没有合适的资源?快使用搜索试试~ 我知道了~
Security audit report for imtoken wallet
0 下载量 163 浏览量
2023-12-24
22:43:47
上传
评论
收藏 2.29MB PDF 举报
温馨提示

试读
17页
This security audit is a requested service authorized by the client. The service is mainly about application penetration testing which helps to find the vulnerabilities and threats of the target. All the penetration testing items are done by simulating the real world malicious attacks against the target, which mimics human hackers’ activities by manual penetration testing with automated tools.
资源推荐
资源详情
资源评论

Security Audit Report
Client: IMTOKEN PTE. LTD.!
Target:!
imToken v2.4.0.538 stg (iOS)!
imToken v2.4.0.533 dev (Android)!
PeckShield, Inc.
2019/4/23"
About this Report
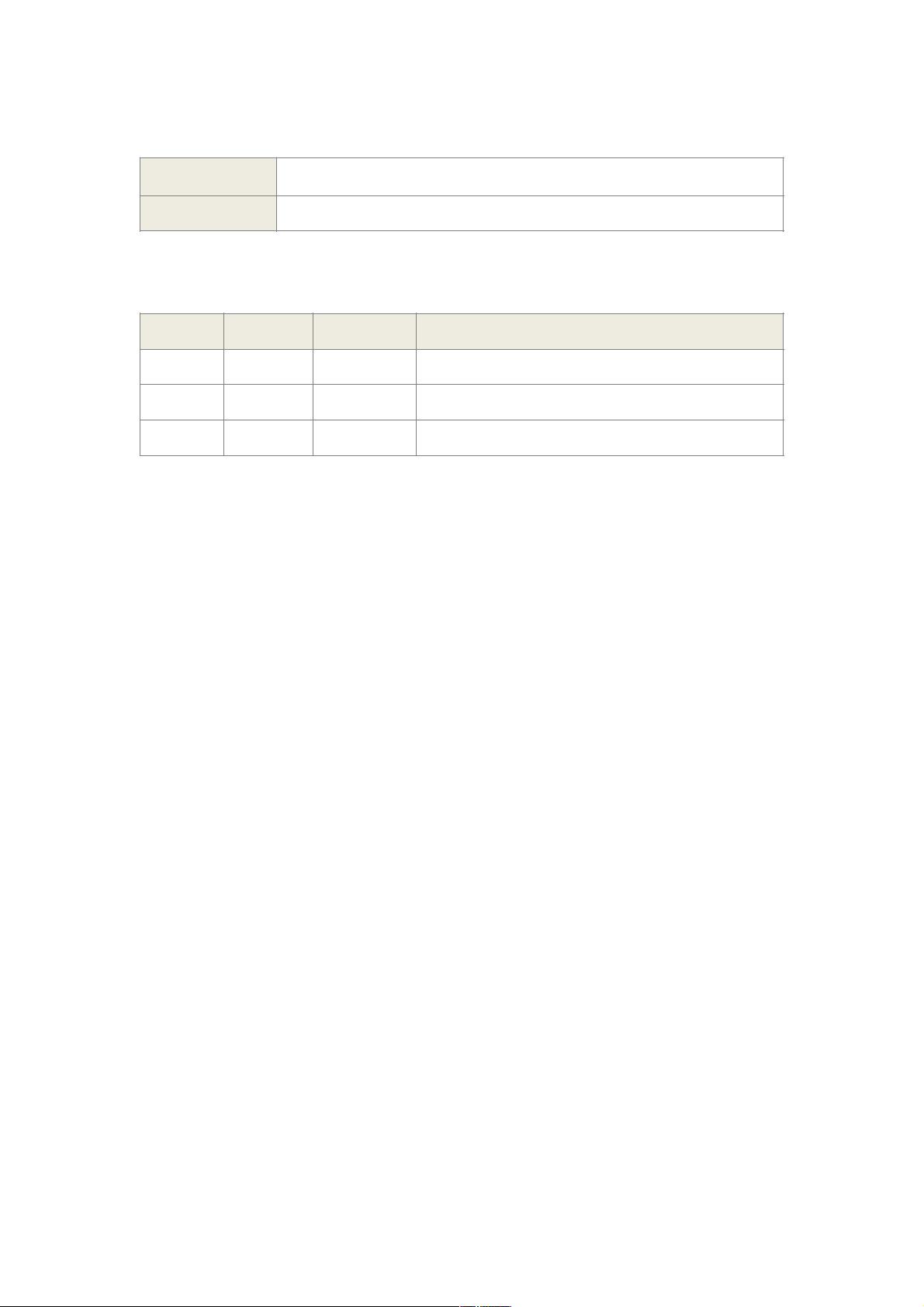
Revision History
Name
《Security Audit Report》
Version
v1.1
Revision
Date
Author
Change Log
v1.1
2019/4/23
Huaguo Shi
Section 3.2.2 updated.
v1.0
2019/4/22
Huaguo Shi
File created with preliminary audit results.
Copyright © PeckShield, Inc 2018

Table of Contents
1. Introduction 4 .........................................................................................
1.1.Background 4 ....................................................................................
1.2.Purpose 4 ...........................................................................................
1.3.References 4 ......................................................................................
1.4.Scope 5 ...............................................................................................
2. Results 6 ..................................................................................................
2.1.Summary 6 ........................................................................................
3. Android Vulnerabilities 7 ......................................................................
3.1.Communication Security 7 ..............................................................
3.2. System Security 8 ............................................................................
3.3. Data Security 10 ..............................................................................
3.4. Cosmos Implementation 11 ............................................................
4. iOS Vulnerabilities 12 ............................................................................
4.1. Wallet Data Security 12 ..................................................................
4.2. Security Risks Detection 13 ...........................................................
4.3. Business Logic 14 ............................................................................
4.4. Cosmos Implementation 15 ...........................................................
5. Risk Rating Methodology 17.................................................................
Copyright © PeckShield, Inc 2018

1. Introduction
1.1. Background
This security audit is a requested service authorized by the client. The service is
mainly about application penetration testing which helps to find the vulnerabilities
and threats of the target. All the penetration testing items are done by simulating the
real world malicious attacks against the target, which mimics human hackers’
activities by manual penetration testing with automated tools. The goal and
responsibilities of this security audit are listed as follows:
• Identify the vulnerabilities which could be exploited remotely by attackers, leading
to financial damage to the client.
• Triage the vulnerabilities in the terms of (but not limited to) the impact to the
client’s business logic, private data leakage, the availability of client’s services, etc.
• Provide the corresponding solution to fix the problem with support services.
In the process of the security audit, we collect information, perform testing attacks,
build threat models, and identify/triage/analyze/exploit vulnerabilities as attackers.
The whole process is based on OWASP TOP 10 and other standards defined by
national institutes, which is controllable and tunable.
1.2. Purpose
The purpose of the security audit is to rate the security level of the target, report the
vulnerabilities identified in the target, and improve the target in terms of stability and
reliability by providing solutions to fix the vulnerabilities.
1.3. References
➢ GB/T 18336-2008: IT security technology information technology security
evaluation criteria
➢ GB 17859-1999: Classified criteria for security protection of computer
Copyright © PeckShield, Inc 2018
剩余16页未读,继续阅读
资源评论

FeelTouchLabs
- 粉丝: 1w+
- 资源: 78
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
