PUBLICATIONS80 CITATIONS
SEE PROFILE
Naeem Ayoub
University of Southern Denmark
15 PUBLICATIONS61 CITATIONS
SEE PROFILE
All content following this page was uploaded by Muhammad Tahir on 06 March 2018.
The user has requested enhancement of the downloaded file.
(IJACSA) International Journal of Advanced Computer Science and Applications,
Vol. 9, No. 2, 2018
341 | P a g e
www.ijacsa.thesai.org
A Novel DDoS Floods Detection and Testing Approaches
for Network Traffic based on Linux Techniques
Muhammad Tahir*
1
, Mingchu Li
1
, Naeem Ayoub
2
, Usman Shehzaib
3
, Atif Wagan
4
1
School of Software Technology, Dalian University of Technology, (DUT), Dalian, Post (116621), P.R. China
2
School of Computer Science & Application Technology, Dalian University of Technology, Dalian, P.R. China
3
Dept. Of Computer Science, COMSATS Institute of Information Technology, Lahore, Pakistan
4
School of Computer Science & Eng., Nanjing University of Science & Technology, Nanjing, P.R. China
Abstract—In Today’s Digital World, the continuous
interruption of users has affected Web Servers (WSVRs),
through Distributed Denial-of-Service (DDoS) attacks. These
attacks always remain a massive warning to the World Wide
Web (WWW). These warnings can interrupt the accessibility of
WSVRs, completely by disturbing each data processing before
intercommunication properties over pure dimensions of Data-
Driven Networks (DDN), management and cooperative
communities on the Internet technology. The purpose of this
research is to find, describe and test existing tools and features
available in Linux-based solution lab design Availability
Protection System (Linux-APS), for filtering malicious traffic
flow of DDoS attacks. As source of
malicious traffic flow takes
most widely used DDoS attacks, targeting WSVRs. Synchronize
( SYN), User Datagram Protocol (UDP) and Internet Control
Message Protocol (ICMP) Flooding attacks are described and
different variants of the mitigation techniques are explained.
Available cooperative tools for manipulating with network
traffic, like; Ebtables
and Iptables tools are compared, based
on each type of attacks. Specially created
experimental
network was used for testing purposes, configured filters
servers
and bridge. Inspected packets flow through Linux-kernel
network stack along with
tuning options serving for increasing
filter server traffic throughput. In the part of contribution as an
outcomes, Ebtables tool appears to be most productive, due to
less resources it needed to process each packet (frame). It is
pointed out that separate detecting system is needed
for this tool,
in order to provide further filtering methods with data. As main
conclusion, Linux-APS, solutions provide full functionality for
filtering malicious traffic flow of DDoS attacks
either in stand-
alone state or combined with detecting systems.
Keywords—DDoS attacks; floods detection; Linux-APS
architecture; mitigation techniques; network traffic; Netfilter;
testing approaches
I. MOTIVATION AND INTRODUCTION
Through the development of information and
communication technology (ICT), our societies become global
information societies with all-around smart computing
environments, but unfortunately, the-security systems and
policies that regulate this environment are not accelerated as
needed. Attackers do not use the quarry in various
vulnerabilities found in applications running on systems.
Among the various cyber-attacks, (such as: SQL Injection
(SQLi), session recording, internal site scripting attack, Denial-
of-Service (DoS) attack, have become the most threatening
attacks so far, as very few methods have managed to mitigate
these attacks problems). Distributed Denial-of-Service (DDoS)
attacks, aggressors do not use a particular crowd on behalf of
their attacks however a cluster of numerous loads or uniform
hundreds of central processing units (CPUs), towards fixing an
SYN (synchronized) attacks. After the creation of development
solutions towards resolution the incidence of attacks stimulated
the development of the attacks themselves. Currently, DoS and
DDoS attacks have been outdated via DDoS attacks. The
World Wide Web (WWW) Safety FAQs, scheduled DDoS
declares that [1].
“A DDoS attack, usages numerous supercomputers towards
promotion of a synchronized DoS attack beside one or further
goals. By client and server machinery, the criminal is
intelligent to increase the efficiency of DoS, pointedly by
connecting the properties of numerous unknowing accessory
supercomputers which help as attack stands. Classically a
DDoS, main suite is connected the one (CPU, storage,
memory, by a filched version). The main suite, on a selected
time, before transfers to some digits of „proxy‟ plans,
connected on CPUs, everywhere on the Internet. The proxies,
once they obtain the -command, recruit the attack. By client
and server know-how, the main suite can pledge hundreds or
else level thousands of proxy series inside ages.”
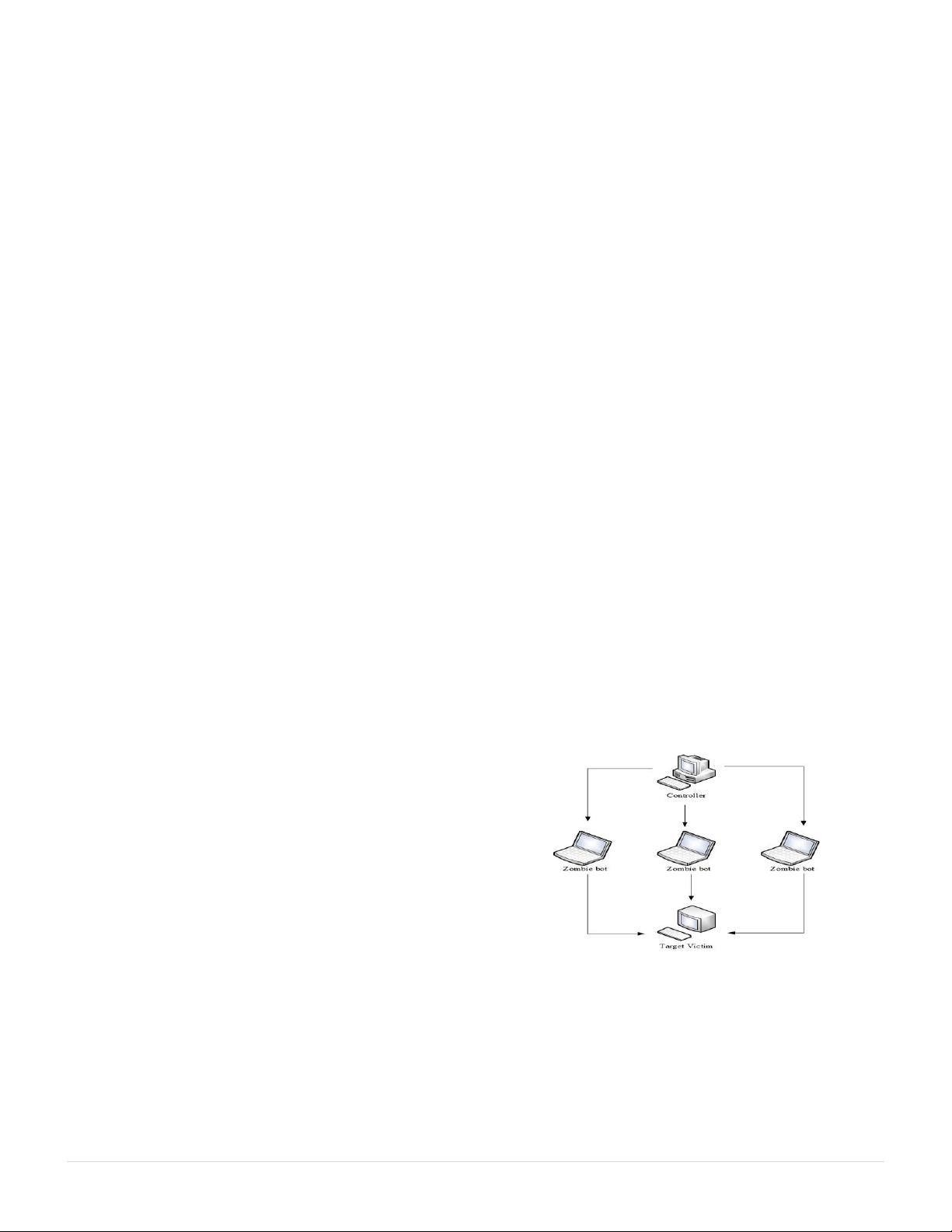
Fig. 1. Provides a clear idea about DDoS attacks.
Fig. 1 proves two main aims that make DDoS attacks, eye-
catching to intruders. Firstly, there are effective automatic-
tools to attack all victims [2]. That is, experience is not
necessarily required. Secondly, that one is typically dreadful
toward find an aggressor lacking general communication with
a person or else lacking novel roles fashionable utmost the
Internet routers [3].

(IJACSA) International Journal of Advanced Computer Science and Applications,
Vol. 9, No. 2, 2018
342 | P a g e
www.ijacsa.thesai.org
According to Akamai-state of the Internet security reports
that the frequency of DDoS attacks has been increased by
131% Worldwide in 2017. Along with recent event, involving
the WannaCry ransom-ware attacker, (also known as
WanaCrypt0r & W-Cry Ransom ware) malicious software
spreading security and protection questions for Internet users
are becoming more important than ever before.
The importance of this research work is to find out and
testing most efficient and reliable tools existing in Linux-based
systems for filtering and aggregation DDoS attacks. Linux-
based solutions are considered as bit and easy to configured
systems among available competitors.
Most common WSVRs, focused DDoS attacks, will be
taken into consideration such as SYN, UDP and ICMP floods.
By configuring filter servers and applying suitable setup, most
efficient and reliable solution will be chosen. Aggregation of
data traffic flow will be considered from a point of impact on
filtering productivity.
This research work, is divided into following four
parts:
Firstly, the overview of the DDoS attack is provided.
Secondly, literature analysis & background gives a
brief survey of research going in the area of most
common types and methods of mitigations of DDoS
attacks and available Linux-based solutions for data
traffic filtering and aggregation. After going through
the literature analysis and its background.
Thirdly, the problem statement and related work has
been identified and will describe experimental network
components and kernel tuning.
Finally, it focuses on the conclusion of the work that
will include implementation of the selected solutions
on data filter servers, differentiated by installed
hardware.
II. LITERATURE ANALYSIS AND BACKGROUD
DDoS attacks have become more common and fashionable
in recent years. Large-scale systems of septic computers
„zombie/bot‟ trust their processing plus processing capabilities
to overload public service and deny it to authentic users.
The attacks on major e-commerce locations in February
2000 and attacks on origin domain name system (DNS),
service 2003 and 2007 made community devotion towards the-
problematic of DDoS attacks [4]. Nowadays, medium-volume
Web pages are generally condemned through crooks toward
getting defense from their venders. These are also deprived of
appealing [5]. Additionally, Internet Service Providers (ISPs),
must address the problem that DDoS traffic and increases the
bandwidth of the communication channel.
The first tools such as Tribe Flood Network (TFN) [6],
Stacheldraht, Trinoo or Mstream [7], have used communication
structures without cryptography and were organized
hierarchically. Best of these implements recycled TCP, SYN,
UDP, and ICMP floods using potentially recognizable limits.
As several of these attacks have been positively relieved, an
innovative formation of robots takes developed Spartan-
dominion Robot (SDBot), Agobot, commonly used Phatbot
and well-known representatives using Internet Relay Chat
(IRC), as a secure link [8]-[10]. These tools also include
distribution methods besides take additional refined attack
algorithms that can stay updated concluded the Internet.
Sudden mitigating techniques of DDoS attacks, on the
Internet sources or on kernel seems impossible owing towards
the circulated and authoritative environment of the Internet
protocol IP, based system network. Several methods were
suggested to search for the original IP address, of the attacker
using filtering mechanisms.
Internet Engineering Task Force (IETF) documented filter
entry approach is defined in request for comments (RFC:
2827) [11]. And assistances mitigate DDoS attacks, through IP
spoofing, which indirectly deal with different types of network
misuse, causes Internet traffic to control source. Network filter-
is a „good neighbor‟. This policy is based on mutual
cooperation between ISPs, for their common benefits.
In order to avoid manipulation of IP addresses, Park et al,
[12] Proposed packet filters distributed on standalone systems
over the Internet are to be stopped packets of counterfeit IP
addresses.
Suspenseful Savage et al. [13] is recommended that IP
Trace back find the basis of fake IP addresses using
probabilistic labeling packages. Song et al. [14] provides an
extended scheme for probabilistic packet selection to reduce
the frequency of false positives to restore the attack path.
Another improved scheme for probabilistic labeling of
packages was proposed by Bellovin et al. [15] to reduce the
cost of calculation. This ICMP is a tracking system similar to a
probabilistic scheme for labeling packages.
In this system, the routers generate ICMP, packets at the
Low-probability destination. For a significant data traffic flow,
the recipient can gradually restore the route made by the
packets in the leak.
Mahajan et al. [16] provide a system where routers learn
fixed costs to provide good traffic from bad traffic. Siris et al.
[17] represents the variance finding algorithms on behalf of
identifying TCP and synchronized SYN attacks.
Modifying threshold algorithm and a specific request of the
total amount of algorithm is for finding of a switching point.
Modifying threshold algorithm associates with number of the
SYN packets established over an estimated number of
predetermined intervals, founded on the new dimensions.
Towards promotion of increases, a panic inception should
remain overdone in series. The, Cumulative Sum Control Chart
(CUSUM), algorithm usages the change among the sum of
SYN packet per time pause besides the number valued on
behalf of the similar range such as „Gaussian‟ random
variable. Then, flood attack SYN, is sensed by consuming the
total amount built on the probability like; instantaneous
significance due to the change in the average velocity of the
circulation.

(IJACSA) International Journal of Advanced Computer Science and Applications,
Vol. 9, No. 2, 2018
343 | P a g e
www.ijacsa.thesai.org
Several authors, including Wang et al., [18] has proposed a
method for detecting SYN flood attacks. These are built and
going on the construction of TCP, SYN, FIN flags and Rapid
Spanning Tree Protocol (RSTP). Protocols on leaflets connect
the final nodes to the Internet. There is a change in the sum of
SYN, FIN packets perceived rest (RST) flag set and CUSUM,
algorithm is used to detect the switch point. Towards decrease
the influence of changed entree designs at diverse locations, the
change among the amount of: (SYNs), (FINs) and (RSTs)
remains controlled with the calculated typical by (FINs) and
(RSTs).
Luo et al. and others [19] Also proposed a system for
detecting Pulsing Distributed Denial-of-Service (PDoS) and
DoS attacks on expressive target's WSVRs, with (t\¥0)
variances produced by PDoS attacks, specifically jitter in
inbound documents traffic flow and reduction of outward---
bound TCP, and acknowledgement (ACK) data networks
traffic flow.
Cabrera et al. [20]. Detecting DDoS using Management
Information Base (MIB), traffic flow valuables on behalf of the
aggressor and destination. Appropriate autographs were
identified towards detect attacks from known attacks. On the
side of the attacker, the DDoS attacks must be detected before
it is launched by identifying precursors based on MIB.
In addition to previous work, intrusion detection systems
and firewalls are one of the best security systems that work by
pairing packets with predefined rules and filtering them
accordingly. Linux-kernels had a 1.1 packet filter. At the end
of 1994, kernel-hacker Alan Cox carried the IP firewall from
Berkeley Software Distribution (BSD), to Linux. In mid-1998,
Rusty Russell et al. [21] and others revised most of the
networks under the Linux kernel of the 2.1 development series
and introduced the IP chains user space tool.
The Linux-kernel that preceded this had some very serious
disadvantages with some main working functionality. The old
Linux-firewall code does not apply to fragments. The 32-bit-
counter (at least on Intel), does not allow to enter other
protocols than TCP, UDP and ICMP.
It cannot make major atomic changes that can not specify
„Inverse Functions‟. It has little and can be tricky to handle
(which makes it prone to user failure).
Russell's work redefined radically the Linux-network layer
and enabled filtering of kernel-packets in user-space (which
simplified usage, configuration, and security).
Finally, the next advanced generation of tools, “Ebtables-
Iptables” and another core transcript took place in mid-1999
for Linux 2.4. The enhancement initiated in 2.2 continued, and
the extensive Linux arsenal of networking tools. The core is
rewritten as „Netfilter‟ [22].
In this research article, we proposed different Linux-based
resolution approaches and testing simulations for network
traffic, filtering data packets to protect against DDoS attacks
using cooperative “Ebtables” and “Iptables” tools, mitigation
techniques, and Linux-based resolution lab design firewall
architecture.
III. PROBLEM STATEMENT AND RELATED WORK
Problem No.1. The DDoS attacks, stands a rigid
challenge towards mark and connected packages
inaccessible near all users, frequently via briefly
disturbing before interrupting sudden services from
their domain server. Originally based on target service
resources limitation, DDoS attacks can be done by
either spoofing attacker IP address or using so called:
'Botnet'. Botnet is a network of hacked devices,
connected to global network which control is gained by
third party. Compromise devices can send data traffic
to target services which makes DDoS mitigation
complex. As it is hard to distinguish authentic
malicious traffic flow from the DDoS attacks.
Problem No.2. The DDoS attacks, stance has a main
warning to the internet. This must be reduced the class
from the internet service. This is significant because
the internet has now become a critical resource whose
violation has financial consequences or even terrible
consequences for human security. More and more
critical services use the internet for daily work. DDoS
attacks do not just mean losing the latest game results
of the environment. This could malicious traffic flow
from DDoS attacks losing an effort on the item you
want to buy or lose to your customers for a day or two
under attack. So this one is significant in the direction
of consume funds towards stop or else moderate the
system.
Smart breaks support unbroken competition among the
aggressors and the protectors. Passing of these remain a real
ramparts beside a confident category of attack. The aggressors‟
revolution devices finding an approach toward avoid this
defense.
In addition, since absolute protection is not feasible,
developing effective defense framework involves an often
complicated set of Trade-offs:
For this purpose, numerous solutions have been proposed
as discussed in literature analysis background. „Firewall‟ is
one of them. By using a dedicated firewall we can block all the
IP addresses that are flood the server to consume its resources.
According to Radware‟s: (2016-2017) Global application
and network security report [23]. The most common types of
attacks were 2016 (e.g., UDP, SYN and ICMP Flood).
A. Distributed Dinel-of-Service (DDoS) Flooding Detection -
Tools & It’s Mitigation Techniques
1) The Synchronized (SYN) Flood Detection:
Attacks of this kind targeting three-way TCP, link
mechanism that sends connection requests faster than the target
computer that can handle them, causing network capacity [24].
In common situations, the client method is activated
through distribution of SYN junk messages toward affecting
server.
The affecting server formerly confirms effective SYN junk
messages by distribution and SYN acknowledgement (ACK)
messages toward sudden client.
剩余17页未读,继续阅读
资源评论

程序员徐师兄
- 粉丝: 1192
- 资源: 2379
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
