
DeFoxIV User Guide
This document is written as an update to the DeFoxIII User Guide. If you are not familiar with
DeFoxIII, you should first read DeFoxIII User Guide that you will find at the end of this file.
Additional feature included in DeFoxIV starting with version 1.008.188
If you are not familiar yet with DeFoxIV, you should first read this instruction beginning with
the next item.
The new code encryption method introduced in DeFoxIV uses the same key for entire
application. If cracker in some way will be able to find this key, then the problem to crack the
application will become much easier. New DeFoxIV version gives you the possibility to change this
key programmatically for some code blocks. To change the key you should use the next command
="DEFOX KEY ON XXXXXXXX"
Instead of XXXXXXXX you should insert arbitrary 8 symbols, which will be used to modify original
key. In order to restore the original key you should use the command
="DEFOX KEY OFF"
This feature should be used with great carefulness. Incorrect use of it may easily lead to the situation
where the code encrypted with one key will be decrypted with another one, so the application will
produce an error. Responsibility that this did not happen lies entirely on the programmer. Here are the
most common rules you should keep in mind when using this feature.
1. In any procedure/function/method where key modification command is used, later there must
be key restore command.
2. Between the commands that modifies and restores the key there mustn’t be command that
may change command flow to get out the block with modified key. Such commands are: user
defined function call, operator DO FORM, operator RETURN, etc. Exception: you may use user
defined function call if the function doesn’t use code encrypting (="DEFOX OFF").
3. If there are such constructions as IF/ENDIF, FOR/ENDFOR, CASE/ENDCASE, DO/ENDDO,
TRY/CATCH inside the block with modified key, they must be included in block entirely. I.e.
you should avoid code similar to the following
="DEFOX KEY ON XXXXXXXX"
IF MyVar = 0
…
="DEFOX KEY OFF"
…
ENDIF
4. It is not recommended to include block with modified key in a cycle that runs many times
because key modifying command is time consuming.
5. If you use commands ON KEY LABEL, ON ESCAPE, ON ERROR, or timers that may change
the command flow outside block with modified key, then code that will run must be
unencrypted (="DEFOX OFF").
6. You should use this feature only on those blocks of code that need highest security.
7. If you after all can’t manage to run your program correctly, better not to use this feature at all.
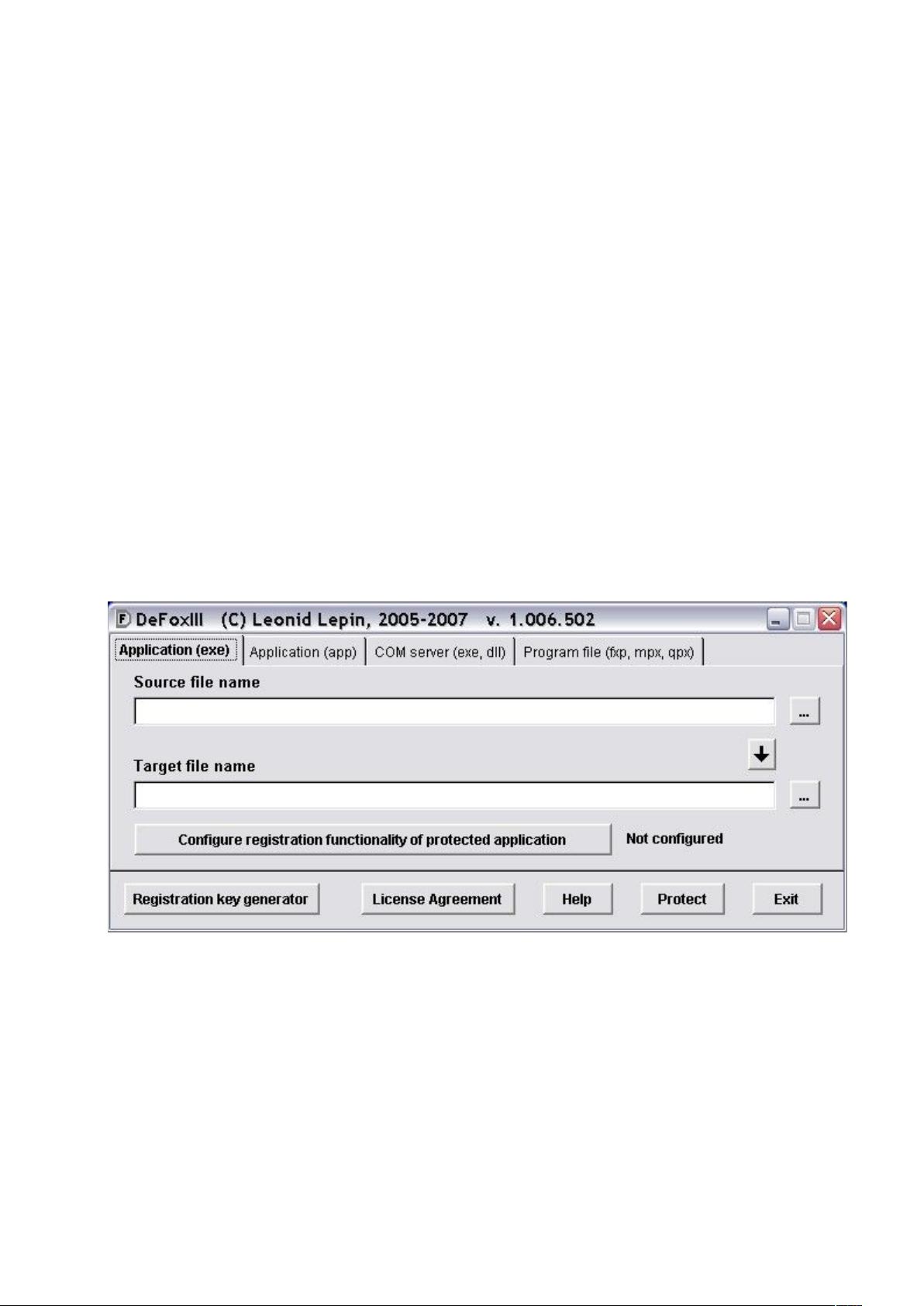
Major Changes Since The Previous Version (DeFoxIII)
Additional protection layer.
Added the capability to protect external scx and vcx files.
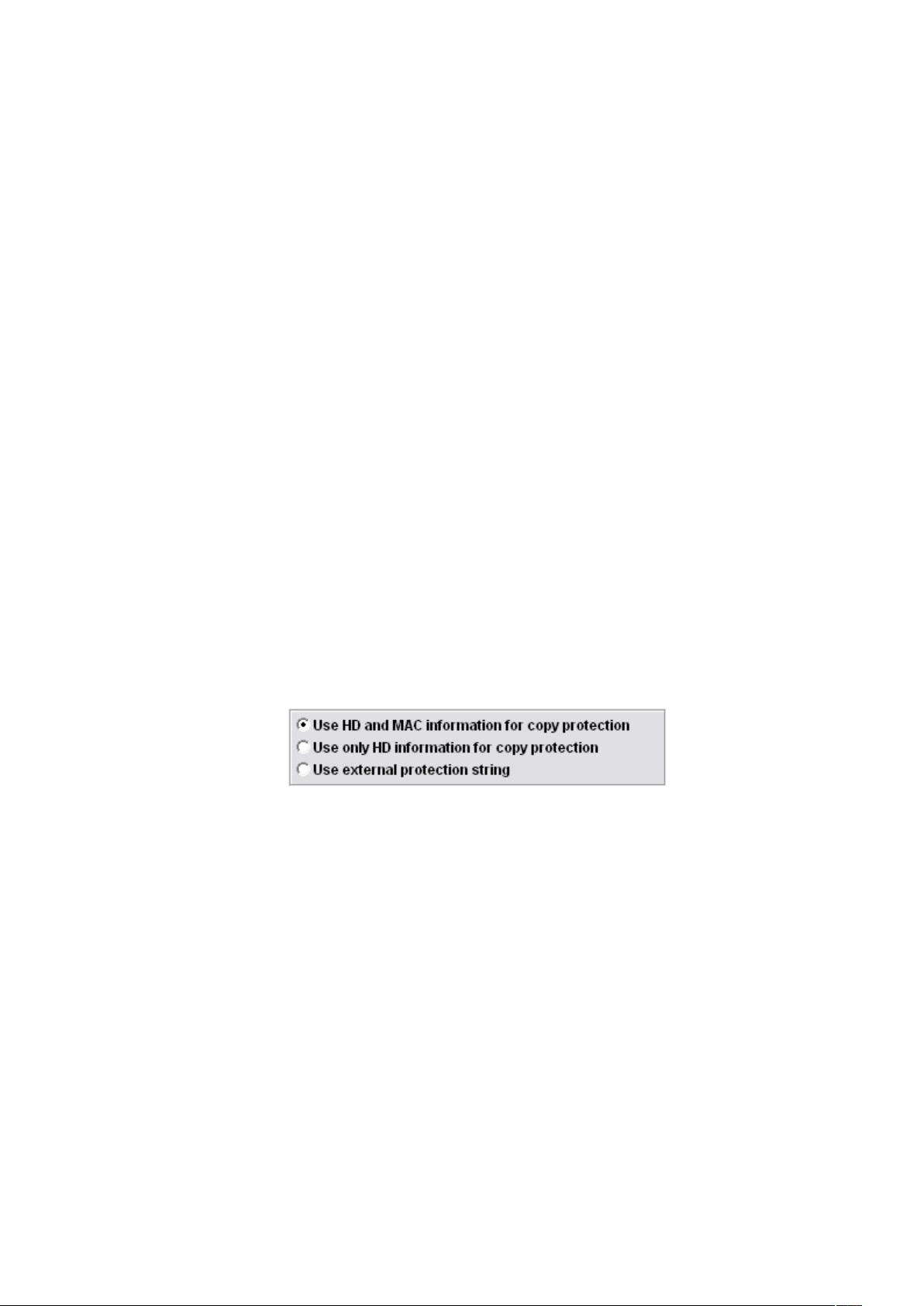
Applications with registration capability may now be bound to a given computer using a
function specified by the application developer.


















- 1
- 2
前往页