没有合适的资源?快使用搜索试试~ 我知道了~
CISSP精要备考文档(高清PDF版)
温馨提示

试读
11页
CISSP精要备考文档,很精要的备考文档,希望对备考CISSP的朋友有所帮助!
资源推荐
资源详情
资源评论
CISSP aide-mémoire
CISSP aide-mémoire
By Éric Allaire, B.Sc., CISSP, P+CP
eric_is@ericallaire.com
April 3, 2007
Table of contents
REFERENCES USED:..............................................................................I
TABLE OF FIGURE:................................................................................I
SPECIAL NOTES......................................................................................I
DISTRIBUTION AGREEMENT: ..............................................................I
DOMAIN 1 – ACCESS CONTROLS........................................................1
D
EFINITIONS
: .......................................................................................1
B
ASICS AUTHENTICATION PRINCIPLES
................................................1
Types of password: ..........................................................................1
B
IOMETRICS
.........................................................................................1
Error types:......................................................................................1
Crossover Error rate (CER):...........................................................1
A
CCESS CONTROL MODELS
: ................................................................1
Discretionary Access Control..........................................................1
Mandatory Access Control ..............................................................1
Role-Based Access Control (RBAC)................................................1
Lattice-based Access Control;.........................................................1
Ruled based......................................................................................1
Restricted interfaces.........................................................................1
Physically constrained:....................................................................1
Control matrix..................................................................................1
Capability table................................................................................1
ACL ..................................................................................................1
Content-dependent Access Control..................................................1
A
CCESS CONTROL ADMINISTRATION
..................................................1
Access control administration – centralized....................................1
Access control administration – Decentralized ...............................1
Access control administration – Hybrid ..........................................1
A
CCESS CONTROL CATEGORIES
: .........................................................1
Technical Access Controls:..............................................................1
Physical Controls: ...........................................................................1
Administrative controls:...................................................................1
I
NTRUSION DETECTION
........................................................................1
A
TTACKS TO ACCESS
...........................................................................1
A
TTACKS ON PASSWORDS
...................................................................1
DOMAIN 2 - TELECOM AND NET SECURITY.....................................1
D
EFINITIONS
: .......................................................................................1
TCP/IP..................................................................................................2
User Datagram Protocol .................................................................2
C
ABLING AND DATA TRANSMISSION TYPES
........................................2
Cables:.............................................................................................2
LAN
TECHNOLOGY
..............................................................................2
Network topology.............................................................................2
Media access technology .................................................................2
Protocols stack: ...............................................................................2
N
ETWORK DEVICES AND SERVICES
.....................................................2
Firewalls:.........................................................................................2
Data diode: ......................................................................................2
C
ONNECTIVITY PROTOCOLS
:...............................................................2
Connectivity protocols .....................................................................2
Authentication protocol:..................................................................2
Tunneling protocols.........................................................................2
R
EMOTE ACCESS METHODS AND TECHNOLOGY
.................................3
Remote network access ....................................................................3
Wireless technology:........................................................................ 3
Wireless Application Protocols........................................................3
Network services ..............................................................................3
T
ELECOMMUNICATIONS PROTOCOLS AND DEVICES
...........................3
A
TTACKS RELATED TO TELECOMMS
...................................................3
DOMAIN 3 – SECURITY MANAGEMENT.............................................3
S
ECURITY DEFINITIONS
: ......................................................................3
C
ONTROL TYPES
: .................................................................................3
Administrative..................................................................................3
Technical..........................................................................................3
physical ............................................................................................3
S
ECURITY MODEL
:...............................................................................3
R
ISK
M
ANAGEMENT
............................................................................3
R
ISK
A
NALYSIS
....................................................................................3
Assigning value to the assets:..........................................................3
C
ALCULATION IN STEPS
.......................................................................3
Annualized Loss Expectancy............................................................3
S
ECURITY
P
OLICY
................................................................................4
L
AYERS OF RESPONSIBILITIES
:............................................................4
Data classification...........................................................................4
Employee management:...................................................................4
DOMAIN 4 – APPS & SYS DEV..............................................................4
D
EFINITIONS
: .......................................................................................4
P
ROJECT DEVELOPMENT SECURITY
.................................................... 4
A
DMINISTRATIVE CONTROLS
:............................................................. 4
S
OFTWARE DEVELOPING MODELS
...................................................... 4
O
BJECT
-O
RIENTED PROGRAMMING
.................................................... 4
A
PPLICATION THREAT
......................................................................... 4
D
ISTRIBUTED COMPUTING
.................................................................. 4
D
ATABASES
......................................................................................... 5
Database Definition: ....................................................................... 5
Database securities:........................................................................ 5
A
RTIFICIAL INTELLIGENCE
(AI).......................................................... 5
T
YPES OF ATTACKS
(
MALWARE
) ........................................................ 5
DOMAIN 5 - CRYPTOGRAPHY............................................................. 5
CIA
GOALS
: ......................................................................................... 5
D
EFINITIONS
:....................................................................................... 5
C
IPHER PRINCIPLES
: ............................................................................ 5
B
ASIC ENCRYPTION METHODS
............................................................ 5
Substitution...................................................................................... 5
Transposition................................................................................... 5
Block symmetric............................................................................... 5
Stream.............................................................................................. 5
S
YMMETRIC CRYPTOGRAPHY
: ............................................................ 5
A
SYMMETRY CRYPTOGRAPHY
............................................................ 5
Asymmetric algorithm ..................................................................... 5
H
YBRID APPROACH
: ............................................................................ 5
K
EY MANAGEMENT
:............................................................................ 5
I
NTEGRITY AND SIGNATURES
(
HASHING
)............................................ 6
C
RYPTOGRAPHY APPLICATIONS
: ........................................................ 6
Mail application:............................................................................. 6
Internet security applications:......................................................... 6
Public Key Infrastructure................................................................ 6
A
TTACKS
: ............................................................................................ 6
DOMAIN 6 – SECURITY MODELS & ARCHITECTURES ................... 6
D
EFINITIONS
:....................................................................................... 6
C
OMPUTING PRINCIPLES
..................................................................... 6
O
PERATING SYSTEM MECHANISM
....................................................... 6
Protection rings:.............................................................................. 7
S
ECURITY MODELS
.............................................................................. 7
S
ECURITY EVALUATION TYPES
........................................................... 7
Trusted Computer System Evaluation Criteria ............................... 7
Information Technology Security Evaluation Criteria.................... 7
Common Criteria............................................................................. 7
C
ERTIFICATION
V
S
A
CCREDITATION
: ................................................ 7
DOMAIN 7 – OPERATION SECURITY.................................................. 7
D
EFINITIONS
:....................................................................................... 7
O
PERATION CONTROLS
....................................................................... 7
C
ONFIGURATION MANAGEMENT AND MEDIA CONTROL
:................... 7
R
EACTING TO FAILURES AND RECOVERING
: ...................................... 7
Systems can react in four different ways:........................................ 7
A
VAILABILITY
:.................................................................................... 7
F
AX SECURITY
:.................................................................................... 8
DOMAIN 8 – DRP & BCP ...................................................................... 8
D
EFINITIONS
:....................................................................................... 8
P
OSSIBLE THREATS
: ............................................................................ 8
S
TEP IN PREPARING THE
BCP
S
............................................................ 8
1.
Project initiation.............................................................. 8
2.
Business impact analysis (BIA):...................................... 8
3.
Recovery strategies/plan ................................................. 8
4.
Plan design and implementation ..................................... 8
5.
Testing, maintenance and awareness training................ 8
DOMAIN 9 – LAW AND ETHICS........................................................... 8
D
EFINITIONS
:....................................................................................... 8
E
THICS INSTITUTION
........................................................................... 8
H
ACKER ISSUES
................................................................................... 8
E
STABLISHING LIABILITIES AND RAMIFICATION
................................ 8
T
YPES OF LAW
..................................................................................... 9
criminal............................................................................................ 9
Civil/tort .......................................................................................... 9
Administrative.................................................................................. 9
I
NTELLECTUAL PROPERTY LAW
.......................................................... 9
Trade secret..................................................................................... 9
Copyright
©
...................................................................................... 9
Trademark
™
.................................................................................... 9
Patent............................................................................................... 9
I
NVESTIGATING COMPUTER CRIME
..................................................... 9
C
HAIN OF CUSTODY
............................................................................ 9
Evidence life cycle ........................................................................... 9
T
YPES OF ATTACKS
............................................................................. 9
DOMAIN 10 – PHYSICAL SECURITY .................................................. 9
D
EFINITIONS
:....................................................................................... 9
A
REAS OF PHYSICAL SECURITY
.......................................................... 9
Physical location:............................................................................ 9
Construction:................................................................................... 9
Computing area:.............................................................................. 9
E
LECTRICAL AND ENVIRONMENTAL CONCERNS
................................ 9
F
IRE DETECTION AND SUPPRESSION
................................................... 9
Detection.......................................................................................... 9
Suppression...................................................................................... 9
P
ERIMETER SECURITY
......................................................................... 9
Passage............................................................................................ 9
Fence................................................................................................9
lighting .............................................................................................9
Surveillance devices:......................................................................10
IDS
(
PHYSICAL
): ................................................................................10
OSI MODEL...........................................................................................10
TCP/IP (INTERNET REFERENCE MODEL).......................................10
D
ETAILS OF
TCP/IP ...........................................................................10
Application layer............................................................................10
Transport layer ..............................................................................10
Internet layer..................................................................................10
References used:
Susan Hansche/John Berti/Chris Hare, Official (isc2) guide to the
CISSP Exam; 2004
Shon Harris, all-in-one CISSP certification guide, 2002;
Shon Harris, Mikes Meyer certification to CISSP, 2002;
Peter H. Gregory; CISSP for Dummies , 2003;
Ellen Dutton, LAN security handbook, 1994;
Peter H. Gregory, Solaris security, 2000;
Ed Tittel/Mike Chapple/James Michael Stewart, CISSP study
guide, 2003;
www.Infosecuritymag.com
www.cccure.net
www.cccure.org
www.isc2.org
Table of figures:
figure 1 (http://searchnetworking.techtarget.com).......................10
figure 2 .......................................................................................10
figure 3 .......................................................................................10
Special notes
This is not a supplement to your readings, web site browsing,
and other studying formulas but intends to be an aide-mémoire
prior to your exam. Many hours are required to study the various
CKB subjects using web sites, books on-line questionnaires, and
forums. The CISSP exam can be very time consuming study, but
worth it!
*This document is not a supplement or a substitution to your
local/area building codes or local laws.
Distribution agreement:
This document may be freely read, stored, reproduced,
disseminated, translated or quoted by any means and on any
medium provided the following conditions are met:
Every reader or user of this document acknowledges that he his
aware that no guarantee is given regarding its contents, on any
account, and specifically concerning veracity, accuracy and
fitness for any purpose. Do not blame me if some of the exam
questions are not covered or the correct answer is different from
the content of this document. Remember: look for the most
correct answer, this document is based on the seminar content,
standards, books, and where and when possible the source of
information will be mentioned.
No modification is made other than cosmetic, change of
representation format, translation, correction of obvious syntactic
errors.
Comments and other additions may be inserted, provided they
clearly appear as such. Comments and additions must be dated
and their author(s) identifiable. Please forward your comments for
insertion into the original document.
*This document is not a supplement or a substitution to your
local/area building codes or local laws.
CISSP Aide-mémoire www.ericallaire.com
i
CISSP aide-mémoire
Domain 1 – Access Controls
The purpose of access control is to protect information and
resources from unauthorized logical access to the information.
Definitions:
Subject: is an active entity requesting access to an object or data.
Object: is a passive entity that contains info or data.
Access: ability of a subject to do something such as: read, write,
create, execute.
Access control: a security feature that controls how subjects and
objects interact with each other.
Granularity: the fine divisions of a component so that it can be
fine-tuned which access controls can be regulated.
Identification: the association of some unique or at least useful
label to a subject. Ascertains the identity of a subject.
Authentication: proving that the subject is who he claims to be.
Something he knows, password; something he has, smart card;
something he is, fingerprint.
Authorization: granting access to resources based on criteria list.
Strong authentication (two factor): is the requirement of having
two of the three factors of authentication.
Excessive privilege: user or administrator has more privileges
then he/she needs for the security of the system.
Basic authentication principles
Identification > authentication > authorization =>> resources
The authentication process is done through the combination of
those three: something you know (password), something you are
(biometrics), something you physically have (cards).
A strong authentication is when the three are used.
Authentication mechanism
Crypto keys: private key or digital signature to prove one’s
identity. A private key is a secret value in possession by one
person. Digital signature is encrypting a hash value with the
private key. More secure than static passwords.
Passphrases: a sequence of characters is typed; software
transforms them into a virtual password. More secure than a
password because it is longer and easier to remember
Memory cards: it holds the authentication information. Just like an
ATM. Added cost of reader, card creation and maintenance.
Types of password:
Cognitive passwords is when fact based information is used to
verify identity. A question is asked to the subject and he answers.
Mother’s name, pet name, favorite idol. It is easy to remember.
One-time password: it is good only for one authentication, uses a
token.
Synchronous one-time password generator: synchronized with
the authentication service by using time or an event to
authenticate. Time /event driven. Encrypted using time value.
Asynchronous one-time password generator: same thing but uses
a challenge response.
Passwords characteristics: cheapest, least secure (easy to
shared, written down), most widely used authentication
technology.
Biometrics
Biometrics is physical attributes for authentication through unique
physical personal attributes, most accurate, sophisticated, and
very expensive. It is not very accepted by society. Biometrics
stores information in a database or on a smart card. It can be a 1-
to-1 matching process, where 1 feature is compared/contain to 1
specific file (retina match to a smart card). Or, it can be a 1-to-
many matching process, where 1 feature is compared to a large
database with many items.
Error types:
Type I: false rejection (False Reject Rate or false negative) is
when a good subject is not authenticated
Type II: false acceptance (False Accept Rate or false positive) is
when an impostor is authenticated.
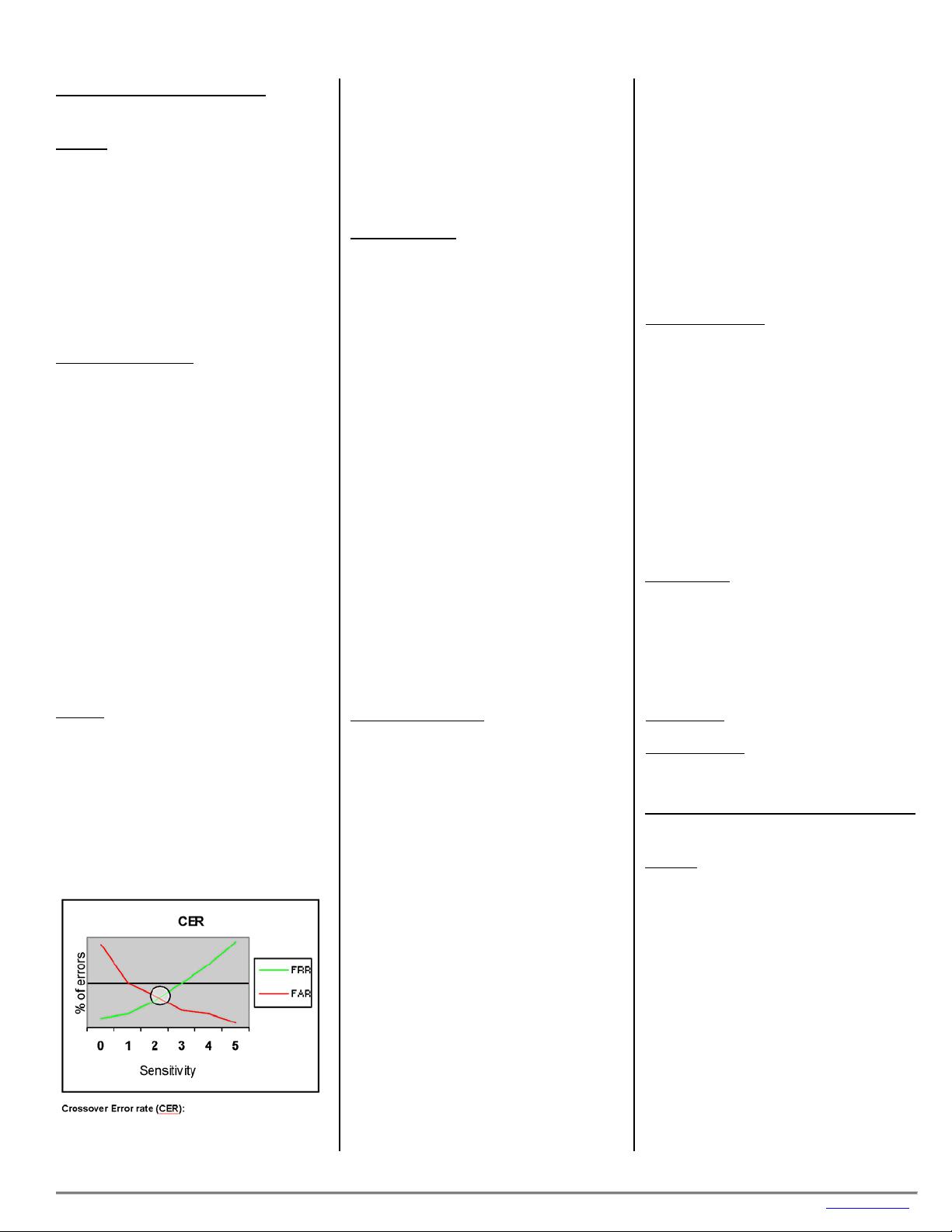
Crossover Error rate (CER):
ction and acceptance intersects.
f 100 rejected then type I errors =
has 1 out of 100 type II errors = 1%
ypes of bio spond time/CER): fingerprints (5/5),
er scan (s nger print), palm scan, hand
),
d
ntrol models:
The CER is the point where reje
system A has 3 persons out oIf
3%. The lower Crossover Error Rate (CER) is, the more accurate
the biometry is.
Example: System A has 1 out of 100 type I errors = 1%
System A
CER = 1
T metrics (re
elective fifing
geometry(4/2), iris scan (2/0.5), hand signature dynamics (7/?
keyboard dynamics, voice print (12/10), facial scan, han
topology.
Access co
scretionary Access Control
control solely granted based on the
r. Uses ACL.
ification of object, in other words
rol. It allows
user holds within the
ach
r permission and
bject to
obal rules imposed for all subjects.
ple. Rule-based access techniques are based on
administrator specifies the menu available to the user.
:
ATM.
ess relationship.
unded to the object.
termined by the sensitivity of the
ple a user may have
cation, logical
on type.
Di
DAC: discretionary access
authorization granted by the owne
Mandatory Access Control
MAC: Mandatory Access Control is based on the security
clearance of subject and class
based on labels. The OS determine access.
Role-Based Access Control (RBAC)
It’s also called a non-discretionary access cont
access to objects based on the role the
company. Administrator assigns to a role certain rights and e
user is placed in a role. Oracle works that way.
Lattice-based Access Control:
Every pair of elements is compared to roles, thei
level of the oclearance levels with the sensitivity
determine access level.
Ruled based
Security policy based on gl
MAC is an exam
specific rules that indicate what can and cannot happen to an
object.
Restricted interfaces
Menus: the
Shells: the administrator specifies the menu available to the user
through OS command.
Database view: limited by table view.
Physically constrained
limiting keypad or touch buttons like an
Control matrix
Table of subjects and object specifies their acc
Capability table
Capability table specifies the access rights a certain subject has
to an object.
ACL
ACL are used to authorize a subject to access an object and they
are bo
Content-dependent access control
Access to objects can be de
content within the objects. As an exam
access to a payroll DB but another user cannot.
Access controls attributes: Groups, physical lo
location, time of day, transacti
Access control administration
Access control administration – centralized
ake access rights policies
thentication protocol that authenticates and authorizes. It
unicate.
DIUS. It
ovides users authentication with more than just SLIP and PPP,
es a
ccess Controller Access Control System is
authentication protocol to authenticate remote users. It splits
ntrol administration – Decentralized
ontrol is given to people closer to the resource. Access control
esents their credential once, the user can then access all
he
rver (AS),
AS sends
ironment. 1) user sends credentials to AS, 2) AS sends token
e Access
terminals network where each terminal
quests tickets from the mainframe.
Decide on the model, 2) decide on the technology/techniques,
d (centralized, decentralized, hybrid)
min methods. One
vidual users are
One entity, senior management m
admin enforce it, RADIUS, TACAS+, DIAMETER
RADIUS: Remote Authentication Dial-in Service is an
au
provides a handshakes protocol. User dials-in to comm
RADIUS server holds a database of users and credentials.
Communication between client and server is protected. Steps: 1)
user dials-in (PPP) 2) RADIUS prompt for credential. 3) User
supplies credential. 4) RADIUS client sends credential to RADIUS
server. 5) RADIUS server accepts, reject or challenge. 6) If
authenticated, RADIUS client access to network.
DIAMETER: is a protocol designed better then RA
pr
it provide protocols for PDAs, laptops or cell phones. It includ
better message transport, proxying, session control and higher
security transactions.
TACACS+: Terminal A
an
authentication, authorization and auditing features. It is a Cisco
protocol.
Access co
C
is processed by several entities.
Single Sign-on technology: is a technology where the user
pr
resources across accredited network. It is less administration,
user is centralized, user only needs to remember one set of
credentials. SSO uses scripts or a directory services (LDAP). T
various protocols are: Kerberos, Sesame, Thin clients.
Kerberos: 1)user authenticates to the Authentication Se
2) initial ticket, 3) user requests to access an object, 4)
each time user requests to access an object the Ticket Granting
Serv (TGS) creates new ticket with session key from the Kerberos
Distribution Center(KDC), 5) user accesses the object. Downfalls
are single point of failure, secret key stored with users, dictionary
attacks, KDC must be available, by default not encrypted.
Sesame: Secure European Applications Multi-vendor
Env
back to user, 3) user with token requests to the Privileg
Server (PAS) a Privilege Access Certificate (PAC), user accesses
the object server.
Thin-client: a dumb
re
Steps of controlling access:
1)
3) how is access be manage
Access control administration – Hybrid
Combines centralized and decentralized ad
entity controls what users accesses and indi
allowed to decide who can access their own resources.
Access control categories:
Technical Access Controls:
ol access
ucted to provide and
ontrols:
work segregation separates the network from others.
the network’s surroundings.
ke
policies standards as a way to enforce
ntrol characteristics are preventive detective,
rective, deterrent, recovery, and compensation. Often these
System access: computer contr
Network architecture: network constr
enforced trough logical controls.
Network access: Network devices are used to control what
entities enter and leave a network.
Auditing: controls through tracking activities of users and
systems.
Physical C
Net
Perimeter security of
Computer Controls provides a physical control to protect. Li
removable HD.
Administrative controls:
e those that useAr
controls.
Access co
cor
controls can be combined.
Intrusion detection
There are two types of IDS, networked based and the host-based.
sequence of user activities or
ggered by activities that compromise the system states.
storical pattern of intrusion to a behavior within the system.
The networks based listen to a segment of the network and the
host-base listen to a host only.
IDS can be ruled-based where a
tri
Statistical/anomaly-based function by comparing a known
hi
Signature-based is compared with a signature database.
Attacks to access
See attacks on telecommunication services
Attacks on passwords
Dictionary attacks is a program with a list of possible passwords
that tries different characters, not
ain 2 - Telecom and net security
Brute force: is a program
words.
Dom
:
The purpose of this domain is to segregate non-trusted networks
using devices, architectures, and protocols to protect the trusted
network.
Definitions
: is a network that allows sharing resource in a small area.
e that connect business to WAN.
tion’s wall connected to
extranet.
in which each character is
without reference to a standard clock;
ationships.
tral hub to which all the
ation).
B,
LAN
MAN: backbon
WAN: bounded by geographical region.
Intranet: network within the organization’s walls.
Extranet: network outside of the organiza
business partner.
Downstream liability: responsibility to partner to not introduce a
vulnerability on the
EDI: Electronic Data Interchange, exchange data between
partners in a standard format.
Broadband: more than one channel.
Base band: one channel.
Asynchronous: A type of transmission
transmitted independently
uses stop and start bits.
Unicast transmission: one-to one relationship.
Multicast: one to many rel
Broadcast: one to all relationship.
MAU Multistation Access Unit: is a cen
computers are connected (ring form
Beaconing: detection of a problem then sending a beacon frame.
Tunneling: refers to encapsulation of protocol A within protocol
such that A treats B as though it were a data link layer. Tunneling
is used to get data between administrative domains, which use a
protocol that is not supported by the Internet connecting those
domains. PPTP and L2TP are tunneling protocols
CISSP Aide-mémoire www.ericallaire.com
1

CISSP aide-mémoire
War dialer: program that dials numbers until a modem is found.
Phreaker: Phone hacker that specializes in telephone frauds.
TCP/IP
Transmission control protocol/internet protocol is a suite of
t rule the way data travels from one device to
e and
tocol
DP is a connection-less protocol which does not handshake,
s, doesn’t communicate back to the
data transmission types
protocols tha
another. It is divided in two TCP and IP. The TCP is a reliabl
connection oriented protocol. The IP is a connectionless pro
that routes data. IP works at the network layer providing routing
services. IP does not provide a reliability that each packet has
arrived. TCP ensures that each packet reaches their destination
using handshakes. Ver6 is 128bit address ver4 is 32. TCP and
UDP have over 65,000 ports, 0-1023 well-known ports.
User Datagram Protocol
U
doesn’t sequence its packet
source, but is faster than TCP and good to provide video
streaming.
Cabling and
bles:
e, more resistant to
ce than CAT, more expensive. Broadband or base band
te noise, attenuation, and cross talk.
,
ubject to interference.
use the right fire rated cable. Plenum
able meet specific fire code and it is made of
Ca
Coaxial cable is a surrounded copper wir
interferen
Twisted-pair made of copper wires shield (STP) or unshielded
(UTP). Each pair are twisted to a different spin per inch to prevent
interference, it is inexpensive. It has a high resistance to flow of
signals, radiates energy and easy to tap. CAT 1 to 7. 1 = voice, 2
= data 4MPS, 3 = 10MPS token, 4 = 16MPStoken, 5 = 100mps, 6
= 155 MPS, 7 = 1GPS.
Electro Cable issues whi
Fiber optic uses light. It is high speed, hard to tap, very secure
not s
Fire issues: it is important to
space c
fluoropolymers. The non-plenum cables are made of PVC.
LAN technology
Network topology
s the physical arrangement of systems and
ng a star, ring, tree, mesh (partial, full), or
y
edia access technology is how systems communicate over the
cast and
lision domains, uses CSMA/CD, full duplex, used on STP,
ring technology developed in 70’s, all nodes are connected
entral device (MAU), the rings extend out the station and
uence of 24-bit known as a "token" is passed from node to
e
s access method used by some
uter/terminal systems whereby a "master" station asks many
,
of rules enabling computers or devices to exchange data
th as little error as possible. The rules govern
solving local network addresses by mapping an IP address (i.e.
otocol that diskless host uses to find its Internet address at
essage Protocol (ICMP). The protocol used to
dle errors and control messages at the IP layer. ICMP is
ard that defines methods for remotely managing active
ch
ectronic mail messages are communicated over the Internet.
Network topology i
devices usually formi
bus (linear, tree) pattern.
Media access technolog
M
media and access method is how the computer gains access to a
shared network object. Here are some technologies:
Ethernet is a LAN sharing technology that uses broad
col
coax;
Token
to a c
back to MAU one token on network at one time;
Token passing is a media-access-control strategy in which a
seq
node. The node that currently holds the token has control of th
communication channel.
Polling is a communication
comp
devices attached to a common transmission medium, in turn
whether they have information to send.
Protocols stack:
A set
with one another wi
issues, such as error checking and data compression methods.
Address Resolution Protocol (ARP). A TCP/IP protocol used for
re
a MAC address) to a physical address. It is not use for routing.
ARP poisoning is the unauthorized alteration of ARP table.
Reverse Address Resolution Protocol (RARP). The Internet
pr
start-up. RARP maps a physical (hardware) address to an
Internet address.
Internet Control M
han
actually part of the IP protocol. ICMP report routing failures, test
node reachability, increase routing efficiency.
Simple Network Management Protocol (SNMP), an Internet
stand
network components such as hubs, routers, and bridges.
Simple Mail Transfer Protocol (SMTP), the standard by whi
el
Other protocols: LDP, NFS, TFTP, FTP, Telnet, BootP.
Network devices and services
What is a difference between firew
trusion blocking system that opens
all and IDS? The firewall is an
certain ports and blocks all
all packe the n e
Th vi ora
s:
method of guarding a private network by analyzing the data
entering. Firewalls can also provide network address
in
the others. The IDS is an intrusion detection system that detects
it filters all network traffic, whereas the IDS does not affect
network traffic at all and that it accepts the input only without an
output.
Firewall
ts on
e firewall ine
etwork in r
tably deteri
al-time and blocks illegal sessions.
tes system performance because
A
leaving and
translation, so the IP addresses of computers inside the firewall
stay hidden from view.
Packet-filtering firewalls (layer 3) use rules
based on a packet’s source, destination, port or other basic
information to determine whether or not to allow it into the
network. More advanced, stateful packet filtering firewalls (layer
7) have access to more information such as; conversation, l
state table and context of packets; from which to make their
decisions. Application Proxy firewalls(layer 5), which look at
content and can involve authentication and encryption, can be
more flexible and secure but also tend to be far slower. Circui
level proxy looks at header of packet only, protects wide range o
protocols and services than app-level proxy, but as detailed a
level of control. Basically once the circuit is allowed all info is
tunneled between the parties. Although firewalls are difficult to
configure correctly, they are a critical component of network
security.
Demilitariz
ook at
ts-
f
ed zone (DMZ) is an area of a network, typically
tween the internal corporate network and either the external
alls,
d gateway, host or set of machines that provide non-
rvices between the protected, local network and the
Firewall placements:
rewall can be placed to create a DMZ allowing a buffer zone
. The bastion is the entry point & exit point
rewall principles:
, security is focused at one point. Having a
d will increased security. Firewalls present a
n inside attackers, IDS does. Remote access
t protected using firewalls. Those were some
ead
ll
ent
sical layer hardware device called a Data Diode is used to
ap between the secure network and the general-
be
Internet or a partner, vendor, or client, usually between firew
providing some service or services.
Bastion:
An expose
secure se
Internet, and resides on the public segment.
Fi
between two networks
out of the system. It is a system tightly locked with no necessary
services running such as user accounts or user files.
Fi
When using firewalls
distributed approache
potential blockage to flow of traffic taking away quick access to
services to lawful users. Most firewalls don’t protect against most
viruses passing trough e-mail, the virus scanner does. Firewalls
of the downside of firewalls. Having two firewall administrators
available to ensure one is always available. Remote access for
administrators should use strong authentication over an un-
trusted. The only account on the firewalls should be those
administrators with privilege set to make changes only. The
firewall configurations should get backed up periodically with r
only media. A second firewall should be ready to go on-line
quickly. Any irregularity should be recorded and reported.
Configured so the “no reply” on port scans or pings. If a firewa
ever goes down the new one should be re-set and re-implem
necessary controls, re-run integrity controls after reconfiguration.
Most vulnerability is caused from missed configuration (default
settings). Ensure to have a security policy dictating regulations
away from the firewall default. The firewall should be set to fail-
safe not fail-open. A full backup before being put into production
(day zero backup).
Data diode:
don’t protect agai
using modem is no
A phy
create an air g
purpose network. The Data Diode then permits data to flow in
only one direction - from the general-purpose network to the
secure network. (I am writing a paper on the data diode)
Connectivity protocols:
Connectivity protocols
access from outside the LAN, this
and dial-up devices.
n’t have
IP,
Password Authentication Protocol used by remote users,
stablished, credentials are sent in
s to get different types of identifications and
: provide remote access to an organization's network via the
cond
re
ternet Protocol Security. IPSec uses encryption
Several protocols assume
connectivity uses modem
SLIP: Serial Line Internet Protocol, replaced by PPP, it is
asynchronous serial connections. Unlike PPP it does
header and data compression, error correction, support different
authentication methods, encapsulate other protocol other than
and support other types of connections other than asynchronous.
PPP: it encapsulates over a serial line for dial-up connectivity.
Authenticated using PAP, CHAP, EAP.
Authentication protocol:
PAP:
authenticates after PPP is e
clear text, vulnerable to sniffing, man-in-the-middle and attacks.
CHAP: authentication protocol that sends a challenge response,
credential have encrypted values, periodically sends a challenge
to protect man-in-the-middle attacks, password is not sent over
the wire.
EAP: Extensive Authentication Protocols: enables more
possibilitie
authorization information from users.
Tunneling protocols
VPN
Internet. VPNs sends data over the Internet through secure
(encrypted) "tunnels." It is encrypted using PPTP, IPsec and
L2TP. Each frames is wrapped and encapsulated within a se
frame. L2TP: (layer 2) Layer Two Tunneling Protocol - A secu
protocol used for connecting Virtual Private Networks over public
lines (Internet).
PPTP: (layer 2) point-to-point tunneling protocol.
IPsec: (layer 3) In
technology to provide data confidentiality, integrity, and
Devices OSI layer Function in order of security controls
Repeater Physical Device used to amplify and/or regenerate attenuated signals.
Bridge Data link Connects two or more networks and forwards packets between t
frames. Bridges do not require IP addresses and will pass broadcas
hem. Bridges read and filter packets and
t traffic.
Router Network Device that determines the next network point to which a data packet should be forwarded towards its
destination. The router is connected to at least two networks and determines which way to send each data
packet based on its current understanding of the state of the networks it is connected to. Routers create
or maintain a table of the available routes and use this information to determine the best route for a given
data packet.
Brouter Data,
network wards based on network layer information). The bridge/route decision is based on
Device which bridges some packets (i.e., forwards based on data link layer information) and routes other
packets (i.e., for
configuration information.
Switch k, but
witch operates on Layer 2 (or above) of the OSI 7 layer model and a hub
Data Similar to a hub, in that it provides a central connection between two or more computers on a networ
with some intelligence. (A s
operates at Layer 1.) Whereas for a hub any message received at the hub is broadcast to all the attached
computers, with a switch it is sent only to the destination computer and is not visible to other attached
devices. This does not prevent "broadcast" messages from being sent to all attached devices.
Gateway Applicati
on
o A computer system for exchanging information across incompatible networks by translating between tw
dissimilar protocols.
Virtual
LAN
Top
physical
A logical, not physical, group of devices, defined by software. VLANs allow network administrators to re-
segment their networks without physically rearranging the devices or network connections.
Firewalls Apps,
ty
sessions,
network
A computer device and/or software that separates a Local Area Network from a Wide Area Network and
prevents unauthorized access to the Local Area Network through the use of electronic securi
mechanisms such as IP filtering, address re-mapping, etc . More on
firewalls.
IDS Session Intrusion detection system which is either host-based or network-based or application IDS. An ID
monitors all of the network traffic from a central point (network-based), generally
S
d
Ss
inside the firewall, an
reports on traffics that seem containing malicious traffic. Needs updates, just like a virus scanner. ID
comes in various detection types: Knowledge/signature-based, Behavior/rule-based (state and model
based) or statistical.
IPS Session
op the malicious activities. IPS systems are able to detect malicious activities using
Intrusion Protection Systems works very similar to IDS, except that IPS will usually take certain course of
action to prevent or st
the characteristics of the behavior and not just an attack signature. This line of defense can help prevent
forecast attacks.
Data Diode
Physical See below and visit www.EricAllaire.com (***if available)
Architecture type characteristics
Dual-homed
Single co
Untrusted net > firewall >
t
mputer with 2
trusted
k
trusted net > hos
(Single tier)
NICs, one to the
network and the other to
external untrusted networ
Screened host
Untrusted net > router >
firewall > host
(Two tier)
Router filters traffic before
it is passed to the firewall
then the firewall passes it
to the host directly.
Screened subnet
t > router > semi
ll > trusted
MZ.
Untrusted ne
trusted net > firewa
net > host
(Three tier)
External router filters traffic
before it enters the D
Traffic heads towards the
internal network then goes
through a firewall and
another router.
CISSP Aide-mémoire www.ericallaire.com
2
剩余10页未读,继续阅读
资源评论

 ok800net2022-02-05垃圾, 都是英文版的。
ok800net2022-02-05垃圾, 都是英文版的。 hao1414212014-08-11学习安全的一本很的资料
hao1414212014-08-11学习安全的一本很的资料 adrianobean2013-11-02非常好的资源 打印出来看也非常好
adrianobean2013-11-02非常好的资源 打印出来看也非常好
猴子搬来的救兵Castiel
- 粉丝: 3577
- 资源: 902
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

 前往需求广场,查看用户热搜
前往需求广场,查看用户热搜安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
